Three things you’re hopefully already doing

In other words, how do you avoid ransomware?
Let’s look at ransomware — software used to hold your data hostage until you pay up — and how best to protect yourself.
Spoiler alert: you already know the answer.

Avoiding ransomware
- Ransomware encrypts your computer’s data and holds it hostage.
- To avoid ransomware, use the same techniques that prevent any malware: run anti-malware tools, stay up to date, and use common sense.
- Backups can save you should you ever get ransomware.
- Ransomware-specific protections exist and may help, but may add to a false sense of security.
- Never pay the ransom.
What is ransomware?
Though it continues to get lots of press, ransomware is nothing new.
Ransomware is malware that encrypts files on your machine and then presents a message offering to decrypt and recover your files if you pay a ransom. Recent versions attacking businesses also threaten to release copies of sensitive data captured at the same time.
Most current variants use good encryption, so once you’ve fallen victim, the outlook can be pretty bleak.
Note the word I used: malware.
Please understand this: ransomware is just malware. There’s nothing special about ransomware and how it gets on your machine. It uses the same techniques as any other malware. Currently, it is most often distributed in email attachments or as downloads of some form.
Ransomware is very destructive malware, but it’s just malware.
That should give you a huge clue on how to avoid it.
Help keep it going by becoming a Patron.
How to avoid ransomware
You avoid ransomware the same way you avoid all malware.
- Run up-to-date anti-malware tools. I recommend Windows Defender, but there are many, many others. Make sure they are running and up to date.
- Keep your system and software up to date. Yes, this means letting Windows, as well as any applications having self-updating capabilities, automatically update.
- Use common sense. Don’t download random things from the internet, and don’t open attachments you aren’t completely certain are valid.
In short, do all the things you should already be doing to keep yourself safe on the internet.
More importantly, back up
If your machine does contract ransomware, having a recent backup1 can save you almost immediately.
If you get ransomware on Tuesday, restoring to a backup taken on Monday makes it almost a non-event. Aside from any work performed since the Monday backup, you’d have your machine running again in no time, without paying any ransom.
There is almost nothing a good backup can’t save you from. This is another case where even something as scary as ransomware doesn’t need to get in your way.
Ransomware-specific protection
CryptoPrevent is a popular tool used to avoid ransomware. Unfortunately, it doesn’t prevent it.
Once installed, it prevents specific actions many variants of ransomware are known to use. (In rare cases, legitimate applications might require these same types of actions, but it’s rare.)
Similarly, Windows 10 has added explicit Ransomware protection to Windows Defender in the form of controlled folder access.
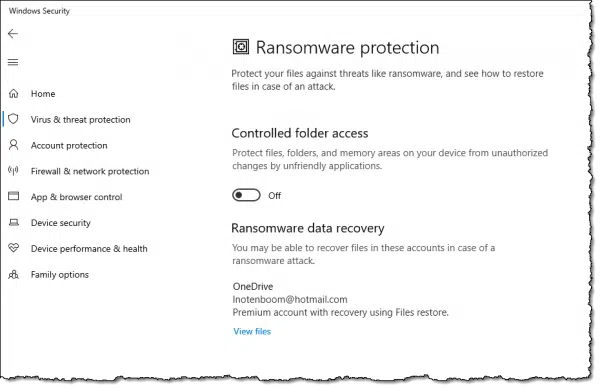
Similar to CryptoPrevent, some applications may have problems if this feature is enabled.
If installing CryptoPrevent or enabling Controlled Folder Access helps you feel safer and doesn’t interfere with something else you need, by all means, feel free to enable them. They’ll protect you from a lot, including some non-ransomware forms of malware. For the record, I use neither.2
My concern with both these approaches is that they focus exclusively on preventing the malware’s malicious behavior, but only after the malware has already infected your machine. In other words, if they helped, it’s because malware made it to your machine.
That’s the problem to focus on. That’s what I believe is most important to prioritize — preventing malware in the first place — and I don’t want any tool or technique to give you a false sense of security leading to letting your guard down.
Should I pay the ransom?
No. Never pay the ransom.
Paying just encourages scammers to keep doing this. Sadly, enough people do pay that it’s apparently turning into quite a lucrative endeavor. Don’t be one of those people.
Stay safe, back up, and never negotiate with hostage takers — even when it’s your data they take.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: Several people have expressed concern that a backup drive, if connected, may also be encrypted and held ransom. It can happen, but to me, it’s much more important a drive remain connected so regular backups happen automatically. More here: Will Malware Infect the Backups on My Connected Backup Drives as Well?
2: I did try controlled folder access some time ago, and discovered that it interfered with some of the tools I use.





Hi Leo
If over the years I have learned anything from from your columns it is “Image Backups”. I do same once a week. If anybody out there thinks this a little wimpish, they should dwell instead on the tremendous freedom and power these give the user. Although it is now years since I have had malware, should and even if when I get again I will always revert to a backup, regardless of what my scanners tell me.
Only codicils would be that other backups are advisable, such as Doc’s, Pictures etc, and that the user should be able to boot directly into the backup. Booting directly into the backups I am guessing varies a lot from comp to comp. Perhaps Leo you might throw some light on this point????
It’s also very important to keep the third party software like Java, Silverlight, Adobe Reader and Flash up to date! We’ve seen many infections come through unpatched versions of the above.
I read in the local paper here threat a local medical business was locked out of their records with ransom ware. Apparently the back up drive was also compromised & locked.
Lesson is do not leave back up drive permanently attached to the computer ..only during backup or reinstall.Perhaps use a cloud solution as well.
Jp
Maybe the backup was performed AFTER the ransomware hit, maybe even after a few days and several backups where backing encrypted data along with the malware itself…
Here, the problem is to always remember to connect your backup drive when performing the backup operation. It’s really to easy to forget to connect, and if the drive is not connected, then the backup operation will fail.
A better option would be to have 2 or 3 backup drives that are used in rotation. In this case, even if you forget to do the rotation, the backup process can still be performed.
I had 2 clients hit with ransomware and it’s not so much that the backup drive was connected. More important is what backup software you run. If it is just a straight file copy then you take your chances. It you are running something like Symantec Backupexec (no plug intended), the ransomware will not encrypt the type of files they the backup software creates. Worked great for us.
johnpro – doing this (not leaving the backup drive attached to the computer) makes running automated backups rather difficult.
A rather cumbersome solution might be to only connect the backup drive at the end of the day and at the same time disconnect from the internet.
Is there are less messy alternative?
Buy a backup drive that has an easily accessible power switch. Turn it on, make the back up, turn it off. You can leave the interconnecting cable (USB 3 recommended) in place since the drive won’t respond to it while off.
I use RoboCopy to make a 5 copy rotation backup of my data files. It only updates changed files and at the end of a normal work day for me it will update a few hundred files and take about 30 seconds to do it. Add a minute or 2 to turn the drive on, allow it to spin up, flush out it’s buffers when “ejected” and to switch it off I’m in it for 2-3 minutes a day to back up.
It’s not an image back up. I do that separately less frequently to the same drive.
For the “average” user, these steps are not good enough. Because the average user has no idea what links and sites to avoid. So…
1) Start at your list
2) Use OpenDNS on the home network
3) Install McAfee SiteAdvisor and only click on Green Checkmark links
Use a user, or limited account, not the administrator account for your day to day computer usage.
I second this: https://www.bleepingcomputer.com/news/microsoft/removing-user-admin-rights-mitigates-94-percent-of-all-critical-microsoft-vulnerabilities/
This a follow up on my earlier post.
In the article a solution to this type of infection is to restore from an earlier backup. In the EBook “Maintaining Windows 7 – Backing Up” automated backup is described in detail. For these to run the external hard drive must be connected.
However in the several references and articles I have seen on malware that encrypts, I have read that backups can also be encrypted (but whether by encrypting the disk or the image files themselves I have not found).
What I have read is advice to not leave an external hard drive connected.
This seems to leave two choices – either do not do scheduled backups, or bet that the protection installed and user competence are such an infection will not get in.
I teach older people coming late to computers, amongst other things, the value of scheduled backing up. I would like to be able to give them good advice on this.
@Dean,
It sounds like the most important thing is to know and follow safe internet practices. If you have a firewall, haven’t downloaded anything suspicious, or clicked on links in emails, then viruses won’t just jump into a computer doing a backup in the middle of the night. So best thing is to teach safe practices.
Thanks Connie.
I do cover the importance of all the usual advice on protective up-to-date software, keeping the operating system and other software up-to-date, not to click on suspect sites etc. And I also recommend at least regular system backups.
Nevertheless I have had two examples of those attending classes where they have somehow got malware.
In one case, action taken was to copy data files to a thumb drive, do a full reinstall of the OS and other software and then add back data files after a check scan.
In the other, a recent backup was available and was used to restore the computer to its uninfected condition. I use this example to emphasise the value of a recent valid backup.
The problem then is – what if the infection encrypts files and has also caught the backup?
The unfortunate user can then no longer get to his files.
Hence the advice I have given that scheduled backups are protection against being trapped into downloading of malware is wrong, if this happens to be of the encrypting type.
“Should I pay the ransom? No. Never.” – I don’t agree. Given a choice between paying a ransom and losing my data, I’d pay the ransom. It all comes down to how much the data is worth to you. That said, the best option is, of course, to make sure you never have to make that choice.
There is no reason to believe that they will unlock your data even if you do pay. After all, they are crooks.
If somebody pays over the money, they’ll almost certainly get their data back Yes, they’re crooks, but they’re also in (illicit) business and it’s in their own interests to provide the decryption mechanism. If it became known that a group didn’t, people and businesses would obviously not be prepared to pay the ransom and their revenue stream would immediately dry up. I’ve actually never heard of a case in which a person hasn’t got their data back after paying the ransom. Even the Assistant Special Agent in Charge of the Cyber and Counterintelligence Program in the FBI’s Boston office advised that payment was often the easiest/only option:
https://nakedsecurity.sophos.com/2015/10/28/did-the-fbi-really-say-pay-up-for-ransomware-heres-what-to-do/
There’s really no point in moralising over the rights and wrongs of paying: it’s up to each person to decide how much their data is worth and whether they’d prefer to lose it or be blackmailed into paying criminals and almost certainly get it back. The best advice is, as I said, to make sure you never have to make that choice.
Let’s not complicated things. I got infected once. I just reformatted my drive, reinstalled my OS and put back my personal data folder from a backup and I was back in business (without messing around with images). The biggest “hassle” was to re-install programs, which I did as I needed them. Quick and simple. If you find yourself having to pay the ransom, then you have number of other problems you need to face: First, there is a problem with your backup and recovery scheme. Next, when paying your ransom, you may have exposed yourself to ID theft depending on your payment method. Finally, how do you know if the ransomware didn’t leave a trojan or other junk on your system which will wake up the next month and ask for another ransom? Remember, the ransomeware guy is smarter than you are. Never pay a ransom.
“Never pay a ransom.” – That’s very easy to say if it’s not your data on the line. If it is your data – and you don’t have a backup – then the decision may be far from easy. As I said, the best option is to ensure that you’re properly backed up and so never have to choose between paying a ransom and losing your data.
I rely on three tools in my arsenal to combat malware, regardless of the type:
1. Antivirus (Windows Defender on my laptop and Microsoft Essentials on my desktop)
2. Sandboxie (to virtualize my browsing and to test any new software)
3. Imaging (scheduled every Monday, Wednesday, and Friday using Macrium Reflect)
Is this combination 100% bullet proof? Probably 99%. If any malware slips by my antivirus, it will be contained in the sandbox and easily flushed. These two tools alone have kept my systems clean for many years. But if something extraordinary happens and an infection occurs, then I’ll just restore an image taken two or three days ago.
Nothing is 100% certain except for death and taxes, but it’s probably better than 99%. I’d add a cloud backup to the mix. Services like Dropbox save your changed files for 30 days, so you should be able to go back to a previous version if your backups become corrupted. This would only protect the files in your Dropbox folders, but I have the paid version and keep all of my personal file in it. It would be inconvenient if it came to that, but I would still have all of my user data.
It’s so good to hear like-minded people doing almost exactly what I have also been doing for years. I am 70+ and always run sandboxed…always! Macrium Reflect backup on Friday each week after a quick cleanup. MSE has been as good as anything as I have not had a problem in years. On top of that its mostly just not being stupid. email attachments from unknown parties…red-flagged websites I really dont need and just knowing that these days you just cant trust anyone. thanks for the nice, reinforcing article. Clas
For the non-techy user the easiest protection is probably paying for online backup such as Backblaze, Carbonite, Crashplan, etc.
This is only safe is syncing is not automatic. I got a case where the business used Dropbox to back up their data (which was held on a single laptop). The Ransomware encrypted all the files on the hard drive at boot time. The Dropbox folder was set to sync automatically, so all the Dropbox content got instantly overwritten with the encrypted version of the files.
Their back up solution turned out not to be much help. Since they only had a basic Dropbox account, they lost all the files that had not been edited within the last 30 days.
“Since they only had a basic Dropbox account, they lost all the files that had not been edited within the last 30 days.” – All files could have been rolled back to previous, non-encrypted versions up to 30 days after being encrypted. The date the files were last edited is irrelevant. Had the business been using Dropbox Pro, it would have had up to a year in which to roll back to previous versions.
As I understand it, the ransomware encrypted versions of the files would look like edited versions to Dropbox. As that’s what they essentially are, so you should be able to find the previous versions.
“So you should be able to find the previous versions.” – So long as it’s less than 30 days since the files were encrypted.
Leo,
Are you familiar with WinAntiRansom? It’s a cousin to WinPatrol (one of my long-time fav programs). Just wondering if you have any opinion about it.
Leo, I’ve long followed your expert advice about image backups and also use Carbonite because I teach 1-week engineering seminars in distant locations and it allows me to access files from anywhere in case my laptop croaks / is stolen. (In case of infected files being backed up you can roll back as far as 3 months to previous versions.) OS updates are out of my hands (Windows 10) but I constantly check apps for newer versions. Finally, my password manager lets me use crazy-long, complex, all-different passwords for each account. You can’t be too careful because it’s a wild cyber world out there.
Carbonite is a good secondary backup. I use a paid
Dropbox[2019 Update:switched to paid OneDrive. For the same price as a Dropbox account, I get license for 5 computers and 1 TB storage each for 5 machines] for that. I had Carbonite for a while, but I wanted more control to know exactly what was backing up. Maybe Carbonite is better for people who wouldn’t be able to set up Dropbox to do that, and Carbonite is less expensive. It also keeps my 3 computers, phone and tabled all synchronized. The fact that I can work seemlessly on all my machines proves to me I have it set up correctly. Before, I had to use Teamviewer to get files from my main computer. I haven’t had to use Teamview for that since getting the paid Dropbox account. Now Teamviewer is mainly for fixing friends’ computers.I have saved my back up sessions on a CD or DVD disc for several years. It gives me a stack of discs but the saved data is not on my computer.
If the data is ONLY in one place (like one of those CDs) then its; not backed up. You need two or more copies to be backed up.
Dispit the use of site block, ghostery, no script and fire walls, some sites still manage to send a new page command which opens with ” your PC has been locked yadda yadda yadda” please be aware that the mear presence of this forced new page does NOT mean your PC is locked. You could be forgiven for thinking so because the open block in the middle of the page is scripted to forbid you from closing the window. BUT, don’t panic – nothing has invaded YET!. To close this window you only need to do 2 things. DO NOT PUT ANYTHING IN THE OPENING BLOCK in the demand window; instead, position the mouse over the window close symbol [ X ] and with your other hand – hit the keyboard exit key and click the exit X window with the mouse immediatly the centre window block disappears. bingo – gone. No matter what is scripted, the script needs time to figure out it;s next move so the quicker these two actions are exicuted one after the other – it will close the whle page before the rest of the script has time to exicute. Hope this helps
Hi Leo. We have a small business which was infected on 12.12.2016 with some type of Ransomware ({email address removed} wanted 22 bitcoins). Unaffordable, so we had the drive removed immediately.
I had backups so although it has been a pain in the @ss- also because we close for the holiday season today- I have recovered everything except some emails.
I had to download some programs and drivers on my second drive (which had been reformatted) and at 4pm on 14.12.2016 the virus started creating files again. So I assume one of those legit websites (I’m thinking the accounting software) is hacked. Or the formatted drive still contains that virus.
Just wanted to let you know my cloud backup and external hard drive were both ransomware encrypted as well- although the three workstations on the network were not. I had another external backup off site a few days old, which is fine.
These people should face a firing squad. Thanks for the page, very helpful.
My strategy for dealing with malware is a defense in depth. I use Windows Defender and paid version of Malwarebytes as second line. Third, I keep UAC active. I activated Controlled Folder Access (it is not a hindrance for what programs I run) as fourth line. I use Macrium Reflect Home (paid version) for backups daily. Macrium Reflect includes Image Guard protection for backup files. It prevents any changes to the backup files unless you are using the program itself to make the changes. I cannot, for example, delete backup files using Windows Explorer.
My first line of defense is me. I pay attention to what I do on the Web and only click on links that are legitimate. Usually, if I have a link in an e-mail, I usually go directly to the sender’s website rather than click on the link.
Image Guard in Macrium Reflect is somewhat new, and I like the concept a lot. Even though backups are rarely encrypted by ransomware, this provides another level of protection that really makes sense.
Is white-list based protection effective? I’ve read of this a few times and even installed a package that uses it. But it was always sending me what seemed to be false alarms and I ended up automatically approving nearly everything it flagged. Then I started wondering why the major players don’t use this, and ended up uninstalling it.
I think you encountered the major objection to whitelist approaches. It’s effective — it can be quite effective, actually — but it can also be annoying to the point of training the user to just approve everything, which negates the effect.
That’s funny. It sounds a lot like the comment I made about UAC. Many people just click through without thinking. Maybe you can do an article on proper handling of UAC warnings.
Doesn’t my Carbonite automatically back me up daily?
It should, but you should confirm that it’s in fact configured to do that. (Not being a current Carbonite users I can’t tell you how to do that — check with their documentation.)
Also be aware that if a file gets encrypted by ransomware, and then Carbonite backs up the file because it changed, you may (or may not) lose access to the original unencrypted file in your Carbonite backups. Again, check with Carbonite to see how they handle the situation.
Carbonite, Backblaze, OneDrive, Dropbox etc. are great secondary backups.
Every Ransomware I have seen the last few years, does in fact encrypt or erase external backup drives. You should always use multiple backup drives and rotate regularly, at least weekly! Another thing i use, and setup for clients, is Macrium Reflect, it locks the external backup drives so that only it can access them, keeping Ransomware from effecting them. Macrium is very reasonably priced and the protection is only provided with the Full Registered Version. Hopefully more backup software will be providing the same protection, sooner rather than later!
My experience is different — I’ve only rarely heard of backup drives being impacted, but it makes sense that that would be on the rise as the ransomware authors get more sophisticated. I do like Macrium’s approach. My concern with disconnecting backup drives is that you then have to remember to re-attach them to get a backup, and many people don’t remember so that when something happens they have no recent backup at all.
I always plug in, backup with Macrium Reflect (free version), then disconnect my external drive. I have a reminder in my Outlook calendar to do this on a regular basis & set up a schedule in Macrium Reflect to start the backup automatically. The reasons I don’t keep my external drive plugged in all the time are 2-fold. I have had several external drives fail ( different manufacturers) after continuously be plugged in 7/24. They don’t seem to have the required longevity internal drives seem to have. I don’t know if that’s because the drives themselves are the lower end models. The current WD drive I use via the scheme above has lasted me for three years now without any problems. The second reason is because malware might sneak through & corrupt the drive, although I am extremely careful & have not been infected for several years now. I run Windows Defender per Leo’s recommendation & also a paid version of Malwarebytes.
Most computers are default to operate in Admin mode, so I created a Local account. Nothing can be installed in this account. Prevents all ransom-ware? Probably not but it’s one more layer of protection and it’s FREE!
And as Leo said, ransomware is just one kind of malware so that would be a layer of protection against all sorts of malware. If you are using Vista or later, Windows has User Account Control. With UAC, although you are an administrator, the computer is running in non-admin mode and any process requiring admin privileges will trigger a UAC warning. It’s a great feature except it can easily become a habit to click through that warning. If you get a UAC “Do you want to allow this app to make changes to your device.” warning when you didn’t explicitly install a program or run a program which requires admin rights, don’t click unless you are sure you initiated the process.
Actually most computers no longer default to Admin mode. That’s what the UAC prompt is all about. You run in normal mode, and then if something needs/wants administrator access UAC pops up and you choose what to do, or not. (Your account being “administrator” really now means “administrator capable”, and the only practical difference is whether or not you need to type a password in the UAC dialog.)
“Several people have expressed concern that a backup drive, if connected, may also be encrypted and held ransom. While technically possible, I believe it remains rare — I’ve not heard of any instances as of this writing.”
Great piece of information, and the reason I keep coming back here.
I do a full image of C: and D: every day through Macrium, and swap the external 2,5″ disks I do it on. So there’s always a disk connected. I just remember to swap it when firing up the computer in the morning.
In theory, some ransomware could, of course, infect silently the backup disks, and delay the actual encryption so that backups would be all encrypted.
From Leo ‘Several people have expressed concern that a backup drive, if connected, may also be encrypted and held ransom. While technically possible, I believe it remains rare — I’ve not heard of any instances as of this writing. ”
Me:
I have only had one computer infected with ransomware and it did encrypt the mobile hard drive files used as a back up.
Why take the risk?. Perhaps alternating hard drives every few days might be an option ?
I had ransome ware about 3 years ago, it was a Europol fake law enforcement site demanding 200 euro for a”fine” to release the computer.
I turned it on and off etc….as soon as I opened the same browser the problem started with the page came back up and wouldn’t close.
Turned it off again with the power button, turned it back on, got the message “windows didn’t shut down correctly, would you like to restore pages?” Answer: NO!
Opened CCleaner, ran cleaning….CC asked that “Chrome is taking a long time to close, would you like to force it to close?” Yes!
Problem solved. Europol fake page gone forever.
Cleaned the comp further after that and ran malwarebytes etc.
A few months ago a friend had a similar problem on a laptop. He just left it turned off for 3-4 weeks and turned it back on, ransomware page had gone and comp back to normal.
Leo,
[I’ve followed your column for years, and have two of your books.] I’m wanting to ask about an aspect I haven’t yet seen in your writings or any of the comments. I use cloud storage (OneDrive, Google drive, and DropBox) heavily, not as a “backup”, but rather for portability (I access my files from several computers, phone, tablet). I have even re-mapped my standard Windows User folders (Documents, Desktop, Pictures) to OneDrive folder locations. If I suffer a malware attack, all of these files could potentially become locked (encrypted) — which would impact every computer accessing those files (correct?). I’m assuming the malware would potentially spread to each PC as well. Restoring from backups would be complicated enough, because it would need to be done on every computer; but how to expunge the corruption from all cloud locations — simultaneously with the computers — has me pretty nervous. This goes beyond a “normal” restore scenario. You’ve talked about cloud storage, drive encryption, regular backup, and safe internet use; but I haven’t read anything addressing this specifically. Do you have ideas on this?
I’ll probably address it more completely in the coming weeks, but OneDrive, and now DropBox, have a feature I’ll refer to as “roll back” specifically for this scenario. IF you suffer a ransomware attack you can tell these services to reset all your files to the state they were in prior to the infection (you basically pick a date prior to it having happened). I love this. The only caveat is that I believe this feature is not available in the free versions of the products.
For $100 a year, you get 5 MS Office licenses and 1TB OneDrive storage for each license. A great bargain. I pay for MS Office mostly because of the storage. I used to pay for Dropbox, also great, but I find Office with OneDrive is the better deal.
I use Malwarebytes Premier at the moment and I use Macrium Reflect for my backups. I run a backup of ALL of my data at 9am every morning, this is sent to an external SSD and then I run another backup of this data at 10am daily to another external SSD, giving me two backups of my personal data. I also run a backup on the first day of the month of my C: drive which holds the O/S and my programmes and, this is sent to a third external SSD.
Whilst I am reasonable on a pc and find Ask Leo invaluable, as an 80 year old wrinkley am I doing things right?
P.S. I am also a big fan of LastPass and use the paid-for version.
You’re doing great — very similar to what I do.
If you want to take it next level, this article has an additional idea to consider: Should I Disconnect My Backup Drive When I’m Not Backing Up?. NOTE: I’m not saying you need to change a thing, but some folks like to take one additional step. (FWIW: I don’t.)
Guilty as charged I’m afraid. Time for a re-think. Thank you.
Wouldn’t running an add-in like No-Script be an extra layer of protection? In case you go to a rogue site, No-Script would block rogue scripts from executing.