Articles in Category: Security Software
Why Don’t Anti-Malware Tools Work Better?
Ever wonder why your antivirus program didn’t catch that virus? It’s not broken. Security is a race, and the bad guys are usually ahead. Learn why security tools can’t stop everything, what that means for you, and the most important step you can take to stay safe.
What Security Software Do You Recommend? (2025 Q3 update)
My updated guide cuts through the hype with four no-nonsense steps to keep your PC safe. Learn what works, what to avoid, and how to stay secure without overspending or overcomplicating.
How Can I Tell If a Website Is Safe?
It’s important, yet sometimes hard to tell, if a website is safe. You can stack the odds in your favor. I’ll show you simple tools and smart habits to help spot shady sites before they cause trouble, even if there’s no way to always be 100% sure.
What Is Ultra AV, and Why Did it Show Up On My Machine?
If you’ve suddenly found an unfamiliar antivirus program running on your computer, you’re not alone.
What to Do About Kaspersky Antivirus
Any software company with ties outside the U.S. comes under scrutiny. Should you be worried?
How Do I Fix “The App You’re Trying to Install Isn’t a Microsoft-Verified App”?
“The app you’re trying to install isn’t a Microsoft-verified app” message is the result of a simple setting you can change.
Do I Need More Than One Anti-malware Tool?
It’s tempting to think more is better when it comes to security software. In reality, too many can cause trouble.
How Do I Pick the Right Tools to Protect Windows?
There are many software programs that protect your system. I’ll review how I make my decisions and give you my advice.
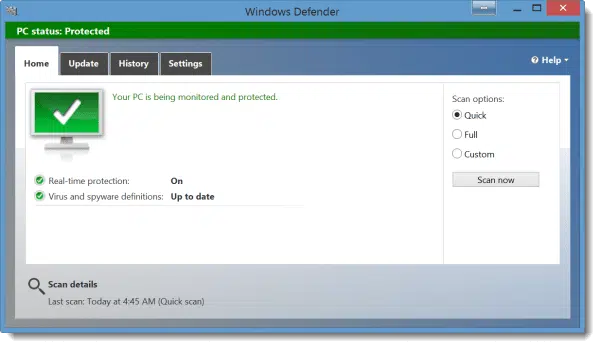
How Do I Run a Full Scan Using Windows Defender?
A full scan scans things a more common “quick scan” bypasses. Here’s how to run one using Windows Security.
What’s the Difference Between Windows Defender, Windows Security, and Microsoft Security Essentials?
Windows Security is Windows Defender is Microsoft Security Essentials, by any other name. Windows Defender has also had different meanings over the years.
What’s the Best Anti-Malware Tool to Keep Me Safe?
Over the years, your choices when it comes to anti-malware tools have become simpler, yet frustratingly imprecise.
Can My School Tell I’m Using Tor?
Your school (or whoever provides your internet connection) can see what you’re connecting to. Do they? There’s no way to know.
How Do I Keep My Kids Safe from Internet Garbage?
There’s a lot of garbage on the internet, and it’s difficult to prevent your children from seeing it. There are tools to help and steps to take.
Does a Lapsed Anti-malware Tool Leave an Open Door for Malware?
Letting your anti-malware subscription lapse is never a good idea. I’ll look at why that is, and available alternatives.
Why Microsoft’s Response to the Windows Defender Zero Day was Spot-On
Microsoft’s response to the recent Windows Defender zero-day vulnerability was an example of how the system is supposed to work.
Offline Anti-Malware Tools
Sometimes, the best way to remove malware is to reboot your system and run a completely separate tool. I’ll list some of the most popular.
Windows Defender Offline in Windows 10
When malware prevents your anti-malware tools from working, the built-in Windows Defender Offline is your first line of defense.
Should I Accept My Security Software’s Recommendation of What to Remove?
Should you trust your security software to make the right recommendations? Typically, yes, as long as you’re using reputable software.
Why would scanning a disk be quick, but just a file on it be slow?
If that large file is a backup image, then maybe your anti-malware tool knows what I know… that there’s no point in scanning it.
How do I safely switch from one security tool to another?
If you follow a few security measures it’s perfectly safe to uninstall an old anti-malware program and then install your new choice.
Why haven’t you mentioned CryptoPrevent?
Preventing one type of malware is not going to help you in the long run. And if it does help in the short run… then you may have a bigger problem!
Do I Need to Deactivate My Old Anti-virus Before Installing the New One?
It’s best to uninstall old anti-virus software before installing a new one, assuming you make sure to stay safe during the transition.
How does a site identify me when I am using a VPN?
There are lots of modules and widgets available online that help websites appear to identify who you are. Your VPN isn’t involved at all.
Does a VPN give me complete security?
A VPN service can offer a certain amount of security, but it ‘s dangerous to think it’s doing things for which it is not designed.
Do I Need to Stop Using Microsoft Security Essentials?
Recently statements were made by a Microsoft spokesperson that some interpreted as implying that Microsoft was giving up on Microsoft Security Essentials. I went to the source and asked for clarification.
Do I really need to uninstall these programs to update my anti-virus?
When you install a new anti-malware tool on a machine that has similar programs already, you may see a warning about possible conflicts. Basically, you have three choices to continue.
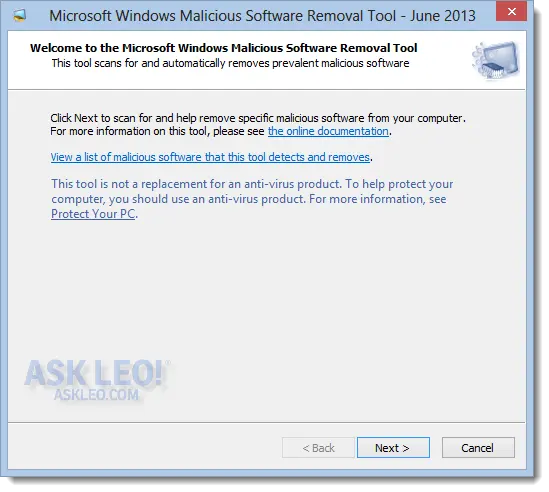
Do I need to run the Malicious Software Removal tool?
Malicious Software Removal Tool is something that’s downloaded and run by automatic updates, regardless of the anti-malware tools that you may already use, to provide a base level protection to the operating system.
Why is Microsoft Security Essentials constantly saying potentially unprotected?
The “potentially unprotected” warning seems fairly common in situations where you really are still protected. I’ll cover several theories as to why it might appear.
TrueCrypt – Free Open Source Industrial Strength Encryption
TrueCrypt provides a solution for encrypting sensitive data – everything from portable, mountable volumes to entire hard disks.
Is this stuff in my ‘hosts’ file supposed to be there?
The “hosts” file can be used for good or evil. Anti-malware programs may use it to block things, and malware may use it to block anti-malware.