Risks at every turn.

Privacy and security are more important, and under greater threat, than ever before. We manage an ever-increasing amount of sensitive information and tasks, while the number of ways our information can be exposed seems to be exploding.
It’s easy to overlook some of the common points your privacy can be compromised — accidentally or intentionally.
Let’s review them.

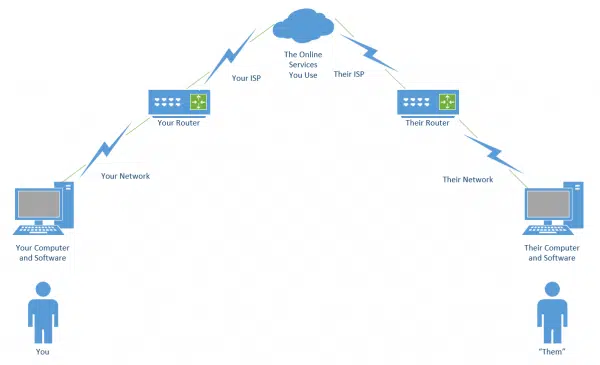
Points of possible privacy compromise
- Your computer, including software and hardware.
- Your network, which connects your computers to each other and to the internet.
- Your ISP, which wields more power than most realize.
- Your online services: are they competent? Do they protect the data they hold?
- Your friends and acquaintances: often the weakest link in the chain.
Let’s review each of these points of risk, exposing the technological hazards we (perhaps unknowingly) face every day.
1. Your computer
Privacy and security start at home (or in your pocket).
Software: operating system, applications, and malware
You trust that the right privacy and security decisions have been made for every piece of software you use. You also trust the vendors to have your best interests in mind.
This is true not only for your computers and mobile devices, but for an increasing number of network-connected devices, including televisions, cars, security cameras, and even baby monitors.
The operating system

When Windows 10 changed its approach to privacy, it became clear how much we rely on Microsoft for privacy and security. Many felt Microsoft had crossed a line, collecting excessive amounts of information in ways outside our control. Exactly what was being shared was unclear, and there were no trustworthy, easy-to-use solutions to avoid it.
While Microsoft added more privacy controls in subsequent versions, trust was irrevocably breached for many.
The most important takeaway is not about Microsoft’s trustworthiness; it’s that every operating-system vendor has the power to do or change any or all of this, with or without letting us know. The amount of trust you place in any OS vendor to manage your privacy and security is enormous.
Aside from being vigilant, managing the available privacy and security options, and paying attention to reliable, objective news sources, there’s little you can do other than switching to alternatives you consider more trustworthy.
Help keep it going by becoming a Patron.
Applications
Everything I’ve just said about operating systems applies to every piece of software running on your computer, phone, or other device.
You probably have dozens, if not hundreds, of apps and applications installed, from nearly as many vendors, and each has its own approach to privacy and security.
That’s a lot of trust spread across a lot of different companies. Besides trusting they’re competent at whatever you use their software for, you’re also assuming they’re competent at keeping your information safe and secure, and that they are not malicious themselves. You give them much more access to our information than you might realize.
The best defense here is twofold:
- Don’t install things you don’t need.
- Only install from reputable vendors.
Malware
When you think about privacy and security on your own computer, the first thing you probably think of is malware: malicious software that somehow makes it onto your computer to steal information or worse.
I’ve placed it last in the software category because by now, you probably understand malware and its concepts. More importantly, you know how to combat it. It’s something making the news almost every day. And while protecting yourself from malware is terribly important, it’s a topic you likely already understand.
You know how to combat malware. You know how to avoid malware. You know how to be skeptical. It’s something this industry talks about every day, so I won’t belabor the point.
Hardware: physical access and gadgets
“If it’s not physically secure, it’s not secure.”
It’s easy to overlook. If someone untrustworthy can touch your hardware, they can do damage to your privacy and security.
Physical access
If someone can walk up to your computer (or phone, or router, or other device) and start using it, that’s a privacy and security hole bigger than anything I’ve listed so far. If someone malicious has access to your device, they can do anything.
Theft is likely your first thought. The good news here is most thieves are unsophisticated. They’re just looking to turn the hardware around for some quick cash; they don’t care what you have stored on it. However, your data is accessible to them — or the person they sell it to — should they have a little technical expertise.
Your more common risks are closer to home: spouses, co-workers, children, and friends. Malicious or nosy, the people around you usually have easy incidental access to your stuff. It’s one thing to go snooping around your medicine cabinet, but something else entirely to poke around in your email, spreadsheets, or other personal data.
How much of a problem this is varies. You may not feel the need to take action, or you might consider a combination of encryption, software locks, and perhaps even hardware locks.
Hardware compromise
You can usually trust that your own hardware hasn’t been compromised.
That’s not a safe assumption when using public devices.
A good example is a hardware keylogger inserted between the computer and keyboard. Undetectable to any software on the machine and hidden behind the computer itself, it can passively collect massive amounts of information until the perpetrator comes along to pick it up.
While it’s significantly less common than other forms of compromise, hardware hacking can take many forms. It’s one reason you should never use a public computer for anything sensitive.
2. Your network: router, wireless connection, other devices
Much of the daily risk you encounter is because of being inter-connected, or networked. It’s also what enables so many of the features, functionality, and rich experience you enjoy with technology. Your network is how your computers connect to each other and to the world.
Router

Routers are powerful devices. They’re powerful computers. They’re usually based on general-purpose operating systems.
You’re trusting that the router vendor is competent and has factored in measures to protect your privacy and security.
Routers are interesting to hackers because by compromising a router, they can access all the devices connected to it.
Besides starting with a reputable device from a reputable vendor, the most important solution in your control is to secure your router. Every router comes with default settings that may or may not be the most secure for you.
Wireless connections
Your router often controls wireless connections, but they deserve additional attention. They’re a common point of compromise, particularly in public.
It’s possible to connect to your wireless access point, or listen in on wireless communications used by your devices, from distances further than you might realize. Particularly if someone is dedicated to the effort and trying to connect, it’s unwise to rely on distance alone for security.
The most important thing you can do in your home and business is to never have an open Wi-Fi hotspot; always use a WPA2 or WPA3 key or password for the connection.
The most important thing you can do when traveling is to know how to use an open Wi-Fi hotspot safely.
Other computers
Your router protects you from many internet-based threats. What if the threat is more local?
Computers and networks are often set up to give locally connected machines — machines on the same side of the router — a high level of trust. Sometimes that trust is unwarranted.
Consider your child’s computer. They may not have the sophistication to know not to download and run malware, which could then infect other machines. The same could be true of a visitor or even a less-than-tech-savvy spouse.
Solutions involve making sure your computer has its own defenses set properly, including its own firewall. Today, these are on by default for most devices. A further step is to segment your network into trusted and untrusted zones, using an additional router or a router providing this functionality natively.
Other devices
There’s been much made of the so-called “internet of things“, or IoT: the network of physical devices in your home embedded with sensors, software, and other technologies, from refrigerators to wearable health monitors.
It turns out neither privacy nor security were at the top of many IoT vendors’ feature lists.
The good news is that their negligence has mostly been limited to those devices becoming part of botnets used to cause havoc elsewhere. Other than using your internet bandwidth, little damage is done at home. Unfortunately, the potential still exists.
The bad news is that, aside from avoiding these devices completely, there’s not much in your control. Once again, you’re limited to using reviews and recommendations from information sources you trust.
3. Your ISP: at home, work, and in public
ISP: Internet Service Provider. Depending on where you live (or how you travel), you may have several options, or very few. Regardless of which you choose, you place a tremendous amount of faith in your ISP.
Home internet connection

Here’s the catch: your ISP can monitor your traffic. All of it. Unless you take additional steps, anything traveling over your ISP-provided connection can be examined — often in detail — or even recorded by the equipment operators.
Normally, it’s not much of an issue. Your ISP is too busy just keeping the lights on, so to speak, to pay attention to your emails or web browsing. Of greater concern are those situations when your ISP can be compelled to disclose your location and web usage by government demands or court orders.
If you’re an average computer user, you probably don’t need to be concerned. I’m not. But if you have reason for concern, then the steps you can take revolve around encrypting the data traveling between your computer and your ISP.
- https encrypts the connection between websites and your computer. Your ISP can still see you connected to https://askleo.com, for example, but they can’t see what it is you asked about or looked at.
- A VPN encrypts all traffic between your computer and the VPN service. Your ISP can perceive you’re connected to the VPN, but can see nothing else.
- TOR — The Onion Router — is a web proxy (most securely used with a dedicated TOR browser) that encrypts all your web activity and routes your traffic in such a way that the server to which you are connecting does not know who you are unless you explicitly tell them. Once again, your ISP can see that you’re using TOR; they just can’t see what you’re using it for.
The most overlooked aspect of this topic is the very literal nature of the term ISP.
Anyone who provides you with a connection to the internet is your ISP. Be it at home, in a hotel, at a coffee shop, or at work (which I’ll discuss next), anyone who provides you with an internet connection is your ISP.
Work internet connection
A separate set of rules apply when you’re at work. This means you need to consider several more aspects related to your privacy and security.
- If you use employer-provided equipment, everything I said about hardware compromise applies. It’s possible and possibly quite legal1 for an employer to install either hardware, software, or both to monitor your activities at any level of detail they wish.
- If you use employer-provided internet, then not only are they your ISP, with all the power that entails; they may be legally allowed to monitor your traffic, even using techniques to intercept encrypted https traffic.
- When you’re at your place of employment, even your private equipment may or may not be subject to your employer’s rules and abilities.
- Regardless of whether the company cares to monitor what you do or even compromises your security, you’re still required to abide by the companies’ rules.
The best advice I can give here is to clearly understand your workplace’s rules and capabilities and follow them to the letter. Then, depending on your level of trust, take care to isolate anything personal from their network, equipment, and possibly even facilities.
Coffee shops and public locations
Open Wi-Fi at coffee houses and elsewhere is rife with security and privacy issues. You likely already know what to do to stay safe using open Wi-Fi.
Those steps may not protect you from the owner of the coffee shop or other Wi-Fi provider. When using their internet, they are your ISP and may have all the abilities I mention above.
You might use a wired connection to avoid issues around wireless connections. Remember, though, the provider of that wired connection still has all the capabilities of an ISP and could compromise your privacy and security. In the worst case, they could be incompetent and expose your connection to other users, making it just as vulnerable as open Wi-Fi.
Remember to treat any internet connection from an unknown or untrusted source with skepticism.
Shared connections
One scenario I often hear is what I’ll call a “shared” connection. Sharing can take just about any form the name implies:
- Using (with or without permission) the internet connection belonging to a neighbor.
- Using the internet connection belonging to your host when visiting friends or family.
- Using the internet connection provided by a property owner.
- Etc.
Each of these situations, and many others like them, place the owner of the internet connection in the role of internet provider. They’re the ISP, and once again have all the associated capabilities.
4. Your online services: email, social media, storage, VPNs, professional services, account management
Online services from email to banking might be what you think of first when we talk about privacy. Given the regular news reports of breaches, it’s important to keep the services we use in mind.
But the topic is both deeper and wider than that. It’s easy to miss all the online services we use. It’s also easy to miss that these services are themselves subject to various laws and regulations that can further put our privacy and security at risk.
Email is unencrypted. Your email provider can read it all. Anyone with access to the servers between your email interface and your message’s destination can access it as it passes by.
The good news is that there’s so much email that you’d need to be pretty darn interesting for anyone to bother paying attention.
I’d love to provide a simple, easy solution, but I don’t have one. Encryption is key, but email encryption is a mess. There are techniques, but they’re cumbersome and not universally compatible.
Most important to your privacy and security is to be aware of the limitations of plain old email.
Social media
Overshare much? With social media — meaning services like Facebook, Twitter, Instagram, and others — you’re often your own worst enemy.
Not understanding the ramifications of social media visibility, you may share more than you should. This isn’t just about the pictures of the drunken party that come back to bite you when applying for a job; it runs a range from unexpected embarrassment to online harassment.
Social media providers have a wide variety of terms and conditions that allow them to do whatever they want with the information you post. Most aren’t interested in doing anything, but be it accidental or under legal pressure, providers have taken action that unexpectedly exposed more than users intended.
The key things to remember with social media are:
- You’re probably sharing more than you think.
- You’re probably sharing to more people than you think.
- Providers can be compelled to provide access logs and your postings to the authorities.
- There is no “undo” button. Once you post something, it’s stored somewhere, for much longer than you think.
Share wisely.
Storage
Cloud storage is awesome. It really is. As backing up is a theme I beat to death regularly, the additional options created by online storage are wonderful. There’s little excuse to lose more than a few minutes of work even in the worst of disasters.
With convenience comes privacy and security issues.
The biggest issue is that the storage provider necessarily has access to your data in order to provide the service. That exposes two risks:
- The provider (or employees) can peek at your stuff.
- The provider can be compelled to provide your stuff to the authorities.
One theme you might recognize here is the solution: encryption. For example, using a utility like BoxCryptor to encrypt the files you store online ensures that those files are accessible only to you.
Connectivity services
One solution for many types of network risk is a VPN, or Virtual Private Network.
It ensures your entire internet conversation, from your computer to the VPN service itself, is encrypted and hidden from prying eyes. It’s a solution often recommended for people who travel a lot who otherwise might need to make use of questionable internet services.
What most don’t realize, however, is that using a VPN simply replaces one set of risks with another.
In a way, the VPN service becomes your ISP. They provide a private, encrypted connection between you and their service. From that point on, your connection continues onto the public internet.
The VPN has provided your connection to the internet, and like any ISP, it implies they can see what you’re up to.
VPNs can slow your online experience down significantly, depending on the provider. It’s easy to focus on that when deciding which service to use.
More important is choosing a VPN service you can trust. You need to trust their technology, but also that they’re not accessing or collecting, or allowing others to access, your data. VPNs are often based in, or have a presence in, other countries, meaning they may be subject to the laws of countries other than your own.
Professional services
I find the financial sector frustrating.
While some understand privacy and security and manage it well, there are many who aren’t as on top of things as they should be. Everything from sending out legitimate mail that looks like spam to outdated password requirements, much of the industry is still playing “catch up” compared to others.
My feeling is that it is no coincidence that many of the hacks we hear about are in financial services.3
Fortunately, your money is generally protected in the banking world. However, with other professional services, such as online bookkeeping, bill paying, financial reporting, and more, things are more haphazard.
When choosing an online professional service, or whether to use one provided by your bank or someone else, I’d recommend looking for a few things:
- The ability to use arbitrary length password, including spaces.
- The availability of two-factor authentication.
- Telephone support that gets you to real people who speak your native language.
- The availability of real-time transaction alerts when applicable.
- And of course, https, and only https, on every related website and page.
You can use online services can safely; I do it myself regularly. But more than anywhere else, privacy and security is a partnership between a service knowing what it’s doing and you making appropriate security-related choices.
Account management
Once again, you may be your own worst enemy.
In my experience, most incidents of account hacking, theft, and loss are completely preventable. I see people making mistakes every day that eventually lead to account compromise. The service involved isn’t at fault, and the hackers are simply taking advantage of those mistakes.
Privacy and security are your responsibility. You may feel like it’s someone else’s — the service, the software, or the coffee shop — but you choose which services, software, and coffee shops to use, and you choose whether to use them securely.
I see too many people neglecting the basics of safe account management.
Make sure you follow these basic steps:
- Choose appropriate passwords.
- Manage passwords appropriately to keep them private.
- Set up account recovery information and don’t let it expire.
- Use two-factor authentication whenever offered.
5. Your friends and acquaintances
One of the odder questions I get is whether it’s possible to intercept and record video chats. The short answer is, as long as you’re using a reputable service, it’s highly unlikely.

The person at the other end can be one of your greatest risks.
I’m not saying they have malicious intent. But when you communicate with someone, your information is flowing across their network and devices as well as your own. Ultimately, you’re assuming the other person is not being spied on and knows how to keep their system and environment secure.
You’re also trusting they don’t have malicious intent. They can share everything we send with whomever they please, including the entire world.
Do this
At this point, you may feel overwhelmed and disheartened. It’s easy to be annoyed that the digital world isn’t a safer place.
Personally, I feel the privilege of playing and working on the internet, and the multitude of opportunities it presents, makes it worth staying on top of what I need to do to use it safely.
All that really means for you is learning who to trust and taking the steps I’ve outlined to keep your identity, reputation, data, and devices protected.
For more ongoing help staying safe online, subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: Caveat: I’m no lawyer, and this is in no way legal advice. Since laws vary dramatically around the world, consult an appropriate attorney for any advice relating to your specific situation and location.
2: Or will when they enter the workforce.
3: In addition to banks being “where the money is”, of course.






I kinda look at having my VPN in another country a security advantage.
Leo says: “While it’s significantly less common than other forms of compromise, hardware hacking can take many forms. It’s one reason I never use a public computer for anything remotely sensitive.”
Unfortunately any time you are accessing an account using a Username and Password you are using it for something sensitive. Your email account is one very sensitive possession. It’s a life line, and in addition to the sensitive information it holds, it can be a way of gaining access to other accounts. The problem is that people who don’t have their own internet access rely on public access internet in libraries or internet cafes. In cases like that, I’d rely on my smart phone, tablet or portable computer and use the free Wi-Fi provided by the library or coffee shop. Most email websites or IMAP access use SSL (https in browsers) and the interaction between you and the email service provider is encrypted end-to-end. Check if any website you are going to which requires a login uses httpS.
One way to mitigate this issue is to use two factor authentication (2FA).
Another thing to watch out for. A few years back I was checking my email at a public library (I know, this goes against what I mentioned in my previous comment, but sometimes it’s unavoidable). While I was logged in and looking at my email, my internet session ran out. I asked the attendant at the desk if that would log me out of my email account. He said no and let me log on long enough to log out of my email account. So watch out for your time on line, and if you are automatically logged of the internet, ask them to let you get back on so you can log off from your email (or other logged in) account. And change your email password as soon as you can.
Your section on hardware security really hit home. After 911, someone used my work computer to send a Talaban joke to 20 managers of the company. I could not prove that I didn’t do it and I was suspended then fired – although I apologized to all of them and explained that I didn’t do it. At subsequent jobs, I never left my desk without password protecting or shutting down my computer.
A big THANK YOU for this article. What a treasure trove of information all in one place. This article should be required reading for all PC users.
Mark Jacobs comments about email being sensitive is dead on. Too many people treat email and access to their email in a frivolous or cavalier manner. One of my banks will send a new password to me via email. (That bank has some problems, but that is another story). If you lose access to an email account, frequently you can another email account to re-gain access to the first email account. I treat all my email accounts seriously.
Excellent article. I am thinking about a VPN. This article has helped me make my decision. And the name and email boxes auto fill! =(8^O
I can’t thank you enough for this detailed, comprehensive and insightful article. I have been trying to follow security best practices for many years now, but no matter how hard I try, I cannot seem to keep ahead of the hackers. I am also hindered by my family who gaslight and accuse me of being paranoid because I use a VPN, set up a guest network, change wifi passwords every 60 – 90 days, etc. My sons and SO do not fully understand or refuse to acknowledge the risks posed by the security flaws in our current technology. I hope you will keep exposing the risks and solutions as you have done here so eventially the naysayers will get on board the cybersecurity individual responsibility train before they experience a breach.
Thank you for this detailed and comprehensive review. I doget annoyed that the technology isn’t put through more rigorous security testing before it is released to fix vunerabilities. I feel that no matter how hard I try to keep on top of security, the neighborhood hackers are always ahead of me. Also friends and family have little appreciation for security efforts like 90 day password changes and keeping wifi passwords secure. Articles like this one are a boost in reinforcing that I am doing the right thing.
Regular password changes don’t add any significant security other than the case when a website is hacked, but the change would have to coincide with a hack on that website. It’s better to stay on top of tech news and change your password as soon as you hear of a hack. It’s more important to have long, strong, random passwords (14-20 characters long). LastPass and other passwords generators do a great job.
Here’s a recent Ask Leo! article on passwords:
Your 6 Strongest Practical Password Techniques, Ranked