Old allegations get renewed focus.

I honestly don’t know.
Update: March 2022. I still don’t know.
Update: July 2024. I still don’t know.
However, my lack of knowledge is now moot; Kaspersky is about to be banned in the United States.
I’d like to share a couple of observations.

Kaspersky: now what?
Because of ongoing political concerns and the upcoming U.S. ban on Kaspersky, it’s time to uninstall it. There’s no conclusive evidence of wrongdoing, but using an alternative like Microsoft Security (Windows Defender) avoids possible risks and keeps you safe after Kaspersky is no longer being updated.
This is nothing new
As long as Kaspersky has been around and as long as it’s been publicized that they have Russian ties, there have been statements ranging from mild concern to outright accusations of spying or other underhanded deals. To the best of my knowledge as of this update, none of it has ever been substantiated.
Naturally, with the current political issues relating to Russia, these accusations are making headlines once again — to the extent that the U.S. government has warned the public against Kaspersky.
Now the U.S. government has escalated those warnings into an outright ban.
Help keep it going by becoming a Patron.
Kaspersky denies it all, of course
Kaspersky denies it all; but then, they would hardly come out and admit it if it were true.
They downplay their Russian connection. The Kaspersky website, for example, says:
Founded in 2004, Kaspersky Lab North America is a Massachusetts corporation and is a wholly-owned subsidiary of its holding company, Kaspersky Labs Limited, based in the United Kingdom.
Searching the Kaspersky website from within the United States, it’s nearly impossible to locate or view pages containing any reference to Russia. Only via the Internet Archive snapshots of the primary contact page can we see that Kaspersky is headquartered in Moscow.
Are they hiding something, or are they simply reacting in a reasonable way by focusing on their international and UK connections? Both approaches seem plausible.
2022: Russia and Ukraine
Even though Kaspersky has enjoyed a good reputation as an anti-malware tool, the risk may have become too great.
With the continued political turmoil, particularly in Eastern Europe and Ukraine, the concern grows that the Russian government could force Kaspersky to do exactly the kinds of things we’ve been worrying about.
As I said, there’s no proof that they have, but the possibility remains that they could.
So where’s the truth?
The truth is elusive.
- Kaspersky could have been spying on us all along.
- Kaspersky could have been completely innocent all along.
- Kaspersky could decide to start spying at any time.
On top of that, the accusations and responses are also questionable.
- The accusations of risk could be political posturing.
- The accusations of risk could be based on a credible threat analysis.
- The claim of innocence could be more political posturing.
- The claim of innocence could be honest and accurate.
I have heard and will continue to hear, I’m sure, strong opinions from people on both sides of this issue. Some folks adamantly believe Kaspersky is blameless and a great security package to boot. Others do not trust the software due to all the kerfuffle.
I don’t know. And to be clear, I’m not taking a position one way or the other. I simply do not know who is telling the truth or the size of the risk now or in the future.
Do this
If you are using Kaspersky software in the United States, uninstall it. Right or wrong, come the end of September 2024, you’re going to stop getting updates, which will leave you at risk.
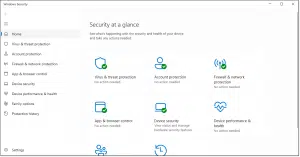
I recommend Microsoft Security, aka Windows Defender, as a primary security suite. In Windows 10 and 11, Microsoft Security should activate when you uninstall Kaspersky.
It feels a tad alarmist and might be an overreaction, but the ban gives us no other choice.




Every thing said here makes good points but when it comes to security, my experience shows that staying close to the original source is often the most secure. That’s why I believe that using the pre-packaged windows defender will provide the easiest and possibly the most secure alternative. I would also say that the very most secure method is to keep secrets totally off of the web. You might also consider using an external source for your storage, not the cloud but a thumb drive or external disc. I know its not practical to have multiple computers but in this day when we buy new every few years why not retain the old but keep it off of the web. You can always transfer files to your web computer if needed. Yes this is cumbersome but if security is your concern then I’m pretty sure the only true way is to be isolated from the web. At least this would make restoring a contaminated computer much easier. Just a thought and I’m sure not very well put.
That’s a good point. Windows Defender is what Leo recommends and he and I use. I’ve resuscitated several impossibly slow computers by uninstalling the AV program they were using and replacing it with Defender. And if you trust Microsoft Windows, you automatically have to trust Defender, because with Windows running on your machine, they can compromise your data in so many ways (I’m saying this theoretically to demonstrate my point), they don’t need Defender to do it.
And if you don’t trust Microsoft, there’s always Linux.
As far as I am aware the only way of knowing if any software is secure is to use free open source software that has been created by free open source software (languages compilers etc), as it can be scrutinised.
The inverse of this, Proprietary software, cannot be scrutinised, as it’s program code is re-coded (Linked and Compiled, so usually only readable by a computer) and is protected by laws, so you have no idea what that software could be capable of doing.
Unfortunately I’m not aware of a free and open-source security package. I know ClamAV (https://www.clamav.net) is out there, but my understanding is that it doesn’t measure up to the commercial packages. 🙁
Re: “Proprietary software, cannot be scrutinised”
For general interest — and *not* to nit-pick — there *are ways* to scrutinize software without having access to source code: decompilation and other reverse engineering techniques, sandboxing and observation… maybe others, not my area. It’s the same techniques used when investigators study malware.
The question is whether these techniques have been turned on “normal” programs, even AV SW, like Kaspersky. I’m going to hazard a “yes” and postulate that that’s how malware *developers* find their exploits. So maybe the real question is *who* is doing such investigation, and whether they’re likely to release their results to the public.
That’s another reason to stick with Microsoft Security. If Microsoft wanted to spy on us, they could do so without the help of their antimalware program.
“To the best of my knowledge, not once has any of it come close to being substantiated.” I’ll say, “Of course not, they’re FSB spies and are professional at not getting caught.” According to Russian law, companies are obligated to assist the FSB when asked.
Bottom line, fake news is everywhere, and it’s getting harder and harder to sort the truth from the BS. We just gotta be as careful as we can. I’ll stick with Defender. I trust Microsoft, but they literally can get access to anything on our computer, so Defender is the last thing they’d need.
Just another twist on this argument, but some of us live outside the USA and might regard any American-owned security offering with some suspicion as well 🙂
As I mentioned in other comments, if you use Windows, Defender is your safest option. Microsoft already has the capability of getting all your data, and Defender wouldn’t increase that capability. I’m not saying they do. In fact I don’t believe they do, but they can. 🙂
Indeed, I chose at least some of my language (“Or whatever country isn’t your country.”) with that in mind.
As a non American how can I trust any software from the US? CIA/NSA/Homeland Security can be using any of the US based companies as a spy tool. And what about the likes of CISCO? This companies products are used around the world so what stops these having software that is used to spy on the rest of the world?
In some ways, the average American has more to worry about with US software. Russia isn’t interested in the average American’s information. 😉 But seriously, it’s almost a certainty Kaspersky is spying on Ukrainian people, and I hesitate to use the word almost. When I was in Ukraine, everybody I knew used Kaspersky. Yevgeny Kaspersky was trained by the KGB.
“The company’s relationship with the Kremlin has never been clear, though Western experts on Russia think there’s no way Eugene Kaspersky could have become a billionaire without having reached an understanding with the government. Under Russian law, any company must open its communications lines to the authorities upon request.”
Hi Leo – Just an FYI. When I clicked your Brian Krebs link in footnote 2, above, I got this message: “The owner of krebsonsecurity.com has configured their website improperly. To protect your information from being stolen, Firefox has not connected to this website.” It seems unlikely that it would matter, but I backed out, “better safe than sorry.”
I just clicked on that – in Firefox no less – and it worked fine. Goes to https://krebsonsecurity.com/
It might be a problem with your browser’s cache.
I’ll suggest you start with this article that has steps to troubleshoot common browser-related issues.
https://askleo.com/dealing-with-browser-problems/
Clearing the browser cache would be the first thing to try as a corrupt cache is the cause of most browser problems.
Sadly these days they don’t have a lot of credibility in my eyes. Especially when it comes to matters of technology.
“Any company with ties or headquarters outside of the U.S. comes under scrutiny.” Actually any company regardless of where their headquarters are located can be suspect. As Leo often says, if malware is installed on your computer, it can do anything. Theoretically, any program can be a Trojan horse. So, if we want to be paranoid, any program installed on your computer can be malware and do just about anything. We just have to determine who we trust with access to our computer. That’s why, at the moment, I’ll stick with Windows Defender. MS already has all the access the could possible get and they don’t need Defender to get that access. And yes, I tend to trust Microsoft, at least now.
“Theoretically, any program can be a Trojan horse.”
Hey, at that rate, and for all we kbow, Windows itself might be a Trojan or some other type of malware!
(And I’m quite certain that there will be people who have always thought this.)
As a regular reader and contributor to our forum, you don’t have to speculate. There are lots of comments claiming that Windows is malware.
I’ve used Kaspersky as part of my security suite for many years with a great deal of success.
I have less fear about them than I do GCHQ and the NSA, Google, Miscrosoft and others snooping into my day-to-day online activities. I know I categorically cannot trust my own government to have my best interest at heart so a corporation that is actually known to be pretty good to keep me safe seems to be a good thing, regardless of where it originates.
Absolutely. Nowadays. most if not all governments snoop on their own citizens. so what the heck. Anyways an average individual has nothing to fear.
Perhaps not yet!
It depends where you are. I’m sure Ukrainians using Kaspersky would be a target. When I lived in Ukraine 22 hears ago, everybody I knew was using Kaspersky. I wouldn’t be surprised if it’s been weaponized for this war. In fact, I’d be surprised if it weren’t.
As Leo has often said, ENCRYPT if you are afraid someone might snoop or hack. Eventually, anything can be hacked, but is it worth it to the hacker?
Encryption wouldn’t help if a program is inside your system sending all of your keystrokes, screen shots and pretty much anything you do on your computer to them.
Everyone is focusing on a single path solution. Who do you trust more, Americans or Russians? Probably best not safe to trust either completely.
But for passwords we have two factor authentication. Belt and braces. What is the parallel in computer protection software?
It is very unlikely that two independent programs from suppliers in different countries would be both be attacking my system or stealing my data at the same time. So can I apply a ‘belt and braces’ strategy to protection? Can I securely run two different protection software programs at the same time, each checking the other?
What would you suggest to give my system ‘belt and braces’ protection against a single rogue protection software program?
“It is very unlikely that two independent programs from suppliers in different countries would be both be attacking my system or stealing my data at the same time.” As a statistics teacher, I can give you the probability. For example, if the probability of being attacked by the Russians is 30% and the probability of being attacked by the Americans is 25%, then the probability of being hacked by both are P(A and B) = P(A) x P(B) = .25 x .30 or 7.5%. The probability of being attacked by at least one are P(A or B) = P(A) + P(B) – P(A and B) or .30 + .25 – .075 = .55 – .075 = 47.5%
As I’ve been saying in other comments the safest antivirus is Windows Defender (MSSE in older Windows versions) because the probability of MS using Defender to hack your data is likely 0, because they already have access to everything on a Windows computer, and Windows Defender wouldn’t add to that. I’m not saying that to be alarmist, it’s just that the probability of malware increases with each program you install. So the belt and braces solution I’d recommend is stick with Defender, stay away from questionable websites, and only install software you know and trust. And don’t worry about 3 letter agencies. If they want your information, they already have it 🙂 .
Mark,
Thanks, that’s a great and entertaining reply. I can see the sense in the Defender Argument. But the flaw in your approach might be that the threat from Agency A will likely be different to Agency B at any one time. For example, CIA might want to see if I have Item 1 (say links to person X) during say one week, whilst KGB might be doing Item 2 (say want to install spyware in Product ZZZ) during another week. I.e. two independent phenomena. I assume its unlikely that both agencies will do the exact same probe at the same time. So isn’t my solution of two protection agents, each testing each other continuously, a better solution than suggested by your probability calculation?
I do actually trust US much more than most other governments, but I guess I have to assume the worst for all in this debate. I think however that all the anti-virus companies need to address the issue of trust better, at least until we find an Alice and Bob solution to all this.
Anyway, is there a way to do this in practice. Do I achieve something similar with for example running Kaspersky with Malwarebytes Premium side by side; do they watch each other?
Thanks for your kind reply again.
The problem with having more than one AV program running in real time is that they can conflict with each other. You can run scans from other antimalware programs periodically, though.
Additionally, 3 letter agencies would very likely be able to create undetectable key loggers. This would especially be the case with AV programs as they have low level access to your computer and are constantly accessing the internet to be able to get the latest updates. That low level access is one of the reasons two AV programs shouldn’t run together in real time. The low level access can cause one antimalware program to think the other is malware.
Anyone depending on Microsoft Defender as their only protection is a naive fool. Period.
Actually, anyone depending on any antivirus as their only protection is a naive fool. There’s a lot more to internet safety than just your AV.
https://askleo.com/internet_safety_7_steps_to_keeping_your_computer_safe_on_the_internet/
Well, that’s insulting.
To be clear, you also need to rely on yourself to not do things that bypass your security solutions, or do things that put you at risk. Defender is my only security software and I consider myself neither naive or a fool. But it’s part of a large strategy that keeps me quite safe: https://askleo.com/internet_safety_7_steps_to_keeping_your_computer_safe_on_the_internet/
Yes, that was insulting, and a poor reflection on Dave G who didn’t have any alternatives to suggest. But back to Windows Defender. It’s a fact that Defender (and the associated Microsoft Malicious Software Removal Tool – MSRT) don’t catch as many malware items as other malware tools, at least not during a scan. Microsoft explains this by saying that it only goes after the big fish and doesn’t report on minor malware or PUP and looks for malware it considers to be currently prevalent. This admission is disconcerting. Also, recently a bug seems to have crept into the MS malware tools during scan: if you watch the status during a scan, it will tell you that it has detected something, but when the scan ends, it says “nothing found”. This problem has also been reported about Defender. If Defender and MSRT find and immediately remove malware without reporting the details, then that’s a problem too. It’s good to have Defender as a real time, background malware tool, but use other tools to scan every so often. The advantage of Defender as a real time tool is that it has a small footprint (in terms of memory and CPU usage) and not too many confusing and esoteric setting options.
I have read recommendations that it is best to stick with 1 (one) active AV/Malware/etc solution that you are comfortable with for your daily security. I have also read that adding more that one active AV/Malware/etc running simultaneously can end in very bad results with 2 (or more?) programs fighting with and detecting each other into a potential death spiral. Too many times Bob Rankin has mentioned this situation as people ask computer related questions. I have not personally experienced this, but have avoided the situation to begin with… (KISS) I have used upon occasion ‘Stinger” or “MBAM” as a run once solution to detect potential threats that I think maybe my regular choice might have missed. So far I have not had too much in the way of headaches, just the occasional pups that seem benign in nature (adverts).
I wanted to add that I kind of liked the idea of using an older computer for a back up machine that is not internet connected… Is there a yah or nay on this idea? A pro verses con discussion?
Very interesting Russ on running duplicate AV type scanners. I have a cyber business and have also installed about 900 copies and installed them with Kaspersky. However, you are correct in that there is mostly a conflict with both Virus programs attempting to scan the same i.e. file where very strange outcomes can emerge. One big issue is speed of your computer will be reduced. If you run an SSD and have fast HW you may not notice the impact. For most AV programs they highly recommend not running two at the same time. As for Kaspersky, many times it won’t even install until you remove the other AV program. However, with Defender, ESSET disables defender from even running. However not to confuse things, I have been able to run the defender scan with Kaspersky but I don’t let it execute after I let it scan with the latest DAT files and updates. Basically I stop Kaspersky, then I execute Defender but to date it has never found anything at all. But Kaspersky has saved my systems dozens of times!!! Plus I like the multiple updates per day with Kaspersky as they work their butts off there. And yes, clone your main drive and back up your data!! Drives are cheap and worth the effort.
In your latest book, The Ask Leo! Guide to Online Privacy, you say:
“The most important take-away, however, is not that Microsoft may or may not be trustworthy; it’s that every operating-system vendor has the power do any or all of this, with or without letting us know. The amount of trust we place in any OS vendor to properly manage our privacy and security is enormous.”
This may sound alarmist, but isn’t that true, to a lesser degree, with any program you install? Once you click yes to the UAC, you’ve given that installation program administrative rights on your machine and at that point, it is capably of doing anything on your machine.
Stay away from Kaspersky. After Putain’s attack on Ukraine, the Russian government has proven it can’t be trusted.
The U.S. Federal Communications Commission has deemed all products and services from the Russia-based cybersecurity firm Kaspersky an “unacceptable risk to national security.”
and
Using Russian tech? It’s time to look at the risks again, says cybersecurity chief
Leo-
Would you be willing to recommend some other protection for my HP Pavilion dv7 Windows 7 Home Premium (x64) Service Pack 1 (build 7601) laptop?
Kaspersky came with my HP Pavilion when I bought it from Costco in 2013.
And I’ve been running Kaspersky on it ever since.
After I read your advice, I entered “Windows Defender” in the “Start->Search” box.
A new “Windows Defender” window opened.
Near the top there was a link “Check for updates now”.
I clicked on the update link.
After about 12 seconds the window changed.
The update Status read that definition updates can’t be installed.
So I clicked on the link “Go online to view troubleshooting tips”.
A Microsoft web page “https://support.microsoft.com/en-US/help/918355” opened.
It read “Sorry, page not found”.
Again, can you recommend something to replace Kaspersky for my Windows 7 Home Edition 64-bit HP Pavilion laptop?
Thanks for your help…
Per the article: “I mention several additional alternatives in What Security Software Do You Recommend?“
Leo, I do use (limited) Windows Defender, but my main program is a US only based called White List software called PC Matic. I have used it for 5 years now and have had 0 problems with it. I have to admit, that $50 bucks per year and 5 machines is pretty darn cheap considering some of the alternatives.
I’ve been using PC Matic ever since day one, and I thought enough of it that I bought a forever license. What I don’t understand is why so many other security programs don’t like PC Matic and suggest that it be deleted. And I don’t run multiple anti-virus programs simultaneously, either.
I use Windows Defender (now Microsoft Defender) in Windows 11, and I used it in Windows 10 ever since I tested it (the OS) as a member of the Windows Insiders Program (beginning January 2015). Over that time, I have never contracted any malware on any of my computers (all of which are protected by Devender). Microsoft releases definition updates regularly, often more than one a day. Defender provides real time protection, email protection, Smart Screen protection (guards against installing suspicious apps from known-to-be unscrupulous sources) and other more advanced features (Controlled Folder Access – aka Ransomware protection for one) that may be more bother for non-technical users than the added protection they may provide is worth.
My logic for using Microsoft Defender is that if I trust Microsoft enough to use their OS, it’s reasonable to use their antimalware suite too, keeping my usage information under one ‘roof’. I understand that others may disagree.
My2Cents,
Ernie
As far as I know Kaspersky moved to Switzerland some time ago. I still trust the program, it works very well in combination with Malwarebytes. Windows Defender is a good alternative although I would not use it to do bank payments. I tested Bit Defender a while ago with a free license for 6 months, trusthworthy even for bank stuff. All the other free versions are (in my opinion) worthless.
Kaspersky has offices in many countries. It’s still a Russian company and I wouldn’t trust them wherever they move. The US and German governments, and Dozens of computer help sites warn against using it. Yevgeny Kaspersky was educated in a KGB university. “The Technical Faculty of the KGB Higher School”. So why take chances?
And boycotting Russian companies shows support against Putain.
As I mentioned in an earlier comment, there’s a nationwide system of Internet surveillance in Russia. Russian Internet Service Providers are required by law to provide direct and unrestricted access (backdoors) to Russian security services. Additionally, a recent law mandates that companies comply with requests to aid in surveillance.
Is this proof that Kaspersky is spying? No. But it’s safest to assume they are. One advantage of Microsoft security is that they don’t spy on us. Microsoft has hundreds of other ways to spy if they want. 😉
And we know the NSA is spying on us according to Snowden. I can’t imagine the FSB is any different. On the other hand, if Kaspersky is spying on its users, they are not interested in most of us. If I had a security clearance or worked for the government or a company with proprietary secrets, the FSB would be interested. I still avoid Kaspersky, though. I’m fine with Windows Security. It’s easier on computer resources and as I said earlier, they have hundreds of other vectors they can exploit without using Windows Security to spy. Many use Linux for that reason.
Many consider China to be a major security concern for the United States and other countries as well. With that is mind, do you have any issues recommending EaseUS software?
Much like Kaspersky, the concerns are not new. And much like Kaspersky there’s been zero evidence of any wrongdoing. It’s worth knowing about, but right now I’m comfortable with it.
No direct evidence, but there’s enough circumstantial evidence to keep me away from Kaspersky. Better safe than sorry.
That’s a possibility, but most of us are of no interest to the Chinese government. I’m more worried about my government spying.
Thank you for your reply and insights on this topic. My concerns regarding China go further than day-to-day wrongdoing via the EaseUS software. China is preparing for war with the United States. This may not ever come to a point of conflict, put the preparation is happening. Cyber attacks will most likely be part of the first phase of this conflict. I believe now is the time to take precautions to minimize this vulnerability.
Thank you Leo, for sharing your expertise.
Shortly after Russia invaded Ukraine, I uninstalled Kaspersky. After it was uninstalled, as I recall, it took quite a bit to get all the remnants of Kaspersky off of my system.
Kaspersky has announced that the company will be shutting down U.S. operations and closing their U.S. office starting July 20, per an article on Bleeping Computer.
While I’m not overly concerned about government surveillance (I’m just one fish in the ocean), I do what I can to protect my data. I use Windows Security because it comes with Windows and take care with what I do online. Data I care about is stored in encrypted vaults. I’m more concerned about data breaches than anything else.
I installed Kapersky anti-virus on my laptop computer years ago. This is after I heard how good of an Anti-Virus software it was from various legitimate sources. Not sure how much I paid for it, but after a few months I had to remove it becuse it was affecting the performance of my computer negatively. I never knew this software was from Russia. My guess was that it was developed by Polish Americans ? The thing I soon realized was how deep this software installed itself on my computer, to the point it affected almost every function at the “cellular level”. It affected things such as CPU, registers and RAM. Uninstalling it was another headache. I’m glad Microsoft finally got its act together and improved MicroSoft Defender to the point where you don’t really need any third-party AV software. These days, hacking and data-breaches are mostly done at the Network level, meaning after the data has actually left your computer and is in route to somewhere else. These type of breaches are not only hard to detect, they are very hard to prevent. The best way would be to encrypt all outgoing and ingoing data going in and out of your computer, but if you don’t have much to hide, is it really worth it ?
That’s another reason to stick with Windows built-in security. Many antimalware programs are heavy on computer resources.
In fact, today my computer was running horrendously slow. I uninstalled an antimalware program I was trying out and it solved that problem.
Latest: Commerce Department has banned Kaspersky.
Kaspersky ending business in U.S.
Not to worry. We still have Meta, Google, TikTok, Microsoft, X, etc., etc.
I worked at a Ontario University during that time I was responsible for my Departments PC’s students and dept faculty.
An individual was there responsible for Administrative PC’s and was trying to force the use of Kaspersky Antivirus, he was Russian and his influence was being used to try and force others to do the same.(My Department). At the time my choice was McAfee. The University made Trend Micro the choice.
This during a time of Oriental Students bringing hacked Windows, AutoCAD and many more program CD’s with them. I had to ask the Chair of the Dept to intervene.
Can I install Microsoft Defender when I already have AVG anti virus installed on my PC?
Microsoft Security (which includes Defender) is already installed. It simply steps aside when another tool is installed. So to use Microsoft’s solution you would simply uninstall AVG.
I started using Windows Defender (Microsoft Security) when I installed the Windows 10 Insiders preview release in January 2015, and I’ve never looked back.
Many years ago (prior to 2015), I gave Kaspersky a try, but I was uncomfortable with the fact that it was/is a Russian company, so I removed it (and performed a clean installation of Windows to insure there were no hidden remnants of Kaspersky). I took this step because I’ve never had any trust in Vladimir Putin, or (by extension) Kaspersky. I may be of no interest to the Russian government, but my computers (combined with those of all other American Kaspersky customers) could provide an avenue for them to initiate attacks on American cyber infrastructure through Kaspersky. Even if this possibility is remote, it still remains.
My2Cents,
Ernie (Oldster)
Of course if you live in Russia or China you trust Microsoft because the Americans wouldn’t be spying on you.
Hmmm… Being spied on by the Russkies or trusting the US Gubment… I’ll take the Russkies. I only read a few comments, but I don’t know how anybody could recommend Windows Defender. It almost never works from the now white screen I have to updates that run seemingly forever to scans that hang etc…
That’s on a fresh install that I just had to do because whatever infected me wasn’t caught by Defender… Although to be fair, most AV’s don’t catch real time anything either.
I need to find a good AV that works, as they all have major flaws.
The elephant in the room is that EVERY country spies on their own citizens intimately. All of our devices as of this moment if it has ever connected to the internet, has a government’s sponsored spyware. This is not speculation, it is an objective fact. Until people can come to terms with that, no judgement is truly going to be accurate. What matters more is your threat profile, who you are hiding your info from. If you work for the USG, you would be stupid to violate any federal policy (it shouldn’t have to be law for you to comply) and risk your job using this. If you are a whistleblower or someone who the current administration (be it local, state, or federal) doesn’t like, you would naturally already assume that your electronic devices are compromised by a default. For nearly everyone in the US, you are much more likely to be targeted by the US government than the Russian government. It’s kind of obvious that unless you are a POI, foreign governments really don’t care about your activities like your own government does. And if you are a POI, you probably work for the USG in some capacity, so again, you would be dumb to not do what your boss tells you to do if you want to keep your job.
Truth be told, none of these programs are really all that great. Even skiddies following a tutorial can exploit your system very easily if you give any access at all, it’s just a matter of targeting and figuring out what they want out of your device. Your best protection is yourself, not putting sensitive info on your devices, and having good protocols like regular password updates, 2FA, not following links/downloads randomly, not leaving their device physically insecure to evil maid/bad USB, etc.
Most people really only want to use Kaspersky as a middle finger to the USG. Being Americans we naturally have an inherent hatred for our government and care more about freedom of choice even if we never intended to choose the option being closed off from us. And I can vibe with that sentiment. Tyranny only begins when people comply. Having a competition of opinions is always a good thing as long as it doesn’t stray into unconstitutionality. One reason why it was good we had some people go anti-Ukraine rather than everyone putting the Ukrainian flag in their PFP and web banners and unanimously embracing the war fever. For dissenters they still have the option of using a VPN to get regular Kaspersky services and updates. Yeah this is the same stuff the Chinese use to circumvent their own tyrannical government blocking youtube and the like, but that’s pretty much the mindset you are going to have to have to continue down this path. You are going against your government’s agenda and are in the exact same situation as people in “non-free” countries.
“Your best protection is yourself, not putting sensitive info on your devices, and having good protocols like regular password updates, 2FA, not following links/downloads randomly, not leaving their device physically insecure to evil maid/bad USB, etc. ”
Your computer is the safest place to store you sensitive information. Be sure it’s encrypted.
Regular password updates are generally a waste of time.
A VPN won’t protect you against malware. If a program like Kaspersky has malware it’s on your machine and a VPN can’t defend against that.
yes microsoft defender gets knocked..I have been using it for 10 years with no issues..although in the past I have had to use malware bytes a few times for some
infilterations that defender may have missed..evenso, in the last few years all has been good…and it is free..best part
Hi to all from an Old Guy (and a longtime reader of Ask Leo) who wants to share this memory: “Kaspersky sold his company to his wife who was in London. He went to Moscow to work for government security.” Anyone remember this decades-ago news story? Just asking. That prompted me to abandon Kaspersky in an abundance of caution. It just didn’t feel right… Leo?
Yevgeny Kaspersky was trained at a KGB University. That’s enough for me to avoid his software. Is it spyware? There’s very strong circumstantial evidence but no smoking gun.
Court document points to Kaspersky Lab’s cooperation with Russia’s security service
as a Non-USA citizen, I do not trust anything from cy’s in the States. I normally try to use as much as possible open-source software, and daily os is ubuntu and in dual boot Windows( I have to admit though that for my FS game , I have to use Windows), which has no personal nor private information at all. What is said about Kaspersky, is (could?) evenly said about American cy’s ,as the states throws subpoenas around like candies in the Tour de France, where those American cy’s are prohibited to open up on that subpoena, speaking about “Freedom of Speach”!”. Not to say that I use Kaspersky, as I do not need it in my Ubuntu and for the FS game, I consider Defender sufficient.
As a non-US citizen you have less to worry about from US intelligence services than US Americans do.
Firstly, I’m in the UK, so the US ban doesn’t affect me.
I’ve used Kaspersky for a number of years and have been happy with it on Windows (Android was another matter), however, when my subscription expires next year, I won’t renew. Not [just] because of the Russian connection (like others I doubt there’s anything on the household machines to interest Russia), but because of the numerous pop ups I endure. If I had the free version then adverts are justifiable, but not otherwise.
One issue I forgot to mention with Windows Defender is the updates. It’s now 1014 EST, and the latest update is yesterday at 1510.
19 Hours with no update.
I don’t expect that little ol me will run into a trojan or anything, but I have a computer that is strictly for banking… Absolutely no web pages of anything else, and it has been solid for 3 years now…
I have had to reset my other laptop several times, and I only go to news sites / news streaming sites / Wall street stuff… I don’t go to any nefarious sites at all. There is viruses on normal sites that no virus program finds.
I have a friend who does his banking by booting into a live Linus from a USB flash drive. Overkill? For me, it is, but it’s safer, easier, and cheaper than a dedicated computer.
So he boots using a potentially infected computer?
Do you mean Linux?
Don’t forget to Disable Automatic renewal in UltraAV Antivirus.
It was horrible how abruptly Kaspersky was switched. My computers were crashing because of UltraAV. I removed and now all is well.
I asked Bing Copilot
Me:
“Does Russia have a law that requires Russian companies to help them spy?”
Copilot:
“Yes, Russia has laws that require companies to assist with national security efforts, which can include surveillance and espionage activities.
For example, the Yarovaya Law, enacted in 2016, mandates that telecom and internet companies store users’ data and provide it to authorities upon request.
Additionally, companies are required to install equipment that allows the Federal Security Service (FSB) to monitor communications.
These laws have raised significant concerns regarding privacy and civil liberties.”
Bottom line: Avoid Russian software