Seriously. Please.
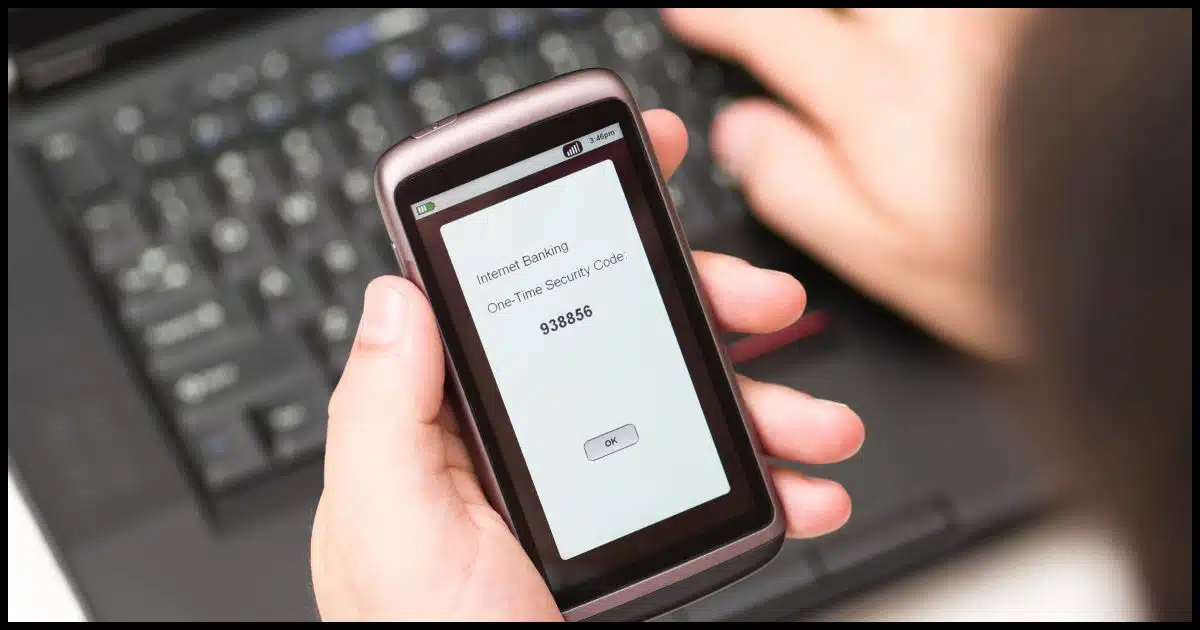
Not long ago, I wrote about SMS two-factor authorization being hackable and why you should use it anyway.
It’s an important enough topic that when I saw another article discussing a potential two-factor exploit — ‘You can’t relax’: Here’s why 2-factor authentication may be hackable — I just had to jump in to reinforce my message.
Use two-factor authentication anyway.
Even if two-factor is technically hackable, it’s essential.

Two-factor authentication hacks
- Using two-factor authentication makes you a less lucrative target.
- Your account is less secure without it.
- Currently known hacks of two-factor authentication are difficult for hackers to perform; some require that you or your mobile provider be fooled.
- Two-factor may not be perfect, but no security measure is.
- Use two-factor authentication on any account you consider important (i.e., all of them that offer it).
Two-factor is a barrier
The short, simple answer is this: Two-factor authentication erects another barrier to unauthorized individuals seeking to access your account. It’s a barrier most hackers won’t bother trying to penetrate. Instead, they’ll move on to other, less protected accounts.
Seriously, that’s all it takes to add significant value to your account security. Make it harder for the hackers, and they’ll go find an easier target.
That alone should convince you to use it. It keeps hackers out even if it is technically hackable.
Help keep it going by becoming a Patron.
Your account is less secure without it
I stand by the position I took in my previous article: your account is less secure — potentially significantly less secure — if you protect it with only a password.
You’re relying on that one piece of information remaining a secret forever.
Ask anyone whose account was compromised because the service they were using was hacked how well that worked for them. They did nothing wrong. They used long, strong, secure passwords and never shared them with anyone. Something completely out of their control exposed their password, and — poof — their account was in the hands of hackers.
Two-factor authentication could have prevented that, even if it is technically hackable.
Possible does not mean easy
That two-factor authentication can be hacked doesn’t surprise me. These are complex systems we’re dealing with. Bring enough firepower to bear, and I suppose anything is possible. There’s no such thing as perfect security, after all.
But that doesn’t mean it’s easy or commonplace.
The previous “OMG! Two-factor can be hacked!” scare required access to the telephone company systems that process SMS text messages for the targeted account. Read that again: it required access to a telephone company! Possible? Sure. Easy? No.
The scare that got my attention for this article requires your participation. You need to be targeted for and fall for a phishing scam that uses the two-factor information you type in to access your account. Let’s face it, two-factor or not, all bets are off if you fall for a phishing scam.
Another type of scam, SIM swapping, requires fooling your mobile provider into reassigning your mobile number to a scammer. To protect you from this, most providers allow you to set up a PIN that you have to give them before they will make any changes to your account.
Different forms of 2FA
The objections above apply almost exclusively to SMS-based two-factor authentication. Other forms of 2FA, including email, Time-based One-Time Passwords (Google Authenticator compatible), and hardware keys, are more resilient. They aren’t perfect, but they are much more difficult to hack.
So yes, if you have the option to choose something other than SMS text-messaging-based two-factor, do so.
But if SMS is the only option, it’s still better than not having two-factor at all.
Do this
Two-factor authentication is not a silver bullet. It doesn’t provide 100% proof-positive security. Nothing can.
Put another way, it can’t protect you from yourself.
What it can do is provide significant additional security to your account to make it practically impossible to hack — as long as you do your part by following best security practices to keep yourself safe.
Use two-factor authentication even if it’s technically hackable.
Also, subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.



A couple of takeaways from that article: never, ever click on a link in an email to go to your bank or any website you have an account with. Beware of Phishing.
To simplify the argument for 2 factor authentication: A password is a lock. 2FA is a lock. No matter how vulnerable the lock, taking it away will only make you less safe.
Not using two-factor authentication because it’s potentially hackable is just like not wearing your seat-belt when driving because seat-belts don’t prevent 100% of all injuries and deaths from vehicle collisions. You use them both because they make you safeER than you would otherwise be, not because they’re 100% effective.
Laurence is exactly right. Why bother to lock my door? I mean, someone *could* still pick the lock!
To get into my house I have to unlock 2 doors. The inside door is very easy to break down. I see no reason to keep it open or unlocked. It’s an extra layer of security. The second factor of 2FA is much stronger than that door and cracking it is probably similar to a robber tricking me into opening it. If you don’t fall for phishing attempts, this new 2FA hack isn’t a major threat.
I like the concept of the google Titan Security device and have read about those devices. However, they do not explain one aspect. My banks now require 2FA with a code sent to my cell phone. Some say the Titan is a better device but does not explain how the current bank 2FA is bypassed. When my bank sends a code to the cell phone, how does the Titan then somehow work?
It doesn’t. The Titan is something that your bank (or any service wanting to support it) needs to add themselves.
I live in South Africa and two-factor authentication is often hacked. However, it is done by insider assistance either at your Mobile operator and / or your Bank (probably both). They use a SIM swap technique, but somehow manage to prevent you getting a notification. With my bank, there is an option to get the 2FA code by email, which I opted for. I feel this is much safer.
For the second authentication factor to be hacked, the hackers would still have to get through the first factor which is your password. Create a long, at least 16 character, non-guessable password and it should defend against hackers getting to the second factor.
How Do I Choose a Good Password
If you can. My stupid bank used to allow a *maximum* of 10 characters – thankfully, they have increased that: first to 12, and now to 16. It is good, I guess, that they require the 2FA, but I would feel better if I could *also* create a decent password. (I do use the random password generator in KeePass to create my passwords/security question answers.)
16 characters isn’t bad for now, but the problem is that the minimum length for a good password increases as computers get more powerful. They might keep increasing the maximum size, but you’d have to be aware that they’ve upped the limit. I don’t understand why any programmer would limit password length. There’s no good reason. I remember when my bank only allowed a 6 character PIN to log in. At least they required a second factor to make a transaction.
Forgot to mention: they also originally allowed only letters and numbers to be used – NO special characters of any sort. At least they’ve changed that now, too. I also love when websites don’t tell you their password requirements/limits – there have been a couple of times I’ve just plain given up on creating an account someplace because I could never figure out what it didn’t like about my password!
Good practice indeed. Should also be unique and have high entropy (be random).
Still vulnerable to phishing, keyboard logger, shoulder surfing, compromised password vault…
True. That’s why the second factor is important even it there are potential hacks. Nothing is perfect but those hacks you mention would be blocked by requiring an SMS text message.
While I can agree that the fear of 2FA being hacked isn’t a good reason to avoid using it, I would be more nervous about something like this: https://www.ethnews.com/cryptocurrency-angel-investor-files-complaint-against-att-for-sim-hijacking
SIM-jacking is out of an individual’s control, and while it doesn’t seem too prevalent, yet, it’s another vector of attack that people should be aware of. It’s been successfully carried out on high-profile (bitcoin-rich) victims: if you have a lot of money, or if the hijackers can figure out how to streamline the SIM-stealing process and employ this on a large scale . . . .
This form of attack is common in South Africa.
A defense against this form of attack, that still used SMS based 2FA would be “security thru obscurity”. Use an anonymous / “burner phone” (would also need to be “pay-as-you-go”) or similar device dedicated to only receive 2FA SMS messages.
High value accounts should not rely on SMS based 2FA! The higher the value, the greater the incentive to hack the system.
“High value accounts should not rely on SMS based 2FA!” If SMS is the only option, then I continue to disagree. It’s STILL better than no two-factor at all.
SMS authentication is just another lock on the door. Taking away a weak lock from the door will only make you less safe. And from what I see, SMS authentication is hackable, but still a strong lock.
Unless cracking that secondary lock allows you to bypass the primary lock entirely (or, I guess, re-key it). The article isn’t about SMS hacking, it’s about SIM hijacking.
Yes, as Leo says, use as many layers of authentication as you need to. But there should a clarification about what is (or isn’t) two factor authentication. The examples that people are talking about and the methods used by websites are not “two factor”, but rather “two step” authentications. Originally the concept behind “two factor” was that you would use two entirely different types of inputs for authentication: (a) “what you know” (a piece of INFORMATION) and (b) “what you have” (a PHYSICAL item). Think about how you get into your ATM, using a card (a physical item) and the pin (something you know). When you’re sitting at your computer (or on your phone) and use two pieces of INFORMATION to get into your account, you are not doing two-factor, at least not as it was intended to. If one type of input can be hacked, then another input of the same type can also be hacked with the same or similar mechanism, especially if you are using the same device to process both inputs. The reason getting an SMS on your phone doesn’t qualify as “something you have” is because access to the phone’s functionality (phone number, WiFi and the SMS) is controlled by information, not the physical thing.
In the case of plug-in device, such as a Titan, the encrypted and proprietary data exchange between the device and the server can’t be replicated (theoretically) even if the data stream is intercepted by a hacker. By the way, the idea for a plug-in security device is not new and has been around since the 1970’s, except that back then it plugged into a serial port. Finally, the CNBC article cited by Leo says something about using the Titan via Bluetooth. Bad idea. This is yet another bastardization of the two-factor concept which opens the door to easy hacking. Bottom line is that the human is the weak link (in this case, too lazy to plug in something into the USB port).
2FA is better than no 2FA, but it also introduces new risks. Specifically the loss of the device that receives the 2FA (SMS) or that carries the application.
Living in South Africa, the risk of losing a cellphone through theft is high. My wife lost one in 5 min of putting her phone down in a bathroom (in a secured, corporate office). My daughter lost one to a mugger when she was stopped at a traffic light. So you need to have a recovery plan AND you need to have some protection on the device, to prevent the person who too it from you from using the apps and information on your phone to compromise your accounts.
The theft of device scenario is in strong contrast to my experience when I left a Kindle in a HEB shopping cart in Houston last year and was able to recover it from lost property the following day.
That’s true. With some Web sites, you have the option of several second factors. For example, my Gmail and other email accounts allow more than one recovery email address in addition to a recovery phone number. If I lose access to my phone, I would lose access to online banking until I either go to my bank and change the number or get a replacement phone with my original number. It would be better if they allowed an alternative method of receiving a TAN (Transaction Authorization Number) via email but unfortunately my banks don’t to that.
Two factor can be a pain in the ass in some scenarios. You are out of town and your phone breaks or is stolen. Now you may not be able to access your websites anymore. Or if for some reason you lose your phone number (service disconnected and the number is released), now you may never be able to get back into your websites.
This is why you must also set up recovery options for two-factor. Any service doing two-factor correctly (which is most) will have approaches. Covered in more depth here: https://askleo.com/easily-avoidable-risk-two-factor-authentication/
That works in most cases but some websites, including my German bank, only have SMS as a second factor. When I travel home to the US, I carry an older phone with my German SIM card. It’s even free to receive an international SMS. If I lose the SIM card, I have a second bank account which uses a challenge-response TAN (transaction authorization number) list which I’ve scanned and encrypted.
Bottom line: If a website doesn’t have an email or other recovery option, try to find an alternative one which does. Of course, in some cases, this isn’t possible, but it should probably work in most cases.
Strong passwords also carry a risk.
I use a password manager to store all my passwords. Most passwords are generated by the Password Manager. If I loose access to my Password Vault my life will become very difficult.
One risk scenario: Stroke or head trauma results in memory loss and I can not access my Password vault.
Mitigation option 1: store the password in a place accessible to trusted friends / family (which opens another risk if the trust was misplaced). If you want to reduce the risk, split the password (or a key to it) between several people who need to collaborate to compile the entire password.
Mitigation option 2: authorize a 3rd party (trusted friend / family member) to be able to request access to my Password Manager account. If the Password Manager receives a request for access they will first check with me. If I do not respond and deny the request within a set period the access is granted.
You can back your LastPass vault up and print it out and keep it in a safe location.
How Do I Back Up LastPass?
No 2FA will help if you succumb to being a “Phish.”
2FA will help in that even if the phishers get your password, they would need the second factor to get in to the account.
That doesn’t invalidate the value of 2FA in all other situations.
What is the difference between RMS and SMS? Sorry if this is obvious.
How do you should off 2-step when it says it is off? Loel
What makes you think it’s on if it says it’s off?