Articles in Category: Networking
Network connectivity and configurations, protocols and problems, articles relating to how computers connect.
How Do I Change My Router’s Password?
Your router’s default password might as well be no password at all. Changing it is an important step you can take to secure your home network. I’ll show you how to find your router’s settings and lock it down with a strong password.
What’s My IP Address?
You might be sharing more than you think when you visit a website. Your IP address, your browser details, and even what you searched for to get there is all visible. I’ll explain what websites see when you show up and why it matters.
Why Doesn’t My Machine’s IP Address Match What I’m Told on the Internet?
Ever wonder why your computer shows one IP address, but websites see something totally different? They’re both right. I’ll describe how your router juggles two addresses behind the scenes and how that protects you every time you go online.
How to Identify Your Machine’s Network Connections
Your computer might be chatting with hundreds of servers right now, including sites you might not expect, without you knowing! I’ll show you free tools that let you see what your machine is up to online.
How Do I Tell Which Wi-Fi Protocols My Computer Supports?
Ever wondered if your Wi-Fi card can handle the latest speeds, or why it won’t connect in certain places? I’ll show you exactly how to check which Wi-Fi protocols your computer supports, and what those cryptic “802.11” labels actually mean.
Four Risks With Free Wi-Fi
Freely accessible Wi-Fi is almost everywhere, and most systems are set up to use it safely. There are a few things to pay attention to in order to stay safe.
7 Ways to Increase Internet Speed in Windows
Internet speed: we all want it. Here’s how to improve yours.
Public or Private? Picking and Changing the Windows Network Setting
Not sure if your Windows network should be public or private, or even what that means? I’ll show you what each means, when to use them, and the simple steps to switch.
How Does a VPN Protect Me?
A VPN can keep your online activity private, especially on open Wi-Fi, but it’s not magic. I’ll show you what a VPN hides and what it doesn’t, so you can decide if it belongs in your security toolkit.
How Do I Get My Windows Computers to Network With Each Other?
Home networking can be very difficult. I have a few tricks that work well for me.
Someone Has My IP Address. Should I Be Scared?
If someone threatens you because they know your IP address, it’s an empty threat.
How Do My Mobile Data Connection, Internet Connection, and Wi-Fi Connection Relate?
Understanding how your devices connect to the internet is useful, especially when the power goes out.
What Is Ping and What Does Its Output Tell Me?
Ping is one of the oldest diagnostic tools. It validates connectivity from point A to point B and provides additional useful information.
Does Having a Visible Wi-Fi Password Add Security Compared to an Open Wi-Fi Hotspot?
Using a password-protected WPA2/3 hotspot is a minor inconvenience for a very significant level of additional security.
Why Might My Internet Connection Randomly Stop Working?
Let me walk you through eight of the most common issues when it comes to internet connections, drops, and general connectivity.
Can My ISP See I’m Using a VPN?
Virtual Private Networks have characteristics visible to your ISP. I’ll discuss what they can and cannot see.
Increasing the Odds That Windows Network Sharing Will Work
Networking is… tricky. Here’s a process that works fairly reliably for me.
How Do I Get Wireless Internet?
You hear a lot about wireless internet, but it’s not something you can just connect to anywhere. It’s more often something you purchase and set up.
5 Steps to Better Wi-Fi In Your House
Wi-Fi has only become more important as more devices and online activities become essential at home. I’ll review some of the things to investigate as you search for better Wi-Fi performance.
How Do I Get Someone’s Location From an IP Address?
While getting someone’s name and address from their IP address is technically possible, it’s also difficult and requires law enforcement’s help.
Is It OK to Use this Random Wireless Network I Just Found?
When scanning for wireless connections, you may find several that are unknown, yet appear open and available. Using them is very risky.
Why Does My Home Network Only Work with One Computer at a Time?
If there is a conflict with your IP address, it could result in only one of the machines on your network connecting at a time.
How Do I Monitor My Home Network Usage?
It’s easy to monitor the amount of bandwidth a computer is using. The entire network? Not so much.
What Is a “Subnet Mask”?
A subnet mask is a way of telling your computer or router what network addresses are local and which are remote.
How Do I Monitor Network Activity in Windows?
You can find out a lot about what your computer is doing online by using the Resource Monitor in Windows.
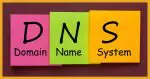
I Keep Getting “DNS Server Not Responding” Errors. What Can I Do?
Slow Domain Name System (DNS) lookups can affect your apparent internet speed. Your ISP should provide fast DNS, but there are alternatives.
8 Steps to Securing Your Router
Your router is your first line of defense against malicious attacks from the internet. Is yours secure?
Who Is My Home Network Administrator?
Some Windows messages indicate that something was set by your network administrator. That’s probably you, even if you didn’t do it.
Proton VPN: A Fast, Reliable VPN Service
On a recent overseas trip, I exercised Proton VPN extensively and was very pleased with the results.
Using Chrome Remote Desktop in Windows
Google’s Chrome Remote Desktop is a free and convenient remote-access tool allowing you to get help from people you trust or be the person giving help.
How to Recover a Wi-Fi Password in Windows 10 and 11
If you forget your Wi-Fi password Windows may be able to remind you what it is.
Why is My Wi-Fi Speed Slow?
Wi-Fi speed can be slow for many different reasons. Slow Wi-Fi can also be a symptom of speed constraints elsewhere.
Why Does My Laptop Keep Connecting to the Wrong Wi-Fi Network?
Windows tries to be helpful by remembering the Wi-Fi networks you’ve connected to in the past. Sometimes, though, you want it to forget.
Increase Your Wi-Fi Range While Camping
Bad Wi-Fi signal strength? A range extender need not be expensive, and can be a handy and flexible solution.
Can a Website Identify Me When I Visit?
Web servers get your IP address when you visit. Whether or not that or other information can be used to identify you, specifically, depends on a lot of things.
How Do I Block Someone From Using My Wi-Fi?
Wondering how to stop someone from using your Wi-Fi? I’ll walk you through the best ways to secure your connection, from setting passwords to disabling guest access.
What is “Limited Connectivity” and How Do I Fix it?
“Limited connectivity” displays when your computer is having problems completing its network configuration. It might as well mean no connectivity.
Is Mobile More Secure than Wi-Fi?
Mobile broadband is a popular internet connection alternative. As with any connection, it’s important to understand the security ramifications and tradeoffs.
You’re Not Alone: Networking Sucks
After all this time, the average user still has trouble networking computers, and that’s really frustrating.
Can I Trace a MAC Address?
A MAC address can easily be traced for as far as it travels — which isn’t far enough to be useful.
If I Share Wi-Fi With My Neighbor, Can They See My Network Traffic?
Sharing Wi-Fi with your neighbor might seem like a friendly thing to do, but be aware you are potentially putting your own computers at risk.
How Do I Stop My Neighbor Using My IP Address?
If it’s certain a neighbor is using your IP address without permission, you need to take steps. But first you need to make sure.
How Do I Connect My Desktop to Open Wi-Fi Nearby?
Wi-Fi hotspots make for a convenient connection. To connect, you need proximity, a little hardware, and most important, permission.
What Are These Access Attempts In My Router Log?
Any device sitting on the internet is subject to a constant stream of “internet background noise”. It’s why you really want to be behind a firewall.
How Do I Protect Myself from Other Computers on My Local Network?
Many households have computers used for sensitive things sharing a network with less trustworthy users. Here’s how to increase your security.
Finding the Owner of an IP Address
While you can’t find the specific owner of an IP address, there are a few tools to see what IP-related information you can get.
Does an Open Wi-Fi Login Page Mean It’s Secure?
Absolutely not. This is a critically important distinction to make, and it’s one I’m afraid many people misunderstand.
How Do I Use an Open Wi-Fi Hotspot Safely?
Open Wi-Fi hotspots at coffee shops and other public places are opportunities for hackers. I’ll review how to stay safe.
Do I Need a Firewall for My Home Network?
A firewall is a critical component of keeping your machine safe on the internet. There are two basic types, but which is right for you?
What Can People Tell from My IP Address?
Curious what someone can really learn from your IP address? The answer is “not much.” This quick read explains what your IP does and doesn’t reveal, why location lookups are often wrong, and when only your internet provider—or law enforcement—can dig deeper.