Articles in Category: Managing Email
Articles discussing how to manage email – from creating accounts, filing messages, and just generally using email effectively.
What Is “Mailer-Daemon” and Why Is It Sending Me Email?
Get an email “from” mailer-daemon? There’s a good reason this mysterious sender keeps showing up.
Why Can’t I Change My Email Address at Some Online Providers?
Your email address changed, but the website where you have an account won’t let you update it. Now what?
How Do I Change My Email Address?
Changing an email address changes a lot more than the address. I’ll look at common scenarios and a few additional approaches.
How Do I Deal With Getting Someone Else’s Email?
You didn’t ask for it, but there it is: email meant for someone else in your inbox. I’ll discuss why this happens and what you can do about it.
Are Deleted Emails Really Deleted?
Deleted an email and think it’s gone forever? I’ll explain what “delete” really means in webmail and desktop programs, why trash folders and database files can leave messages recoverable, how backups and even court orders can bring them back, and the inconvenient fact that the other person may still have a copy.
The Wrong Way to Change Your Email Address
Emailing your entire contact list with a notice that you’ve changed your email address is NOT the way to change your email address. I’ll show you what to do instead.
How to Back Up Outlook.com Email
Outlook.com accounts are hacked into and lost every day. Here’s how to ensure you won’t lose email or contacts if it happens to you.
How Do I Send an Email to Many People?
Want to email a big group without looking like a spammer or getting blocked? I’ll show you why the usual tricks don’t work well and walk you through safer, smarter ways to send group emails, from simple groups to full newsletter services.
Can I Tell If Email I Sent Has Been Read by the Recipient?
People want to know if someone’s opened their email. I’ll explain why features and tools claiming to do that can’t work most of the time. I’ll share the only way to know for certain your message was read.
How Do I Get an Email Address for Life?
Tired of changing your email every time a service shuts down or your ISP changes? Learn the smartest way to secure an email address that’s truly yours for life, and why relying on free or “lifetime” promises could leave you stranded.
Why Does Email I Send Fail But a Reply Works?
If sending an email bounces but replying works, the culprit is usually a wrong address hiding in plain sight. Learn how display names, typos, and auto-complete can fool you, and how to fix the problem so your messages get through every time.
How to Transfer Your Email From a PST to Thunderbird for Free
Switching from Outlook (classic) to Thunderbird? You don’t need to buy tools. With a little time and a free email account, you can move your messages yourself. I’ll walk you through the steps to transfer your email safely and reliably.
Why Must I Re-Enter my Email to Unsubscribe?
If a website makes you re-enter your email just to unsubscribe, it’s bad design, or worse, a shady tactic. I’ll explain why this happens, what it means, and how to spot when it’s just spam trying to trick you.
Why Email Forwarding is Broken and What to Do Instead
Learn to pull your email together rather than push it.
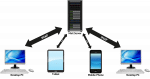
What is IMAP and How Can It Help Me Manage My Email?
IMAP is a protocol that makes dealing with email on multiple devices much easier.
How Do I Tell Someone They’ve Entered the Wrong Email Address?
Many websites ask you type your email address in twice because it’s so easy to make a typo and bring communication to a screeching halt.
Why Am I Getting a “Delivery Status Notification (Delay)” on an Email I Sent?
Delays happen for many reasons; it’s the nature of the email infrastructure. If you get a “Delivery Status Notification (Delay)” message, your options are limited.
What Does the “Mailbox Unavailable” Error Mean and How Do I Fix It?
“Mailbox unavailable” is a common email bounce message that tells us very little. I’ll review some of the more common causes of this message.
How Do I Stop Outlook.com from Putting Legitimate Messages in the Junk Mail Folder?
Outlook.com, like most email services, tries hard to keep spam out of your inbox. Sometimes it gets a little too aggressive. I’ll look at how to tame it.
What’s the Difference Between an Email Domain, Account, Address, and Alias?
Email terms can be confusing, but they don’t have to be. I’ll explain the differences between domains, accounts, addresses, and aliases—plus how they work together to get your messages delivered. This simple breakdown (with an easy metaphor) will help you understand and manage your email with confidence.
How Do I Find Someone’s Email Address?
It can be extremely difficult to find the email address of someone you want to contact. To begin with, they must want to be found.
How Do I Move My Address Book From One Provider to Another?
Taking your contacts with you when moving from one platform to another is a clumsy process.
Can Permanently Deleted Email Be Recovered?
In most cases, deleted email is gone beyond your ability to recover it. As always, however, there are exceptions.
What Does “Over Quota” Mean? What’s a Quota?
Being over quota means you’ve received or kept too much email. To deal with it, you need to understand where that email is being kept.
What Is the Thunderbird Email File Location in Windows?
Thunderbird stores everything in what it calls a profile. I’ll show you how to locate yours.
Can I Recall an Email From Gmail or Outlook.com?
You may have heard of a feature called “message recall”. For all intents and purposes, it’s not real.
How Do I Move Emails From One Account to Another?
Moving email from one account to another just takes some configurating and drag-and-dropping.
Why Are My Mail Folders Not Showing In Outlook?
You’ve got your online email nicely organized into folders. Then you move to a desktop program, and none of the folders come with you. What now?
Thunderbird: a Free, Open Source, and Powerful Email Client
Thunderbird is a robust and powerful email program that can meet the needs of both light and power users. I use it all day every day.
How Do I Change My Email Name?
Changing your email name is usually easy, but changing your email address involves setting up a new account.
How Does “Undo Send” Work?
Gmail and other email services offer the ability to “undo” an email. I’ll look at how it works and why it’s not what people expect.
Will Email Bounce If I Send It to a Closed Account?
If you send email to an invalid address or a closed account, you may get a bounce back. You just can’t count on it.
How Do I Forward My Old Email Address?
A few email providers have an email-forwarding feature, but most do not. If available, forwarding only works as long as you continue to own the original account.
How Can I Avoid Losing My Business Email Account?
Losing your business email account can have dire repercussions. I’ll show you how to protect yourself.
What are POP3, IMAP, and SMTP?
POP, POP3, IMAP, and SMTP are all acronyms used in configuring email. We’ll look at what they mean and how they relate.
How Do I Edit a Reply?
Edit a reply before sending it. Clean up your message, remove email addresses, and more.
How Do I Find Where My Email Has Been Used as a Recovery Email?
Turns out that finding all the places you’ve used your email address as a recovery address is close to impossible.
How Do I Delete Multiple Emails When I Have a Lot to Delete?
It can be a challenge to delete multiple emails. I’ll look at some of the concepts and techniques used by various email programs to make it easier.
Why Online Petitions are Often (and Still) a Bad Idea
Internet and online petitions seem like a quick and easy way to make a statement. Unfortunately, they’re often ineffectual, and at worst, they do harm.
All the Emails in My Inbox Disappeared! What Do I Do?
I get reports of people who have lost the contents of their inbox. We’ll look at a couple of common causes and resolutions.
Why Do Edits Made to a Document Emailed to Me Disappear?
Changes you’ve made to a document that was emailed to you can easily disappear. Let’s avoid that.
How Do I Keep My Email Address When I Change My ISP?
Changing your internet provider doesn’t mean you have to lose your email address. I’ll explain why ISP-issued addresses can trap you, and offer better options like free online services, mail forwarding, or even owning your own domain—so your email stays yours no matter where you move.
How Do I Reactivate an Old Email Account?
A closed email account is either waiting for you to reactivate it or is closed for good. The only way to tell is to try.
Be Careful Deleting Email If You Use IMAP
When an email account is configured to use IMAP protocol, it’s easy to accidentally delete more than you realize.
The Frustration of Email Contacts Backup and Transfer
Address book contacts suffer from a lack of standardization, particularly when it comes to synchronizing or transferring between systems.
How Do I Hide the Email Address I’m Sending Email To?
It’s possible to send email to someone without having their email address show up on the To: or CC: lines by using Blind Carbon Copy, or BCC.
If I Send to a Bad Email Address, Will Someone See It?
People often send email to the wrong address by mistake. But what happens if the email address is invalid?
Outlook Keeps Asking for Password — Why?
When your email program starts repeatedly asking you for your password, it’s a sign of a problem. Most of the time, it’s a simple problem.
Can I Have Two Different Email Accounts with the Same Email Address?
Having multiple email accounts with the same email address is not possible, and may reflect a misunderstanding of how addresses and accounts relate.
Will I Lose My Email If I Don’t Check It for a While?
It’s important to check and possibly download your email from time to time so that you won’t lose email, or even the entire account.