Things are never as bad as the naysayers and media make out.
There are two answers:
- Almost by definition, the bad guys will always be in the lead.
- It rarely affects the average consumer directly.
The bad guys aren’t necessarily winning, but they’ll always present a challenge for the good guys.

Good guys and bad guys
The bad guys, or Black Hats, often seem to be ahead in computer security because they’re constantly finding new vulnerabilities. This doesn’t usually affect the average consumer directly. It’s a race, and the good guys, or White Hats, are always working to catch up. Although the media may exaggerate the severity of threats, by following basic security practices the average person can stay safe. It’s important not to panic and remain skeptical of sensational headlines.
Bad guys in the lead
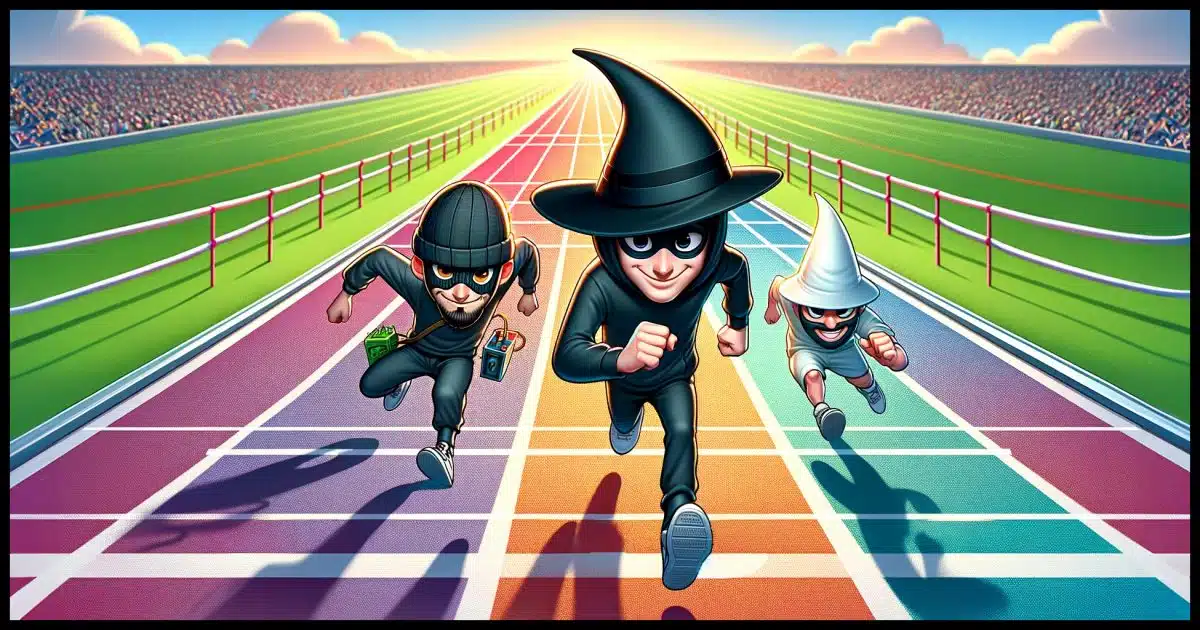
I’ve referred to this as “the race” before: the race between the good guys and the bad guys (the hackers). The bad guys are always in the lead. In fact, they can only be in the lead because they start the race. The question is by how large or small a margin.
First, we have to understand that there is no such thing as perfect software. None. Period.
Put another way, all software — even the best, most artfully written, most thoroughly-tested software ever — still has bugs. Most are small; some large; but there are always errors. This acknowledgment is not about resignation or giving up on the issue; it’s a reflection of the complex nature of software.
Ideally, software gets released with no known1 errors.
Then the bad guys discover one: a vulnerability they can exploit for malicious purposes.
And the race begins.
Help keep it going by becoming a Patron.
The media is not helping
In my experience, the media makes these discovered vulnerabilities seem like much more of an imminent threat than they are.
This is one of the reasons I’m mentioning skepticism more frequently of late — not just being skeptical of promises made in advertisements or spam email but being skeptical of news media reports on technology.
Things are rarely as bad as the headlines make them out to be. Remember, their goal is to get you to click and see an ad. The more frightening the headline and the more you think it might apply to you, the more likely you’ll click.
Yes, of course, the <latest scary-sounding vulnerability> could absolutely delete all your files, expose all your information, steal your identity, reveal nuclear launch codes, and who knows what else. And that’s exactly what you see in the headlines.
In reality, once made public (and often even before), vulnerabilities are quickly fixed, updates are quickly applied, and the malware exploiting the vulnerability rarely has the wide reach that the headlines scare us into believing.
Haters gonna hate
Just like the media likes to jump on every problem to exploit it for views, clicks, and likes, haters are no different. They just use every issue to say “I told you so” in the loudest possible voice. To them, that <latest scary-sounding vulnerability> just proves how incompetent the engineers are at Microsoft or Apple or Google (or whatever the target of their ire and agenda).
Again, things are never as bad as the haters would have you believe. They’re simply amplifying it to amplify their hate.
I’m not making excuses for Microsoft or Apple or Google or whomever — they do make mistakes, and occasionally big ones — but the haters shouldn’t be anywhere close to your primary source of information.
Pragmatic reality
In reality, the average consumer needs to do nothing more than follow basic security practices and not panic. Following those practices, people rarely experience any impact as a result of the latest news-making threat, and even if they do, it’s relatively minor and easy to bounce back from. (Especially if you back up.)
Are there outliers? Of course! Generally, folks who are impacted by the <latest scary-sounding vulnerability> didn’t follow security best practices and/or were specifically and individually targeted by hackers for some reason2.
Do this
Don’t panic. Never panic.
By definition, the bad guys are always in the lead, but all you need do is keep up the basic security practices you should already be following anyway and remain skeptical as you read the headlines and other online discussions.
Something else you can do: subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: Technically untrue. All software is released with known errors. The goal is that they are minor and of little impact. The tradeoff is, of course, the time it would take to fix them all.
2: I often refer to these folks as high-value targets. Unless you have some legitimate reason to be considered “high value” for some reason, it’s not you. If you’re not sure… it’s not you.







When I hear about the latest vulnerability that gets reported in the media, I’ll sometimes start looking into what it actually does. A lot of times it turns out to be some esoteric piece of software weakness that would require some action on the part of a user, direct access to the computer, or affects a server or system that I don’t even have. It would be of concern for an IT department running a big corporate or government network, but not me.
Also by the time these vulnerabilities do make the news, the problem has already been examined and an update made available if it is serious or the update is included in the regular update schedule if it is minor or only affects a limited number of users. Which means that if I keep my computers updated regularly, it is a non-issue anyways.
It does get interesting to read about some of these vulnerabilities as it does give some insight of what it takes to exploit them and how some systems work.
As Leo stresses in this article: “In reality, the average consumer needs to do nothing more than follow basic security practices and not panic.”
Internet Safety: 7 Steps to Staying Safe OnlineIt’s so important to practice safe surfing. Follow Leo’s advice in this article and book and you will rarely if ever get malware. I’m speaking from experience. I’ve been hit with malware only once or twice in the 21st century. I popped in my Macrium Reflect rescue disk and restored it from my backup. I went out shopping, came back an hour later, and the malware was gone.
Mark Jacobs said:
“I’ve been hit with malware only once or twice in the 21st century.”
The one and only time I’ve ever been hit with any type of malware was back in the late 1990s when I downloaded some software from a BBS. That event taught me a lesson I’ll never forget – “Never trust anything online (from the Internet)”. Being skeptical has become my favorite security-related watch word.
Ernie (Oldster)
The only malware I’ve ever had was on a Linux server many years ago.
So much for Linux being invulnerable to malware.
Why does software have ‘bugs’? Mostly because of the limited return. Developers spend days trying to get some software to actually work, after months planning and writing the software. Once they get the software to actually perform the duties it was designed to, they start testing for other ‘bugs’, if corporate management gives them time to. Many times the software is released knowing that there is unfound ‘bugs’. Why do they release before they have found all the ‘bugs’? Software that has not been released yet does not generate any revenue. Management is always pushing to release as soon as possible. The developers test for and find the big ‘bugs’, but cannot test all the configurations of hardware and software a person might have.