Ransomware is scary, but a little preparation goes a long, long way.

That’s one of the comments I received on my article “Using OneDrive for Nearly Continuous Backup” .
I often recommend using an online service to back up your files in real time as they change, and that article is one example. It’s one way to back up changes between your image backups.
Encountering ransomware would generally call for using an image backup to reset your computer to a time before the malware arrived. You might then turn to your online backup to recover files changed between that image having been taken and the present. Unfortunately, as the questioner points out, it’s possible — likely even — that those files might also be encrypted by the ransomware.
Worse, of course, is if you’ve only been relying on that cloud backup.
But before you give in to a knee-jerk reaction to avoid online backups completely, consider this: they’ll give you more options, not fewer, should ransomware ever strike. In fact, they could save you in ways other backups might not.

OneDrive and ransomware
When files change or are deleted — perhaps by ransomware — OneDrive moves prior versions to a Recycle Bin or version history online, allowing you to recover files after a ransomware attack or any other error. OneDrive also has ransomware-specific detection that allows you to easily roll back all files affected. While it’s important to have multiple backup methods, OneDrive is a valuable tool against all kinds of threats.
Online backup to the rescue
Whenever a file is deleted from your computer in a folder being continuously backed up by OneDrive1, the following happens:
- Any prior copy of the file is moved to a Recycle Bin on the OneDrive servers.
Whenever a file changes on your computer in a folder being continuously backed up by OneDrive, the following happens:
- The prior copy is moved to the version history for that file. (A kind of recycle bin specifically for that file.)
- The new copy is uploaded.
Yes, OneDrive has a Recycle Bin. This means OneDrive can save your data from ransomware.
It works like this.
- You use OneDrive to keep a more-or-less continuous backup of your data online.
- Your machine becomes infected with ransomware of some form, and all your data files are encrypted (and therefore lost to you).
- If you are online, OneDrive dutifully notices that the files have changed, and backs up the now-encrypted files.
- You panic. (Technically, this step is optional but quite common.)
- You disconnect, clean up, rebuild, or otherwise remove the malware from your machine, but your files are still encrypted.
- You visit OneDrive online2, and recover your unencrypted files from its Recycle Bin and/or each file’s version history.
- You vow to never again do whatever it was that allowed the malware infection to happen in the first place.
- Life goes on.
OneDrive just saved your bacon. What’s more, everything I’ve described above all happens without any other form of backup in place.
But of course, you also have other forms of backup — right?
Help keep it going by becoming a Patron.
Belt and suspenders and suspenders
The person who originally left the comment continued:
A simple but probably inefficient means I use is to make a copy of my OneDrive files weekly.
This is (almost) exactly what I do myself. Every night, I make a copy of everything in my OneDrive folder, in the form of a (password-protected) “.zip” file, and save it elsewhere. Should I ever succumb to ransomware, I can recover my files from that additional backup.
Of course, on top of that, I have nightly backups running to an external hard drive: monthly full backups with daily incrementals, meaning I can always recover the files “as of” a few days ago, before the ransomware attacked. (And in case I happen to run across ransomware that also tries to encrypt backups, some of those backups are copied elsewhere, effectively “offline” and not directly accessible to my machine.)
It would take a lot for even the nastiest ransomware to cause me to lose any significant number of files.
But wait, there’s more!
OneDrive includes ransomware-specific detection and recovery.
In short, if it sees a large number of files being changed in short order (or possibly a large number being deleted), it will ask if you’re experiencing the effects of ransomware.
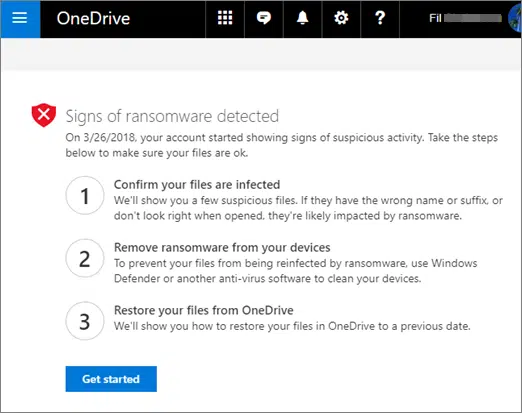
After you’ve cleared the ransomware and secured your system, OneDrive makes it easy to restore your OneDrive — all of the affected files at once — to the state they were in prior to the suspicious activity.
Microsoft has all the details and instructions in their support article: Ransomware detection and recovering your files.
You don’t need to go overboard
You don’t need to be as backup-crazy as I am. You can protect yourself with just a few simple steps.
- Use OneDrive for nearly continuous backup of your day-to-day working files.
- Enable File History. File History, though sometimes disabled by more aggressive ransomware, will also let you restore a file to the condition it was in before encryption, and can protect files outside of those you keep on OneDrive.
- Take periodic full and more frequent incremental image backups of your entire system to protect from almost any type of failure.
- Every so often, take one of those full backup images and copy it to offline storage.
And, honestly, that last one is just to make people panicking about ransomware encrypting their backups happy. That doesn’t happen often at all, and I don’t consider it critical, particularly with what we’ve just discussed about OneDrive’s Recycle Bin.
Do this
Don’t let the worst case scare you away from reasonable choices.
What concerns me most are folk who say they won’t use online backups because their files might be encrypted by ransomware, and they think their online backups would be useless. We’ve just shown that’s absolutely not true, thanks to online Recycle Bins and the like.
More importantly, ransomware is only one type of threat. It’s not even the most likely threat.
For example, a hard disk failure can be much more destructive than ransomware and is probably much more likely to happen. Even more bluntly: you’re more likely to accidentally overwrite or delete a file than you are to encounter ransomware.
Even if the Recycle Bin didn’t exist, continuous online backups save your files from many threats that don’t involve invalidating the backup.
The same is true for nightly backups to an always-connected external hard drive. Yes, there’s a chance that ransomware could encrypt your backups. There’s a much higher probability that you’ll be glad you had those backups current for a variety of other failures.
Making backups easy, timely, and automatic is more important than fearing one specific — albeit destructive — form of malware.
Something else easy and timely? Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: I’ll keep referring only to OneDrive as it’s baked into Windows, but most of these concepts apply to DropBox as well. Other services may also include similar features, so if you choose to use something other than DropBox or OneDrive, I encourage you to research the options available. The amount of free storage you get is not necessarily the most important factor in deciding which to use.
2: Within 30 days, that is. I’d strongly recommend doing it as soon as you possibly can, just for added safety and reassurance.




Leo, I was at a friend’s house one day recently when a ransomware demand popped up on her screen. She had no backups, so we had a few minutes of panic. I was able to unlock the screen and determine that this was, fortunately, fake ransomware. The scare was enough to get her to start backing up her files online. That paid off for her last week when Hurricane Harvey hit. She got flooded and her computer won’t boot (I don’t think it is dead, but I won’t know more until I can get over there and check it out). She was able to locate her backups online and get back to work on another PC.
We faced a flooding threat here, too, and I was a little calmer than I might otherwise have been knowing that even if something happened to my laptop, my files would live on. A backup to an external drive is good (and I do that), but a backup that fails due to the same thing that took out your computer is of no use. Thank you for your constant admonitions to back up and to back up your backup!
you forgot to mention one drive is only on windows 10. i`m sticking with win 7 ult until the bitter end.
anybody else out there doing the same?
OneDrive can be installed on Windows 7. It comes pre-installed on Windows 10 & 11.
https://onedrive.live.com/about/en-us/download/
I personally don’t like backing up on line. I do two kinds of backup. The first is a program called FoldrSync. The user creates a script which contains as many actions as desired. A typical action looks like these 2
[Action3020]
Path1=D:\Scanned and digital photos 2
Path2=F:\RBH WIN7 BUP\Scanned and digital photos 2_BU
[Action3050]
Path1=C:\Users\All Users\ddisoftware
Path2=F:\RBH WIN7 BUP\Qimage_BU
Mask=*.ini;*.flt
I use a variety of internal and external drives to store files to. My typical script contains about 40 actions. I also use them to keep other machines up to date. I always have complete sets of files in many places, so I will hopefully never lose at least one set.
And, I use Macrium Reflect to create images of my C drives in all my machines. This protects against everything, including HD failures, numerous of which I have had in my 30 years of personal computers.
Both of these tasks have saved me from a variety of catastrophes.
I’ve been backing up since 1989, when I used a magnetic tape device to contain the backup. It stored at the rate of 5 MB per hour. These days backing up and imaging of 50-100 GB takes only minutes.
When choosing an external drive for your back up pick one with an on/off switch (Fantom is one brand that has an on/off switch). This makes it easy to turn it on for the back up and then off when done. No unplugging under the desk. Simple and easy.
My external backup drive is connected through a USB3 hub. Each hub connection has its own on-off switch with a LED indicator. Backup finished, just push the button (after dismounting so all data is finalized). Light goes out. Drive is offline and since the drive is USB3 powered, also turned off.
Most online backup programs, such as IDrive and Carbonite, keep multiple historical versions of backed up files, unlike online storage services such as OneDrive, which only keeps a the most recent historical version in its recycle bin. That can be crucial at times.
Checking my online Onedrive Recycle Bin it would appear that only deleted files are moved to the ‘online Onedrive Recycle Bin’, not changed files as you advise ?
‘Whenever a file changes on your computer in a folder being continuously backed up by OneDrive1, the following happens:
Any prior copy of the file is moved to a Recycle Bin on the OneDrive servers.’
PS. Thanks Leo for all your helpful advise over the years.
I just experimented and found that although previous versions of files are not found in the recycle bin, you can go to the OneDrive website and right click on a file, select version history and download previous versions of files.
OneDrive for Business allows you to right click on a file and under Properties directly from File Explorer and click on the Previous Versions tab to recover older files.
It would help to know how long an online backup or full system image will take. My ISP provides 6Mbs download speed and 1Mbs upload. (That’s megaBIT, not megaBYTE.) Those speeds are not absolute. It all depends on time of day (my ISP throttles back at night to roughly 2Mbs D/L and .5Mbps U/L), and how many people are sharing the bandwidth. Just as a personal example, Windows 10 Pro was a 3.2GB D/L package from Microsoft. It took 14 hours. If my math is correct, it would take more than 5 days for me to upload 60GB to the cloud at my current U/L speed.
The cloud may be a viable solution for those who have a fast internet connection. But as for me? I’ll stick to my external hard drives.
With my internet connection 42 Mb down 8 Mb up, it took me about 2 weeks to download 100 GB of data to OneDrive when restoring my system. Uploading would take probably 5 times longer. That’s why it’s not practical to use the cloud for a full system image backup. Many people I know only have one or two GB of user data. In that case, even a slow DSL should work for data backups.
Performing a full image backup online is impractical at today’s connections speeds and disk sizes. Online backups are best for collection of your data files.
I use the MegaSync cloud service to maintain an online backup of my important data files. This includes my Documents folder. MegaSync includes zero-knowledge end-to-end encryption. Since I have the MegaSync app on all my devices, these important files (things like receipts, bank statements, passport images, car registration and insurance, etc.) are always available. Since the data is encrypted and decrypted on my own device it’s un-hackable in practice. Of course I maintain comprehensive local backups of data and OS as well.
I got an email from Microsoft OneDrive telling me 7273 files were victims of malware. I believe that is a false positive based on having a similar number of Cryptomator files and not finding any other encrypted files.
What I found interesting in the email was:
“Visit OneDrive.com within 30 days of the attack to:
· Review suspicious files and confirm they have been compromised
· Remove ransomware from your devices
· Restore your files on OneDrive
You can restore your files on OneDrive for only 30 days after they were compromised. If you don’t restore the compromised files within 30 days from the ransomware attack, the files won’t be recoverable. “
If using Macrium Reflect to make file backups to a second drive, does image guardian prevent encryption of the backup files by malware?
If the results are “mrimg” files, then I believe so, yes.
Yes. It also protects against you accidentally deleting or damaging a backup as the only way to delete or modify a .mring file is with the Macrium Reflect program.
You make this sound relatively simple. Reformat the machine and reinstall from your backup. It makes me wonder, why does it take a couple months for major retailers/organizations to be back up and running after an attack?
What I find shocking is that many companies don’t have proper backups. When I was coding, my first program for any system was to back the system up.
Usually the number of computers involved, and their need for up-to-the-second restoration, which is not something this solution addresses.
What the person commenting on the fact that the OneDrive files would also be encrypted missed was that OneDrive protects against this by keeping a version history of your files. I still do full image backups and daily incrementals protected by Macrium Image Guard. I haven’t needed to restore a file from a Macrium backup since I’ve been using OneDrive, because the backup has always been available on OneDrive. I have used Macrium Reflect a few times to replace an HDD and once to get rid of malware.
This also works with Dropbox, and probably other Cloud sync programs.
This is what I’m thinking. Some surgeries in some Ontario hospitals were being delayed for weeks after several hospitals (all on the same system) were hit with ransomware. Canada’s largest bookstore chain was down for a month or more. Bricks and mortar got back up and running sooner but online was still hobbled for a lot longer. I’m sure the more sophisticated the system, the longer it takes, so I don’t expect it to be back up the next day, but several weeks or months seems crazy, unless you don’t have a proper backup system.
I have a desktop and two laptop PCs. My desktop is my primary production machine, so it’s the only one I back up. I don’t keep any local files on my laptops. When I use a laptop to work with a file, I get the file from OneDrive, do my work, then save it back to it’s original location on OneDrive.
I sync my desktop with OneDrive, but not my laptops. I use Macrium Reflect (the paid version) to back up my desktop PC with Image Guard enabled. I have it configured to generate a full system image every Monday and a differential image every other day (Tuesday through Sunday). I Keep four backup sets (one full and six differential images) so I can restore versions of any file going as far back as twenty-eight days. On the first Monday of every month, after that day’s full image backup is created, I copy it to a 256GB USB drive that lives in my fire-proof safe in my office the rest of the time (in the event of fire, etc.), but that’s probably not necessary since I have all my files on OneDrive. I used to upload the image to Google Drive, but that sometimes took a few days and tied up a computer in the process, so now I use the USB drive (mentioned above) instead (it usually takes less than a half-hour).
All three of my computers dual boot Windows with one of two GNU/Linux distributions (Solus-KDE on the desktop and my primary laptop; EndeavourOS-xfce4 on my older laptop). I use the onedrive client I found on GitHub (https://github.com/abraunegg/onedrive) on all three. I have used it for several years. After installation, I get it set up my running the synchronization command (onedrive –synchronize) in a terminal window. Because it’s running for the first time, it gives me a onedrive link to open (all I have to do is ALT+Click the link to open it up in my web browser), and requires me to copy/paste the web address I get after confirming my identity with OneDrive. After I open the link, OneDrive asks me for my account email address, then requires me to confirm my identity with a 2FA notification on my phone (eazy-peazy). After I confirm my identity I/m moved to a second web page. I copy the address to my clipboard then paste it into the terminal window, after which the OneDrive client proceeds to download all my files from OneDrive to the new ~/OneDrive directory in my user’s home. I can set it up to run as a system service so it syncs with OneDrive every five minutes, but I don’t because I’m in and out of my GNU/Linux systems so many times a day that having it run as a system service would get in my way when I want to work with a file on OneDrive or upload something and restart the computer. Instead, I created an alias (alias sync=”onedrive –synchronize”) so I can simply open a terminal window and enter ‘sync’ when I want to synchronize my local OneDrive directory with my OneDrive cloud storage. One advantage of having all my files on OneDrive synchronized to all three GNU/Linux installations is that if I ever do something stupid that wipes out all my OneDrive storage (and I have – once), I can restore everything form one of the other GNU/Linux systems on a different device.
That’s my backup regimen. If you haven’t set one up yet, you should,
My2Cents,
Ernie (Oldster)
Question for you: are you finding the Linux OneDrive client reliable?
Absolutely, Leo. I’ve been using it for several years now. I had an issue (the first and only) about a month ago because of something I did while experimenting with it (I learn most of what I know by ‘experimenting’ 🙂 ) and I was able to fix everything by rebooting to Windows, restoring the contents of my OneDrive Recycle Bin, returning to GNU/Linux, deleting the onedrive directory from ~/.config, and re-registering the onedrive client (as if I had just installed it). It’s a command line utility so it may not be for everyone, but I like it.
Ernie (Oldster)
I want to amplify on what Leo said about companies recovering from ransomware attacks. Recreating all the last second system configuration is impossible – because we’re not talking about recovering just data or an OS image, but an entire multi-computer networked system configuration. This would be difficult for a couple of computers interacting, let alone hundreds of servers spread across the world. Recovering a large corporate system, particularly one that does business online, requires restoration of the OS, company and customer data, applications, databases, licenses, system configurations, timing synchronizations, networking configurations, etc. After all that, you can still lose most of the pending transactions, which can be in the millions.
It often comes down to how much the incident (ransomware attack) will cost. Will it be cheaper and quicker if the company paid the ransom or spend months reconfiguring their systems using unreliable backups? One risk of attempting a backup-based recovery would be running into unexpected problems (and they will), and then having to publicly disclose that the company’s systems were not properly maintained and protected. If a company can recover from a ransomware attack within a few hours and only report that the downtime was because of some “technical malfunction”, it would be a big public relations plus. Sometimes a ransomware attacker claims that it has stolen the company’s data and will expose it online if the ransom isn’t paid. Whether that claim is true or false, the risk, fallout, and law suits would be unacceptable for most companies, so they pay.
Besides continuing with business as quickly as possible, paying a ransom can have some potential “advantages”. When the system is restored, a company can take its time doing forensic analysis to determine its vulnerabilities. Or, a “cost effective” ransom payment can lead to a reevaluation of company data protection practices and more infusion of money into IT processes.
For most big companies, time lost doing business can be a big financial hit and it’ll cost less and take less time to just pay. Besides, companies have disaster insurance, so they get their money back anyway. All this is about money and not about right or wrong, ethics or altruism.
But Note: this is NOT an endorsement for paying the attacker. With a home computer there should be no reason to pay and recovery should be straightforward and fairly easy (just do the Leo thing).
Comment on Mark Jacob’s post about Microsoft saying it will “Remove ransomware from your devices”. Really? That’s REMOVE? What magic is this?
“If a company can recover from a ransomware attack within a few hours and only report that the downtime was because of some “technical malfunction”,” If a company does that and information leaks the reputation of that company would suffer tremendously. Look what happened with the LastPass breach.
LastPass Breach 2022: My Recommendation
“just do the Leo thing” might be my favorite quote ever.