The risks of over-exposure.

Email Password: Exposed Online (may or may not be readable) Type of Compromise: Potential breach Where your data was found: webpage Potential Impacted Site: www.adobe.com Email Password: Exposed Online (may or may not be readable) Where your data was found: social media
This happens to me from time to time as well.
I want to be clear: normally, this does not mean your accounts have been broken into.
However, depending on the specifics of the breach and your own security habits, it could mean your account is at risk. Your initial response to change passwords is a good one.
Let’s walk through what you should do next.

When your information is involved in a breach
- A breach typically exposes personal information, not passwords.
- If there are concerns, change your password.
- If you reuse the same password elsewhere, change those passwords also; make them strong and unique.
- If your account has actually been hacked, you’ll need to confirm or repair all recovery information.
- Now is a good time to consider two-factor authentication, if it’s available.
Data breach
What we call a “data breach” is nothing more than hackers having penetrated or “breached” a large company’s computer security, gaining access to databases not normally publicly accessible.
The database breaches we most commonly hear about are customer lists that include confidential information.
The information normally exposed includes our names, email addresses, and hashed passwords. As long as the breached company has proper security, a breach does not include actual passwords.1 Additional information may include physical mailing addresses, phone numbers, and more, depending on what kind of information was collected by the company and how they stored it.
It’s important to realize that rarely — very rarely, in fact — do hackers get your password. But that doesn’t mean you shouldn’t change it anyway.
Help keep it going by becoming a Patron.
The first thing to do
If you have any concern at all, changing your password is exactly the right first step. Most of the time it’s unnecessary, but since we can’t predict when “most of the time” really is, it’s by far the safest thing to do.
Use this opportunity to change it to a secure password, if you’ve been lazy in the past.
You’re at much higher risk if you had a weak password, even if the hackers didn’t get the passwords this time. There are techniques hackers can use to figure out your password anyway. The weaker your password, the more likely they are to discover it.
You’re also at much higher risk if you used the same password elsewhere.
The second thing to do
Depending on your personal security habits, the next step can get messy.
Did you use that same password for other accounts?
If so, go change the password at each of those other accounts. Make sure to give each a long, unique, strong password so you never use the same password twice. Use a password manager if you have trouble keeping track of it all. Doing so lets you use lots of different, complex passwords without needing to remember them yourself.
The issue is simple: if a hacker is able to get your password for the account affected by the breach, they’ll have an email address + password pair. Those are often the exact same log-in credentials you’ve used at other online services. Hackers know this, and immediately start trying that combination at a variety of online services. If you use the same password at multiple sites, losing one could be as good as losing them all.
This “password reuse” scenario has recently been blamed for several widespread account hijacks at popular, sometimes sensitive, services.
If your account has been hacked
If you suspect your account has been hacked and accessed by someone else, you need to do much more than just change a password.
In short, you need to change or verify every bit of your account profile that could be used to reset or recover your password (for instance, phone numbers, security questions, etc.). If all you do is change your password, hackers can use those other factors to re-hack an account. They’ve also been known to change this information so they can get back in whenever they want — and you can’t.
There’s much more to do after a hack than just resetting your password, and this applies to much more than just email accounts.
Strongly consider two-factor authentication
This is the perfect time to consider two-factor authentication, if your account provider(s) support it. More and more providers are supporting it every day.
Two-factor (or multi-factor) authentication is an added security layer that prevents hackers from signing into your account even if they know the password.
I strongly suggest two-factor authentication, along with complex and unique passwords, for any account you consider even moderately sensitive. (Spoiler: even the accounts you think of as “throw-away” or unimportant accounts are often much more important than you think. If it disappears, will you miss it?)
Is this common?
You asked if this was common.
Yes.
We hear about massive account breaches regularly. In my opinion, the pace will only escalate.
As I said, it happens to me semi-regularly. My email address shows up on several lists of breached accounts.2 I’ve changed more than a few passwords as a result.
But even showing up in all those breaches, I’ve not been hacked. I believe that to be common as well, but there’s no way to know for sure.
Find out if your account is part of a breach
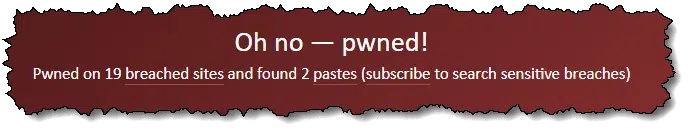
Aside from the various security and credit monitoring services that include this as a feature, you can look for your own email address on major breach lists. ‘;–have i been pwned?3 is a free service that will tell you if your email address appears in any breach for which they have the data.
You can also sign up to be notified if a new breach contains your email address. This is how I learned of my involvement in several breaches.
They have another free service that will check your password: Pwned Passwords. Using the same technology that prevents your password from being exposed in breaches, Pwned Passwords can tell you if a password you use was discovered in any breach, anywhere. If so, then you know you must stop using that password.
Backing up email
You also asked if there was a backup application for email should you decide to get a new account.
Absolutely. It’s called any desktop email program.
Seriously, get a program like Thunderbird or Microsoft Office Outlook or any of a number of others. Install it on your PC and configure account access using IMAP protocol, and the program will dutifully download all of your email to your PC as a backup. On top of that, since I’m certain you’re also backing up your PC, you’ll be further protected that way as well. 🙂
Back up your email regardless of whether you’re involved in a breach or not. There are so many different ways you could lose access to your email, you simply must have a backup or you risk losing everything, often without warning or recourse.
Remember: if it’s only in one place, it’s not backed up.
Each week I publish articles covering tech topics and solutions, including how to prevent, detect, and recover from security issues such as breaches. Subscribe to Confident Computing — more articles that help you solve problems, stay safe, and increase your confidence with technology, delivered to your inbox once a week.
Hope to see you there soon,

Podcast audio
Footnotes & References
1: Passwords are encoded into hashes, but hashes cannot be reverse-engineered into the passwords that generated them.
2: Apparently I still have a MySpace account. Who knew?
3: “pwned” is hacker-speak for “owned” as in, has your account been “owned” by someone else. Pwned is typically pronounced “powned”.
4: It’s important to note that no passwords were exposed in any of these breaches. At worst, hashed password data may have been included. In all cases, of course, email addresses and other possibly personal (but less sensitive) account information may have been included.


Do NOT just click on a link in a notice of hacked e-mail or anything else.
This could just be a Phishing scam.
Go to the site and access it as normal and change your data there. If it is scam mail you probably weren’t breached but this is a good opportunity to do as Leo says. Choose a strong password that you don’t use elsewhere.
Was the first thing I thought also. It’s a well known scam, Leo might want to add this to his article, preferably in the first few lines.