What Is “Mailer-Daemon” and Why Is It Sending Me Email?
Get an email “from” mailer-daemon? There’s a good reason this mysterious sender keeps showing up.
How Do I Change My Email Address?
Changing an email address changes a lot more than the address. I’ll look at common scenarios and a few additional approaches.
How Do I Deal With Getting Someone Else’s Email?
You didn’t ask for it, but there it is: email meant for someone else in your inbox. I’ll discuss why this happens and what you can do about it.
Are Deleted Emails Really Deleted?
Deleted an email and think it’s gone forever? I’ll explain what “delete” really means in webmail and desktop programs, why trash folders and database files can leave messages recoverable, how backups and even court orders can bring them back, and the inconvenient fact that the other person may still have a copy.
The For-Pay Email Providers I Recommend
People often use free email providers only to lose everything when a problem occurs. So what should you look for in a paid email provider?
“From” Spoofing: How Spammers Send Email That Looks Like It Came From You
Ever get an email from yourself that you didn’t send? You’ve likely been spoofed. I’ll show how spammers fake your address without touching your account at all, why it happens, and what (little) you can do about it.
How Do I Send an Email to Many People?
Want to email a big group without looking like a spammer or getting blocked? I’ll show you why the usual tricks don’t work well and walk you through safer, smarter ways to send group emails, from simple groups to full newsletter services.
What Happens When You Close an Email Account?
Thinking about closing your email account? You might want to think again. From lost data to unexpected lockouts, and even someone else ending up with your old email address, I’ll walk you through what happens, and why keeping the account might be the smarter move.
What is IMAP and How Can It Help Me Manage My Email?
IMAP is a protocol that makes dealing with email on multiple devices much easier.
9 Reasons Email Is Wonderful
Some say that email is dead. My take is completely opposite: email is one of our most effective communication methods.
Do You Really Need to Reply?
One way to reduce the amount of email you get is to reduce the amount you send. One way to do that? Think twice before replying.
What Does the “Mailbox Unavailable” Error Mean and How Do I Fix It?
“Mailbox unavailable” is a common email bounce message that tells us very little. I’ll review some of the more common causes of this message.
How Do I Find Someone’s Email Address?
It can be extremely difficult to find the email address of someone you want to contact. To begin with, they must want to be found.
Why Are They Saying I’m Sending Too Much Spam?
How your email can get blocked for spam you didn’t send, and what to do about it.
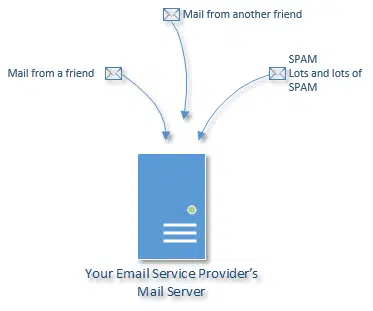
What Does “Over Quota” Mean? What’s a Quota?
Being over quota means you’ve received or kept too much email. To deal with it, you need to understand where that email is being kept.
How Do I Move Emails From One Account to Another?
Moving email from one account to another just takes some configurating and drag-and-dropping.
Can You Make an Email Without a Phone Number?
There are legitimate reasons for not wanting to give your phone number to an email service. Let’s look at alternatives.
Thunderbird: a Free, Open Source, and Powerful Email Client
Thunderbird is a robust and powerful email program that can meet the needs of both light and power users. I use it all day every day.
What are POP3, IMAP, and SMTP?
POP, POP3, IMAP, and SMTP are all acronyms used in configuring email. We’ll look at what they mean and how they relate.
How Do I Edit a Reply?
Edit a reply before sending it. Clean up your message, remove email addresses, and more.
How Do I Delete Multiple Emails When I Have a Lot to Delete?
It can be a challenge to delete multiple emails. I’ll look at some of the concepts and techniques used by various email programs to make it easier.
My Email Is Hacked, How Do I Fix It?
If your email is hacked, there are several steps you need to take to get it back and prevent it from being hacked again.
How Secure Is Email?
Email is ubiquitous and convenient, yet surprisingly, not particularly secure. I’ll look at why that is and when you should worry.
How to Email Large Files Using Any Email Program or Service
Emailing large attachments is typically a bad idea, as your mail may not be delivered. I’ll look at alternatives.
My Email Disappeared While Composing. Can I Get it Back?
It’s no fun to write a long email and lose it. Here’s how that happens and a few ways to avoid it.
If I Do These Things, Will I Be Anonymous?
Anonymity on the internet is really, really hard. Some of the practices we might use to stay anonymous could still be leaking identifiable, traceable information.
How to Get Email with Attachments Delivered
Emailing attachments — particularly large files — is getting more and more difficult as ISPs limit size and scan for malware.
Why Are Pictures Not Showing in Email?
There are many reasons pictures don’t show up in email. I’ll review the complex world that is email, and some of the things that can go wrong.
How to (Accidentally) Give Someone Else Your PayPal Account
Entering your email address incorrectly might just be a typo, but it can have surprising ramifications.
You Can Use Free Email Safely (But Most People Don’t)
Free email is popular, ubiquitous … and risky. Free email accounts are lost regularly with no hope of recovery. I’ll review how you can use free email accounts safely.
Why Is an Email Address Sometimes in Angle Brackets?
Computers use email addresses to route email. Angle brackets are used when a more human-readable name is also included.
‘Tis the Season … to Unsubscribe!
The holiday season brings with it a flood of email. That’s a great opportunity to evaluate, and unsubscribe from things you no longer need.
How Do I Access Email Stored in Outlook Express on Windows 8?
One of the problems with Outlook Express is difficulty in exporting data. Your best bet is to find a more recent software to help with the migration.
How Do I Deal with One Email Account on Two Machines?
There are various options to access one email account from multiple computers, and there are pros and cons to each.
2013’s Ten Most Popular Posts
As 2013 draws to a close, I review which articles on Ask Leo! were the most popular and briefly discuss what trends that I feel they reveal.
Why Does Mail Hang Around in My Outbox Before Being Sent?
There are many steps between your email and it’s journey out of the “Outbox.” Any one of those steps could be slowing you down.
Can I access the mail on my desktop from a networked machine?
There are several ways to share email accounts across computers. The best ones have to be set up before you need them.
How Do I Get My New Email to Be the Default Email in Windows?
Figuring out what is what with emails and email accounts can be quite confusing. But when all is said and done, you only need to change a simple configuration.
Did Someone Log In to Google with My Password?
It’s frightening, on the server side, to watch the constant attempts being made to slowly brute force a way into email accounts. So it’s safe to assume that if Google notified you – someone got in!
What if the forwarding service goes away?
There is little that you or I can do when a website goes away except to use online tools to try to trace it, or find some other way to replicate the service.
Why Can’t People Click on Links I Send Them?
Ninety-nine percent of the time when links aren’t clickable the problem is on the receiving end. It’s usually because their email program is trying to protect them from something that looks suspicious.