Encryption may not work the way you think it does. And that’s okay.

I’ll assume you mean BitLocker whole-disk encryption, but the concept applies to many different encryption tools. You can often change your Windows password (or passphrase) without needing to re-encrypt what you’ve encrypted.
How’s that possible? The secret is this: your Windows password wasn’t used to encrypt the disk.
And that’s okay.

Your password isn't the key
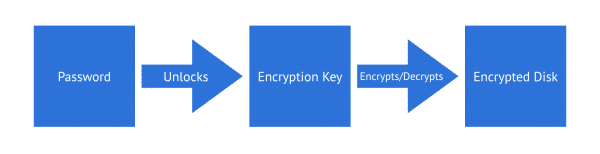
When you use BitLocker (or a similar tool) to encrypt your drive, your Windows password does not directly scramble your data. A hidden random key does the encrypting, and your password locks that key. So when you change your password, only that lock changes — not your data encryption.
Encryption keys
I’m not saying that this is exactly how BitLocker, or any specific encryption, works. This is a conceptual discussion of a technique that makes what you’re asking about possible, and I’m fairly certain the technique is common.1
When you first encrypt a disk, an encryption key is generated for you. It’s a key you never see. It’s referred to as a 128-bit, 256-bit, or other-sized encryption key. (The larger the key, the more secure the encryption, but the slower the encryption/decryption process.) It’s not something you would recognize as text — it’s a purely random2 binary number. It’s much more random than any password you might create. An example might be:
C6EDBC47 B7B4566C 99A9E1A3 6B7B47C3
That’s a randomly generated number displayed as 32 hexadecimal characters, meaning it’s 128 bits. This encryption key is used to encrypt your data, not your password. In fact, your password hasn’t even been involved yet.
Your password — be it your Windows sign-in password, or a password used with another encryption tool — is hashed, possibly several times, into a number. This hash of your password is used to encrypt the encryption key that is eventually used on your data. This encrypted copy of the encryption key is stored securely somewhere on your device.
Put another way, your password is used to encrypt only one thing: the “real” computer-generated key. That key is used to encrypt all of your data.
Help keep it going by becoming a Patron.
Decrypting your data
When you sign in, you provide your password3. If the password is correct, you can log in.
That password’s hash is then used to decrypt the encrypted copy of the actual encryption key.
That encryption key is then used to decrypt the data on your hard drive.
Changing your password
When you change your login password, all the system has to do is:
- Decrypt the encrypted encryption key using the hash of your old password.
- Re-encrypt it using the hash of the new password.
The key used to encrypt and decrypt your hard disk never changed.
If, for some reason, you need to change the encryption key used to encrypt your data, you would need to decrypt it completely and re-encrypt from scratch. For example, you might turn BitLocker off and then back on again. Turning it back on would cause a new, completely random encryption key to be generated, which in turn would be secured in your Windows profile using your password. Fortunately, this level of re-encryption is rarely, if ever, needed.
Saving the key
When setting up a BitLocker-encrypted drive, you’ll be encouraged to save a recovery key.
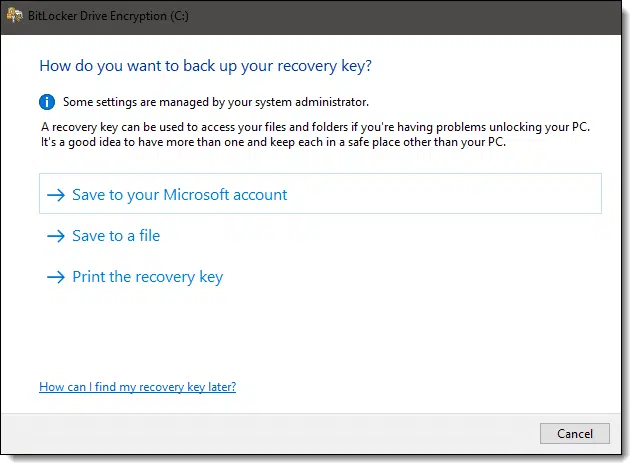
Again, while I can’t confirm the exact inner workings of BitLocker, I suspect it’s either:
- The actual key generated and used to encrypt the data on your hard drive (or some encoded variation thereof).
- A different password, not unlike your own, that can then be used to unlock the true encryption key.
Other programs
Many encryption programs operate this way. It’s easy to tell; if changing the password is quick, then they probably store a separate encryption key. If the password update takes “a while” (it depends on how much data has been encrypted), then it’s possible the actual encryption has been changed.
VeraCrypt, I believe, is one example of an encryption tool that allows changing the passphrase without re-encrypting all the data. Many password managers also operate in this way.
Drawbacks
The one drawback of this technique is that the key used to encrypt your data is stored on the same device as the data4. It’s encrypted separately, but if that key could be accessed by some other means — say, cracking its encryption, rather than the encryption used on the data — the key could be accessed and your data exposed. The argument against this being a risk is simply that strong encryption is used for both your data and the encryption key itself.
I want to say that’s enough and that the risks of this technique are minuscule.
Sadly, I could be wrong.
The issue is that the technique allows alternate access mechanisms in addition to your password to access the encryption key.
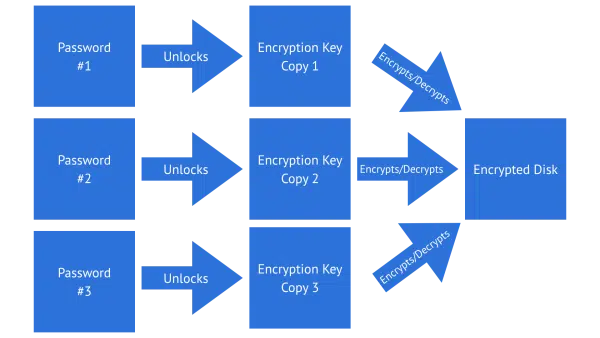
In the example above, three separate copies of the single encryption key used to encrypt the data are stored. Each copy is encrypted using a different password. Any of those three passwords could be used to unlock their copy of the single encryption key, thus granting them access to the data.
This might be how to implement a “master key” in a corporate setting. You have one password while your IT department has the master key. Either password can access the encrypted data.
This might be how your BitLocker recovery key works: it could just be a password to unlock another copy of the disk’s encryption key.
This might also be how you would implement a “back door”: encrypting (or worse, just storing) an additional copy of the encryption key accessible only to those who know of its existence, and possibly a backdoor password.
It’s currently theorized that this, or something similar, is what’s led to the recent BitLocker bypass exploit.
Do this
Choose good passwords or passphrases for your encrypted data, but don’t be alarmed if changing a password seems “too quick”. The more secure encryption key probably didn’t change, nor did it need to.
While you’re thinking about security, why not subscribe to Confident Computing? Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Footnotes & References
1: One place I do know a similar technique is used is in SSL network connections.
2: This is one reason that truly computer-generated random numbers are so important. If the generated key could be predicted, it loses its security.
3: Or something else to prove you are you. In our example, even if you don’t specify your password specifically, you’ve specified enough for Windows to be able to proceed.
4: I believe this is one of the more important uses of a TPM.
