passwords
Why Can’t I Paste a Password Into This Site’s Password Field?
You’ve got a password manager and you’ve done everything right. Then you encounter some website that won’t let you paste your password. It’s maddening. And here’s the kicker: whoever designed it that way actually made the site *less* secure.
The Top Five Small Business Security Risks
Running a small business, especially from home, puts your data at risk in ways you might not expect. I’ll discuss what I see as the five biggest security threats facing small teams.
Do Complex Passwords Still Matter If You Use 2FA Everywhere?
Do you think your passwords don’t matter because you use 2FA everywhere? I’ll break down why weak passwords still put you at risk, how attackers work around 2FA, and the steps that keep your accounts safe.
Is It OK to Reuse Passwords on “Unimportant” Sites?
Reusing passwords on sites you don’t care about might feel harmless, but it still can open the door to bigger problems. I’ll look at why even “unimportant” accounts matter more than you think, the risks of cutting corners, and simple ways to stay safe.
Size Matters! (When It Comes to Passwords)
The results are in for last year’s most common passwords. The implications are depressing.
What Is a Passkey?
Passkeys are a new form of signing in that promise to be easier and more secure. I’ll walk you through some of the high level concepts and how they work, and how they keep you safer than passwords.
Many Ways Your Account Can Be Hacked and What to Do About It
There are many ways accounts can be compromised. There are also many simple ways you can protect yourself.
Going Passwordless Without Going Passwordless
Passwords are dying. On some services, you can start playing with the process by creating a secure password… and then forgetting it.
Is a Periodic Password Change a Good Thing?
Conventional wisdom says to change your passwords periodically. I disagree.
Why Do I See Lots of Failed Login Attempts on My Account?
I’ll show you how to look at your Outlook.com recent activity and review why it might be full of failed login attempts.
Has a Hacker Really Hacked My Email Account?
An email claims your email account has been hacked, possibly even including a password you’ve used. Don’t be fooled; it’s a scam.
How Can Passkeys Possibly Be Safe?
Passkeys may feel confusing now, but they’re a doorway to a more secure, less frustrating, passwordless future.
How Do I Recover My Outlook Account?
Outlook.com, Hotmail, and Microsoft account compromise and loss happens. Here’s how to get your account back depending on what happened to it.
No, Don’t Write Down Passwords
The world’s largest magazine dispensed some bad tech advice. Here’s why I so strongly disagree.
What’s a Dictionary Attack?
A dictionary attack is a common brute-force way of achieving a hacker’s goal. The goal of a dictionary attack could range from compromising your system to sending spam.
How Can Four Random Words Possibly Be More Secure Than 16 Random Characters?
Passphrases are just as secure as passwords — perhaps even more so — and are easier to remember if needed.
Why ANY Two-Factor Is Better than No Two-Factor
Headlines are proclaiming that two-factor authentication has been hacked. That in no way means you shouldn’t use it. Your account is still much safer with two-factor enabled.
Why Is It Important to Have Different Passwords on Different Accounts?
Using a different password for every login is crucial — and it doesn’t have to be difficult.
Your 6 Strongest Practical Password Techniques, Ranked
Six practical approaches to generating passwords, ranked from best to worst.
12 Steps to Keep from Getting Your Account Hacked
Here are the steps you need to take to prevent losing your account forever to a hacker.
How Tech Mistakes in Media Harm Us All
Please don’t base your understanding of technology on what you see in TV and movies.
LastPass Password Manager and Vault
One of the challenges with current online safety advice is keeping track of multiple different secure passwords. LastPass not only does that, but does it securely across multiple devices.
I’m Told to Change My Password. Why?
If you’ve been told to change your password, do so, but do so in the right way. I’ll explain what that means and why it’s important.
Why Your “Unimportant” Accounts Matter
Regardless of your initial thoughts, every account is important, and we are all targets.
Is Passwordless Authentication Safe?
Passwordless authentication removes the need for a password and replaces it with something else. But can that be secure?
Do Random Words Make Better Passwords?
As few as three random words make better passwords than strings of random characters — but not, perhaps, for the reasons you think.
A Data Breach Has My Data. What Do I Do?
Data breaches are everywhere but what should you do if your info shows up in one? I’ll break down the risks, explain what really matters (hint: it’s not just your email), and give you steps to protect yourself. Don’t panic, but do get informed and stay safe.
How Do Websites Keep Passwords Secure?
A high-level overview of how websites and services should store passwords security, so next time there’s a breach you’ll know what to look for.
Isn’t Storing Your Passwords In One Place a Security Risk?
Yes, password managers put all your information in one place. It better be a very good place.
Why Is It So Important to Use Different Passwords for Everything?
Using different passwords on different sites is not only good practice, it’s necessary to keep your accounts safe. I’ll review why, and how best to handle a plethora of passwords.
What Should I Do When My Information Is Involved in a Breach?
If your account is ever part of a breach, secure it to avoid further risk.
How Can a PIN Be as Secure as a Password?
On the surface, signing into Windows using a PIN feels less secure than a traditional password. It’s possible it’s more secure.
How Do I Choose a Good Password?
With occasional security breaches at service providers and rampant email account theft, password security has never been more important. Make sure you choose and use secure passwords.
View Your Saved Passwords in Google Chrome
Google Chrome can save your and display your passwords. That’s convenient, but is it secure?
Why Am I Getting “Invalid Password”?
“Invalid password” messages frustrate a lot of people, particularly when they’re certain they’ve typed in the right thing. I’ll review how what you enter might still be invalid.
Is Online Banking Safe?
You can bank online safely, as long as you know what to look for and what steps to take.
How Can I Recover My Current Account Password
Trying to recover the existing password for an online account is usually an exercise in frustration. There’s one possible straw to grasp at.
Password Checkup: A Recommended Chrome Browser Extension
Password Checkup is a browser extension that tells you if the password you’re using has been discovered by hackers.
Tip of the Day: Sign in With a PIN (or Not)
Windows 10 introduced the ability to sign in using a PIN. It’s quick and easy to set up and use.
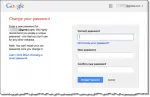
How Do I Change My Gmail Password?
It’s not necessarily obvious where Google/Gmail hides the “Change Password” functionality. I’ll walk you through it.
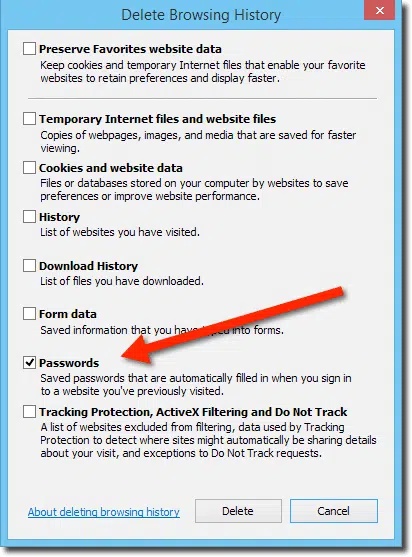
How Do I Disable Remembered Passwords in My Browser?
Web browsers aren’t necessarily the most secure approach to saving your login passwords. I’ll show you how to disable the feature and clear out any previously remembered passwords in IE, Firefox and Chrome.
Why Do I Need to Change Passwords After HeartBleed?
Heartbleed: what it is, what it isn’t, why it’s important, and of course what you need to do.
Is It Safe to Stay Logged in to My Password Vault?
Remember, the goal is to keep malware off your computer, not to try and manage it once it’s watching you. But there is another security hazard you may not be thinking about.
2013’s Ten Most Popular Posts
As 2013 draws to a close, I review which articles on Ask Leo! were the most popular and briefly discuss what trends that I feel they reveal.
Why Are Sites Making It Difficult for Password Managers?
Long passwords are your top-line of defense in internet security. Don’t let any trends steer you in the other direction.