Articles in Category: Privacy
How Can I Send a Document to Someone Securely?
Sending private documents by email feels risky because it is. What’s the safest way to get sensitive information to the right person without it falling into the wrong hands?
An Unexpected Way Videos Can Expose Your Location
Something many people do every day may expose their location in ways they aren’t aware of.
Privacy and Searching for Phone Numbers Online
You have an email address and you want the associated phone number. It’s unlikely you’ll find it, but there are a few things to try.
On Trusting and Not Trusting Microsoft
Worried Microsoft is peeking at your files in OneDrive? The truth is more complicated and perhaps surprising. I’ll look at what scanning really means, why avoiding OneDrive may not be enough, and how trust in Microsoft’s products comes down to risk, reality, and choice.
How Do I Remove Myself From a Computer?
Leaving a job and worried about what’s on your work computer? From browser history to email accounts, traces of you remain. Learn what you can (and can’t) erase, and the smartest way to protect your privacy before you walk out the door.
Are There Hidden Files that Save Every Keystroke I’ve Ever Typed?
Worried your computer is secretly saving everything you type? It’s not. While there are hidden files and places keystrokes can live temporarily, there’s no master file of your entire typing history (unless malware is involved). Learn what’s real, what’s myth, and how to truly erase your data.
How Can an Employer Recover Information I’ve Erased?
Think clearing your browser or deleting files keeps your work computer activity private? Nope. I’ll walk you through the ways employers can recover or track what you’ve done, sometimes even after you’ve “erased” it, and why you should always assume they’re watching.
Is Internet Provided by My Landlord Safe?
Connectivity is becoming an added perk in some housing situations. Make sure you know the risks and alternatives when someone else provides your internet connection.
Does a VPN Protect Me From Telemetry and Other Data Gathering?
VPNs don’t impact data tracking or collection. We’ll look at why that is and what you might want to do about it.
Think Before You Share: Protecting Yourself From Email Harassment
It’s so common to give away personal information, we don’t think twice about it. Let’s start thinking twice.
Is Automatic Sign-in Safe for My Email?
Having your email automatically or continually signed in to can be a security risk in some situations, but very convenient in others.
Is My Smartphone or Smart Device Listening In on Me?
It’s not uncommon to think our smart devices are listening in when advertisements seem to follow our discussions.
Surprising Reasons to Use a VPN at Home: More Than Just Privacy
Although a VPN service is probably not necessary at home, there are a few scenarios where you may want to consider it.
I Gave AI My Search History and Here’s What It Told Me
I was listening to a podcast recently in which one of the hosts described giving ChatGPT the history of the questions he had asked it and then asking it to build a profile on him based on that. It was interesting, of course, but it got me to thinking… why not use internet searches as … Read more
How to Securely Wipe the Windows System Drive
Reformatting the system drive takes a little more effort than other drives. Here are three ways to get it done.
Yes, You Should Give Google Your Mobile Number
Google uses your mobile number for verification if you lose access to your account. Some people don’t want to provide it. They should.
How Do I Prevent a Service From Logging Me in Automatically?
Preventing someone else from accessing your account is as easy as signing out before you leave.
Can Everything I Do Online Be Monitored at the Router?
While it’s not easy, your internet traffic can be monitored at or near your router. I’ll look at how this might be done.
Privacy Begins with the Operating System
Your operating system sees everything you do—and that means it holds the keys to your privacy. I’ll look at how much trust you place in Windows, Mac, Linux, or mobile systems, why that matters, and what steps you can take to protect yourself wisely.
How Do I Delete Google Search History?
Deleting your search history can seem simple, but there are complications worth knowing about if you need to be thorough.
Can My Neighbor View My Internet If I Use Their Wireless?
Using any shared internet means other users on the service might be able to see what you are doing. Extra security steps may be necessary.
What Should I Assume About Workplace Technology Monitoring?
Many employers can and do monitor the technological activity of their employees. Here’s what you need to consider doing.
They Set Up My Computer and Now My Ex Is Spying on Me. What Can I Do?
Trust is tricky when it comes to computers. When you add relationships to the mix, things quickly get complicated.
What is a Digital Fingerprint?
Digital fingerprints are another way that websites might track you, should they want to. What can you do? Should you be worried?
What is End-to-End Encryption?
If you’re sharing private or sensitive information, end-to-end encryption is an important term you need to understand.
Lock Your Computer When You Walk Away
If your device is not physically secure, neither the machine nor your data is.
What VPN Should I Use?
VPNs protect from certain types of surveillance and more. I’ll discuss what they’re good for and what to consider when selecting one.
How Should I Wipe My Windows Hard Drive Before Giving It Away?
Giving away your old computer is a great idea, but handing over your personal data along with it is not. I’ll show you the difference between a wipe that works and one that just looks like it does.
Can Hotel Internet Traffic Be Sniffed?
Many hotels offer both wired and wireless internet, but with those hotel internet connections comes a security risk most folks don’t consider.
The Biggest Risk to Your Privacy Revealed
We worry a lot about privacy, but our concerns are often misplaced. Fortunately, the biggest risk to our personal privacy is right under our nose.
You’re Just Not That Interesting (Except When You Are)
Worried about privacy? I believe we over-imagine the risks and at the same time are our own worst enemies.
Granting Location Permission: Why You Should and When You Shouldn’t
Granting location permission gives apps and web sites a more accurate idea of exactly where you are. The question is: do they need or do they abuse it?
Can People Track My Email Address Location?
Email addresses can be used to locate public information, which could allow someone to track your location from your email address. Use caution when sharing it with someone you don’t trust.
How Do You Delete Things from the Internet?
Realistically, it’s impossible to delete things from the internet. Yet in an apparent contradiction in terms, if you happen to delete something in your control, you also can’t get it back.
Can My Work Spy on My Home Computer?
Using a computer at work puts you at their mercy. It’s technically possible your workplace could spy on all your activities.
Can My Workplace See What Else I Do When I Work from Home?
Working from home can be convenient, or even a necessity. Does it open up your other online activity to scrutiny by your company?
How to Keep Information on a Shared Computer Private
When using a shared computer, it’s too easy for others to see your data or history. If you must use a shared computer, you need to protect yourself.
Can My Mobile Provider Track What I Do Online?
Your mobile provider is indeed your ISP when you use their data services, and that means they can see a lot of your activity.
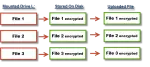
BoxCryptor: Secure Your Data in the Cloud
Many online cloud storage providers encrypt your data — which means they can decrypt it themselves. BoxCryptor is a great solution to ensure that your online data remains private, regardless of how it’s stored.
What Can a Website I Visit Tell About Me?
Websites can collect a fair amount of information about you. Let’s look at what every website sees.
Can My ISP See What I’m Doing If I Use a Virtual Machine (VM)?
A VM doesn’t get you any additional privacy from your ISP… although it might be a convenience as part of a more complete solution.
Download Your Facebook and Google Data
It’s a worthwhile exercise to download the data made available by Google and Facebook, if only to realize exactly what information is being kept.
How Did I Get Advertising About the Contents of an Email?
Sophisticated targeted ads can sometimes seem creepy. Here I explore how a few techniques work, and one I can’t explain at all.
Google Remembers More than You Realize
Wherein we consider how much information we “give away” in our daily lives online.
Sometimes the Threat Is in the Hardware
We spend a lot of time on software-related issues, but malicious activities and privacy violations can happen via hardware as well.
How Do I Protect Myself from My ISP?
If you’re using an internet connection from a source you don’t trust, there are a few alternatives.
How Do I Give Someone a Laptop Without Including Access to My Accounts?
It’s not easy to give someone a laptop without giving them access to your personal accounts. Depending on intent and trust, there are steps you can take.
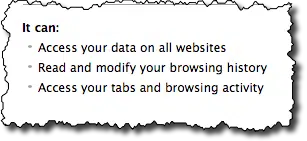
Do privacy apps really keep me private?
Privacy on the internet means different things to different people. I discuss three different privacy applications out there, explain what exactly each does, and offer some of my own thoughts.
Can spyware see what you did before the spyware was installed?
When a hacker gets ahold of your computer they can do anything. Keeping them off is the best plan.