How to keep private things private.

This presents quite a dilemma.
To answer your second question first: no. There’s no way to determine if your files have been viewed or copied.
As for protecting your data, there’s no guaranteed solution. I’ve even heard of companies electing not to repair a hard drive because doing so would expose sensitive data to repair technicians.
Your options are somewhat limited, but if you can plan ahead, there’s a chance of preserving security.

It all comes down to trust
When you send your computer to a repair shop, your private files go with it. A password alone will not keep them safe. The best move is to encrypt your data before repair is needed. Without that, you are putting your trust in a stranger.
Physical security
The problem is basic. Handing your computer — or even its hard disk — to a technician violates one of the fundamental principles of computer security: if it’s not physically secure, it’s not secure. Period.
That’s true regardless of the reason. Handing your computer over to anyone is fundamentally insecure.
It all boils down to trust. In an ideal world, a trustworthy technician would work on your machine. In the real world, we’ve all heard stories of data being exposed or stolen by folks performing repairs.1
So what to do?
Help keep it going by becoming a Patron.
Plan ahead with encryption
The only secure solution is to encrypt the sensitive data you store on your hard drive.
You might think whole-disk encryption would be the way to go. The problem is, the technician will need to boot your machine to perform the repair, meaning you’ll have to share the decryption key so they can boot the system. After doing so, they’ll have access to everything.
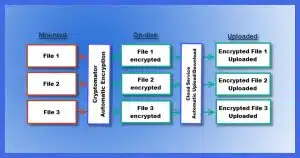
The more practical solution would be to encrypt only your data using tools like VeraCrypt, Cryptomator, or others.
When your data is not “mounted” (the approach both of those tools use to access your encrypted data), your technician can work on your machine without being able to access sensitive information.
Last-minute solutions
Encryption ahead of time is nice if you’re willing to put in the effort in case the computer might someday need to be sent to a technician.
For most people, it may not be worth the effort.
Unfortunately, there aren’t really any last-minute solutions. If the computer is so broken you can’t encrypt your data before you send the machine off for repair, you’re stuck.
There’s one possibility: if the problem you’re having is not hard-disk-related, one option is to remove the hard disk while they work on your computer. Someone would need to provide a temporary hard disk so they can work on the machine, but at least it wouldn’t have your data on it. When you get the computer back, you replace your hard drive, and hopefully, all is well.
Sadly, most problems involve software on the hard disk. What’s on the hard disk is typically at the heart of any repair work.
Application password protection
Using a program’s password protection is better than nothing. If your bookkeeping program, word processor, or some other program provides this layer of protection, use it.
Ultimately, however, application password protection isn’t the same as taking steps to secure a hard drive. It’s best to think of it as just keeping honest people honest.
Here are a few of the problems with using the password protection provided by many applications.
- Sometimes, a password doesn’t mean the data is encrypted; it simply prevents the application from opening the file without the proper password. The information in the file remains unencrypted and possibly visible.
- Sometimes, the encryption is “light”. By that, I mean the encryption is more properly called “obfuscation” to keep the data from being easily visible. It’s not much of a barrier to someone truly interested in cracking the file.
- Sometimes, the encryption is incompetent — perhaps there are bugs, or poor decisions were made in creating the software, to make the encryption less than secure. Application authors are rarely security experts. The result is that the file could be vulnerable to a hacker intent on breaking in.
Yes, it’s possible — probable, even — that with major software, the encryption is secure. It’s also unlikely that your technician is an expert hacker ready to crack reasonable encryption.
But how do you know?
The bottom line is trust
Your options are few and inconvenient.
- If you can, encrypt sensitive data ahead of time. This also protects you should your computer be stolen.
- Investigate the password protection your software offers, and use it to secure your data.
- If you have sensitive data you know is unencrypted, vulnerable, or particularly sensitive, never give that computer to someone you don’t completely trust.
- If you can’t find someone to trust, then perhaps not repairing the system — or at least the hard drive — is the most realistic solution.
Backing up can help
Naturally, I have to throw in a recommendation for backing up.
Backups sidestep this issue almost completely. If your hard drive dies, rather than having a technician fix it — and potentially access your data — replace it, and restore data from your most recent backup. Destroy the broken drive for additional security if you like.
If the problem is not your hard drive, you could still remove or reformat it before sending it in for repair. Once the repair is complete, restore your data from backup. This doesn’t resolve software issues, where the technician requires access to the software on your computer, but it does provide an additional option for other hardware-related failures.
And like most of the solutions I’ve discussed, proper prior planning is required.
Do this
Consider encrypting your important data now, before you need to.
Then, learn more about security and safety each week by subscribing to Confident Computing! More confidence and less frustration — solutions, answers, and tips — in your inbox every week.
Podcast audio
Footnotes & References
1: To be clear: it’s only a tiny percentage of repair folk responsible. The catch is knowing who’s trustworthy.


If possible I would put in a substitute hard drive if available.Almost everyone I know that has brought a PC in for repair has had the hard drive formatted by the tech even if you leave instructions for them now to do so.
[link removed]
I “Hide” my sensitive folders with Free Hide Folders from http://www.itusoft.com/hide_folder/free_hide_folder.htm
works for me but don’t lose your password. I THINK they can help you recover it if you lose it so maybe a service person could also pretend to be YOU and get that help to get into your stuff.
My Solution – I have a second H/D that I have straped as a slave and use hardware from Manhatan (Hi-speed USB 2.0 to SATA/IDE Adapter w/powersupply about $25.00). That way I can save my data to the slave and after any repairs I just transfer my data back to my orignal H/D. Very User friendly.
Sending back a laptop without a booting hard disk drive is not acceptable to at least one of the largest mfg’s (provided the problem is not the hdd). Jim’s solution above would be one the best.
This is basically Jim’s ans above but with a twist. It seems to me that the simplest way is to put your sensitive data on an external drive. With your data there it doesn’t matter what happens to your computer. Basically, you don’t worry about sensitive data on your computer because it never was on your computer in the first place. BTW, I just got a 1TB drive for under $130.
06-Feb-2009
I’m glad that there are others that have taken the words right out of my mouth. Always do you best to learn how to keep your pants at your waistline and not at your knees. LOL Shawn Patrick from Toronto, Canada
When I get a new computer or install a new HDD, the the first thing is to make an image of the HDD with Acronis True Image to external media. Then make regular image backups. Before turning the computer over to someone else, Wipe the HDD and put the orignal image back on it.
Use DBAN to erase it.
Some very good suggestions. Thanks. However one of my concerns, not covered, is how to securely lockdown one’s email client prior to handing over the computer? Seems to me that email itself often contains a huge amount of personal data. Mine sure does. Password protection of the app is sometimes possible, but useless, as so easily broken.
Just a word here too about the security passwords built into laptops. These provide very good protection, too good, as I found out to my lasting regret when I spilt a BIT of water onto the k’board. Some of the keys shorted and I was no longer able to enter a part of my password, so was permanently locked out of my laptop. An external USB keyboard of course was no help at all. These passwords are so built-in esp. the SVP which I believe resides in a hidden chip on the m’board, that you’re hosed if you forget them or have a disaster like mine. Seems there’s no password unlocking utilty around that can recover them. Well I certainly hadn’t forgotten mine. So be warned!
If anyone’s got any lateral thinking on a solution for this, other than a new MB, please reply.
15-Mar-2009
Hi
Thanking Leo.
Regarding this problem how a technicine is going to repair your computer if the hard disk is empty ?
I was rather thinking of a deontological protection.
06-Apr-2009
I know techs who say they never pay any attention to what’s on a hard drive and I know techs who say they always look at what files are on them. Some of the latter say they just look to see what the person has in their music and picture folders. One guy was honest enough to tell me that he goes through the files of every hard drive that comes through his shop, looking to see what (if any) porn pics the person has on there.
So the basic rule is, never have anything saved on your hard drive that you’d be embarrassed to have a computer tech see if he snoops through your stuff.
Why not be present during the repair?!
Unfortunately, most technicians wouldn’t allow it. The job takes usually takes longer with someone asking questions, making useless suggestions etc. I don’t mind it so much if I’m getting paid by the hour. 🙂
What if they agreed to duct tape over the mouth 🙂
Mostly because repair people are often in other places miles away. Some are large corporations that dont’ allow random strangers into their work areas. And some technicians work on their schedule, not yours.
The obvious solution that comes to mind is to learn to do your own repairs. It is not nearly as difficult as many people seem to think. You can find videos on YouTube about diagnosing problems and replacing components, and once you get into it, you will probably find yourself wondering why you ever paid anyone to do these things.
I have two 2TB external drives that everything goes on, and to play it real safe I also have Google and Asus Cloud Storage for my docs. But I also have nothing to hide.
I have Roboform Everywhere so I uninstalled it, and then reinstalled it using the online sync function after repair.
Zip your data with a password. Don’t tell the tech the password!
Excellent article and some of the replies are good too:-) In particular, Jenny’s one about locking down your email client rang very loud alarm bells! I have all my user folders stored on a slave hard drive, which I could easily remove before sending my PC for repair. I also have a 10GB folder encrypted by VeraCrypt, into which I save all my sensitive data. And I do regular daily backups to external drives. But it had just never occurred to me that anyone can just click on your email client, get all your email addresses and read all the emails still stored on it! And even if I disconnected the slave drive, which contains my Windows Live storage folder, because all my emails are now IMAP, they would all just be downloaded again if anyone opened the email client while the slave drive was disconnected. And I cannot see any way round that problem at all. So if anyone has any suggestions, I would be most grateful.
To protect my emails from snooping, I run Thunderbird Portable inside an encrypted folder. With the entire Thunderbird Portable folder stored in the encrypted container I keep my data files in.
Another thing to think about are “shortcuts” for your browser. The shortcuts can be easily found, copied to an external drive, then deleted from your main drive leaving just an empty folder. Shortcuts may be the most embarassing thing on your computer. If not embarassing at least it will tell them sights you frequent.
Sorry about using sights instead of sites. I’m at that age (over 60) that doesn’t accept new words easily. When I went to school site was a mis-spelled word. Now it is a real word. Aint wasn’t a word either bur was listed in the dictionart as a comonly mis-used abreviation for is not and are not. Times change faster than I can keep up.
Site has always been a real word. example: “I used to work on construction sites when I was in college.”
I have seen a couple of suggestions close to mine, but not quite the same.
If you are talking about a corporate environment, then the standard should be that ALL work files, sensitive or not MUST only be stored on the corporate network. That way there is no sensitive data on computers that are in exposed work areas (assuming the servers have adequate physical protection) for hackers to be able to reach. And also, corporate IT is responsible for providing adequate backup of information on the servers.
If you are talking about a personal computer then my favorite solution is to create a separate “Data” partition. This makes it easier to target files for encryption. This is half way to using an external drive.
For home users particularly, they should look into make full use of the backup features available in Windows 8 and 10. Using the “FileHistory” tool to automatically save files to a local, but external (second) drive provides protection against physical drive death. Then using the Windows and OneDrive “Sync” feature you can have automatic ‘Offsite” backup and a “3rd” copy of each file.
Here are some links to Win 8 and 10 specific backup articles:
Win10’s hybrid backup system
http://windowssecrets.com/top-story/best-of-breed-win10s-hybrid-backup-system/
With a combination of File History and OneDrive, your files are automatically saved to three separate locations: your primary data drive, your external File History drive, and your secure OneDrive offsite “cloud” account — all in near-real time. This virtually guarantees that you’ll never lose an important file again!
This one set of features is almost enough to encourage me to recommend that people upgrade to Win 10 . Win 10 now allows CONSUMERS to easily do a PROFESSIONAL grade total backup system.
Win 8/8.1 Total Backup System: File History + RecImg.EXE + Refresh + SlimImage – Wiki
http://answers.microsoft.com/en-us/windows/wiki/windows_8-files/windows-881-total-backup-system-what-ms-forgot-to/06f16f5e-6e82-4332-b39e-7d674d8fea28?tm=1414346084295
http://www.davescomputertips.com/wp-content/uploads/2015/03/backup-now.jpg
Unlike Fred Langa (author of the Windows Secrets article) I’m not a big fan of Windows 10’s backup. That being said, it’s better than no backup at all, and anything that gets people to actually back up is a good thing.
My apple imac wouldn’t switch on after a power cut, so I had to send it off via a technician. I had not backed up for 2 weeks, so they are going to see if they can retrieve all files , as they think something has seriously grilled inside. Now, they will have access to all passwords saved in the computer etc,
I assume if I change my email server password ( with my mini ipad which is still working!) , at least anyone untrustworthy would not be able to change passwords on paypal, amazon etc because hopefully they would not be able to access the emails in the computer after the server password change. Whereas I am still able to access my emails myself in mail on the ipad. Therefore just changing the email server password should be enough, as apposed to having to change all shopping account passwords. For the rest of the files photos, my artworks etc , I must just hope no-one will be interested in them….
Although it’s unlikely that a professional technician would do something like that, there’s still a chance. Personally, I’d change all of the passwords. Changing your email password wouldn’t be enough as someone with the passwords could still buy things on Amazon clean out your PayPal account, etc., and in some cases even change your passwords, as not all accounts require a verification email or text message to change a password.
“Now, they will have access to all passwords saved in the computer etc” I do not quite understand how and where do you store your passwords on a computer? Surely you do not store them unencrypted?
Yes, that’s the beauty of password managers, they keep all of your passwords encrypted and you can only get in to it by logging in with your master password which you should memorize and never store on your computer.
Just a thought – back up everything on your hard drive using Macrium Reflect (even make an image backup), securely erase all data on your drive (you could even just reinstall Windows so it would boot.) When you get it back then you can just restore the data or the image and be ready to go.
I am glad you mentioned to plan ahead before your mac breaks by encrypting your sensitive data. I recently got my computer repaired after cracking the screen. Thank you for the information on how to secure your information before fixing your computer. {Link removed}
I have over 35 years of experience with PCs [I first used an IBM PC in 1983 before hard disks were available] so I don’t need external support, but I’d like to suggest a solution that means you don’t have to secure your hard disk!
Don’t store your data on your PC; store it on an external ‘drive’. This would be appropriate to your data volume. My father has hardly any data, so he stores it on a USB3 pendrive. A friend with more data uses an external hard drive in a USB3 enclosure. I have lots of data [pictures, documents, videos etc. from over 30 years], so I use a NAS with 2TB drives in a RAID 1 format [mirroring]. These are all backed up by copying the data from the external media to another drive somewhere else on a frequent and regular basis. [I backup the 2TB NAS to an external USB3 hard disk enclosure temporarily connected to my PC with SyncBack Free software].
In all these cases, no user data is stored on the ‘C: drive’, only Windows and installed programs. So there’s no need to secure the PC if anyone takes it away to investigate problems. The added benefit is that the C: drive only needs to be a small inexpensive SSD – 128GB – as Windows and our programs easily fit within about 50GB, and only need to be backed up about once a month [with Macrium Reflect].
Obviously this data technique needs to be planned before your PC needs ‘fixing’, but it’s worth the effort knowing that any ‘outside user’ doesn’t have access to your data when they’re looking at your PC while they are trying to fix it …
Yours is a good approach. It avoids sharing sensitive data with people who should not have access to it. Many computer users are not experienced or motivated enough to follow your example, alas, at their own peril. So, when stuff happens to their computer, they are stuck with a decision: share the data or give up.
I have been an advocate of separating private data from essential data. Essential data is what the computer needs to run and serve your needs. As you said, a small “C” drive with the OS and installed software is all that is necessary for it. For me, private data is in one folder under Dropbox, but there are alternatives. Most of that is just stuff that nobody would care to exploit, like family pictures. Other data that is sensitive is in encrypted volumes. My preference for encryption is VeraCrypt, but almost any other will serve as well.
So, two purposes are served. One, my personal data is backed up and can be potentially shared and mirrored on any of my computers. The other, data that must remain private is encrypted. So, even if the computer were stolen, my data remains safe.
Following Leo’s advice over the years, I also do daily backup on external hard drives. If stuff happens I may be inconvenienced, but I will not lose or share data with an untrusted person. My approach does not need extensive computer knowledge, just a bit of careful attention.
I solve this problem by not having any really sensitive data on my computer. It is all on separate hard drive/cloud storage which are backed up at least daily, including any cloud storage. If the hard drive goes down, which it has once over the years, I just replace it and write back the data from backups. I’ve had cloud storage go down with data losses too, so that is not totally safe. If the computer goes down, which again is once over the years, I send it to the repair shop knowing there is very little on it in terms of sensitive data. I can plug my separate hard drive into a spare/wifes/my own laptop computer and carry on with minimum disruption.
That would add a layer of privacy, but encrypting your sensitive data is more effective, and it allows you access to all of your data from anywhere in the world. When I brought my computer in for repairs, I didn’t have to think of sensitive information being compromised. Cryptomator is great for this. Whole disk encryption won’t work if you use OneDrive or Dropbox, because the data synchronized with the cloud server is unencrypted. VeraCrypt might work, but only if you have a small amount of data to be encrypted. If your encrypted volume is large, you’d have to download and upload the entire volume every time you worked on a file.
When the HD fails, there is no way to protect the data on it before sending it for repair.
Depends on what you’re repairing. Repairing HDs is rare these days, it’s usually just a replace. So remove the HD before sending it in,
One problem nowadays is that if it’s a laptop, the average person can’t get to the HD to remove it.
I suppose I’m one of the lucky ones here. I have been building and repairing my own PCs since my MS-DOS powered desktop suffered a head crash back in the late 1980s or very early 1990s (I forget . . .), so I don’t have to worry about a technician seeing my files and passwords, or other sensitive information because when something goes wrong, I fix it myself.
With that said, I still concern myself with securing my boxes in the event any of them are ever stolen. For Windows, I use a ‘password-less’ Microsoft account with a (locally stored) pin, and biometrics (fingerprint) access to log on. For passwords, I use LastPass with 2FA (Microsoft’s Authenticator on my smart phone). I also have all the web sites I frequent set up with 2FA that support it.
On each of my PCs, I use BitLocker full disk encryption to secure my system and data partitions (each on a separate internal drive). I do not encrypt the partition where I store my back-up sets so I can access them if the need should ever arise. I do however encrypt, and password protect my back-ups (Macrium Reflect Free) so they cannot be accessed.
I have set up a password to access my system, and another to access my BIOS (UEFI). Fear not, I have them memorized and written down on a piece of paper stored in a safe.
If someone should succeed in steeling one of my machines, they will be unable to log on because they do not have my system access password, or my second factor (my fingerprints or pin), and they will not be able to boot from a USB drive to access my data (its encrypted), and they will not be able to access my UEFI settings without my password. Without my passwords and phone, my boxes are all essentially door stops for the most part. Even if a thief knows enough to wipe my passwords, they will still have to also wipe my drive(s) and re-install Windows to have anything like a usable device. The bottom line here is that my data is as safe as I can make it.
Ernie
Bitlocker is great in case your computer is stolen, but it won’t work when you bring a computer in for repair in some cases. One example: the only time I’ve brought my machine in for repair, it was a warrantee repair for a defective keyboard. I was asked to give them the password so they could test out the keyboard before and after the new one was installed. I told them I’d open it for them to test in front of me before and after the repair. I was lucky. They agreed. Not all repair centers would do that. That was in MicroCenter. I mention the name because good service should be rewarded with a good review.
I agree, but I fix/replace my own hardware and I never send anything out for service (only for replacement if defective and under warranty). My use of BitLocker is to thwart thievery and to limit their ‘reward’ to only the stolen hardware. I’m sorry if I did not make that clear.
Ernie
The time I brought my computer for repairs was under warrantee. You never know when that will happen.
I agree. Since I build my own desktops, it has never occurred to me that I may run into this issue. I do have a new laptop that will be under warranty for one year. I should probably consider making changes to accommodate the potential need to send it in for service, so I don’t have to worry about that. I have an external drive already connected to it for backup purposes. I’ll have to consider how I want to make the changes. Perhaps I’ll create a new partition on the external drive and move my user’s folder tree to it (C:\users\[username]). This way, everything I add to the system is stored on the external drive. I’ll post back after I give the situation some thought.
Ernie
Surely the simple solution is – at least for a desktop PC – DO NOT PUT ANY DATA ON YOUR C: DRIVE.
I have a SSD C: drive for the OS and all of my programs, a HDD for D: with all of my data.
It is easy to remove the HDD if the PC should need repairing, though I am a tech so fix mine myself.
Not applicable to a laptop, but why not keep sensitive data on an external drive that can more easily be kept secure and is less attractive to most thieves than a laptop.
One thing that comes to mind after reading this article and the comments. It shouldn’t be necessary to give technicians access to your Windows password in case of hardware problems in most cases. Technicians have bootable live OSes, usually Linux and some even use bootable live Windows (Windows PE).
Whole‑disk encryption isn’t always the right solution. If a technician needs to boot your machine to diagnose or repair it, tools like VeraCrypt won’t even let the system start without the password. BitLocker only protects your files while the machine is off. Once you log into Windows, the drive is decrypted and everything on it is readable to the system — and to anyone with access to your logged‑in session.
In a hardware‑repair situation, the technician can boot the machine from a live USB drive instead. That lets them run diagnostics and test components without having to unlock your encrypted system drive. Your data stays protected, and they still get full access to the hardware they need to work on.
I use BitLocker but only on a folder called “HUH”. That folder has all my important documents (mostly financial and family papers). Setting up BitLocker only on a folder can be a chore. When I need to add or modify a file, I unlock the folder, do what I need to do, then lock the folder. Be cautious if a folder uses BitLocker. Some back-up software, and other software like Carbonite, will only “see” the folder when the folder is un-locked.
Cloud‑backup services like Carbonite and Backblaze can’t back up the unencrypted files inside a BitLocker folder because that folder is actually an encrypted Virtual Hard Drive (VHD) volume. When it’s locked, the backup software only sees one large, encrypted file. When it’s unlocked, the files inside are visible but no longer encrypted, so Carbonite refuses to upload them for safety. Backblaze can be told to back up the VHD, but that defeats the purpose of encryption because the files would be uploaded in plain text.
You can use VeraCrypt instead, but VeraCrypt containers work the same way BitLocker containers do: they’re fixed‑size encrypted volumes. That means they encrypt all the free space along with the actual data, which wastes disk space and increases the size of anything you back up, seriously affecting Internet bandwidth.
I prefer VeraCrypt over BitLocker because it’s more transparent and easier to manage, but I actually don’t use either one for syncing to the cloud. I use ZIP‑AES, which provides strong AES encryption without the wasted space. ZIP only encrypts the actual files, not empty space, so the encrypted archive stays as small as possible and is easy to store, sync, and back up.
Cryptomator is ideal when you’re storing a lot of files in the cloud because the cloud service only uploads the individual encrypted files that change. That saves a huge amount of bandwidth compared to BitLocker or VeraCrypt, which store everything inside a single large encrypted container.
I used to use Cryptomator for that reason. But in my case, my encrypted documents only take up a few megabytes, and I prefer something simpler and universally compatible which can be decrypted on any computer or device. That’s why I switched to ZIP‑AES. It gives me strong AES encryption without the overhead of a fixed‑size container. ZIP only encrypts the actual files, not empty space, so the archive stays as small as possible and can be opened on any computer or device without special software.
https://askleo.com/cryptomator-vs-veracrypt-which-do-you-want/
https://askleo.com/bitlocker-vs-cryptomator-why-i-use-both-and-when-you-should-too/
Whenever I have sent a laptop in for repair (always an ASUS laptop, never a Dell or Lenovo) I do the following
1. full image of C: to D:
2. two complete backups of D:
3. wipe D:
4. reset to factory
It’s not clear what D: is that you are referring to.
Is it a second internal disk, partition on the system disk, or an external drive? The fact that you back it up and wipe it leads me to think it’s internal. It would be more efficient to back up directly to a external drive and back that up to another drive.
Silly silly silly! Never, but Never have any data on your box you are not willing to share with all comers, unless securely encrypted. For heavens sake, this has been the case since the first computer was born. Before the invent of encryption the rule was ‘do not put it there at all!’ Now, at least for the time being, simply encrypt blocks of data you are not willing to share with anyone. IMHO do not use Vera Crypt – research for yourself how this came into existence, and ask yourself just what may have driven the team of the True Crypt to walk away from their project, only to see an identical program, with the identical (only translated) name appear, and vigorously recommended by the powers that be. Make sure you notice a little detail that prior to this event the True Crypt encryption was never broken, in spite of the extreme efforts of exactly those powers that be.
You are correct that TrueCrypt was abandoned by its original developers in 2014, but the implication that VeraCrypt is a suspicious replacement is unfounded. VeraCrypt was created by a community of volunteers specifically to fix unpatched security holes in TrueCrypt and continue its development as an open-source project. It has since undergone rigorous independent security audits and is widely considered the industry standard for encrypted containers, far more secure than the outdated TrueCrypt. The theory that it was pushed by “powers that be” to compromise security is a conspiracy without evidence; the reality is that VeraCrypt exists because the original team could no longer maintain the software safely.