Articles in Category: Email Security
Keeping your account, your contacts and the contents of your email private, safe and secure.
Why Am I Being Asked for Additional Verification on Sign-in?
Traveling and suddenly locked out of Outlook.com? I’ll explain why Microsoft asks for extra sign-in proof, what “something unusual” really means, and how to set up backup email, phone, or authenticator options before you leave so you can get your code and your account back when it matters most.
Searching for a Technical Support Support Phone Number? Avoid This Huge Trap
I’ll explain why searching for a tech-support phone number is one of the most dangerous steps you can take when you’re looking for help.
Could Someone Reopen My Closed Email Account?
Closing or abandoning an email account can have unexpected and perhaps unwanted side effects. I’ll explain what those are and what options you have.
How to Send Email from Your Own Domain (Without Getting Blocked)
Anti-spamming measures complicate email. This makes sending “from” your custom domain a little trickier.
Why Do I Need Another Email Address to Access My Account?
This is a system designed to help you recover your email account if something should go wrong… and things go wrong more often than you would like to think.
Can My School See My Email and Other Messages?
Numerous people and programs can track your internet activities. But are you really that interesting?
What Is Modern Authentication?
OAuth2, aka a “Modern authentication method”, removes the burden of authentication from the email program to the email service itself, enabling a number of important security features.
Are Zip Files Safe to Open?
ZIP files are useful for compressing and containing collections of files. Unfortunately, they’re also useful to hackers, spammers, and scammers.
Has a Hacker Really Hacked My Email Account?
An email claims your email account has been hacked, possibly even including a password you’ve used. Don’t be fooled; it’s a scam.
Why Am I Getting Email from a Dead Person?
It’s hard enough to experience the loss of a friend or a loved one. To get email from them thereafter can be very disturbing.
Can I Get Malware From Opening an Email?
It used to be that simply viewing a malformed email could allow a virus to spread. Thankfully, that’s no longer the case.
Can You Make an Email Without a Phone Number?
There are legitimate reasons for not wanting to give your phone number to an email service. Let’s look at alternatives.
Will I Lose My Account If I Don’t Set a Recovery Email Address for My Google Account?
Recovery email addresses are an important safety net. Here’s what you need to do.
How Can I Send an Attachment If It’s Blocked by the Recipient’s Email Program?
Many email programs try to protect users from malware by blocking certain kinds of attachments. What if you’re sending something that’s legitimate, but blocked?
I Enabled Two-Factor Authentication and Now My Email Program Can’t Sign In
Two-factor authentication is an important security tool. To access those accounts in some programs, though, you may need an app password.
My Email Is Hacked, How Do I Fix It?
If your email is hacked, there are several steps you need to take to get it back and prevent it from being hacked again.
If Someone Hacks My Gmail, Can They Hack My Other Accounts?
If someone has access to your email, they can use that as a starting point to hack your other accounts.
How Secure Is Email?
Email is ubiquitous and convenient, yet surprisingly, not particularly secure. I’ll look at why that is and when you should worry.
I Know My Password Is Right, But I Can’t Sign In. What Do I Do?
If your password won’t work and your secret questions are different, it’s pretty clear what’s happened and what you need to do.
Why Would Someone Use My Email as their Recovery Email?
It’s not uncommon to get account-recovery requests for accounts we know nothing about. Here’s why, and what to do.
5 Reasons Your Closed Email Account Sends Spam
Closing an email account is many people’s first reaction to seeing spam sent from their account. It rarely helps, if it’s even possible. I’ll explain.
What Recovery Email Address Should I Use?
Your recovery email address is easy to overlook and forget, but it can be critical to regaining access to a compromised account. Here’s what you need to do.
What Should I Do When My Information Is Involved in a Breach?
If your account is ever part of a breach, secure it to avoid further risk.
How Do I Keep Outlook.com from Locking Me Out When I Travel?
When your email is suddenly accessed from a new location, it could mean someone other than you is trying to log in. Email providers like Outlook.com watch for this.
Why Does Thunderbird Think this Message Might Be a Scam?
Occasionally, security software examines links in email and alerts you if something is suspicious. Frequently, it’s totally benign.
Dealing with Fake “Ask Leo”
Someone’s sending spam that looks like an Ask Leo! recommendation. It’s not, and it gives us clues to keep in mind when evaluating any email message.
How to (Accidentally) Give Someone Else Your PayPal Account
Entering your email address incorrectly might just be a typo, but it can have surprising ramifications.
Will a Hacked Website Leak My Email Address?
Your password protects your account from unauthorized access, but it doesn’t protect your email address from exposure.
Who do I contact for legal help?
I get questions like this all the time. Individuals’ accounts have been hacked and they want to know who did it, or they already believe they know. And with that knowledge they want to do something. Typically, they want to see the offender get punished in some way. Sadly, life on the internet just isn’t … Read more
Why am I getting Amazon notifications for someone else?
It’s pretty scary that you are getting notifications from someone else’s account – but not scary for you!
How Do I Force My Email Account to Close on Another Device?
There are possibilities here that are, perhaps, even more unsavory than having someone you know reading your mail. So first things first!
Is it worth upgrading to get Windows XP Mode?
Installing a recently unsupported operating system so you can use an email program that hasn’t been supported for years is something I’ll advise against. There are safer ways to go.
Why Does this Email Message Ask Me to Enable HTML When It Already Is Enabled?
Viewing an email in HTML seems to be the default in the new Outlook.com. There is no easy way to change it. So why are you seeing this message?
Why is mail getting automatically placed in a folder I didn’t create?
If you didn’t change the folder rules, then who did? I’ll show you how to fix this problem.
If My Email Account is Hacked, What Kinds of Things Should I Check?
When a hacker has access to your email account, they can do anything — even change settings you know nothing about. Let’s take a look at some of the possible dangers.
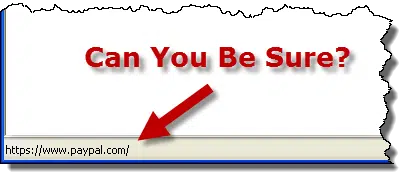
Can I Rely on the URL Shown in the Browser’s Status Bar Being Accurate?
There are both legitimate and malicious reasons why a link author may send you to a place that is different from the link showing in the status bar. Let’s look at why that may happen.
Did Someone Log In to Google with My Password?
It’s frightening, on the server side, to watch the constant attempts being made to slowly brute force a way into email accounts. So it’s safe to assume that if Google notified you – someone got in!
How Do I Protect My Email Address Book?
With email account hacking on the rise, it’s important to understand what it takes to keep your account (and its address book) safe from compromise.
My mail account has a virus, how do I get rid of it?
Email accounts don’t get viruses. Depending on what you’re seeing, though there is something that email accounts do get, and that is: hacked.
How Can I Trace Where Email Came From?
A good rule of thumb is to begin at the bottom and work your way up in the headers to determine where an email is from.