Articles in Category: Email
Email – the most used, most long lived communications medium offered by networks of interconnected computers.
How Do I Report Spam to the Originating ISP?
Want to report spam to the ISP it came from? These days, spam comes from massive networks of hacked computers, not a single traceable server. I’ll explain why reporting spam to what you think is the source of that spam is mostly a waste of time.
What Is “Mailer-Daemon” and Why Is It Sending Me Email?
Get an email “from” mailer-daemon? There’s a good reason this mysterious sender keeps showing up.
Why Can’t I Change My Email Address at Some Online Providers?
Your email address changed, but the website where you have an account won’t let you update it. Now what?
How Do I Change My Email Address?
Changing an email address changes a lot more than the address. I’ll look at common scenarios and a few additional approaches.
How Do I Deal With Getting Someone Else’s Email?
You didn’t ask for it, but there it is: email meant for someone else in your inbox. I’ll discuss why this happens and what you can do about it.
What’s the Difference Between Outlook, Outlook, and Outlook.com?
Microsoft continues to confuse us with repetitive product names. I’ll clarify the difference between Outlook, Outlook, and Outlook.com, and help you decide which you want.
Are Deleted Emails Really Deleted?
Deleted an email and think it’s gone forever? I’ll explain what “delete” really means in webmail and desktop programs, why trash folders and database files can leave messages recoverable, how backups and even court orders can bring them back, and the inconvenient fact that the other person may still have a copy.
Why Am I Being Asked for Additional Verification on Sign-in?
Traveling and suddenly locked out of Outlook.com? I’ll explain why Microsoft asks for extra sign-in proof, what “something unusual” really means, and how to set up backup email, phone, or authenticator options before you leave so you can get your code and your account back when it matters most.
Is It Safe to Look, Just Look, at Spam?
Curious about what’s hiding in your spam folder, but worried a single click could infect your computer? I’ll explain the simple rules that keep you protected and how to view raw message source safely.
How Long Does Email Delivery Take?
Email is typically very fast, but sometimes it can take hours or even days. I’ll explain why delays might happen, what spam filters and busy servers really do, and how long mail servers keep trying before they give up.
Three Ways Spammers Can Tell If You’ve Opened One of Their Emails
I’ll share three simple ways spammers know you’ve read their email, and how you can avoid more spam in the future.
The For-Pay Email Providers I Recommend
People often use free email providers only to lose everything when a problem occurs. So what should you look for in a paid email provider?
How Do I Route My Email Through Gmail?
Google quietly removed the Gmail feature that let you pull all your email into one inbox. If you relied on Gmail as your central hub, it’s time to rethink your setup. Here’s what no longer works and the options that still do.
Find Your Microsoft Account Recovery Email
Your Microsoft account recovery email address is an important part of making sure you never lose access to your account.
How Do Spam Filters Work?
Spam filters can be sophisticated or simple. I’ll look at some of the characteristics of email that spam filters check.
Six Signs of a Phishing Attack
A friend received a fairly convincing phishing attempt. I’ll cover the signs that showed it was spam.
What to Do When Your Outlook.com Storage Is Full
Microsoft changed the free storage allocation for Outlook.com and OneDrive.
The Wrong Way to Change Your Email Address
Emailing your entire contact list with a notice that you’ve changed your email address is NOT the way to change your email address. I’ll show you what to do instead.
How to Back Up Outlook.com Email
Outlook.com accounts are hacked into and lost every day. Here’s how to ensure you won’t lose email or contacts if it happens to you.
“From” Spoofing: How Spammers Send Email That Looks Like It Came From You
Ever get an email from yourself that you didn’t send? You’ve likely been spoofed. I’ll show how spammers fake your address without touching your account at all, why it happens, and what (little) you can do about it.
How Do I Send an Email to Many People?
Want to email a big group without looking like a spammer or getting blocked? I’ll show you why the usual tricks don’t work well and walk you through safer, smarter ways to send group emails, from simple groups to full newsletter services.
Gmail Is Removing “Check Mail From Other Accounts”
Gmail is taking away the handy “Check mail from other accounts” feature in 2026. If you use it to manage multiple email accounts in one place (Gmail), you’ll need an alternative approach. I’ll cover what’s changing, why it matters, and the options you have left before your mail disappears.
Replying to Spammers to Tell Them to Stop
Tempted to hit “reply” and tell spammers to knock it off? Don’t. Here’s why replying makes things worse, and what you can do to keep spam under control.
Why Am I Being Labeled a Spammer?
Possibly being labeled a spammer is another reason not to forward political and other emails. Do it enough, and your normal email may not get delivered.
What’s the Difference Between an Email Account, an Email Address, an Email Program, and an Email Service?
What’s the difference between your email service, account, address, and program? I’ll break it down so you’ll know what each term means, why it matters, and how not to get tripped up next time you want to change your email or ask a question.
Can I Tell If Email I Sent Has Been Read by the Recipient?
People want to know if someone’s opened their email. I’ll explain why features and tools claiming to do that can’t work most of the time. I’ll share the only way to know for certain your message was read.
How Do I Stop Email from Going to Junk in Outlook.com?
It’s frustrating when email previously marked as “not junk” continues to get sent to the Junk folder. Let’s look at your options.
How Do I Get an Email Address for Life?
Tired of changing your email every time a service shuts down or your ISP changes? Learn the smartest way to secure an email address that’s truly yours for life, and why relying on free or “lifetime” promises could leave you stranded.
Why Am I Getting Bounces for Email I Didn’t Send?
Spammers want to send email that looks like it’s coming from someone who can be trusted. They want it to look like it’s coming from you — and you may end up getting the bounce notifications.
Why Does Email I Send Fail But a Reply Works?
If sending an email bounces but replying works, the culprit is usually a wrong address hiding in plain sight. Learn how display names, typos, and auto-complete can fool you, and how to fix the problem so your messages get through every time.
How to Transfer Your Email From a PST to Thunderbird for Free
Switching from Outlook (classic) to Thunderbird? You don’t need to buy tools. With a little time and a free email account, you can move your messages yourself. I’ll walk you through the steps to transfer your email safely and reliably.
Why Must I Re-Enter my Email to Unsubscribe?
If a website makes you re-enter your email just to unsubscribe, it’s bad design, or worse, a shady tactic. I’ll explain why this happens, what it means, and how to spot when it’s just spam trying to trick you.
What Happens When You Close an Email Account?
Thinking about closing your email account? You might want to think again. From lost data to unexpected lockouts, and even someone else ending up with your old email address, I’ll walk you through what happens, and why keeping the account might be the smarter move.
Searching for a Technical Support Support Phone Number? Avoid This Huge Trap
I’ll explain why searching for a tech-support phone number is one of the most dangerous steps you can take when you’re looking for help.
Could Someone Reopen My Closed Email Account?
Closing or abandoning an email account can have unexpected and perhaps unwanted side effects. I’ll explain what those are and what options you have.
Does Getting Bounces to Email I Didn’t Send Mean I’ve Been Hacked?
Email bounces from messages you didn’t send can be disconcerting. I’ll explain what’s happening, why you probably don’t need to worry, and what steps you might take anyway.
What Happens If You Click a Bad Link?
Accidentally clicking a malicious link might be benign if you catch it soon enough. I’ll review what makes the difference, and what steps you need to take next.
All the “Ishings” Trying to Scam You
The concept of phishing has spawned a variety of “ishing” terms. They represent different ways scammers try to achieve a common goal: to scam you. I’ll review what they all mean.
Avoiding Scams: Why Hackers Can’t Recover Your Gmail for You
You’ll often find testimonials and offers of amazing account recovery success. It’s a trap.
The Hidden Cost of Free Email: Protecting What Matters Before It’s Gone
I hear of free email accounts being lost constantly. Here’s how to reduce your risk and use free email accounts safely.
Security, Privacy, and Spam: What Disposable Emails Truly Protect
Disposable email addresses are convenient for some things, but it is important to understand what they offer and what they don’t.
Why Email Forwarding is Broken and What to Do Instead
Learn to pull your email together rather than push it.
The Email Tracking Myth: Why You’ll Never Reliably Know If Your Message Was Read
We often want confirmation that an email has been opened, delivered, or read. In the age of spam, it’s not possible with any accuracy.
How to Send Email from Your Own Domain (Without Getting Blocked)
Anti-spamming measures complicate email. This makes sending “from” your custom domain a little trickier.
Someone’s Sending From My Email Address! How Do I Stop Them?
Seeing emails that look like they’re from you but aren’t? Spammers are probably “spoofing” your address. Learn why it happens, how to tell if your account is truly hacked (probably not), and what, if anything, you can do about it. The solution may be simpler than you think.
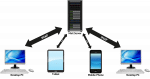
What is IMAP and How Can It Help Me Manage My Email?
IMAP is a protocol that makes dealing with email on multiple devices much easier.
Am I Wasting My Time Reporting Scam and Spam Emails?
Reporting spam in your email program with the spam button is critical. Reporting it by forwarding it somewhere isn’t going to do any good.
What Happens When I Mark Something as Spam?
Marking spam as spam is an important tool in the war against it. Exactly what happens when you do so is clouded in mystery.