Articles in Category: Security
Why Do Services Like Google and Microsoft Ask for a Phone Number?
Many online services request your phone number. I’ll look at how that’s typically used and why it’s a good thing.
Secure Your Most Important Accounts
Experts always recommend securing your “most important accounts”. Great. Which accounts would those be?
Why Your Computer Has Probably Not Been Hacked
I regularly hear from people who believe their computer has been hacked and is under someone else’s control. It’s very rarely the case.
Think 2FA Is Bulletproof? Here’s Why You’re Still Vulnerable
Two-factor authentication is one of the most important ways you can secure your online accounts. But that doesn’t mean you’re done.
How AI is Revolutionizing Scams: Can We No Longer Trust Our Eyes or Ears?
Scams are bad enough. Throw AI into the mix, and things only get worse.
Why Encryption Backdoors Are a Horrific Idea
A phrase we’ve heard more and more often in recent years is encryption backdoor. The concept is simple: government agencies want to be able to monitor otherwise encrypted communications. The concept is flawed.
How to Add Two-Factor Authentication to Your Google Account
Adding the most common and secure form of two-factor authentication to your account.
Is Automatic Sign-in Safe for My Email?
Having your email automatically or continually signed in to can be a security risk in some situations, but very convenient in others.
Going Passwordless Without Going Passwordless
Passwords are dying. On some services, you can start playing with the process by creating a secure password… and then forgetting it.
Is a Periodic Password Change a Good Thing?
Conventional wisdom says to change your passwords periodically. I disagree.
What Is Ultra AV, and Why Did it Show Up On My Machine?
If you’ve suddenly found an unfamiliar antivirus program running on your computer, you’re not alone.
Is My Smartphone or Smart Device Listening In on Me?
It’s not uncommon to think our smart devices are listening in when advertisements seem to follow our discussions.
Is a Passkey Two-Factor Authentication?
Passkeys are secure, but they’re not two-factor authentication in and of themselves. I’ll run the scenarios that explain why that is and when 2FA might be involved as well.
What If I Lose Everything When Traveling?
I hear from people who are concerned that they’ve put so much security in place they’ll keep themselves out in case of emergency.
Social Security Number Compromised — What to Do?
Billions of records of personal information, including Social Security numbers, has been exposed. What to do?
What’s the Best Two-Factor App?
Two-factor authentication adds a vital layer of security to your accounts, but which app should you trust? From Google Authenticator to password managers and cross-platform options, I’ll break down the best choices so you can pick the one that fits your devices, your needs, and gives you peace of mind.
More Passkey Questions
Passkeys seem like magic, and confusing magic at that. I’ll address a set of questions I received recently.
What to Do About Kaspersky Antivirus
Any software company with ties outside the U.S. comes under scrutiny. Should you be worried?
Changing Your Password After a Hack May Not Be Enough
Changing your password is a common response to account hacks. Unfortunately, it isn’t enough.
What If There’s a Passkey on My Lost Phone?
Losing a device with a passkey isn’t a disaster at all. I’ll describe why that is.
One-Time Code Contradiction: When to Share and When to Beware
You’re told not to share your two-factor or other authentication code. And then you’re asked for it.
Can Someone Install Something on My Computer When It’s Not Logged In?
If your computer is not physically secure, someone could install something even if you’re not logged in.
Surprising Reasons to Use a VPN at Home: More Than Just Privacy
Although a VPN service is probably not necessary at home, there are a few scenarios where you may want to consider it.
What to Do With an Unexpected Two-factor Code
Getting an unexpected authorization code on your phone or via email can be concerning. Let’s see when it’s a sign of a problem and what to do about it.
I Got a Call from Microsoft and Allowed Them Access to My Computer. What Do I Do Now?
A very common scam has people supposedly from Microsoft, your ISP, or other authorities calling to help you with computer problems. Don’t fall for it.
How Do I Recover Encrypted Files From Cryptomator?
Recovering individual files from a Cryptomator encrypted vault can be tricky. I’ll discuss why and how to protect your access to those files.
Beware the Middleman: How Your 2FA Could Be Compromised
Some forms of two factor authentication have vulnerabilities. Here’s how to avoid it.
Facebook Marketplace Scams: 3 Warning Signs You Shouldn’t Ignore
Facebook Marketplace scams are on the rise. Here are three red flags that should tell you something’s not right.
What Is Credential Stuffing?
Credential stuffing: less complicated than the fancy words imply and easy to prevent.
Don’t Be Ashamed or Smug
If you’re embarrassed at having fallen for a scam, it’s tempting to want hide and not tell anyone. But it’s important to learn from the experience and share it. There’s no need to feel shame.
6 Steps to Dealing With Phone Spam
Phone spam, be it voice or text, is as annoying as it is persistent. Here’s what (little) you can do.
How Can Passkeys Possibly Be Safe?
Passkeys may feel confusing now, but they’re a doorway to a more secure, less frustrating, passwordless future.
How Can I Recover an Outlook Password Without Resetting It?
Microsoft doesn’t know your Outlook.com password. Honest. That makes recovering it without changing it challenging.
How to Protect Yourself From a Two-Factor Hack
Two-factor authentication isn’t perfect, but it’s much better than not using it at all. Here are the various risks and what you can do to protect yourself.
When You Change Your Phone Number, Change Your Phone Number
The ability to keep your old phone number when getting a new phone can avoid several headaches. If you get a new number, there are steps you must take.
What Is a Pig-Butchering Scam?
Pig-butchering is a nasty term for a particularly painful type of scam. Here’s how to protect yourself.
Could Malware Record My Chats and Video Calls?
If you’re curious what might happen if a hacker was in control of your computer, the question really is “What can’t they do?”
Dealing With the Demise of Authy Desktop
Authy’s desktop version is going away (darn it!). Here’s how I will replace it.
Are the Bad Guys Winning?
Media hype makes it seem like the bad guys are winning. They’re always in the lead – but don’t believe the hype.
Can My ISP Monitor My Internet Connection?
Your ISP controls your internet connection, and it’s easy for them to monitor the data you send and receive. The question is, why would anyone monitor your internet?
Another Way to Protect Yourself From 2FA Loss
A little bit of preparation when you set it up can make losing your Google Authenticator 2FA device a minor inconvenience.
I Lost My Two-Factor Authentication (2FA) Device. How Do I Sign In?
Fear of second-factor loss prevents some people from using two-factor authentication. There’s no need to fear that scenario.
I Gave AI My Search History and Here’s What It Told Me
I was listening to a podcast recently in which one of the hosts described giving ChatGPT the history of the questions he had asked it and then asking it to build a profile on him based on that. It was interesting, of course, but it got me to thinking… why not use internet searches as … Read more
What If Password Autofill Won’t Work?
Password vaults are sometimes unable to auto-fill fields. There are several ways to work around this.
If They Got Into My Account Once, Could a Hacker Get In Again?
Once your account has been hacked, there are many things you need to consider to prevent it from being hacked again.
How to Securely Wipe the Windows System Drive
Reformatting the system drive takes a little more effort than other drives. Here are three ways to get it done.
Yes, You Should Give Google Your Mobile Number
Google uses your mobile number for verification if you lose access to your account. Some people don’t want to provide it. They should.
How Do I Change My Password for Google Mail?
There are times when a new password is what you need. Here’s how to change it.
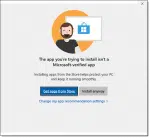
How Do I Fix “The App You’re Trying to Install Isn’t a Microsoft-Verified App”?
“The app you’re trying to install isn’t a Microsoft-verified app” message is the result of a simple setting you can change.
How to Use Just a Single Password for Everything
It’s very tempting to use only a single password everywhere. That’s dangerous, and there are better alternatives.