Simpler than it sounds.
Security experts often express concern about something called credential stuffing. It’s a way hackers gain access to online accounts.
The good news is that it’s easy to understand.
The better news is that it’s easy to prevent.
The bad news is that too many people don’t.

Credential stuffing
Credential stuffing is when hackers use stolen login information from one site to try to sign in to other sites. You can prevent it by using unique passwords for every site, ideally managed by a password manager.
Credential stuffing in simple terms
Credential stuffing is nothing more than using your credentials (login ID and password) from one service to attempt to log in to other services.
Say you have a Gmail account with username “example@gmail.com” and password “areallygoodpassword”. Somehow your Gmail credentials are compromised and end up in the hands of a hacker.
A credential-stuffing attack looks like this:
- The hacker tries to sign in with “example@gmail.com” and “areallygoodpassword” at Outlook.com.
- The hacker tries to sign in with “example@gmail.com” and “areallygoodpassword” at Facebook.com.
- The hacker tries to sign in with “example@gmail.com” and “areallygoodpassword” at a popular bank.
- And so on and so on …
IF you used the same email address and password at any of the online services the hacker attempts to sign in to, they gain access to the account. It doesn’t even matter how good that password is.
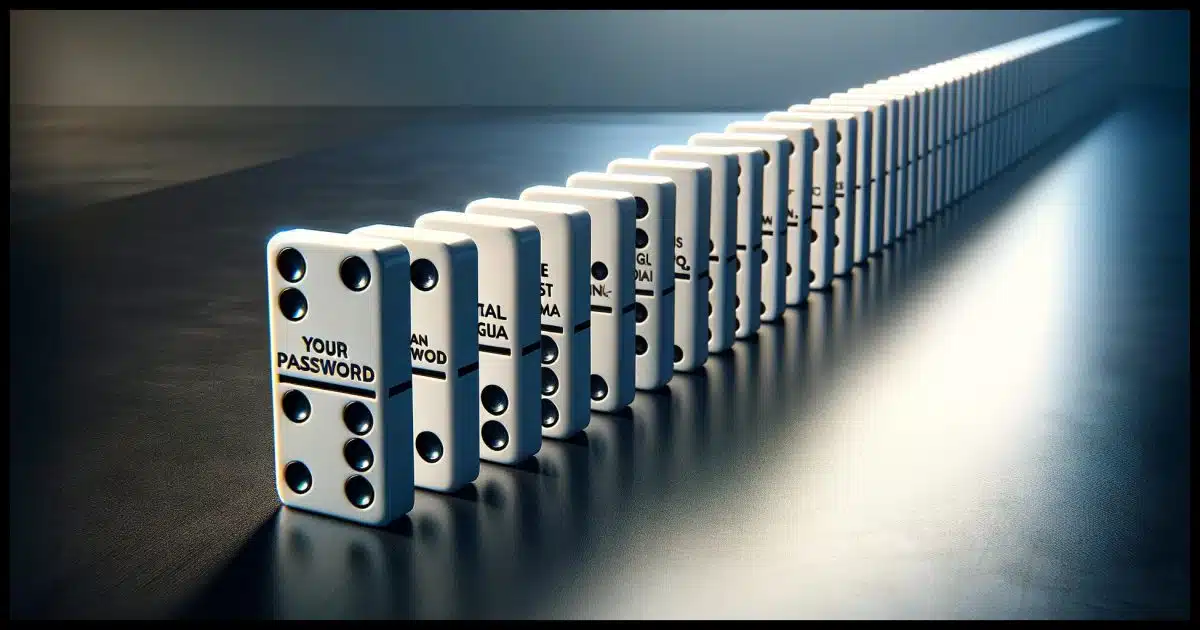
Think of it as a row of dominos. Tip the first one, and the rest follow and fall.
It’s a popular attack. The reason it’s popular is because it works.
Help keep it going by becoming a Patron.
Prevent credential stuffing
You can already see where this is going. The attacks are successful because people use the same password for more than one site.
To protect yourself, don’t do that. It’s as simple as that.
Use a different password for every site or service that requires one. That way, if any of your credentials are compromised at one service, the damage is limited to that account.
Cue the objection: “How am I supposed to keep track of all these different passwords?”
That has a simple solution as well.
Use a password manager
I don’t care which one1, but password managers (AKA password vaults) are the solution.
You don’t have to keep track of all the different passwords; your password manager does it for you. You don’t have to dream up secure passwords; the password manager can do that for you. Your passwords can be longer than you can remember; the password manager can make ’em long and strong.
Password managers are safer than every other alternative.
And they’re perfect for preventing credential stuffing.
Do this
Use different passwords for every online account. Use a password manager to keep track of them.
You’ll no longer be vulnerable to credential-stuffing attacks. It’s as simple as that.
Also simple: Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
![Why Password Managers Are [Still] Safer than the Alternatives](https://bcdn.askleo.com/wp-content/uploads/2021/01/vault-1-300x158.jpg.webp)




Unfortunately, Google is actively trying to proliferate credential stuffing by getting you to use your Google credentials to log into just about every witesite. So does Facebook. Don’t do it. You’re not in good hands.
Don’t some sites leave some kind of token behind on your device if you check the “remember me on this device” box when signing in the first time? This should prevent a sign in attempt from another device and result in a notice to you I would assume.
It’s in a cookie, but has no effect on signins elsewhere.