You may not be able to, but there may be clues
I frequently get questions that boil down to “How can I trace where this email came from?” or “Can I determine the IP address of the sender of an email?”
The answer is both yes, maybe, and it may not do you any good. However there is a lot of interesting information in your email that you normally don’t see, and the trail of mail servers is part of that.
So let’s interpret some email headers.
Getting headers
First, there’s the challenge of even getting to the real email headers. Depending on your email program or interface, look for items like “Show Original” or “Show headers” or something similar.
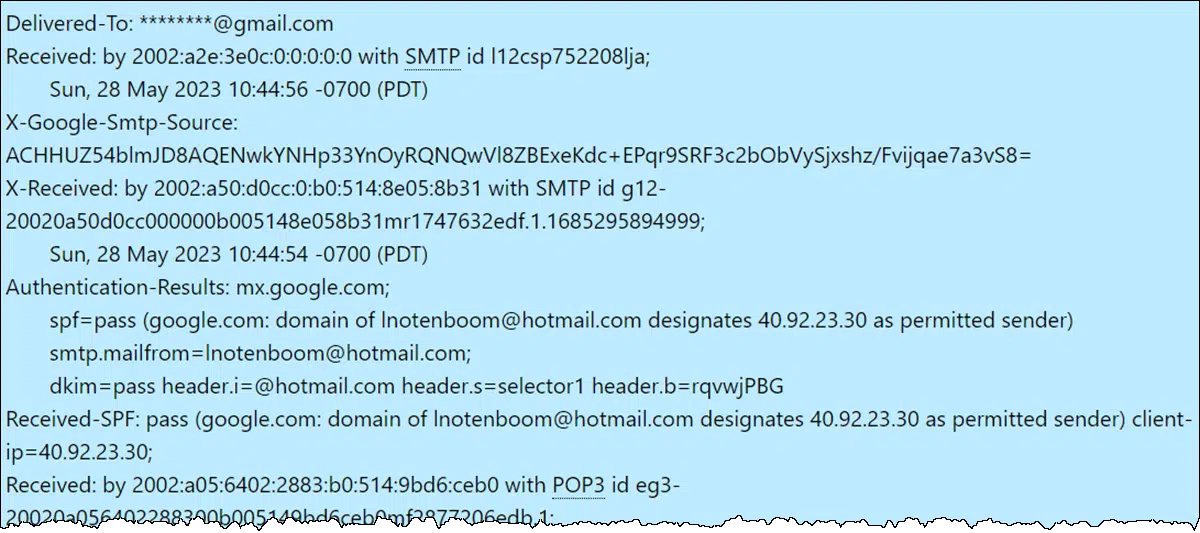
Here’s a rather lengthy example:
Delivered-To: ********@gmail.com
Received: by 2002:a2e:3e0c:0:0:0:0:0 with SMTP id l12csp752208lja;
Sun, 28 May 2023 10:44:56 -0700 (PDT)
X-Google-Smtp-Source: ACHHUZ54blmJD8AQENwkYNHp33YnOyRQNQwVl8ZBExeKdc+EPqr9SRF3c2bObVySjxshz/Fvijqae7a3vS8=
X-Received: by 2002:a50:d0cc:0:b0:514:8e05:8b31 with SMTP id g12-20020a50d0cc000000b005148e058b31mr1747632edf.1.1685295894999;
Sun, 28 May 2023 10:44:54 -0700 (PDT)
Authentication-Results: mx.google.com;
spf=pass (google.com: domain of lnotenboom@hotmail.com designates 40.92.23.30 as permitted sender) smtp.mailfrom=lnotenboom@hotmail.com;
dkim=pass header.i=@hotmail.com header.s=selector1 header.b=rqvwjPBG
Received-SPF: pass (google.com: domain of lnotenboom@hotmail.com designates 40.92.23.30 as permitted sender) client-ip=40.92.23.30;
Received: by 2002:a05:6402:2883:b0:514:9bd6:ceb0 with POP3 id eg3-20020a056402288300b005149bd6ceb0mf2877206edb.1;
Sun, 28 May 2023 10:44:54 -0700 (PDT)
X-Gmail-Fetch-Info: leo@pugetsoundsoftware.com 8 mail.pugetsoundsoftware.com 995 leo@pugetsoundsoftware.com
Return-Path: <lnotenboom@hotmail.com>
X-Original-To: leo@pugetsoundsoftware.com
Delivered-To: leo-pugetsoundsoftware.com@ec21.pugetsoundsoftware.com
Received: from NAM12-MW2-obe.outbound.protection.outlook.com (mail-mw2nam12olkn2030.outbound.protection.outlook.com [40.92.23.30]) by ip-172-31-17-218.us-west-2.compute.internal (Postfix) with ESMTPS id 110B43EDA7 for <leo@pugetsoundsoftware.com>; Sun, 28 May 2023 10:44:31 -0700 (PDT)
Authentication-Results: ip-172-31-17-218.us-west-2.compute.internal; dkim=pass (2048-bit key; unprotected) header.d=hotmail.com header.i=@hotmail.com header.a=rsa-sha256 header.s=selector1 header.b=rqvwjPBG; dkim-atps=neutral
ARC-Seal: i=1; a=rsa-sha256; s=arcselector9901; d=microsoft.com; cv=none; b=nMpyQYEpO8XO662sHkSehsUO6bGLK5ayE+QlmBDkRgg4WaJt4erHl9ncGXfHn8bu5w0LLrQopczGi34GzJ8jIduOCnDzZ65471C4dXnWxTiXNrCleKv5QZwE+TRO2+Zbhx/x0XgOgYQT7JctNJo/9jD5PHRyUxu7r2bDuegg88Q1YO/1ADIxqUmxtRq8LhXo1SaQokF1pG0aagfHZd/th6rBk1RQPWf7GGk5Ff69GFp3Wp+BY16usQNcaZJ0DQqaNJxLZ05jNIIe3jc/b8DNWzyCNVZrYXuupTZej7t2rsSpKcFDWmeUXaIn7KHhI8MJwXPoDFWPVgOmJyzRidYIHQ==
ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=microsoft.com; s=arcselector9901; h=From:Date:Subject:Message-ID:Content-Type:MIME-Version:X-MS-Exchange-AntiSpam-MessageData-ChunkCount:X-MS-Exchange-AntiSpam-MessageData-0:X-MS-Exchange-AntiSpam-MessageData-1; bh=+Lh76dB/N6CxzAWlwUtgFiqBtyHhR4SRmOHu5IjfHRc=; b=WjDLpWOLqfggv/2SQ1kE8874i+9SMYQ/MEpCgqopqbmCbe/xGHDitwYUjkKI74ivyr2vMo58oY8OwN4fFnX3rSIqHsDinbIyAJBbowWr/scUGxNFx2OsCvQJGIm2muWCsBzZns+rgMoWp/vNMLe32FOmroqQ415EQ+85k4e/ecetVZnBYprt9haRu3VWoaMi5suKp4uTHmeRXAHaFRFC2PF5VT6IYkQ8cxZcAkE846BWfZTkQ8JgMMzw3SoATg3s+Gy5Y/PUpV3p3GSDGVRn4k7VCkimTvyvKOegp3fhH5QRIyncwasuuJ2NE3Agbuz34yweL+d4s1wInUFk4Fqj0w==
ARC-Authentication-Results: i=1; mx.microsoft.com 1; spf=none; dmarc=none; dkim=none; arc=none
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=hotmail.com; s=selector1; h=From:Date:Subject:Message-ID:Content-Type:MIME-Version:X-MS-Exchange-SenderADCheck; bh=+Lh76dB/N6CxzAWlwUtgFiqBtyHhR4SRmOHu5IjfHRc=; b=rqvwjPBGkdNEvPb6tAotTTGhaYdiMX7h8fDAoqdW85GTtv3qVOGVGjX77Dwg2NA5hDXrQMg74I16cs0tcgQmLWDXAawh8Yx+Bs5Igs78T/DDL9RhXVyD61MbeX+G/3+uuxg+Xa4Ivj+kSLquUfq1jUvKDd3GccL+H5um0T7kVVjQcsIeSBMSl3SyEH9sJJKF6lpoF6X0TMubBJavAExEuiMx9kVOTHUOESSXGMPXg7I9YXCMAds8NF1gHMPxnKRbjEgjehwkYZsW6TbE8plW0ZllUfgZHIFR/7qAXFEvV6ysw5KErrxKQmyN1ET4xGIJjOc97LQawSv9K7hMc6zoWA==
Received: from MW4PR19MB7031.namprd19.prod.outlook.com (2603:10b6:303:228::16) by SJ0PR19MB6678.namprd19.prod.outlook.com (2603:10b6:a03:44f::22) with Microsoft SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id 15.20.6455.12; Sun, 28 May 2023 17:44:29 +0000
Received: from MW4PR19MB7031.namprd19.prod.outlook.com ([fe80::9f2a:c282:3c86:681d]) by MW4PR19MB7031.namprd19.prod.outlook.com ([fe80::9f2a:c282:3c86:681d%4]) with mapi id 15.20.6455.012; Sun, 28 May 2023 17:44:29 +0000
From: Leo Notenboom <lnotenboom@hotmail.com>
To: “leo@pugetsoundsoftware.com” <leo@pugetsoundsoftware.com>
Subject: This is the subject line of the email.
Thread-Topic: This is the subject line of the email.
Thread-Index: AQHZkYwI0wxJiQ9egkeTpacLL/Q7LA==
Date: Sun, 28 May 2023 17:44:29 +0000
Message-ID: <MW4PR19MB70311D8A4C956B9341595652D2459@MW4PR19MB7031.namprd19.prod.outlook.com>
Accept-Language: en-US
Content-Language: en-US
X-MS-Has-Attach:
X-MS-TNEF-Correlator:
msip_labels:
x-ms-exchange-messagesentrepresentingtype: 1
x-tmn: [45zwzglZHWlrONuqhfOJVC+BHfwdOnYG]
x-ms-publictraffictype: Email
x-ms-traffictypediagnostic: MW4PR19MB7031:EE_|SJ0PR19MB6678:EE_
x-ms-office365-filtering-correlation-id: cc519a00-8b95-4404-b143-08db5fa33053
x-microsoft-antispam: BCL:0;
x-microsoft-antispam-message-info: Glpl3bwWCdU2LoFKHH+wAZ5ANc5tCoVIGiJfD5P1xojHc5cEe+nO6awNXxNR9v3oj6vMSwnvUjf3VcSr7Zgc0IIFZaw4n6nothQ9NYvfL04WhSrmODB3ajRJNl7lF+xERXyBUpQ7SUbEydi2LMTF93HVEsN6SOFConfI/tARzdHuaVkqz6hxW96+Uo3BsQF1p8wcnOrjIrA+8vaKWbYZiYaqyE+/az7lNw8ddy0ByRrSylx8S6XaoI1sBhrJAatq8TitgG9diMsdnU93UC3tfVCJnkvGpBxxQTMVKvgIgOKuEMcwKJks7Lncn7XM0tpQ1H4zui0WP8CL3RiLO9iO0aVJzAn1qD9ZwnFlx+PK2G4d2HK6TRt2PR8LJdSd85VyzGaARfSCHTobHHAcWuYvnXfzhnR5XyJRGm21wc/Y/CbKiwIabffqLNCnW8meiVH4Bz2UZ3fnBkfDU3ejbp9tkrR4A0C7/Z02949kb4PMu6ossWprM1OvjqLjcqBjND6Djrn4QnFEJZptRzLtgXxozexft4rRiQWbezpz27Kz35/0eG+H0Kx0L8X9eQmqvjRNlFM2e9MyGXZRs4cn5SCtzCFSZwuhffAzyC/mYVZhl5E=
x-ms-exchange-antispam-messagedata-chunkcount: 1
x-ms-exchange-antispam-messagedata-0: 7Y9mlcHFcH7x/fiTq/lF9TM6ciVmyxqotiyLtc4pDkaGBvikpP95W0qvwZPgct5NU+Ft1i7npFHo1+pwv+RKdYJtmBFj3mBLHlSNSfFWLzf/q+wEmVV1Om7XYMHOta4OFyJUyBvJXj5U2WNzed0yK8c7QOHNRBbas1uLbPf1SEUQOnlciFiHmrEy/t3VnW9kN0ou5S7WkLC7NFwwSf+cT34IKg4t1xiMys8D9p0r1N55S/DfDgYR4OLkMPfHIuEKgyaj/J48EO19uWoW1xdOCcXPLksJsTz0+1VZ3cNlOI1r702YHR7g7JozrEaHPBk+ECYfOm2rG1j+iFjK0s7CvpYLxvUeguV+Suqx62/Yy1rE52pUYWp0PxJkHMUdyLjgEQriD5i6LBgQjqS1i1a/RW6WawZmebNhvqCRXzNzJIKYSCpvQ2jrOVuGgh5CMR+Tl0GQy5CfrptY9UrnS0o5gYHVJTDqMLE0IGqzVtPbrhZZgwg7+xf0TFJRExCNL+fNmvkkeks9fFJ3uL3f1eaOtWJTrSFaR/QopQWLz/5A1daJt/k+/vZUxxZp5+5H8r8FU1psFLvi16opFmZxVn8bmAQE0POZUpHmxolI4L1fSwmjgoxfdJuE5FHk9Ka8yKHf4SUVAma1xnKNKhynQaz1Ubh9XIMO2u4Cp4MmwE16eLPD1iza2Usi5qqUl5JXFEAO4Q8rbrLabN7myUa8TbX5Wtk4VmKRzZqsJ+41yny/wFkyuoL8uSn1jk5xLQFuEPP2fGu9R034iPhcHUgTV4VTl4+1Oxffykkiq4eLjP6xstmuJLl7gr+YNBrXHuBP3nWJDHDj0vHgEVhFAwfnNt2EtJMnnvCHJi8uhaqevtSg+mR2rsLC+FkOrHbvPOlonT5irp97InOsHsxfZIWN0HBSUN5JWlS579V5i77HEOlYVNwNEOO00YrqRxJRlIpXaguHBglr+7eXXmwqK74rV+c7H1ilhooMRqaMd+boaxyDuFAK99PWTIhlU9YnxShuPMZTwH1j/tY8nfetq8UMJrGll1+eRoU6DWRRzs8APTRAj5uPAUPjRR5vO+9pqyIXnn2J4TruDuY1dEcPDTKTuVgjb9PcOPlpb13+P7XyKCkD//f4PYknin68KyOzP4t5uBa8jAXN4Msl+MayeXxASc/MC90kd8ZPc45E5xGx8VQpL4Rn1btU7lEaiW9sXIKHKO0jbgT/btBpE5Jb7ZQGsNK37A==
Content-Type: multipart/alternative; boundary=”_000_MW4PR19MB70311D8A4C956B9341595652D2459MW4PR19MB7031namp_”
MIME-Version: 1.0
X-OriginatorOrg: sct-15-20-4755-11-msonline-outlook-e7757.templateTenant
X-MS-Exchange-CrossTenant-AuthAs: Internal
X-MS-Exchange-CrossTenant-AuthSource: MW4PR19MB7031.namprd19.prod.outlook.com
X-MS-Exchange-CrossTenant-RMS-PersistedConsumerOrg: 00000000-0000-0000-0000-000000000000
X-MS-Exchange-CrossTenant-Network-Message-Id: cc519a00-8b95-4404-b143-08db5fa33053
X-MS-Exchange-CrossTenant-originalarrivaltime: 28 May 2023 17:44:29.7764 (UTC)
X-MS-Exchange-CrossTenant-fromentityheader: Hosted
X-MS-Exchange-CrossTenant-id: 84df9e7f-e9f6-40af-b435-aaaaaaaaaaaa
X-MS-Exchange-CrossTenant-rms-persistedconsumerorg: 00000000-0000-0000-0000-000000000000
X-MS-Exchange-Transport-CrossTenantHeadersStamped: SJ0PR19MB6678
Now yours may look a lot different. It may be longer or shorter, or have additional information, or less. But the basic idea is that there’s a lot of information in the headers that has to do with the administration of getting the email from the sender to the receiver.
Some Individual headers
A detailed reference is much more than I can present here, and quite honestly, probably more than you need. But let’s examine the headers above a little more closely, since it’s a good example of a “normal” email message. They are from a message I sent to my regular email account from my Hotmail account.
A good rule of thumb is to begin at the bottom and work your way up in the headers. That’ll make more sense in just a minute.
Note that headers that begin with “X-” are “non standard”, and may not be used by all mailers, and might even mean different things to different mailers. They’re often just informational.
Highlighting just a few of the headers, working from the bottom:
- X-MS-Exchange-: The message was sent from my Hotmail account, which is processed by Microsoft using the Exchange email server. These headers are a number of items added by Exchange to the message. The most interseting might be X-MS-Exchange-CrossTenant-originalarrivaltime, the time the message was submitted to Hotmail … in other words, the time I pressed “Send”. In this example the date/time is 28 May 2023 17:44:29.7764 (UTC). The “(UTC)” means that the time is recorded as “Universal Time Coordinated”, sometimes thought of as Greenwich Mean Time or GMT. Since I’m in the Pacific time zone, and daylight savings time is in effect, that means I sent it at roughly 10:44 AM PDT.
- Content-Type: is how the mailers tell each other what the format of the mail is: plain text, as this example is, or HTML, or something else.
- Mime-Version: “Mime” stands for Multipurpose Internet Mail Extensions, and is the formatting protocol most often used to encode attachments and alternate representations in a single email. In this example the type is “multipart/alternative”, meaning that the message may be included more than once, typically once in HTML format, and once again in plain text.
- Date: This is the more common place you’ll find the date and time that the message was sent. This is added by the sending mailer or email program, and is commonly used by your email client as the “Sent Date”. Interestingly, it need not be accurate. Note that the time zone is specified as an offset (+0000 hours) from UTC. You can use this to calculate the time in the local zone.
- Subject: As you’d expect, the subject of the email as you typed it.
- To: Again, as you’d expect, the list of recipient email addresses that this message is addressed to. What most people don’t realize is that the To: line doesn’t define who the email actually goes to, but rather simply lists who the mailer claims it’s to go to. Spammers, for example, can easily create a mail message that has bogus addresses in the To: line, and then send the mail to someone else entirely. That’s known as “spoofing“.
- From: Just like To:, the “From:” address shows you from whom the mail was supposedly sent. And also like “To:”, it’s very easy for the spammers and virus writers to spoof the From: address to be pretty much anything they want.
- Received: Herein lies the gold. I’ll get into more detail on that below.
- Delivered-To: is added by the receiving mail server when it finally delivers the email to a specific email alias or mailbox.
- Return-Path: is the address that the email, if it fails to be delivered, should be bounced back to.
- Authentication-Results: and Received-SPF: are headers added that relate to spam detection. DKIM (mentioned within the first) and SPF are two approaches to confirming that the message is being sent by servers authorized to send from the source email address, and that the message has not been tampered with.
- Delivered-To: In my case I manage my leo@pugetsoundsoftware.com email (the To: address) using a Gmail account, and this logs which account is being used.
Received:
The series of “Received” headers are the trail that tells us from where the message was sent, and along what path or series of servers it traveled across the internet. And this is why we started at the bottom, as each mail server adds a received header to the top.
The first “Received” header is:
Received: from MW4PR19MB7031.namprd19.prod.outlook.com ([fe80::9f2a:c282:3c86:681d]) by MW4PR19MB7031.namprd19.prod.outlook.com ([fe80::9f2a:c282:3c86:681d%4]) with mapi id 15.20.6455.012; Sun, 28 May 2023 17:44:29 +0000
Or, in something closer English, the email was “Received”:
- From a server namedMW4PR19MB7031.namprd19.prod.outlook.com
- At the IP(v6) address: fe80::9f2a:c282:3c86:681d
- By a server named MW4PR19MB7031.namprd19.prod.outlook.com
- At the IP(v6) address: fe80::9f2a:c282:3c86:681d
- With mapi id 15.20.6455.012
- At the UTC date/time: Sun, 28 May 2023 17:44:29
Some interesting things to note:
- It was sent from and received by the same server. It’s not that uncommon for email servers to do this for a variety of reasons.
- The servers don’t list a IPv4 address.
- “MAPI” is Messaging Application Programming Interface, which is a mail API used within some Microsoft email programs and servers.
- It was sent at Sun, 28 May 2023 17:44:29, or, in my local time zone, 10:44:29 AM.
Immediately above that is another “Received” line (showing only the relevant portions of the lines):
- from MW4PR19MB7031.namprd19.prod.outlook.com
- by SJ0PR19MB6678.namprd19.prod.outlook.com
- with Microsoft SMTP Server
- at Sun, 28 May 2023 17:44:29 +0000
This is a different email server, fractions of a second later. Of note in this Received line is that it includes the software used: Microsoft SMTP Server.
Six lines above that, another “Received” line:
- from NAM12-MW2-obe.outbound.protection.outlook.com
- by ip-172-31-17-218.us-west-2.compute.internal
- at Sun, 28 May 2023 10:44:31 -0700 (PDT)
This represents the transmission of the message from the Microsoft outgoing mail server, to my server, two seconds later. This line also includes additional information: different email server software running on my server (Postfix), and the email address for which the message is destined (leo@pugetsoundsoftware.com).
Six lines above that we find a received line that doesn’t include a “from”, only the server actually receiving the message:
- Received: by 2002:a05:6402:2883:b0:514:9bd6:ceb0
- with POP3
- at Sun, 28 May 2023 10:44:54 -0700 (PDT)
Note that it indicates the protocol used: POP3. I have my Gmail account configured to fetch email from my server. Also note that this happened a full 10 seconds after the prior Received. This means the message sat on my server for that amount of time prior to being picked up by Gmail.
By now you can see that Received lines are somewhat consistent, but also vary a great deal. They all include the “by” server and a date/time stamp, most include a “from” server, but they can include additional information as well.
Received in spam
Now lets look at the headers of some SPAM I recently received:
Delivered-To: ********@gmail.com
Received: by 2002:a2e:3e0c:0:0:0:0:0 with SMTP id l12csp802812lja;
Sun, 28 May 2023 14:03:57 -0700 (PDT)
X-Google-Smtp-Source: ACHHUZ4dWy4F8CcN8M6MzHK/cpMVhEiK2rCImNs+OUUFwioak6TMspw8W0GRdRXhRMAk3brfYIeNV+LiTxg=
X-Received: by 2002:a50:c054:0:b0:50b:c79d:5201 with SMTP id u20-20020a50c054000000b0050bc79d5201mr2698809edd.6.1685307834268;
Sun, 28 May 2023 14:03:54 -0700 (PDT)
Authentication-Results: mx.google.com;
spf=neutral (google.com: 5.105.94.40 is neither permitted nor denied by best guess record for domain of unitedairlinesopinionrequested@********.live)
smtp.mailfrom=UnitedAirlinesOpinionRequested@********.live
Received-SPF: neutral (google.com: 5.105.94.40 is neither permitted nor denied by best guess record for domain of unitedairlinesopinionrequested@********.live) client-ip=5.105.94.40;
Received: by 2002:a05:6402:2883:b0:514:9bd6:ceb0 with POP3 id eg3-20020a056402288300b005149bd6ceb0mf3447868edb.1;
Sun, 28 May 2023 14:03:54 -0700 (PDT)
X-Gmail-Fetch-Info: leo@pugetsoundsoftware.com 8 mail.pugetsoundsoftware.com 995 leo@pugetsoundsoftware.com
Return-Path: <UnitedAirlinesOpinionRequested@********.live>
X-Original-To: leo@pugetsoundsoftware.com
Delivered-To: leo-pugetsoundsoftware.com@ec21.pugetsoundsoftware.com
Received: from 0029f27a.********.live (unknown [5.105.94.40]) by ip-172-31-17-218.us-west-2.compute.internal (Postfix) with ESMTP id 7152B3EAAB for <leo@pugetsoundsoftware.com>;
Sun, 28 May 2023 14:02:41 -0700 (PDT)
Received: from 0029f27a.xa9i22izk.********.live ([127.0.0.1]:35729 helo=xa9i22izk.********.live) by xa9i22izk.********.live with ESMTP id 00BMJO29F2MOLY7A; for
<leo@pugetsoundsoftware.com>; Sun, 28 May 2023 14:02:39 -0700
Date: Sun, 28 May 2023 14:02:39 -0700
Message-ID: <31729385271732131729233621471031516000@xa9i22izk.********.live>
To: <leo@pugetsoundsoftware.com>
From: United Airlines Opinion Requested <UnitedAirlinesOpinionRequested@********.live>
Subject: Congratulations! You can get a $50 United Airlines gift card!
Content-Language: en-us
MIME-Version: 1.0
Content-Transfer-Encoding: 8bit
Content-Type: multipart/alternative; boundary=”—-=Part.940.8142.1685307759″
[Note: every instance of “********” is something I changed to either maintain my own privacy, or to avoid giving spammers, or a compromised account, any visibility.]
A couple of interesting things about these headers:
- The source domain, “********.live”, is clearly and completely unrelated to the subject line referencing United Airlines.
- The source domain is registered at GoDaddy, but the contact information is hidden.
- The first Received line (starting from the bottom), is an internal server to same server transfer.
- The IP address of the source of the email in the second Received line, 5.105.94.40, is hosted in the Ukraine.
- Received-SPF: neutral isn’t necessarily bad, but it’s also not necessarily good.
So what to make of it all? It is possible that the originating computer hosted in Ukraine, is, in fact, sending out spam on purpose. It’s also possible that this machine has been infected with a virus, and is sending out spam without realizing it. There’s even a possibility that one of these headers has been spoofed (it’s unlikely in the case above, but it is possible).
That the source domain and the topic of the spam don’t match is a red flag, as is the fact that email “from” an email address supposedly registered in the US is coming from a server in the Ukraine.
Do this
While the information in email headers can be interesting, it’s rarely something that will help you track down the true source of spam or other messages intentionally hiding their source. I tend to think of it as “for entertainment purposes only”.
That being said, I do find them occasionally useful to determine where an email might have been delayed. If the timestamps between two “Received” headers differs by a significant amount in indicates the email spent that time waiting on the first before being sent to the second. It doesn’t tell you why, but it at least tells you where.
Want another good source of information? Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.


I read your article and it was very helpful in my understanding. Do you offer help to anyone seeking to understand the header of an abusive email, and in giving advice as to how to proceed with law enforcement or take a legal route?
Thanks.