Does never work for you?

Well, let me put it this way… never is what works for me. I never run it.
With that said, let’s look at why you might want to run it. From there, we can come up with how often you might want to do it.

Well, let me put it this way… never is what works for me. I never run it.
With that said, let’s look at why you might want to run it. From there, we can come up with how often you might want to do it.

I’ve been wrongly labeled as a spammer. What can I do about it?
I have used the same email address (me@mydomain.co.uk) for about 10 years. I am the author of a newsletter which goes to about 150 people, ALL of whom have ASKED to be included in my list, and I send and receive about 30 emails/day, mainly business. I never have and do not currently use my ID for any spamming to anyone, nor do I forward any of the dozens of spam emails I receive from “friends.”
When I sent an email to two different local contacts recently, I received the same message by return: “This message was undeliverable due to the following reason: Your message was not delivered because the return address was refused. The return address was “<me@mydomain.co.uk>” Please reply to <Postmaster@ispmail.ntl.com> if you feel this message to be in error.”
I DO consider this message to be SERIOUSLY in error. I have written to them several times, but I have been ignored. What do I do now, please?
Very little you haven’t already done.
You’re assuming the message means the remote system thinks you’re a spammer. While I suspect that is likely, it’s not always true.
Even if it is, it’s important to realize this isn’t some global database where everyone in the world now thinks you’re a spammer.
On the contrary; it’s likely to be this one email system you’re having trouble with — and perhaps only a couple of users.

In the past, Google’s search engine was the best. I would regularly try searches in some of its competitors, and I always came back. Google’s results were more accurate and gave me what I needed more often than not.
In recent months, that’s flipped. Google’s results are disappointing at best and misleading at worst.
There’s a word for it.

Actually, I talk about browser problems all the time. Particularly since people encounter browser problems all the time. 
The problem is that it’s never as simple as telling you, “Well, here’s what you do to stop ‘not responding’ problems.” There are so many possible causes there’s no way to know which one applies to your situation.
What I use instead is a more general approach to dealing with internet web browser problems that applies to all popular browsers — not only FireFox but Chrome, Edge, and others.

There are two separate items raised by this question I want to address:
They’re separate issues, but sometimes they’re related.
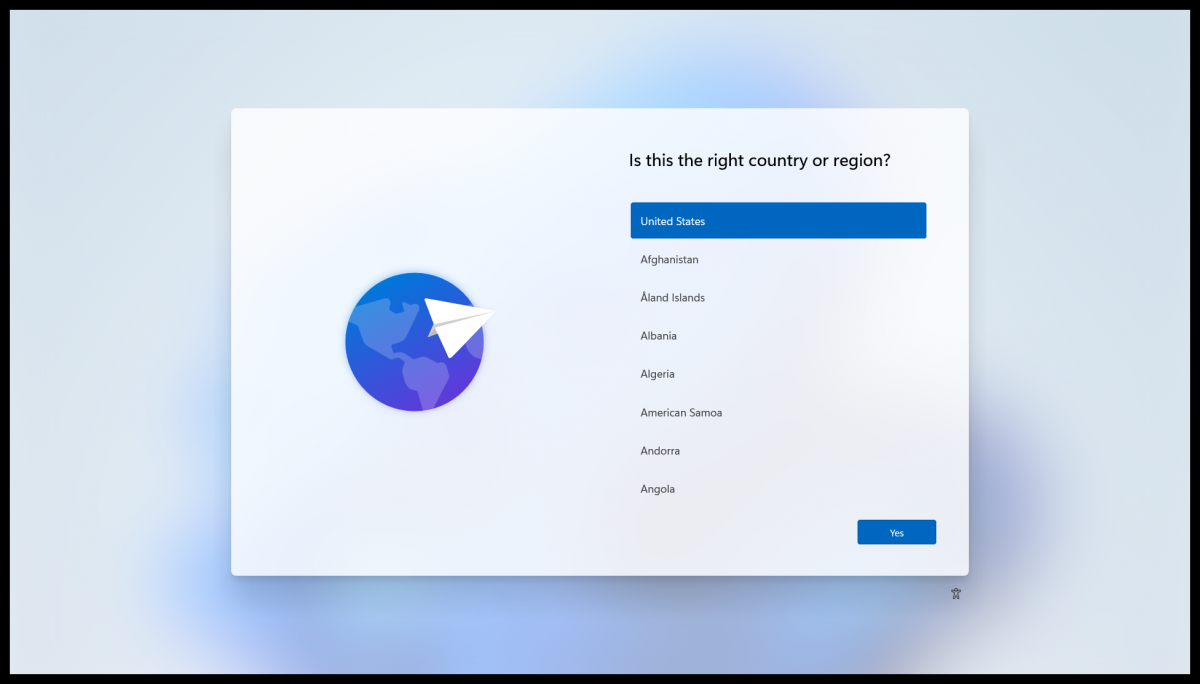
You may or may not remember setting up Windows 10 the first time you used it. You were walked through a process of questions and answers and options and waiting — probably lots of waiting — while Windows set up your machine.
It’s called the Out-of-Box Experience, or OOBE.
It turns out you can revisit the experience at any time.
In recent months, I’ve been thinking a lot about the news media and journalism in general.
It dawned on me that while Ask Leo! looks kind of like a news site, it’s not. It also occurred to me that several sites and other tech-support options that operate similarly to Ask Leo! are written and run by actual journalists while hobbyists run others.
None of that is a bad thing. A variety of experiences and opinions is a valuable thing.
But if I’m none of those, what am I?

A family member got scammed by a telephone call from someone saying that they were from Microsoft and calling because of PC error reports. Unfortunately, remote access was given. What should be done to prevent further compromise of the PC data? Help!
Note: MS scanner and a Norton scan were done and showed no problems. Remote access software files were removed manually from PC. Could the scammer again access the PC data? Data is backed up to the external drive (not plugged in at the time of the scam). Can the same files/data be safely loaded onto a new HD/computer?
As you point out, it’s a scam. Microsoft doesn’t call people because of errors on their computers. Neither do ISPs, security companies, or pretty much anyone else who might have some role of internet authority.
To quote Admiral Akbar, “It’s a trap!”
In recent years (yes, years) I’ve received many reports of this scam and its variants. Fortunately, many people are rightfully suspicious and cut it off before it goes too far. Unfortunately, your family member having fallen for the scam puts you in a difficult and dangerous position.
Let’s not hook up that external hard drive just yet.
Great question. Unfortunately, you may find the answer somewhat frustrating.
Your email may or may not be backed up. It depends on where your email lives. Once we know that, then we can make some more helpful suggestions.
Internet connection drops and failures are frustrating. They always seem to happen at the worst possible time.
Unfortunately, so many things can cause various types of failure that even the diagnostic process can get frustrating.
I’ll review some of the common things to look at if your internet connection randomly stops working.

Internal Server Error
The server encountered an internal error or misconfiguration and was unable to complete your request. Please contact the server administrator webmaster@******.com and inform them of the time the error occurred and anything you might have done that may have caused the error. More information about this error may be available in the server error log.
Additionally, a 500 Internal Server Error was encountered while trying to use an ErrorDocument to handle the request.
How is this resolved?
I’m very familiar with this error. Too familiar. I see it all the time when setting up or making changes to websites.
The good news? It’s not your fault.
The bad news? There’s probably nothing you can do.

The short answer is that you can’t. Not directly. I’ll explain why in a moment.
Cryptomator is a free program built to encrypt files before they’re uploaded to cloud storage. To access those files, you must have both Cryptomator and your passphrase. Even with the information, if you want to recover just a single encrypted file, things get challenging.
I’ll address how to protect yourself from scenarios like this. One approach relies on something I’ve been suggesting you do for a long time.

OneDrive is confusing to many people. It can be difficult to understand where your files are at any point in time on your PC or online.
Some folks want to download everything. They may want to walk away from OneDrive or just make sure all OneDrive files are included in their backups.
Depending on your situation, there are a couple of approaches.
Computers and technology, much like medicine, automobiles, and many more disciplines, has its own set of words, buzzwords, and terminology.
And just like when you go to the doctor or take your car to a mechanic, it’s important that you be able to communicate clearly what you want them to look at.
The more accurately you use terminology, the more likely you’ll get the correct and desired outcome.
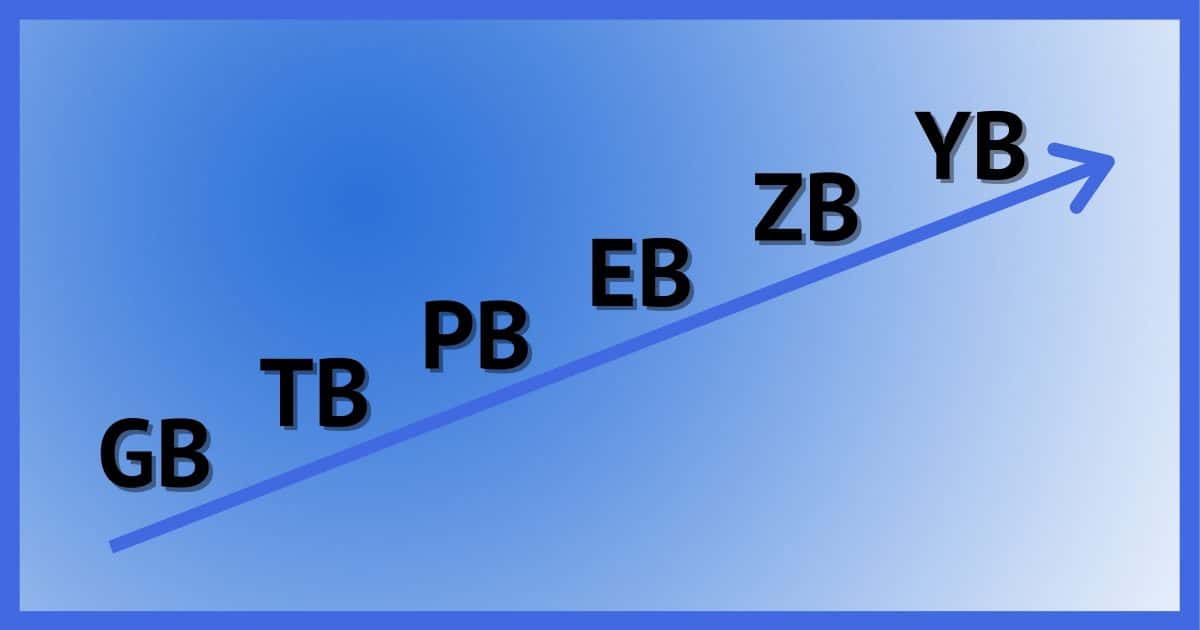
The only unchanging thing in the computer industry is change itself. Today’s topic is storage: specifically, how much and what we call it.
Let’s review some size-related and speed-related terms for good measure.
That was the question that spawned this article some 12(!) years ago, but I’m revisiting it for a simple reason.
It’s happening to me. Right now.
No error messages; Excel just goes away after a few seconds when I open a spreadsheet.
It’s time to repair Microsoft Office.
It seems like such a direct and simple question would result in a direct and simple answer.
In a practical sense, I suppose, the answer would be “Yes, as far as you’re concerned, they’re really gone and they cannot be recovered.”
But that qualification — “as far as you’re concerned” — opens up a Pandora’s box of possibilities.
Whether those possibilities matter depends on why you’re asking.

In a recent article, I discussed the different ways that various forms of two-factor authentication (2FA) can be compromised and which are the most resilient.
I need to explain one of those approaches in a little more detail, since it targets perhaps the most popular form of 2FA: the one-time password. If you’re not wary, you could fall victim.
The good news is that this attack requires your participation. The bad news is that you might not realize it until too late.
Once I answered a question from a reader, and they responded to the answer by saying, “So easy when you know how.”
I don’t know if they were making an honest observation or a snarky comment (I suspect the former), but I started thinking about what I’ll call my deep, dark secret.
I didn’t know how. In fact, I often have absolutely no clue.

I received a rather lengthy question mentioning a specific service claiming to turn the tables on spammers either by spamming them back or by using the content of their messages to harm them in some way… or at least annoy the heck out of them.
However, as much as spam angers us, besides ultimately being ineffective, vigilante justice isn’t the answer. Here’s why.
To reformat and reinstall is considered the “nuclear option” when it comes to dealing with Windows problems (or just cleaning up).

As Facebook Marketplace gets more use, it also gets more scams. It’s a popular place to buy and sell, which makes it more profitable to scam there as well.
There are several things to look for, but in this article, I’m going to focus on the concept of accountability and what scammers do to avoid it.

Every so often, I get a request that boils down to someone wanting to change the email address associated with their Microsoft account. I’ve maintained that you couldn’t — that your email address is your Microsoft account, and vice versa. No change was possible.
Turns out I was wrong.
Not only can you change the email address, but you can have multiple email addresses, and you can sign in with any one of them you like.
Pretty wild! Let’s look at what it takes.

You don’t need to do anything.
The email in question described how this person’s account had been hacked, how changing the password wouldn’t help, and that the account was being held for ransom to be paid in Bitcoin. And it appeared to be “From:” this person’s email address.
Variations of this scam even include a password — a password you’ve actually used. I’ve gotten them myself.
Even so, “complete BS” is very accurate.
Though if there is a password, there is one thing you should do.
This question took me by surprise. Seriously.
I mean, why would you consider deleting the System32 folder?
Well, apparently there’s a prank or scam running around (again) that encourages people to do exactly that.
Don’t.
I understand this would be a deeply disturbing event, regardless of the cause.
Unfortunately, I don’t have much good news. There are things to try and things to understand.
And sadly, some things to prepare for.