Signing in becomes a little more inconvenient. (But only once.)
Nope. Not at all.
If you lose your second factor, your next login just gets slightly more inconvenient…
…in a secure way.

Losing your two-factor authentication device
- Someone who finds your second factor does not have access to your accounts; they still need your password.
- If you’re using SMS two-factor, contact your mobile provider and move your phone number to a new device.
- Otherwise, access the account using recovery methods. Then remove and re-add two-factor with a new code or device.
Two factors means two factors
Remember, two-factor authentication needs two factors to sign in.
Even if hackers have your password, they can’t sign in without your second factor. This is the reason I so strongly recommend two-factor authentication.
But the converse is true as well: if hackers have your second factor — say they stole your phone or found your YubiKey — they still can’t sign in without your password.
Both factors are required. If they don’t have both your password and your second factor (whether that’s a device, an app, a code, etc.), your account remains safe.
So there’s no need to panic if you lose that second factor.
Help keep it going by becoming a Patron.
Accounts using SMS-based two-factor
SMS-based (text message) two-factor authentication is the easiest to deal with. SMS two-factor is based on your phone number, not on your specific phone.
If you lose your mobile phone, reach out to your provider, get a new phone, and transfer your existing number to the new phone. You’re done. Your two-factor notifications will now arrive on your new device and not your old one.
If you don’t get a new phone immediately, contact your provider as soon as possible and disable your lost phone. This prevents whoever has it from getting your SMS messages… or anything else.
It’s conceptually simple, and covers all accounts that use SMS two-factor authentication.
For other accounts: first, regain access
Some accounts don’t use SMS notifications for the second factor. For each account you have that uses a device or an app as its second factor, you need to sign in and set a new second factor.
For some accounts, you’ll already be signed in and can proceed to the next step right away. For others, when you sign in, you’ll be asked for your second factor.
If you use a tool like Authy on multiple devices — like Windows and your mobile phone — you can sign in using the two-factor code provided by one of the other Authy installations. (This, and the ease of moving to a new phone, is the big benefit I see using from Authy.)
If, however, your second factor is only a single device — such as only your mobile phone or a single, specific, USB security key — then you no longer have the second factor you need to sign in.
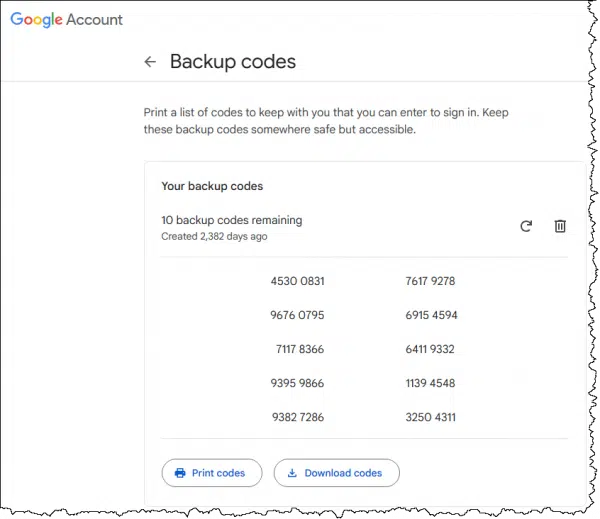
When you set up two-factor authentication, you should also have also set up a recovery mechanism. Most services almost insist that you do so.
That may be an alternate email address, an SMS-enabled phone number, a single recovery code, a collection of one-time use codes, or even an additional two-factor device. Use that mechanism to sign into your account. (And if you haven’t set up a recovery mechanism, go do it now.)
This is what I meant about signing in being more inconvenient: you’ll need to jump through one of these additional hoops to sign in without your second factor. It’s secure because only you have access to those hoops used for recovery.
Then, reboot two-factor
The goal is to invalidate existing two-factor devices and re-establish a new one.
In most cases, that’s a two-step process: turn off two-factor authentication and then turn it back on again. It’s kind of like a reboot.
Turning two-factor off accomplishes the first goal: any pre-existing second-factor devices, codes, or associations are disabled and forgotten. The codes provided by previously configured two-factor applications like Authy will no longer work. You also need to delete any entries for the account in authenticator apps you still have access to. Any recovery codes and such will also be invalidated.
Your account will, for a brief moment, not be protected by two-factor authentication. That’s why the next step is important.
Turn two-factor back on. This establishes a new code you can use with your two-factor app, a relationship with a replacement hardware key, or whatever two-factor technique you use. Your account will once again be properly protected by two-factor authentication.
Do this
Having someone else gain access to your second factor is similar to having someone else discover your password.
What do you do when your password is compromised? You change it.
What do you do when your second factor is compromised? You reboot it.
As long as both are not compromised by the same person at the same time, your account remains secure throughout.
Looking for more security tips and safety nets? Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.





On my device, I have Google and MIcrosoft authenticator. I have scanned the QR codes for a couple of different websites. If I need to replace my device and reinstall Authenticator, will it still have the QR codes for those different websites?
– Genuine question- a little bit confused?
No, you will not. You will need to:
In the past I’ve screen-shotted the QR code and kept that in a safe location so I didn’t have to jump through these hoops. Also QR codes are just a representation of a code, which some make visible as text (also, or optionally). Saving that text code works as well.
Hi Leo, thanks for this article, it is eye opening. I like to make an addition on the answer of the comments from Chris.
I just have been given a new smart phone and I have a different experience with my Authy authenticator.
I used Authy on my smart phone, tablet and PC; so plenty of recovery options. Now with my new Phone, I installed Authy App and logged in, with authy credentials. Then, Authy immediately picked up the codes and started working properly given correct 2FA codes. I guess this is the advantage of Authy!
The upcoming DISadvantage to Authy is that they’re discontinuing their desktop application.