One of the hidden issues in online storage is privacy. Almost all online storage providers have the ability to examine your data or hand it over to law enforcement even if the provider has encrypted your data.
Hopefully, most of us will never have to deal with the law-enforcement scenario, but even the realization that a rogue employee at an online data storage provider could peek into what we keep online can cause concern. For some, it’s enough concern to avoid using cloud storage at all.
The solution is simple: encrypt the data yourself.
Unfortunately, implementing that “simple” solution isn’t always that simple or transparent, and can add a layer of complexity to online storage some find intimidating.
BoxCryptor is a nicely unobtrusive encryption solution that is free for personal use.
The hidden issue
Online1 storage is powerful when used properly. By “properly”, I mean the account is set up with appropriate security, and the data you place online is backed up somewhere else as well. Ignoring either of those items can lead to permanent data loss.
Even with those basics covered, a potential privacy issue remains. Unless you take additional steps of your own, the provider of that online service has the ability to view your data.
- Your data may not be encrypted, and is stored in view of anyone with administrative access to the service provider’s servers.
- Your data may be encrypted by the service provider, but since it’s encrypted by the service provider, it can also be decrypted by the service provider. As a result, those with administrative access still have access to your data.
In reality, the folks at major online storage providers are professionals who have no interest in snooping around in your data. Instances of the so-called “rogue employee” are rare. But, of course, it’s still possible.
More legitimately, the service provider may be required to turn over your unencrypted data to law enforcement should appropriate court orders be presented.2
For whatever reason, you might consider all of this a problem. Fortunately, this problem has a solution: encryption.
The hidden cost of doing your own encryption
There’s at least one good reason to allow your online storage provider the ability to decrypt your data: web access.
Some online storage providers encrypt your data when it’s stored on their servers. However, whether or not they do they must be able to decrypt it to provide you the ability to access the data via a web interface. For example, even though Dropbox encrypts your data on their servers, it also allows you to log in to your account from any machine and access the files stored in your account via the web.
If you encrypt the data yourself using BoxCryptor, the online storage provider can only access your data in its encrypted form. You’ll need BoxCryptor (and of course, your password) on every device to decrypt it before you’ll be able to use that data.
Traditional encryption solutions
The idea here is that if you encrypt your data before it gets uploaded to any online storage provider, they have no ability to decrypt it. You, and only you3, control the access to your data.
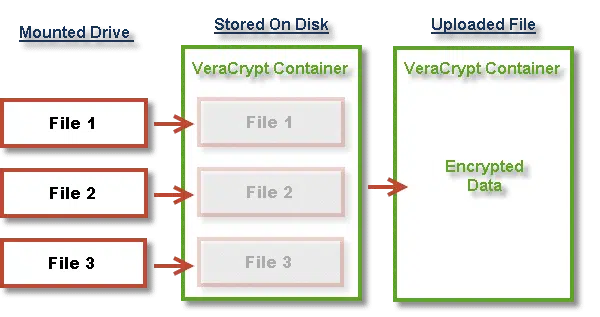
Traditionally, it works this way:
- You have a file or set of files you want to store online.
- You use a program such as 7-zip, VeraCrypt, or similar to create a new file or files containing encrypted versions of the files.
- You place those encrypted files into online storage.
Now, when you want to use those files on any machine that doesn’t hold the originals, or want to make sure you have the most current copy, you need to:
- Retrieve the encrypted files from online storage.
- Decrypt the files.
- Make your changes.
Then, finally, to update the online copies of the files (if you made any changes), you would:
- Re-encrypt the files as you did originally.
- Upload the encrypted file or files into online storage.
As you can see, that’s a lot of work just to update, for example, a single file.
That’s where BoxCryptor comes in.
The BoxCryptor model
In a sense, BoxCryptor operates similarly to programs like VeraCrypt.
To use VeraCrypt, you create a special container and tell VeraCrypt to mount that container as a virtual drive, supplying the correct passphrase to do so. A new drive appears on your system — say drive T: — and the contents of the encrypted container appear as unencrypted files. As long as the container is mounted, the contents of the “vault” are directly accessible to any and all programs running on your machine. Dismount or fail to mount the container, and all that’s visible is the vault file itself, which appears to contain random noise.
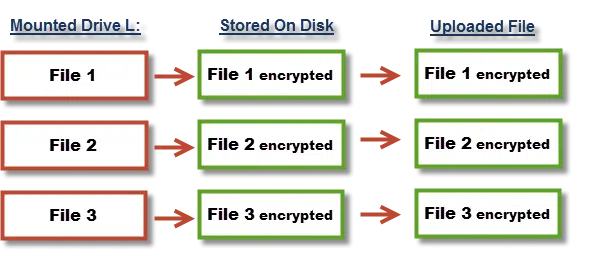
BoxCryptor works similarly, except that the container is nothing more than a source folder: any other folder on your machine. You mount that folder in BoxCryptor, and another drive — I’ll call it L: — appears on your machine. Anything written to drive L: is encrypted and written to the folder you specified when mounting. Anything read from that drive causes the corresponding encrypted file in the source folder to be read and decrypted on the fly.
While technically slightly inaccurate, you can think of BoxCryptor as operating like VeraCrypt, but at the encrypted file, rather than encrypted container, level.
The files in the original source folder are always encrypted. It’s only when the folder is mounted in BoxCryptor that the files are visible in their decrypted form in the virtual drive.
An example of BoxCryptor in use
Let’s say I use Dropbox. On my machine, I have a folder:
C:\My Dropbox
In that folder, I have many other files and folders that automatically synchronize with the Dropbox servers and any other machines on which I have Dropbox installed.
One of the folders in my Dropbox folder is:
C:\My Dropbox\Boxcryptor Files
I don’t place any files in the Boxcryptor Files folder directly. It starts out empty.
Next, I install BoxCryptor, and configure it to mount “C:\My Dropbox\Boxcryptor Files” as drive L:. I set up the password required to mount it again in the future.
Drive L: appears on my machine.
I create a Word document on drive L:
L:\MyPrivateInformation.docx
As soon as I save that document to drive L:, a new file appears on C::
C:\My Dropbox\Boxcryptor Files\MyPrivateInformation.docx
The file that was saved to L: is automatically encrypted and placed in the BoxCryptor folder. Dropbox then notices a new file has appeared, and the encrypted file is also uploaded and distributed to all my machines running Dropbox. Note that only the encrypted version of the file has been uploaded.
I can continue to work on the file on L: to my heart’s content. It’s just a file, and can be manipulated like any other. As changes are saved to disk, the corresponding encrypted version of the file is updated.
Once I dismount the BoxCryptor folder, drive L: — along with the unencrypted versions of the file — disappears. All that remains are the encrypted versions stored in the BoxCryptor folder within the Dropbox folder.
All that has been uploaded to my online storage provider are the encrypted versions of my files.
VeraCrypt or BoxCryptor?
There’s a reasonable argument that you can use BoxCryptor for almost anything you might use a standard VeraCrypt vault for.
The practical differences boil down to this:
Monolithic versus incremental update: the biggest drawback to using VeraCrypt with a service such as Dropbox is that it’s a single file. Any changes to any of the files contained within it means that the entire file is considered changed and must be uploaded or downloaded. BoxCryptor maintains individual files as individual files; only files actually modified need updating.
Open- versus closed-source: VeraCrypt is an open-source project4, and its source code can be examined and audited. BoxCryptor is a commercial product by a German company, so using BoxCryptor requires that you implicitly trust this company.
VeraCrypt is free no matter what you do with it. While BoxCryptor’s base version is free, there are licensing levels for additional features that may be important, as well as for commercial use (more on that below).
In short, BoxCryptor is an excellent solution for encrypting files that are going to be placed in online storage management utilities such as DropBox. In my opinion, VeraCrypt, or Windows own encryption, Bitlocker, remain better choices for encrypting offline data or entire hard drives.
It’s for more than PCs
Like many online services similar to Dropbox, BoxCryptor supports multiple platforms.
BoxCryptor is available for:
- Windows
- Mac
- Android
- iPad & iPhone
That means you can continue to share your documents across all the platforms and devices supported by your online storage provider, but now you can easily encrypt the data you share.
Help keep it going by becoming a Patron.
It’s free for personal use, but…
I recommend you spring for a BoxCryptor personal license.
Besides better support, it includes a feature I suspect many people might want: filename encryption.
As you saw above, my example document:
L:\MyPrivateInformation.docx
was saved as:
C:\My Dropbox\Boxcryptor Files\MyPrivateInformation.docx
In other words, the name of the file remains visible.
For many, that might not be a problem, but for others, names of files (and folders) represent an unexpected way sensitive information can leak, even if the contents of those documents are encrypted.
When you purchase the “Unlimited Personal” license, file names are instead stored encrypted. For example, my example document might appear as:
C:\My Dropbox\Boxcryptor Files\怐栶旵樍椌憲歃晗怐栶旵樍椌憲歃晗
— where the Chinese characters above represent the encrypted filename. Only when successfully mounted do the file names once again appear unencrypted (on drive L:, to continue the example above).
How I use BoxCryptor
As I update this, I’ve been using BoxCryptor for many years.
Much like the example above, I have a Dropbox folder dedicated to the files I wish BoxCryptor to store encrypted. I have BoxCryptor installed on my Windows PCs, as well as my Macs and my Android phone.
Using BoxCryptor allows me to feel secure leveraging online storage and using it for even more things — things I wouldn’t necessarily place into a large monolithic VeraCrypt container, but still hesitate to upload unencrypted.
BoxCryptor is a convenient solution for making sure the data you place in online storage services remains secure, and is accessible only by you.
I recommend it.
Podcast: Download (Duration: 12:40 — 5.9MB)
Subscribe: RSS


Here’s how I use Boxcryptor.
I have my data encrypted in a Truecrypt Volume to keep it secure if the computer is stolen.
I use Carbonite to continually backup the files in Truecrypt. As Leo says, these are now unencrypted.
I’m not worried about my data being visible by Carbonite – I have a certain amount of trust. That does NOT extend to more sensitive data. For this I use Boxcryptor. For instance, I use Lastpass and export the passwords for safe-keeping to my boxcryptor mounted volume. This is necessary because the exported passwords are ‘in the clear’.
So, my recommendation:
Truecrypt, Lastpass AND Boxcryptor.
Although I have a TrueCrypt volume in Dropbox, I can’t imagine why I would keep my passwords in it, when they’re encrypted by KeePass (and stored in Dropbox).
Of course, if I did ever export them from KeePass, I would store them in the TruCrypt volume.
But I’m very interested to hear of BoxCryptor.
Hi!
This is my first post and I just want to say that I’ve never tested BoxCryptor but I will very soon (as soon as I finish this message) 🙂 Just to share with you how I use TrueCrypt and Dropbox.
First I created a TrueCrypt file with the same size of my Dropbox and had it as my favorite on TrueCrypt (drive w:).
In second place, I told Dropbox to use all my drive w: as its location.
Finally, another TrueCrypt file inside the drive w: (drive z: in my case) where I write all the info I want to protect.
This way I only need to know one password and I’m protected from the curiosity of any employee and/or someone at the office 🙂
I have a very simple question.
Exactly how do you mount and dismount a volume step by step?
I re-read your true crypt column but I still don’t understand it.
Why use DropBox (which isn’t secure) and BoxCryptor when you can just use SpiderOak and get the benefit of both without the hassle?
25-Aug-2012
A useful article. I’ve been using Dropbox and TrueCrypt for some time and, as described, it is something I use for particularly sensitive files. BoxCryptor is new to me and sounds ideal for more general privacy concerns. I plan to take a good look at it. Many thanks for bring this to readers’ attention.
excellent article AND it explains the pros and cons of cloud encryption quite wel.. Thank you.
@Vaidya
Yes. That’s the whole idea of BoxCrypt. Just run the program, mount the drive and copy/cut and paste to the BoxCrypt folder. One thing though. If your data is sensitive, it’s better to copy and paste and then do a secure wipe of the original file. If the file is simply moved, it can still be recovered.
Is deleting a file and emptying my recycle bin enough?
Mark says: “If your data is sensitive, it’s better to copy and paste and then do a secure wipe of the original file.”
THIS IS IMPORTANT. One thing I just learned from the Boxcryptor staff is that when using BC to encrypt an already-existing file, it DOES NOT securely delete (i.e., “shred”) the original unencrypted file. It deletes the original file, but not securely. I consider this to be a huge security flaw. It can be worked around by using a secure file recovery and deletion tool like “Recuva” (which is recommended by Leo but which I have not tried yet myself) to erase your original unencrypted files, but I’m disappointed that a two-step process using a separate third-party application is required to properly encrypt a file using Boxcryptor.
Does anyone know of a good, single file-encryptor for use on the local computer? One where you (for instance) merely right-click on a given file (including a binary file), select “Encrypt” from the resulting menu, enter a passphrase in a pop-up dialog, and get an encrypted version of the file in AES256 or Twofish right there and then (and optionally with the original securely wiped)?
Preferably usable equally on WinXP Pro SP3 32-bit and Win7 (Home Premium, or Pro) 64-bit…?
@Glenn
Here’s a recent Ask Leo! article on file encryption: How do I encrypt a file? For single file encryption Leo recommends AxCrypt.
I’ve tried BoxCryptor before. One important issue that I think is relevant to point out is that with file name encryption, encrypted versions of file names are often considerably longer than unencrypted names. Add to this the fact that some cloud storage providers limit the size of file paths to 256 characters and suddenly you can no longer store deeply nested files.
(Note: I switched my cloud storage provider many times in the past. When I tried BoxCryptor, I was using Microsoft SkyDrive; this may not apply to other providers, but as I understand, the issue is/was present among several of them.)
Interesting. I can confirm it works well with both DropBox and Bittorrent Sync. 🙂
I tried the newer version of BoxCryptor, but I found that the classic version is exactly what I want for my needs. The newer version seems to be a bit too complicated to use.
Hi Leo,
What about Mega?
It encrypts files locally and it’s a zero-knowledge hosting service.
However, encryption is done by javascript directly in your browser.
Also, I think you can inspect the code so you can be sure there is no backdoor which is, tell me if I’m wrong, better than relying on a closed source service like boxcryptor or SpiderOak (the last one recommended by E. Snowden itself!).
Best of all, you start with a 50GB plan FOR FREE.
This is probably too easy, but how do you appropriately back up this file?
Do I store the unencrypted files on my computer? Do I store the files on
a second online data storage provider? Is there an easier way?
If you use BoxCryptor, the files are encrypted on your computer. Whether you keep an unencrypted version on your computer is something you can optionally do if you want by simply copying those files from the mounted BoxCryptor drive to a folder on your computer. That’s not a common practice as it defeats the whole purpose of encryption. Most people don’t want those files to live on there computer unencrypted.
As for backup, you can copy the BoxCryptor folder to another drive and mount it from the the new location to decrypt the files. One caveat with the free version is: you’ll have to remove the original BoxCryptor folder from BoxCryptor before adding the backup folder because the free BoxCryptor can only work with one volume at a time.
I’m not sure what you’re asking.
I backup the unencrypted contents of my BoxCryptor files in a different, secure, location that’s off line.
Boxcryptor Classic encrypted files can be decrypted and encrypted by encfs under Linux. In fact, Boxcryptor seems to use the encfs encryption engine. Encfs is free and open source. Note that it only works with Boxcryptor Classic.
Why use Dropbox when great apps like Spideroak exist? Spideroak encrypts all files with zero-knowledge for the company; meaning there is no way for the company to access or view your files at any time – period!
I believe Leo answered that question above. (25 Aug. 2012)
If you want to encrypt your files names, you can either choose non-descriptive names for the files (ie file1.docx) or zip the folders which contain those files. If you try to view the filenames in the zipped file in C:\My Dropbox\Boxcryptor Files\my_files.zip they will be unreadable.
Leo says “Once I dismount the BoxCryptor folder, drive L: – along with the unencrypted versions of the files – disappears. All that remains are the encrypted versions stored in the BoxCryptor folder within the Dropbox folder.”
Unfortunately, that’s not true, at least as it applies to encrypting previously-existing files. Yes, if you create a NEW file within the Boxcryptor drive (as Leo did in his example), it will be encrypted when saved and no “clear” version will exist on your computer. But if you use Boxcryptor to encrypt an already-existing file on our computer, it will “delete” that original unencrypted file but NOT securely. You will have to use a secure file recovery and deletion tool like “Recuva” (which is recommended by Leo but which I have not tried yet myself) to erase your original unencrypted files.
This is a disappointing shortcoming of Boxcryptor. You have to use a two-step process using a separate third-party application to properly and securely encrypt an already-existing file using Boxcryptor. I suppose that because Boxcryptor is designed to be used with cloud services like DropBox, the makers of BC didn’t think it was necessary to securely delete the files on the user’s own computer after encrypting them. But of course that leaves the sensitive data on the computer vulnerable to anyone with physical access to the computer.
That’s a good thing to keep in mind.
To wipe the files you can run the Drive Wiper Tool in CCleaner (from the same company as Recuva) with it set to wipe “free space only” to automatically wipe all the contents of your free space.
http://ask-leo.com/ccleaner_windows_cleaning_tool.html
Very good, yes…..the only problem with using that tool is if you have a large hard drive with a lot of free space (as I do — currently 744 GB!), then it will take a long time to wipe all that free space. And in my case, the vast majority of that free space is “virgin” — never written to at all, ever. That’s why I mentioned Recuva, which can wipe just the deleted files that it finds and save a lot of time (at least in my situation’).
FYI, I’ve been using very large (50 GB) Truecrypt files as space fillers to fill up the empty space on my drives. This allows me to wipe the free space in less time. When I need more space I delete a space filler.
How secure is 7-Zip encryption compared to TrueCrypt or VeraCrypt ? I have always worked under the assumption that it was a lightweight method, not to be trusted against persistent adversaries. If not, why even bother with TrueCrypt or VeraCrypt for file encryption ?
My understanding is that 7-Zip is quite secure. Quoting their site: “Strong AES-256 encryption in 7z and ZIP formats”. That works for me. As for why or why not 7-zip versus VeraCrypt: depends on how you want to use it. Rather than having to build and maintain an archive file, some find it easier to just mount a vault and play with the contents as needed directly.
Just curious, what happens if someone breaks into your cloud account and deletes the boxcrypt folder? Does that affect the boxcrypt virtual drive on your machine?
If Dropbox is running on your computer, the files would be deleted from the computer. However, Dropbox maintains a copy of the deleted files in its trash folder for 30 days. But if you’ve been paying attention to what Leo has been saying over and over on Ask Leo! you would have an image backup or two to fall back on. You should always have a few backups in various locations.
Depends on the cloud account. Remember … they’re just files. If your cloud account (DropBox, OneDrive, whatever) would replicate those changes, then indeed, they’re replicate down to your PCs as well.
I too am a fan of BoxCryptor. I’ve been using it for quite some time and it works great. I feel comfortable knowing my cloud data is encrypted and, yes, I do access it from multiple computers. Enjoyed the article.
Since Leo originally published this article he wrote another article recommending a software title called Cryptomator that I use and with which I am very happy. It works just like Boxcryptor with the notable exception that it gives all files and folders random names without having to purchase a premium package. Thank you Leo for that heads up!
I actually need to update my article for Cryptomator … it’s caused some folks problems. I had it randomly disconnecting the mounted drive on my Mac, which turned out to be an annoyance. That’s actually what caused me to re-visit BoxCryptor. I still love Cryptomator, and I want it to succeed as well, but right now … be careful. 🙂
Hmmmm….that’s not been my experience at all. Then again, all of my devices are Win 10 so maybe what you’re describing is an Apple thing. Also, when I’m finished editing files that are Cryptomator protected, I lock the vault. Then again, I’ve walked away from my computer and left my Cryptomator vault unlocked for many hours at no detriment to me. Go figure.
I have used VeraCript before but when I uploaded the files to my One Drive account One Drive would not back them up even though it has no problems backing up my other files. I’m guessing One Drive has a rule about not backing up encrypted data? If I wanted to use cloud storage, encrypt the data, and have the cloud storage backup my files unlike One Drive what cloud service and encryption software should I use?
Thanks for the help.
This is a different John then the John who posted previously. I’ll change my name to John G.
There’s no rule about not backing up encrypted data — you can back up whatever you like. Why veracrypt failed depends on EXACTLY what you were trying to back up and how.
As for what to use … that’s EXACTLY what the article you just commented on is all about. 🙂
It might have had something to do with the file size as OneDrive can’t recognize that a file is encrypted. OneDrive used to have a file size limit which they removed but if a file is very large, it just might still be in the process of uploading. That’s why BoxCryptor or Cryptomator are the way to go for encrypting files in the cloud. And as Leo mentioned in this article, if you change even one tiny file in your Veracrypt container, the whole container needs to be uploaded again and downloaded to any other computers synced to that account.
Great article and useful discussion!
The Boxcrypter site and help manual also look very professional and comprehensive covering a range of user & group / corporate scenarios. The technical overview page looks like it will pass the Steve Gibson “Trust No One” test.
This might be a bit off-topic, but I’d be interested in hearing what types of documents and information Leo and followers regard as being sensitive and that should be encrypted (outside of the special cases where you are plotting the downfall of your spouse / neighbour / colleague / boss / company / state / world)?
Utility statements
Bank statements
Tax records
Brokerage accounts
Other financial documents
Medical records
Travel documents
Family photos
What is sensitive is purely a personal decision. I encrypt password lists, financial and medical information and not much else. You also encrypt family photos which are important for you to have protected. I don’t have a need to encrypt those but I’m sure you have good reasons so there’s no way to give a list which would apply to other users.
Hi,
I own several websites and my pc contains documents, ebooks, images, videos and things like that. I don’t mind anyone seeing these files. I don’t have any passwords, or sensitive information on my Pc (other than perhaps my id/car license card). My passwords are in Lastpass, I don’t have a backup copy on my pc.
I backup everything to external drive, DVD’s and online storage, what’s the point to encrypt my files?
Thanks
I have Boxcryptor on my phone, and it has my files in it.
When I download an app on my phone, like OneDrive, or any other, and it says:
“Allow to access photos, media, and files on your device?”
And I click yes in order to download the app, does that allow them to have access to the files in Boxcryptor?
Thank you for all that you do,
John.
I believe so, yes. But the files are only accessible unencrypted through BoxCryptor. Any other app would see only the encrypted data.
[ My comments below sound like I represent ‘Sync’. Not so. Just a non-heavyweight satisfied Sync customer, passing along two cents. ]
‘Sync’ (sync.com) is a piece of my backup regimen. Quoting: ‘Sync desktop and mobile apps support file level de-duplication, which means that the apps will not re-upload identical files that have been previously uploaded to your account, even when renamed or moved’.
A single Sync subscription covers multiple Desktop and Mobile device, and it supports macOS, Windows, Linux (as I recall), iOS/iPadOS, and Android, etc.
Sync’s ‘Help’ is well-presented, crisp, and necessary to take full advantage. I am -amazed- with the product’s many provisions and ease-of-use. I have used/tried several aggregator and cloud services over the years. Overall, ‘Sync’ is by far the best for me.
‘Sync’ (located in Toronto) offers a demo/free trial.
For anyone interested, highly recommend checking out:
https://www.sync.com/pricing/#features
https://www.sync.com/help/
Just curious if as of 2021, Boxcryptor is still your tool of choice. 🙂
It is. I use it every day.
How do I dismount Boxcryptor?
Right click on its icon in the notification area and hit “exit” is the quickest. In settings you can also dismount individual volumes if you have more than one.
Yes, that works, (thanks for the reply!)
Clicking on its icon then remounts it. But it doesn’t ask for a password.
So it does not protect the data on the machine, only in the cloud. I suppose that is the main purpose of installing BoxCryptor, but from your description above it sounded like it should ask for a password when being remounted.
Is there a setting I should change?
Yep. In Settings, in Security, check either Password Proteection or PIN Protection.
Poking around the settings for any app you have installed is always a good idea and can lead to many answers a lot more quickly.
Using Boxcryptor, can I encrypt my entire Windows10 ‘Documents’ (system) folder for automatic storage in OneDrive?
Yes, I do that.
Putting Documents in OneDrive is a separte step. But yes, you can use BoxCryptor to encrypt whatever you have in OneDrive.
If I use BoxCryptor to encrypt a folder, and then decide I don’t like BoxCryptor, can I decrypt the folder to get back to the original state? Thanks.
Yes. If nothing else you can copy the contents to a new un-encrypted folder, remove boxcryptor, and then move everything back to where it was. But there are also easier ways.
Thank you. I’ll give it a go…