Articles in Category: Security
How Do I Remove Myself From a Computer?
Leaving a job and worried about what’s on your work computer? From browser history to email accounts, traces of you remain. Learn what you can (and can’t) erase, and the smartest way to protect your privacy before you walk out the door.
Can Malware Survive If I Reset My PC?
Worried a reset won’t wipe out malware? While it’s technically possible for some infections to survive, it’s extremely rare. Learn where malware can hide, which reset options are safest, and the extra steps you can take to ensure a truly clean and secure Windows reinstall.
What Security Software Do You Recommend? (2025 Q3 update)
My updated guide cuts through the hype with four no-nonsense steps to keep your PC safe. Learn what works, what to avoid, and how to stay secure without overspending or overcomplicating.
How to Safely Change Two-factor Authentication
Changing two-factor authentication apps isn’t hard, but doing it incorrectly can lock you out of your accounts. Here’s a safe step-by-step approach to make the switch smoothly, protect your access, and keep your accounts secure.
How to Save or Recover Your BitLocker Recovery Key
BitLocker could be running on your PC without your knowledge. Without the recovery key, you risk losing everything. I’ll show you three ways to check, find, and save your key.
Are There Hidden Files that Save Every Keystroke I’ve Ever Typed?
Worried your computer is secretly saving everything you type? It’s not. While there are hidden files and places keystrokes can live temporarily, there’s no master file of your entire typing history (unless malware is involved). Learn what’s real, what’s myth, and how to truly erase your data.
Prepare to Lose Your Phone
Your phone holds the keys to your digital life. If it’s lost or stolen, things can get messy fast. I’ll show you simple steps like locking, tracking, and backing up that protect your data and give you peace of mind before the worst happens.
Is It OK to Reuse Passwords on “Unimportant” Sites?
Reusing passwords on sites you don’t care about might feel harmless, but it still can open the door to bigger problems. I’ll look at why even “unimportant” accounts matter more than you think, the risks of cutting corners, and simple ways to stay safe.
Two-Factor Might Be Hackable. USE IT ANYWAY!
Another scare about two-factor authentication being hackable? DO NOT let that stop you from using it.
Faking Reality: How AI Images Are Being Used to Scam You
Scammers take advantage of AI’s ability to create fake photos that look very real. From phony images of your car to completely made-up situations, it’s easier than ever to be fooled. Learn how they’re made, why they’re dangerous, and what you need to do to protect yourself.
Do I Need a New Email Address if Mine Is Involved in a Breach?
Was your email exposed in a data breach? Don’t rush to get a new address. I’ll discuss what really matters, like strong passwords, staying alert, and simple steps to keep your account secure.
How to Protect Your Cloud Storage and Backups from Ransomware
Do you worry that ransomware might lock up more than your files? It can. I’ll show you how to better protect your cloud storage and backups using tools like Macrium Reflect, OneDrive, and Dropbox. Even if malware strikes, you’ve got a way to recover.
Romance Scams: When Loneliness Makes Us Vulnerable
Loneliness can leave us vulnerable, and scammers know it. I’ll cover how romance scams work, the tactics scammers use to build trust and steal thousands, and the red flags to watch for, both for yourself and your loved ones. If you think it can’t happen to you, think again.
How Can an Employer Recover Information I’ve Erased?
Think clearing your browser or deleting files keeps your work computer activity private? Nope. I’ll walk you through the ways employers can recover or track what you’ve done, sometimes even after you’ve “erased” it, and why you should always assume they’re watching.
A Hacker’s Four Favorite Ways to Get You
A security professional shared the top four most successful hacks that compromise business accounts. I’ll walk through them and show how they all apply to you and me as well.
How Can I Tell If a Website Is Safe?
It’s important, yet sometimes hard to tell, if a website is safe. You can stack the odds in your favor. I’ll show you simple tools and smart habits to help spot shady sites before they cause trouble, even if there’s no way to always be 100% sure.
What Should I Do About the Latest Breach?
Yet. Another. Breach. Don’t panic, I’ll walk you through what you really need to do next. From checking if you’ve been exposed to strengthening your account security, it’s all here in simple terms.
How to Share Two-Factor With Another Person
Two factor authentication is one of the most important things you can set up to protect your accounts. Even so, it’s possible to share certain 2FA types with multiple authorized people. I’ll show you how I do it.
How to Run a Full Scan Using Windows Security
Here’s my step-by-step guide on how to run a complete malware scan using Windows 10 and 11’s built-in Windows Security.
Two-Factor Authentication: It’s Not as Complicated as You Think
There are some persistent myths about two-factor authentication that stop people from adopting it. I’ll clear them up so you can use this simple yet powerful security feature with confidence.
I Run Security Software. Why Do I Still Sometimes Get Infected?
Any security software can miss something, no matter how good. It’s important to understand why this is and what you can need to about it.
Size Matters! (When It Comes to Passwords)
The results are in for last year’s most common passwords. The implications are depressing.
Passkeys and Hardware Keys
Passkeys and hardware authentication keys are completely different but partially related. You can use some, but not all, hardware keys as passkeys. I’ll clear up the confusion, and tell you what to look for.
What Is a Passkey?
Passkeys are a new form of signing in that promise to be easier and more secure. I’ll walk you through some of the high level concepts and how they work, and how they keep you safer than passwords.
How Can I Securely Delete Everything Except the Operating System?
Before giving away a machine or returning a loaner, it’s important to remove your personal information from it. That may be both harder and easier than you think. I’ll show you where traditional suggestions fail, and what you need to do instead.
Is Internet Provided by My Landlord Safe?
Connectivity is becoming an added perk in some housing situations. Make sure you know the risks and alternatives when someone else provides your internet connection.
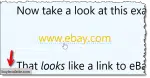
How to Hover Over a Link to Check It’s Not a Scam
When it comes to links on webpages and HTML email, what you see is not always where you go. Hovering over a link is an important technique to look before you leap.
How End-to-End Encryption Protects Your Messages and Where It Fails
You would think that for such an important concept as end-to-end encryption there’s be some agreement on exactly what it means. Sadly, not so. There’s the correct definition, and then there’s the marketing definition. One protects you, the other not so much.
Many Ways Your Account Can Be Hacked and What to Do About It
There are many ways accounts can be compromised. There are also many simple ways you can protect yourself.
Can You Really Know Your PC Is Clean and Malware-Free?
It’s common to want confirmation your machine hasn’t been compromised in some way. We can get close, but we can’t prove it.
Passkeys Are Never the Only Way In
Losing a device with a passkey to one of your accounts will not lock you out.
How Does Security Software Protect Me After Windows 10 End of Support?
Security updates and security software have different jobs, and that difference matters.
How Do I Know If My Hard Disk Is BitLocker-Encrypted?
Even running Windows Home edition, your hard drive might be BitLocker-encrypted without you realizing it. If you don’t have the recovery key, you could lose everything. Learn how to check, why it matters, and the simple steps to protect yourself before it’s too late.
Protecting Your Data: Why I Avoid Most Pre-Installed Security and Encryption Software
External hard drives often come with security and backup software. I’m not convinced it should be used.
BitLocker vs. Cryptomator: Why I Use Both (and When You Should, Too)
Use different tools for different purposes.
What Happens If I Lose My Microsoft Authenticator App?
Microsoft Authenticator is not necessarily two-factor authentication, but the two do share one important characteristic: the need to prepare for loss.
Does a VPN Protect Me From Telemetry and Other Data Gathering?
VPNs don’t impact data tracking or collection. We’ll look at why that is and what you might want to do about it.
Cryptomator vs VeraCrypt: Which Do You Want?
Cryptomator and VeraCrypt are both excellent encryption tools. We’ll look at how to choose the right one for your situation.
How to Back Up 1Password and Why You Should
Backing up is important, and that includes your password vault.
Should I Always Sign Out of My Online Account?
It is safe to stay signed in to your online account as long as you’re protected from a few specific scenarios.
Do Not Search for Support Phone Numbers
You want a phone number to call. Scammers known this and try to insert themselves in the process.
Think Before You Share: Protecting Yourself From Email Harassment
It’s so common to give away personal information, we don’t think twice about it. Let’s start thinking twice.
How to Recover When You Lose Everything Traveling
Imagine you’re traveling overseas and all your digital “stuff” is lost. What do you do? How do you reconnect?
Does Turning a Computer Off at Night Keep It Safer From Hackers?
There are reasons to turn your computer off at night or leave it running. Getting hacked isn’t one of them.
How Do I Make Sure Malware is Gone?
Of course we want to be certain malware has been removed. Unfortunately, certainty is difficult to come by.
More Tips to Protect Yourself from AI Scams
AI has entered the chat. And the email. And the voice call. And the video. And it’s making scams even harder to detect.
Online and Phone Scams: What to Watch For and How to Stay Safe
Know the characteristics of online and phone scams, and don’t be afraid to take steps to protect yourself.