Pretty easily, in most cases.

There’s so much more to your computer, as well as your activity history, than just cookies and tools like CCleaner can clean.
So much more.
I’ll review a few of the more obvious ways employers can recover or collect information about your activity. I’m not doing this so you can hide things better, but to illustrate the futility of trying.

What your employer can see and recover
Even if you delete files or clear your browsing history, your employer can find out what you’ve been up to. Deleted stuff can be recovered, other hidden info might still exist, and they can track you through network activity. If it’s their computer, assume they can see everything, because they probably can.
Cookies and CCleaner
Cookies are small files left on your computer by websites you visit. The contents of the files might not be useful, but their presence shows that your web browser has at some point visited that site. It’s a way to see where you’ve been.
Tools like CCleaner can easily and quickly clear cookies.
These tools can also clear other traces of activity, like your browser history, temporary files, the contents of your browser’s cache, and much more that can hold information about what you’ve been up to. They are an easy first step in removing traces of your activity.
But they’re not complete.
Help keep it going by becoming a Patron.
Resurrecting data
Deleting a file on your PC doesn’t delete its contents. Unless you take steps to overwrite the data, there’s a possibility someone could recover and restore it. This is what undelete tools are all about: trying to recover deleted files.
Clearing your cookies or history, or whatever else a data-cleaning tool might remove, does nothing more than delete the file(s) containing the information. The files could still possibly be undeleted.
The only way to avoid this is to overwrite the data after a delete. CCleaner and similar tools have a “free space wipe” tool that overwrites all the free space on your hard drive with random data, rendering what was there practically1 unrecoverable.
That may still not be enough to erase all of your tracks, however.
Don’t forget backups!
No, not your backups — your company’s backups.
In corporate environments, the company should have some kind of backup solution in place for all the equipment used there.
That’s great if something goes wrong and your computer dies, or you lose something important. It’s a safety net for both you and the company.
But depending on how often backups are created and how long they’re kept, they’re also a potential source of digital data coming back from the grave to haunt you. Even if you carefully and securely delete a file today, if it was on your PC prior to the most recent backup, it can still be recovered.
Data you’re unaware of
Windows is a complex operating system, as are the applications that run on it. Programs store information in places you might not know about, or in places you know about — like the registry — but have no way to remove. Even so-called registry cleaners only remove or correct certain types of information. They are more about the health of your system than removing evidence of your activities.
For example, someone knowledgeable could analyze the paging or hibernation files to collect or infer information about what you’ve been up to.
There’s simply no way to know that there isn’t some amount of evidence of your activities left somewhere.
The only way to remove all evidence of activity from your computer is to erase it completely. There are two approaches. One is to use tools like DBan to erase the hard disk. The other is to reinstall Windows from scratch, reformat the hard disk as part of the process, and perform a free-space wipe when the install is complete.
Both are likely to act as warning signs to an employer.
And both may still not be enough.
They may not need your computer
When we think about tracking and evidence of our activities, we immediately think of all the data that’s stored on our devices. Your company may not even need access to that.
Remember, they provide your internet connectivity and local networking. That means they can monitor where you go and what you do.
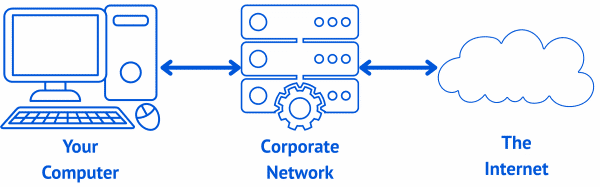
They don’t need access to your machine; all they need to do is monitor your online activity through the devices they control.
Also, it’s not your computer
When you use a computer provided to you by your employer, it’s not your computer. In most jurisdictions2, you don’t have a right to privacy on workplace-provided equipment.
The most obvious implication is that your employer has a right to snoop on what you’re doing by examining your computer or monitoring your internet traffic.
More concerningly, though, your employer could legally install spyware on your machine or interfere with the “privacy” implied by HTTPS-secure websites. That means that even if you completely erase what’s on your computer, they may have already collected information about your activity and sent it to their own servers for storage and analysis.
Do this
It all boils down to trust.
You may or may not trust your employer not to spy on you, but it’s important to realize that they can. If they want to, they can recover much of how you use their equipment.
Similarly, they may or may not trust you to use their equipment according to their rules and guidelines. Once again, it’s important to realize that they have ways of verifying their trust in you.
I can’t say how much invasive spying or forensic analysis is common, and I certainly can’t say how much of it is ethical or justified. I can say, though, that it’s possible. If you have any concerns, act as if your employer can monitor everything you do with their equipment.
It’s by far the safest thing to do.
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: Sadly, there are no absolutes. For example, there’s a tiny chance that data overwritten on magnetic material could still be recovered through extensive (and expensive) forensic analysis.
2: Remember, I’m not a lawyer, and none of this is legal advice. If you need legal advice, get an attorney.



Some companies install key-loggers which is generally legal for them to do. With those, every keystroke including deletions and corrections, and more such as screen-shots, are recorded and sent on to them. So there’s absolutely nothing you can do after the fact because they may already have all of the data.
Bottom line. Never use the company computer or company Internet connection for any non-work-related activity. Never use a company computer at home for anything but company related work.
The same applies to school computers.
…but… they should also inform every employee of the fact.
Forwarned is forearmed to the employee.
The upshot is, unless stupidity reigns supreme with an employee, less problems and less to see by the employer (usually the IT team though)
I call that a win/win. Employee is less likely to go to sites they shouldn’t (but remember there ain’t no cure for stupidity) therefore less chance of pernicious malware on the system. Employer therefore has less issues to deal with and time savings is $ savings.
My employer tracks what I do on my computer … and they make it known. As you log in to Windows, they put up a message box to tell you. But then, my employer has a lot of information that should not be disclosed, either on purpose or accidentally.
I appreciate my employer making it known that they monitor my actions. While they do have the right, I don’t think employers should do it surreptitiously.
Our company for a time used Spector CNE now called something different but i dropped the practice due to little or no enforcement after breaches of policy and sometimes law, we commenced using it due to a few staff stealing critical information. It’s an interesting dilemma. The software recorded EVERYTHING, screenshots every 30 seconds, key strokes , sites visited, facebook and other chat systems all recorded. We used to put up a warning message as you logged in to the workstation or laptop that informed the user that everything was recorded, i even showed people what we could see and capture.. Yet still people would download porn, set up drug deals, spend the day on gambling sites , unbelievable but sadly true. As is said we stopped using it costly and little benefit with no enforcement.
I have read that even if you ‘delete’ a file and then overwrite it with another file or random data, the original file can still be recovered by forensic analysis. I find this a little hard to believe but am just curious (nothing to hide) about how true this is?
When data is written to an HDD, it doesn’t write it in exactly the same location. It can be off by a tiny offset. Sometimes forensic analysis can find those tiny traces and determine what has been overwritten. That’s why some wiping programs overwrite up to 30 times. SDDs can’t be retrieved that way but that’s not saying someone won’t come up with a method to retrieve overwritten data in some other way.
And remember that this applies to the USofA. Other jurisdictions, i.e. countries, will have different laws. Some better, some worse, some totally diabolical.
Boot Linux from a flash drive and you don’t have to worry about deleted files or key loggers. Router logs could still be a gotcha.
Many companies use hardware keyloggers which can’t be bypassed that way. And standard company security usually blocks booting from anything but the installed OS. Use your phone and access the internet via your mobile carrier. Don’t go through the company’s network to access the internet and you should be safe.
Router logs, proxy logs, and hardware keyloggers, at a minimum, could all still be a problem. Just don’t do it.
You can also be blamed for your computer usage while you are away from your computer. Never ever leave your computer while you are logged in. Entering a password after every break is easier than finding a new job.
As far as the ability of the employer to do something like this, it’s a sad commentary. In my working life, I always had one rule when I hired someone: ‘If you don’t trust the people you hire, hire people you CAN trust.
Many companies have a trust but verify policy.
“Trust, but verify.”
A ridiculous term, because If they have to “verify” you, then they don’t trust you. Period, end of sentence.
I look at it as an ironic oxymoron. Of course, the two are mutually exclusive.
This article applies to the US. The law is very different in other countries. GDPR (General Data Protection Regulation, the law that makes websites annoy the hell out of you with cookie warnings) prohibits companies from monitoring their employees computer and Internet use. There are exceptions, but the conditions are strict.
The last thing you should do on an office computer is anything you wouldn’t want seen by your employer. Actually you should neve do anything you wouldn’t want your mother to find out. I remember when contracting on an Air Force contract using AF owned computers. We had to sign in and could use them for personal web browsing if we wanted to. One of the computers went down so was taken by IT for repair. While there the IT technician looked through all files stored on the computer and found one of my coworkers had child porn in his personal files. Needless to say all computers were confiscated and all files reviewed. One other had questionable files but not enough for prosecution. My coworker’s fate was never learned but I’ll bet when returning to the states he was met by law enforcement.
No matter what the company’s policy, don’t use the company computer or network for anything personal. It’s just not worth the risk. If you need to use the Internet for something personal at work, use your phone.
… Unless it’s a company-provided phone.