Why would they?
Yes, they can.
The real question is, would they? Probably not. And yet there are new concerns they might occasionally even be required to.
If it’s of real concern to you, what might you do? I have some ideas.
Become a Patron of Ask Leo! and go ad-free!

Monitoring your internet connection
Employees at ISPs technically have the ability to monitor your online activity, but it’s unlikely they would without a reason. To further protect your privacy, a VPN is a common recommendation. Using a VPN transfers the visibility of your activities from your ISP to the VPN provider, giving them the same access as your ISP. Governments may require ISPs to log user data, but the specifics vary and can change frequently. Most folks need not take protective measures.
Your ISP
If you have a connection to the internet, it’s provided by an ISP; that’s what the acronym stands for: Internet Service Provider. Be it your work, school, phone, or cable company, your internet service is provided by someone, and that someone is your ISP.
Not only do they provide your internet connection, but they completely control it.
Your ISP knows a lot about you. Traditional ISPs, like telephone and cable companies (and quite possibly many “non-traditional” ISPs, such as wireless providers and others), know where you live so as to be able to set up your connection physically (not to mention know where to send the bill).
As I’ve said over and over and over and over, to locate you by your IP address typically takes law enforcement and a court order. Where do they take that court order? To your ISP, to reveal your physical location.
Monitoring your connection
Your ISP controls the equipment your internet data flows over once it leaves your location. You connect to your ISP, and your ISP routes the data to where it’s supposed to go elsewhere on the internet.
Can they “sneak a peek” at your data while they route it? Yes, they can.
The question is, would they?
Folks, I’ve said this before, too: we’re just not that interesting. Why would anyone spend time looking at terabytes of data just so they can spy on your surfing habits or email? Most ISPs are overworked enough without adding some kind of electronic voyeurism to their job.
In my strong opinion, most people don’t need to protect themselves from their ISP.
Protecting your connection
OK, what if you still want to protect yourself? What if you have a legitimate reason for being paranoid?
There are several things to consider.
- Secure connections. Any connection beginning with https, which is most web connections these days, is an encrypted connection. While your ISP can see which sites you are visiting, like askleo.com, the data sent to or displayed from the website is hidden from them. Using an https connection to an email service like Gmail is one way to secure your email from snooping by your ISP.
- Anonymous web surfing. If you use services like Tor, your ISP can tell you’re using an anonymizing service, but they cannot tell anything more than that — everything’s encrypted. It’ll be slower, but it’ll be encrypted. Of course, you’re trusting the anonymizing service not to snoop on you.
- Encrypted email. There are several ways to send encrypted email (though sadly, none are particularly easy). Your ISP will be able to see who you’re emailing, but your message will be encrypted and hidden.
A special note about VPNs
The most common response to this issue is to use a VPN, a Virtual Private Network.
When using a VPN, everything between you and the VPN service is encrypted. Anyone between you and the VPN service, including your ISP, can’t see a thing. It’s a common recommendation when using an open hotspot or other untrustworthy internet connection.
There’s a big issue that’s commonly overlooked: in a very real sense, your VPN becomes your ISP. As a result, the VPN service can see everything you’re up to, just like your ISP could without the VPN in place.
In other words, do you trust the VPN service?
One area of concern
Some governments require ISPs to keep information about your internet habits. Anything your ISP can see is potentially logged to be available should those governments come knocking.
What’s kept? Which ISPs? How long? Which governments? There’s no way to know with certainty. The landscape changes often, and today’s answers to any of these questions may be different tomorrow.
Once again, I maintain that most of us simply aren’t that interesting, and aren’t likely to be doing anything warranting the interest of your government, much less your ISP.
Do this
It comes down to a pragmatic risk assessment. Are you likely to be targeted by your ISP or government? For the vast majority of us, the answer is no. We need do nothing.
On the other hand, if you do believe you’re at risk, the options above, carefully considered and implemented, can provide you with some measure of privacy.
While you’re ahead, why not subscribe to Confident Computing!? Less frustration and more confidence, solutions, answers, and tips in your inbox every week.





Hi!…
.
Are persons being tagged on the Internet (by whomever… and e.g., by anti-SPAM groups such as Akismet and the The SpamHaus Project [and their software], or by groups who hate the users of the Tor Browser) to the extent, that those being tagged are neither able to send or to receive anonymous emails, or emails generally? And if so, how would those being impacted be able to communicate anonymously or even overtly their victimization, or even know that sundry of their “sent messages” are not being received?… and how many of the netizen community (and even Human Digital Rights Advocacies!) would even be able to learn (anonymously, or overtly!) what’s going on?
Not that I’m aware of. Seems pretty conspiracy-theory to me.
It has been almost 10 years since I received a letter in the mail from my ISP, Comcast. An individual in my household had been downloading movies and videos using BitTorrent to do so. And yes they were illegitimate copies.
The letter, as I recall, not only was a warning to cease and desist, but also informed me who the culprit was. He wasn’t happy about it, but it was either stop or lose internet service for the household.
I’m positive that ISPs have software that monitors internet traffic to customers and that software is capable of flagging suspicious looking traffic, probably by volume. It is a minor reason that I do not use Comcast/Xfinity’s gateways. It is less expensive to have my own cable modem and router (no rental fee) and Comcast can only see the modem, not the router and the settings and password for the router. Even a retail gateway approved by Comcast allows the ISP access to the security settings and network passwords.
It’s not necessarily the ISP monitoring for pirated files. Bit Torrent programs allow you to see all the seeds and peers you are sharing with. Film Studios and Music companies search for torrents of their products and monitor the traffic. They, then, get a court order get the names and addresses of the up/downloaders. This happened to a friend.
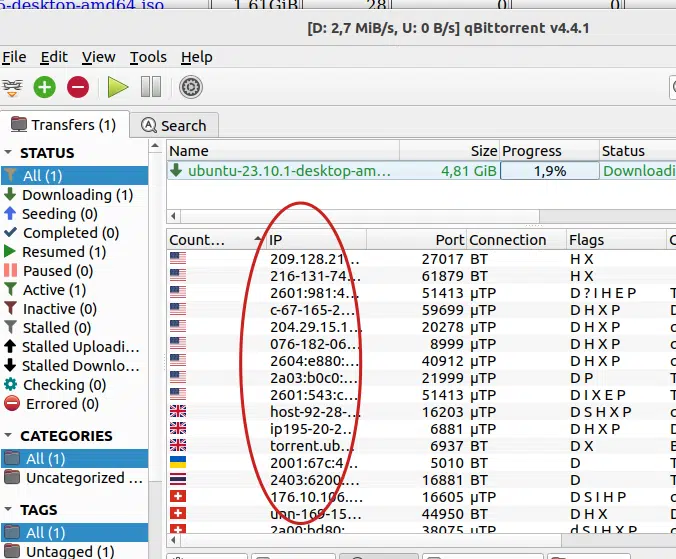
At the time we were using a Comcast approved gateway/router. There was no court order involved, just a letter from Comcast specifically identifying the user and the IP address of his computer and including a paragraph that Comcast would cancel our account if he didn’t stop downloading using torrents. Ten years later, he still grumbles about it.
I logged into the gateway and verified his IP address on our network. That’s when I decided to use an Arris T25 gateway and a TPLink router. Comcast can see the T25 but cannot see anything behind the router firewall. Comcast touts being able to provide remote troubleshooting with gateway issues and also use their gateways as mobile hot-spots, which customers have no control over. Customers can change SSIDs and network passwords, but they can be seen by Comcast and reset remotely.
We’ve not had an issue with any notification letters since I switched over to the T25 and AC1750. I’m not necessarily paranoid, but I prefer to know who is on my network without Comcast having access.
If the individual in your household had been using a reliable, no logging VPN this wouldn’t have happened. Comcast would have been able to identify he was using a VPN but that’s all. The IP addresses shown in qBittorrent are the addresses of either the actual user (if the user isn’t using a VPN) or the VPN’s server if a VPN is engaged. Since hundreds or thousands of users are using a VPN server at the same time it’s very difficult, if not impossible, to single out one user. Unless you’re a terrorist or some type of serious neer-do-well nobody’s going to bother trying. When using bittorrent it’s often difficult to tell whether the files you’re downloading are copyrighted or not. Thus it’s always prudent to use a VPN for such activity.
This all happened almost 10 years ago. What their current practices are, I don’t know. What bothered me as the one responsible for the account about the situation was that Comcast/Xfinity could see everything connected to the internet in my home, had access to all WiFi passwords and SSIDs and had the ability to remotely reset everything when using their equipment. Comcast also was specific as to who the user was by name and the IP address of his computer on our home network.
Using my own cable gateway and a separate router, Comcast can only see the gateway and nothing behind the router’s firewall. I prefer to have more control over my home network and the security of it. Comcast can still see the traffic coming to and from the home, but not the individual computers and users in the home. And, yes the individual involved did start using a VPN.
Comcast recently suffered a security breach and subsequently required customers to change passwords and encouraged enabling 2FA, which we were already doing.
This was an early lesson of just how much information was available to an ISP when using their provided equipment. I’ve come to believe Comcast did this more as a warning that they could do this. But, I still don’t trust them to not snoop around.
Most ISP’s have their employees sign a document specifying how they can use User Protected Data. That includes your usage of their system, as well as credit cards and addresses. If an employee tells others about what they have seen on an account, activity or otherwise, they can be fired and taken to court. Employees of ISP’s may, depending on their job, have access to your usage, rarely what you are actually doing, but where you are doing it. Unless you are a celebrity, like Taylor Swift or Trump, the odds of somebody looking at your account to tell somebody else your activity is slight. We just don’t care.
Think of your phone company tracking what numbers you called and where they are. Cell phone companies can even track where you were calling from when you made or received the call. They cannot listen to what you were saying, unless there is a court order for a tap.
Here, on AskLeo, we’re mostly talking about home users and perhaps small business operators. With that perspective, using a VPN for “privacy” suggests you trust the VPN provider more than your ISP. Your ISP is a probably a big name company, but most VPN providers are shell companies owned by other companies you’ve never heard of. So, you trust an online company (website, actually) over a regulated utility. You believe that the VPN company doesn’t eavesdrop or collect usage information. You believe that the VPN company’s database is less likely to be hacked. You believe that law enforcement can’t access your usage from the VPN company. Think again.
There are a few good and technically advantageous reasons to use a VPN service, but “privacy” for home users isn’t one of them – unless you really don’t trust your own ISP and have good reason to believe so.
Call me a puritan, but if you are not doing anything wrong, why is there a need to worry who is looking? If I was into dirty content, illegal operations, or stealing music and movies, then yes, but why not pay for it legally? As I have seen Leo say before… if you do nothing wrong, the authorities are just not interested in you (or similar).
Those aren’t the only things the average user needs to worry about. Bank accounts, Social Security numbers, credit card numbers, passwords, etc. are hacker targets.
My concern would be with them having access to banking and other sensitive personal finance sites and pages. If they can see that kind of stuff, you are at the mercy of the employees of the organization.
All banks I know of use SSL (HTTPS:) end-to-end encryption, so the data is encrypted before it is sent from your computer and is decrypted by the bank. It all appears as gibberish to anyone sniffing the connection including at your ISP. If your bank doesn’t offer that (as I said, I don’t thing you’ll find one that doesn’t), switch banks immediately.
As long as the connection is https, they can see what bank you connect to but they CANNOT see any of the data.