I use Authy too, and I also use it in multiple places, including my laptop and phone.
Indeed, it would be exceptionally inconvenient to log out after every use — so inconvenient I’d have a difficult time using or even recommending two-factor1 authentication. And it’s not just Authy — it’s any of the two-factor authentication “factors”, be it an app, your SMS-receiving phone, a security key, or anything else.
Once someone else has one of them — say if you lose your phone and they gain access to your two-factor app — what does that mean for your security?
Well, it’s serious and perhaps a little painful, but it’s not a disaster.

- Someone with access to your second factor does not have access to your accounts — they still need your password.
- SMS two-factor: contact your mobile provider and move to a new device.
- For all others: access the account using alternate methods, then remove and re-add two-factor with a new code or device.
Two factors means two factors
Even if hackers have your password, they can’t sign in without your second factor. This is the reason I so strongly recommend two-factor authentication.
But the converse is true as well: if hackers have your second factor, they still can’t sign in without your password.
Both factors are required. If they don’t have both your password and your second factor (whether that’s a device, an app, a code, etc.), your account remains safe.
You still want to take action if you lose your phone, though.
Accounts using SMS-based two-factor
SMS-based (text message) two-factor authentication is the easiest to deal with.
If you lose your mobile phone, reach out to your provider, get a new phone, and transfer your number to the new phone. You’re done. SMS notifications will now arrive on your new device, and not your old, lost one.
If you don’t get a new phone immediately, do contact your provider as soon as possible and disable your lost phone. This prevents whoever has it from getting your SMS messages … or anything else.
It’s conceptually simple, and covers all accounts using SMS two-factor authentication.
Help keep it going by becoming a Patron.
For other accounts: first, regain access
For each account you have that uses a device or an app as its second factor, you need to sign in and set a new second factor.
For some accounts, you’ll already be signed in, and can proceed to the next step right away. For others, when you sign in, you’ll be asked for your second factor.
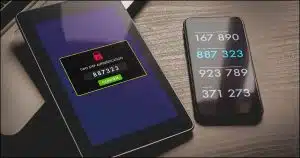
If you use Authy on multiple devices — like Windows and your mobile phone — you can simply sign in using the two-factor code provided by one of the other Authy installations. (This, and the ease of moving to a new phone, is the big benefit I see to using Authy.)
If, however, your second factor is only a single device — such as being on only your mobile phone, or being a single, specific, USB security key — then you no longer have the second factor you need to sign in.
When you set up two-factor authentication, you should also have also set up a recovery mechanism. That may be an alternate email address, an SMS-enabled phone number, a recovery code, or even an additional two-factor device. Use that mechanism to sign into your account. (And if you haven’t set up a recovery mechanism, go do it now.)
Then, reboot two-factor
The goal is to invalidate existing two-factor devices and re-establish a new one.
In most cases, that’s a two-step process: turn off two-factor authentication and then turn it back on again. It’s a kind of reboot.
Turning two-factor off accomplishes the first goal: any pre-existing second-factor devices, codes, or associations are disabled and forgotten. The codes provided by previously configured two-factor applications, like Authy, will no longer work. You also need to delete any entries for the account in authenticator apps you still have access to.
Your account will, for a brief moment, not be protected by two-factor authentication. That’s why the next step is important.
Turning two-factor back on establishes a new code you can use with your two-factor app, or a new relationship with a replacement hardware key. Your account will once again be protected by two-factor authentication.
It’s just like having your password exposed
Having someone else gain access to your second factor is the same as having someone else discover your password.
What do you do when your password is compromised? You change it.
What do you do when your second factor is compromised? You reboot it.
As long as both are not compromised by the same person at the same time, your account remains secure throughout.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: I’ll use “two-factor” throughout this article, but you may encounter terms like “2FA”, “multi-factor”, or others that mean the same thing.




The article mentions getting a new phone if one is lost or stolen. For those using GSM (SIM card) phones as most of the World uses, it’s not a new phone you need but a new SIM card which can be used in any unlocked phone.
This is true. But people rarely lose SIM cards — they lose their entire phone, which, when replaced, will have a new SIM.
My comment refers to losing a phone. I never buy a phone with a SIM card. I always buy an unlocked phone. If I ever lose my phone, I’d get a new phone and SIM card separately as I don’t like contracts.
In New Zealand we have number portability. So if I lose my phone, and with it the SIM card, I can go to any one of my phone provider’s stores and get them to lock out that SIM cards info thereby rendering it useless to someone who has stolen it or found it. Then I’d have my original phone number attached to my new SIM card and insert it into my new (to me anyway) cellphone.
On top of that though, my phone is password protected, but of course transferring the SIM card to another phone probably won’t stop a thief from using it in another phone. But the phone company can most definitely lock out the original SIM card. I figure that going back to CDMA would in fact be an improvement from a security point of view.
My 2.37859 cents worth. Inflation adjusted of course.
In most cases, a thief wouldn’t be able to use the SIM card. By default, SIM cards are password protected and are locked out after 3 attempts and permanently after 10 attempts with the unlock code. You can block your SIM card with a phone call as easily as with a CDMA phone. I believe it works that way in all countries.
Thanks, Leo, all good info. I would add – Phone secured by a 7-digit PIN. (Probably should be longer.) Laptop secured by a 14 character password, and the disk is encrypted. Nobody can use either one if stolen. (Without encryption, it’s pretty easy to boot from a password reset disk and gain full access to a stolen computer.)
When searching for reviews about Authy on the web, I stumbled upon the next comment to a blog:
“Just a note, if 1 is already using LastPass, it, too, has an Authenticator app, which integrates w/ the service & cloud saves into the account. (Just so 1 doesn’t have to create yet another account w/, e.g., Authy.)”
If that’s true, what would be the benefit of Authy over LastPass, considering that LastPass is frequently recommended here on Ask Leo?
Be clear that we’re ONLY talking about authenticator apps here — the apps that show you the number you need to type in when requested for 2FA. I use Authy to provide my LastPass 2FA token. That means I don’t need to install the LastPass authenticator app — but I do have the LastPass password manager app installed. Basically it’s just one less app to install if you put it all in Authy.
This makes sense and would work for me. However, it appears there are some people who change their number every time they change their phone. Then they have verification difficulties with various sites and accounts.