It’s time to move on. The questions are, to what and how quickly?
“The time has come,” the Walrus said,
“To talk of many things…”
– Lewis Carroll
The last month or so of news and articles and general hysteria and misinformation (in both directions) around the LastPass breach have been challenging. Faced with all the conflicting information, it’s been difficult to sort out truth from fiction and make rational decisions.
Particularly since some of those decisions might involve a lot of inconvenience.
My recommendation is that it’s time to leave LastPass behind, but of course it’s not quite as simple as that. I’ll review what I think needs to happen and the path that I’ve embarked on myself (and why).

Leaving LastPass
- If you’ve been considering LastPass… don’t.
- If your LastPass master password was weak, immediately change passwords for important accounts such as financial accounts and your primary email account(s).
- Choose a new password manager. 1Password or Bitwarden are my recommendations.
- Migrate your vault to the new tool.
- Change passwords over time.
- Keep using a password vault.
The elephant in the room
LastPass has handled this entire situation horrifically. After watching these last weeks, I’ve given up hope that they will ever do so to my satisfaction, and thus recommend choosing a different password manager.
There’s exactly zero data that the contents of anyone’s vault has been compromised.
Zero.
However, enough information has surfaced to make it clear that LastPass is no longer to be trusted.
- The URLs of your vault entry were not encrypted, only usernames, passwords, and secure notes.
- “Old” LastPass accounts used a slightly less secure encryption of the master password, and users were never told to update.
- LastPass’s communication has been disappointing, to put it politely.
LastPass has let us down, and it’s time to move on.
The “weak password” thing
There is a small chance that if you have a “weak” password (which implies it pre-dates the improved master password encryption I mentioned above), your encrypted data could be vulnerable to a brute-force attack. I don’t consider this likely, as hackers will probably have better results with the treasure trove of exposed information, like the URLs, to improve their phishing attacks for a lot less work.
However, it’s possible. If your LastPass master password is not appropriately strong, consider changing the passwords of all “important” accounts stored in your vault as soon as possible, and all accounts eventually. Consider adding two-factor authentication to those accounts that support it for even more security.
Changing all your passwords can be a major inconvenience, but this is a “better safe than sorry” situation.
In my case, even though my LastPass master password was long and strong, I changed the passwords at all my financial institutions.
A new password manager
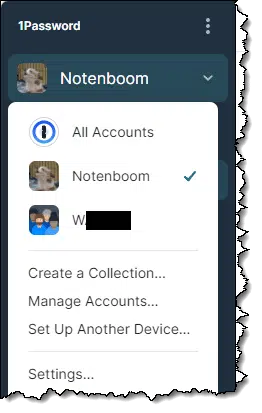
I’ve selected 1Password as my new password manager. My alternate recommendation is Bitwarden.
Both provide functionality roughly equivalent to LastPass, both are popular, and both come highly recommended from a variety of sources. The biggest practical difference is that 1Password does not have a free offering, whereas Bitwarden does. I’m comfortable recommending either.
The reason I personally am now using 1Password is because their Teams offering handles using separate vaults for separate organizations. Since there are organizations I support that use password management tools, it’s important that it be easy for myself and others on the team to access both our own vaults, and the organization vault, as seamlessly as possible.
Both 1Password and Bitwarden are cloud-based, making your vault(s) available on multiple devices simply by signing in. If you’re now cloud-shy (as I am not) then I would point you at Keepass, an open-source tool that maintains its encrypted vault locally, leaving it up to you to store, copy, synchronize, and use as you see fit.
Set up the new tool
Whichever tool you select, when you set up your account, make certain to:
- Choose a long, secure master password.
- Save that master password somewhere secure.
- Take advantage of any and all recovery or account security offerings.
For example, 1Password offers you the opportunity to create an “Emergency Kit”, a downloadable PDF containing all your account information with a place for you to write in your master password. Create that and save that in a secure location.1
Most tools include browser extensions to make password capture and entry easy. They may include programs you can run on your computer to manage your account and vault, secure web access, and apps that allow you to access your vault from mobile devices. Choose the combination of tools that works for you — usually the browser extension — once you’ve created your account.
Migrating the easy(ish) way
The most common way to migrate from one password manager to another is to:
- Export your data from the password manager you’re using. (Instructions for LastPass are here.
- Import your data into your new password manager. Instructions vary depending on the tool you use.
- Save a copy of your export file somewhere secure, much like a backup.
- Delete the copy of the export file you used for import so as not to leave the information on your computer unencrypted.
- Eventually, stop using the old tool, uninstall its components, and (optionally) delete the account.
In concept, it’s fairly simple, and most tools do it well.
However.
The basics transfer over nicely: the URLs, user IDs, and passwords of the accounts you have stored in your vault. However, any additional information, ranging from equivalent URLS to secure notes to stored credit card information, may or may not transfer depending on the capabilities of the tools involved. This is why I recommend saving the export file somewhere safe. That way, should some data not have transferred directly, you’ll always have access to the information later should you need it.
For the record, while I recommend this as the approach most folks should take, it’s not what I’m doing.
Migrating the hard(ish) way
After exporting my LastPass database, I examined the .CSV file and discovered that it had over 1,000 entries. I’ve been using it for some time, and things accumulate.
So my approach to migrating has been to essentially start over. As I visit sites and need to sign in, I grab the credentials from my backup,2 enter them, and instruct 1Password to save them. This way, my 1Password vault will contain only those entries I actually use.
The downside is that I’ll need to do this for months to come. Far in the future, I’ll need to sign in to a site for the first time since I switched, and it won’t yet have a 1Password entry.
Change passwords over time
The remaining question is what to do about the passwords in LastPass. Again, and to be clear, no actual passwords were compromised in the LastPass breach, only encrypted data. The risk is that the encrypted data could be brute-force attacked and decrypted. That risk ranges from extremely small to miniscule, depending on the strength of your vault’s master password.
But it’s not zero.
I’m not a fan of forced periodic password changes. They tend to cause more security issues than they prevent.
However, there’s nothing at all wrong with changing passwords to important accounts — or any accounts — because you want to.
Assuming you had a strong master password, in theory you shouldn’t need to change any passwords. I changed a few anyway because it made me feel better.
And when it comes to security, trusting in and feeling good about your situation is important.
Keep using a password vault
One of the first questions I got after recommending 1Password to someone was this:
How do we know they won’t get breached in the future, and we find ourselves right back in the same place?
We don’t.
Seriously. There’s no guarantee that any of the software or services you use anywhere for anything won’t suffer a catastrophic breach, and that includes whatever tool you choose to manage your passwords.
There’s no such thing as perfect security.
There is only more secure and less secure.
You can stack the deck in your favor and reduce the odds that you’ll ever be impacted by a breach in the future, but you cannot guarantee it’ll never happen, no matter what approach you use.
I remain firmly convinced that using a reputable password manager, including those with a cloud-based component, is safer than any alternative you might devise. Most importantly, it enables using long, unique, and truly random passwords for every site, which is perhaps the single most important thing you can do for password security. Every other alternative I’ve seen proposed compromises that or the fundamental security of how the passwords are saved and stored.
Do this
If you’re using LastPass and you have a weak master password, start changing passwords to your important accounts.
If you’re using LastPass at all, it’s time to move to another tool. It doesn’t have to be immediate, and you need not panic. LastPass has simply failed us too many times. While I’m not concerned about my data having been compromised (again, no actual credentials have yet been exposed), I no longer trust them to do the right thing moving forward.
Password management is nothing without trust.
Hopefully, you trust me to give you good advice about staying secure. Subscribe to Confident Computing, my weekly newsletter. Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: You can create the emergency kit at any time, but I strongly recommend doing so when setting up the account.
2: Two approaches: I have the export stored securely and can reference it at will. The other approach is to have a separate browser — Brave, in my case — that still has LastPass installed. I can then access my vault directly therein to copy/paste whatever I need. A third approach, I suppose, would be to visit LastPass.com on the web and access the vault that way.




I switched from LastPass to Bitwarden before the breach happened because I didn’t care for some of the changes Logmein was making which made it somewhat more difficult for non-technical users in my household to use.
Bitwarden has three tiers: Free, Premium for $10/year, and Families for $40/year. The Free and Premium tiers can have one or two users, the Families tier can have up to six.
I’m subscribed to the Family plan, which allows unlimited sharing for users and has other features such as advanced 2FA, emergency access, and unlimited collections. The Premium plan has the advanced 2FA and emergency access and allows for one vault to be shared between two users.
Bitwarden has a bit of a learning curve in setting it up and it took me a couple of days to set things up. Importing data from LastPass was easy, however there are differences in the way the data is arranged and took some editing.
With Bitwarden I set up an Organization and then invited members of my household to join it. Each member has their own vault and can share passwords with the organization. Logins can be sorted into Collections and access to each Collection can be granted to individual members.
I am the administrator for the organization and can control privileges for members and what they are allowed to do.
It has been a year since I switched and once set up, it has been easy to maintain. I still have the data exported from LastPass saved in a spreadsheet in the event I need it.
For myself, I use KeePass. With a 16-character passphrase that uses letters both upper- & lowercase, numbers, punctuation, and symbols. And I’m quite happy not to be using a cloud-based program. Please don’t get me wrong, I’m not cliud-phobic by any means; ferinstince, I make extensive use of Dropbox, among other services.
But IMNSHO, some things just aren’t appropriate candidates for cloud storage — passwords being very high up in that “inappropriate” category. In my view, just the fact (which you yourself have elsewhere pointed out, BTW) that cloud-based data can suddenly just vanish, all by itself makes it inappropriate to store passwords in the cloud, any other factors quite aside.
But oh wow, Leo. When I see you quoting from The Walrus And The Carpenter, things really must be bad…!
I see a hacking risk with cloud storage which is mitigated to almost nil with strong encryption, but your vault is store on you computer and only mirrored on the cloud. And any risk of a vanishing file can be eliminated by backing up.
And Lewis Carroll was a mathematician and hobbyist cryptographer. He would have had something to say about this issue.
Not starting a flame war with others who have other preferences but like TheGrandRascal, I also use Keepass (have for years). It is encrypted and safe to use. I maintain it on Google Drive and back it up to OneDrive using KPSimpleBackup. It easily syncs across my Windows devices and Android using Google Drive and is very easy to use on Android via Keepass2Android app. Keepass is free and well-supported. It is not very GUI-looking but that’s over-rated anyway. Keepass is easy to set up but there is a lot more beyond that to learn about if desired and that takes time. It can be used on the command line (I don’t). It can also be used with a key file or with a YubiKey. It has one-time and time-based password capabilities as well as auto-type (with/without obfuscation). I use it constantly and it is very easy to generate new passwords of any configuration. Oh, and it’s free. I really can’t say enough good things about it. The biggest obstacle I’ve found to getting other people to use it is that they don’t use any password manager and, well, what can you say about them?
I’ve heard many good things about KeePass. It’s resistant to that kind of hacking because it resides on your computer and if you keep it in OneDrive, Dropbox, or other cloud sync service, it’s not part of a central database of passwords and can be double encrypted if you use Cryptomator or another encryption program on the already encrypted vault file. I’ve never personally used it, but people I know swear by it.
The article points out a difference between 1password and bitwarden is that bitwarden has a free tier. That can be an important deciding factor.
I’ve also heard that bitwarden is open source. If 1password is not open source it could be a deciding factor as well.
Can you speak to this?
You are correct on the Open Source aspect. 1Password does publish periodic third party security audits, though: https://support.1password.com/security-assessments/ (as does Bitwarden: https://bitwarden.com/help/is-bitwarden-audited/)
Leo, I think you’ve offered on your videos and article the clearest and most easy-to-understand explanations about LastPass, thank you.
But one thing about LastPass that others have pointed out and unless I missed it, I don’t think you’ve talked about is the fact that LastPass did not encrypt the entire vault, and many think that they should have. If that is true, then do bitwarden and 1password encrypt everything? Right now, apparently information about websites visited with passwords and other fields are available to the hackers of LastPass.
Thank you for your response to this part of the issue.
I did mention it: it’s the fact that URLs were not encrypted, but usernames and passwords were. To be clear: ALL USERNAMES AND PASSWORDS (And secure notes) ARE ENCRYPTED. It’s the URLs that were disappointingly not.
My understanding is that other password vaults — 1Password and Bitwarden specifically — do this correctly.
Leo & readers,
Does anyone use Password Safe (pwsafe,org)? Originally developed by Bruce Schneier I believe it’s now open-sourced software. Does not require cloud storage. No charge. Other authors have written extensions for phones and OS beyond original Windows.
Do users who used LastPass in the past (switched to Bitwarden 2 years ago) need to be concerned?
All I can say is maybe. Did you actively delete your LastPass account, or did you just stop using it? If the latter, then your vault may still be up there.
I switched from LastPass to Bitwarden a couple of years ago and found the transition rather easy.
When I made the switch, I had no particular reason to change my passwords, etc. Would the information I originally stored on LastPass still be there–and would that put my Bitwarden logins at risk?
Unless you explicitly deleted your LastPass account, then your vault it likely still there. It’s not your Bitwarden account that could be at risk, but rather the accounts listed in that LastPass vault for which you had not changed passwords in the intervening time.
I have been using yubikey with Lastpass for what I thought was a high level of vault access security. When doing some initial research on 1password some have complained that although yubikey can be integrated into 1password, because of the way the 1password app is set up it is essentially bypassed as the ultimate access controller. I would appreciate anyone who has any insight on this issue, if it is one. Thanks.
I was lucky to find a lifetime offer few years ago to a very good and secure password program, Sticky Password Premium, for just $18 lifetime which is a super bargain, today it costs $99.99. It allows unlimited devices and after activating the provided “2-step authentication” all my passwords are very safe and very secure. I highly recommend for any password program user to activate the very important “2-step authentication” to stay safe, secure and properly protected.
I have been very pleased with Sticky Password and you may want to test it, they do offer a free version.
I also use KeePass. Whether you sync to the cloud is optional – you can set it up that way or not. It is free (after trying it, I made a donation), open-source, and cross-platform. I doubt you could go wrong with any reputable software, though (of course, that used to include LastPass . . . ).
I understand the concept of getting passwords via a brute force attack, but don’t understand how they would actually work. Every one of my financial accounts [and many others] will lock me out after “X” attempts. Right? Wrong?
Check out: How Can a Hacker Try All Possible Passwords If Systems Block the Login Attempts?
Previously you have written albeit briefly about dropbox.passwords. Do you consider this a reasonable alternative or is it fundamentally inferior to 1Password, Bitwarden, and KeePass?
I’ve not written about Dropbox passwords to the best of my knowledge. I have no experience with it. It might well be a good alternative, but I tend to shy away from solutions that aren’t the primary focus of the company behind them.
Since the LastPass breach, I have received a new level of spam emails and a phishing attempt to procure payment through PayPal. PayPal is the only one of my financial accounts that I used with LastPass. As a paid subscriber, I’m very disappointed in LastPass. I will checkout 1Password.
Thanks for sharing. I’ve been eagerly waiting for your view on this because you are someone I trust on the Internet (a point you’ve made in other videos). LastPass is very convenient for me, and until this November, I’m still on the $12/year plan, but likely not going forward.
I have been using Dashlane for a number of years and have been satisfied. Your article made me wonder if it is as secure as I believe it is. Does anyone have any comments for or against Dashlane?
I have no direct experience, but I’ve heard good things.
In the past, you have mentioned RoboForm which is what I use. Why is it not one you are recommending?
I left Roboform years ago because they didn’t have an export ability. My understanding is that they do now. I’ve not mentioned them today because there are simply too many password managers for me to evaluate them all. My understanding is that they have a good reputation.
FYI I talked about Roboform back in 2006: https://askleo.com/roboform_password_manager_and_more/
Leo,
I think you’re being a little harsh suggesting we leave Lastpass. Okay, they’ve been hacked, but so have many large Corporations around the world, including Optus & Medibank in Australia. It can happen to anyone it seems.
However, no important information was accessed, and as you say, no actual passwords were compromised.
No guarantee that a “new” password manager would not suffer the same fate, so I’m staying with Lastpass.
We all get spam emails and our email addresses are out there every time we subscribe to anything or send an email, so we can’t blame Lastpass for spam we may be getting.
Understood, and honestly, it’s what made some of this decision making process more difficult. That being said, LastPass has been REALLY poor at communicating what’s up, and what they’re doing about it (if anything). I’ve not seen anything from them past their questionably timed pre-Christmas press release. That and some of their decision decisions (URLs in clear? Really??) just have me losing faith and not being willing to recommend them any further.
“However, no important information was accessed” That’s not entirely true. The list of websites was exposed along with their corresponding email address login names. That information is important to keep out of the hands of spammers. It allows phishers to write convincing phishing emails because they can make it look like it came from that company. For example, if the hackers have the company name and my email login address, they can send me an email with a link to log in to a fake website which looks like the real one. That’s where two factor authentication can be a life (or at least and account) saver.
“The list of websites was exposed along with their corresponding email address login names”
This is incorrect. The websites were exposed, but their corresponding email addresses and login names were NOT.
If the email addresses weren’t exposed, how was that a spam and phishing risk? I’ve read articles saying this breach opened people’s accounts to phishing attacks. Are those articles wrong?
To be clear:
So ONLY when the LastPass email address happened to be the same email address used in the individual accounts (common, I’ll admit) was there an issue.
But if your username for an account was “Mark”, and not an email address, or it was a different email address completely, that was NOT exposed.
I guess I lucked out. My LastPass email is the account I only use for ordering things on the web. I only check it occasionally to keep it alive.
I also use Roboform and would be very interested in why you do not recommend it.
I left Roboform years ago because they didn’t have an export ability. My understanding is that they do now. I’ve not mentioned them today because there are simply too many password managers for me to evaluate them all. My understanding is that they have a good reputation.
FYI I talked about Roboform back in 2006: https://askleo.com/roboform_password_manager_and_more/
Hi Leo, I still use Roboform from your recommendation many years ago, before you transferred to LastPass
I don’t see any mention of Roboform here, are they OK or should I move all my logins to 1 Password or Bitwarden?
I left Roboform years ago because they didn’t have an export ability. My understanding is that they do now. I’ve not mentioned them today because there are simply too many password managers for me to evaluate them all. My understanding is that they have a good reputation.
FYI I talked about Roboform back in 2006: https://askleo.com/roboform_password_manager_and_more/
So LastPass, a password manager meant to keep you secure, has been breached.
And now Norton LifeLock (of all things), also meant to protect your security, has been breached.
I have lost faith in these companies. I will add them to my non-trust list of politicians (either party), the IRS, the DOJ, Nigerian princes, the CDC and the FBI.
Am I missing anyone else?
You don’t trust Nigerian princes?
I bought two RoboForm licenses in 2003 for $35 and I have never paid a penny more since then. It has improved significantly through the years. Up through V7 everything was stored on your own devices. V8 introduced RoboForm Everywhere so that data could be synced on all of your devices. This feature of course required that your data be stored in the cloud and at the same time they introduced an annual fee. I declined to use this feature and therefore avoided the new fee. V8 did introduce an export feature which I had used but this feature has now disappeared unless you pay the annual fee, currently $39.
I have tried, over the years, all the password managers mentioned except Bitwarden, simply because I hadn’t heard of it at the time. I settled on Dashlane finally, mainly because it was seamless to use across multiple devices, and had a clean interface, although it did not work with certain browsers, which I didn’t use anyway. Today I would recommend it to anyone (I have no connection except as a satisfied user)
I haven’t used LastPass for years, so I thought I didn’t need to be concerned. But it occurred to me that my account might still be there, and sure enough I logged into LastPass and all my sites were still there. So now I have to test each one and change passwords that haven’t been changed in the intervening time since I left GasPast.
Replying to A Mike January 17, 2023 at 9:22 am,
I have been using Password Safe for years. It is a simple program 353KB from 1998 that is almost a portable app – all it needs is the executable and your data file. I say almost portable, because it writes your last opened data file path to the registry. It does not have export capability, but KeePass has a plug in that can import the Password Safe data file, which can then be exported.
When copying from the secure notes, control-c does not work, but right click copy does.
I have been using an old version 1.7 from Counterpane Systems, but I see newer open source versions are available at https://pwsafe.org/.
Hey Leo. Such amazing content, you’re really doing the world a great service. You might consider doing a very simple series targeted at the elderly population who don’t have a lot of technical knowledge, or even computer skills. Something to help them spot scams, and avoid identity theft.
I do have a question. I couldn’t find it on your website. How much additional security do you think is provided by the “Secret key” feature in 1Password? I understand their rationale and explanation on the website. However, some people have commented that it would be equally secure to just have a longer password for your account. (Like if you appended the secret key onto your password). It seems to me that this argument is true to the extent that you are protected from a server breach and subsequent attack on your encrypted vault. But it does not give you protection against, for example, keyloggers. If someone were able to use a keylogger to obtain your 1Password vault password, they still wouldn’t be able to use it (because they don’t have access to a trusted device). Whereas with bitwarden, they could use your vault password on an untrusted device.
Also how does the security provided by the Secret Key compare to hardware 2FA?
I like the additional security of the secret key for two reasons:
It can be a slight inconvenience when setting up a new device, but so far I feel it’s worth it.
Can anyone speak to 2FA with 1Password? I’m trying to find out my options to be able to log in if my 2FA devices are lost or stolen. Perhaps a backup code, or a recovery email to someone. But I can’t find any info on it other than to “turn off 2FA by accessing 1Password from another device that was already approved.” Well, what if I don’t have a device already approved?
I have been using LastPass for several years on all of my computers. I have no complaints using the free version. I grant you the potential problem that you pose, so I tried Bitwarden as a possible alternative. I had a hard time establishing an account, but finally worked that out. Then I tried a couple of business sites where I manually entered my user ID and password. That worked ok, but Bitwarden did not create the new site entry like LastPass does. Expecting some help from Bitwarden I then tried to log in to the site just as I used to do with LastPass. There was no help. I still had to enter the UID and the PW manually. In LastPass I can click on the site name, it comes up in the browser, and ID and PW are both entered. I am sure that I am missing some features. Any suggestions?
My LastPass security dashboard is now telling me 85 passwords are at risk. It also shows I’ve dropped to 52.1% safety, compared to the 86% I can remember from some time in the past.
How does this line up with the fact that I have a very long and strong master password? Should I be worried and start changing all those site passwords?
I’m looking at the alternative password manager recommendations, but change is not something I easily adopt.
This has nothing to do with the master password. At least two things come into play with that security rating:
A new password manager won’t fix that.
That warning isn’t about your master password. It’s about the website login passwords it has stored. It sounds like your dashboard score is lower because as time goes on, computers get more powerful and it becomes easier to perform brute force attack on them.
Leo, first and foremost, I wanted to express my sincerest gratitude for all your posts about the LastPass breach. I’ve been using them for a few years and have a couple hundred passwords and sensitive info in my vault.
When I learnt about the breach and read/watched all the apocalyptic posts out there, I was beyond concerned to put it mildly. Luckily, I saw one of your videos where you explain everything with unparalleled clarity, especially the critical importance of having a strong, unique Master Pass, which fortunately it is my case. I also saw you ended up switching to 1Password and I was wondering if by chance you had the opportunity to evaluate Keeper as well. I switched to them in the middle of the frenzie but I find their interface a bit lame compared to LastPass. In any case, thank you again for your knowledge and invaluable down to earth advice.
Unfortunately I have zero experience with Keeper. Sorry.
For anyone reading this far, another very alarming issue was posted by a user on TheVerge dot com. He said he left LP 3.5 years earlier and DELETED all of the items in his vault (pwords, notes, etc). After this breach, he logged back in to confirm his account was empty, and it was but the deleted items area still had all of his data from 3.5 years ago. A few others in the comment section confirmed they too had the problem. Not sure if this is true because I checked my “trash bin” and it’s empty. To be safe, go to Advanced Options > View Deleted Items.
HTH
With the recent admission by Lastpass that they were breached twice, the second time targetting a Dev Ops tech working from home, what confidence do we have that this security breach method can’t occur to other password manager companies such as Bitwarden or 1Password ?
Should we still use a password manager where our vault is stored in the cloud and a clear target of threat actors opposed to storing it locally ?
I continue to recommend using a password manager as being MORE secure than any alternative. Note that even though LastPass was breached, there’s zero data that any user passwords have been exposed. The concept remains solid, and, as I said, more secure than the alternatives people keep proposing. I’ve switched to 1Password.
As a senior citizen, while reasonably comfortable with my desktop computer, I (and many other seniors) would greatly appreciate a “first grade level” instruction on how to set up/begin/deal with a password manager. I have over 200 sites with passwords (some not all that great) and I worry about beginning a pw manager and then getting locked out of some sites due to lack of knowledge about a manager.
Remember: there’s ALWAYS “I forgot my password”. If you lose access to your password manager completely, you can still access the accounts therein by setting new passwords.