Scammers try to fool you.
There are several ways to hide where links go. But the good news is, the most common approaches are the simplest to detect. There are several ways to look at a link (both in email and on webpages) before you click on it to make sure it is what it claims to be.
So let’s go about disrobing those cloaked links.

Links can lie
What you see isn’t always where you’ll end up. Hover your mouse pointer over a link to see its true destination (usually shown at the bottom of your browser window). If it looks weird or doesn’t match, don’t click. Copy/paste if you’re unsure. Always look before you click, especially in email.
The anatomy of a link
First, a little refresher on what a link is. There are two parts: the part you see and the part you don’t. For example, if I give you this link:
The part you see is “Ask Leo!“. The part you don’t see is the URL the link will take you to, called the target: “https://askleo.com“. To get a little geeky for a moment, that link is encoded in HTML. It looks like this:
<a href="https://askleo.com">Ask Leo!</a>
In HTML, you can see exactly how both parts, seen and unseen, are encoded.
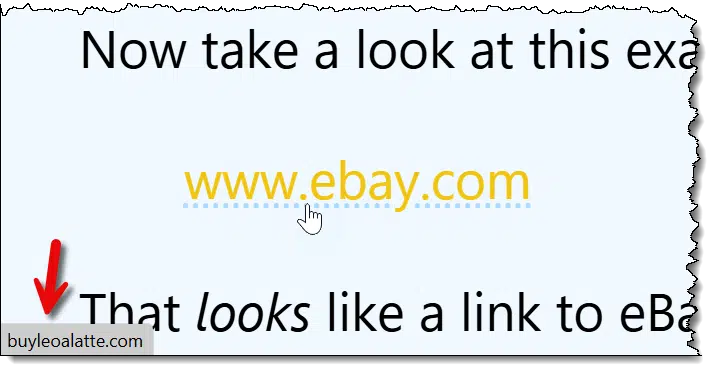
Now take a look at this example:
That looks like a link to eBay, doesn’t it? Here’s how it’s really encoded:
<a href="http://buyleoalatte.com">www.ebay.com</a>
The part you see is “www.ebay.com“, but the target you don’t see is something else entirely: “http://buyleoalatte.com“. When you click on it, it looks like it’ll take you to eBay, but it will instead take you to buyleoalatte.com.
This is a basic component of phishing: making it look like you’re going to one place when instead you’re taken somewhere else entirely. Usually (though not with our example) it’s with malicious intent, taking you to a site that looks just like the one you expect but is not.
Help keep it going by becoming a Patron.
Hovering
Hovering your mouse pointer over a questionable link is one way to determine its validity. All that means is you move the mouse pointer over the link but don’t click.
Using the example above:
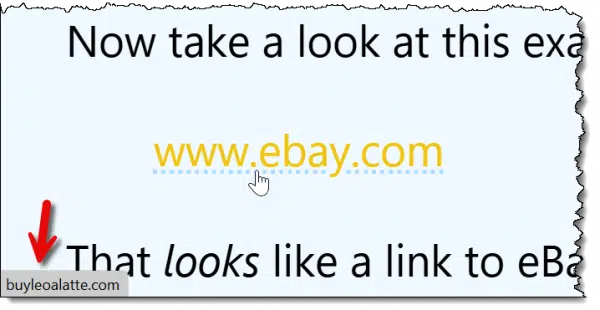
In the Edge browser, I’ve moved the mouse pointer over the “www.ebay.com” link. When I do, Edge changes the mouse pointer to a pointing finger and displays the target link in the lower left of the window.
Most browsers show you the target of the link somewhere near the bottom of the window. Sometimes it appears as a pop-up or tooltip.
You can see that my mouse pointer is hovering over the link that says “www.ebay.com”, but Edge is showing you the URL you’ll really be taken to: buyleoalatte.com.
This isn’t just about webpages and web browsers. Email often contains links, and that’s where a lot of scams happen.
If you view your email in a web browser — say by visiting outlook.com or gmail.com — everything I’ve described above should work for the links displayed in messages. If you’re using an email program like Thunderbird, Microsoft Office’s Outlook, or others, most behave just like web browsers: if you hover the mouse over a link, somewhere it’ll display the true destination of the link — most likely in the status line at the bottom of the email program’s window.
Copy/Paste
Another excellent approach to validating a suspicious link is to use copy/paste.
Rather than just hovering over it, right-click on the link you’re uncertain of.
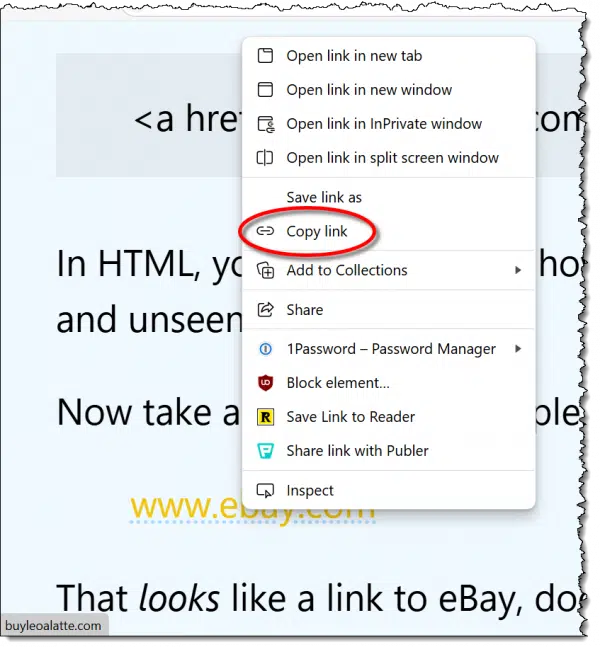
In the resulting pop-up menu, click on “Copy link” (or its equivalent) in your browser or email program. This copies the target — the part you don’t see — to the clipboard.
Now, right-click on the address bar in your browser.
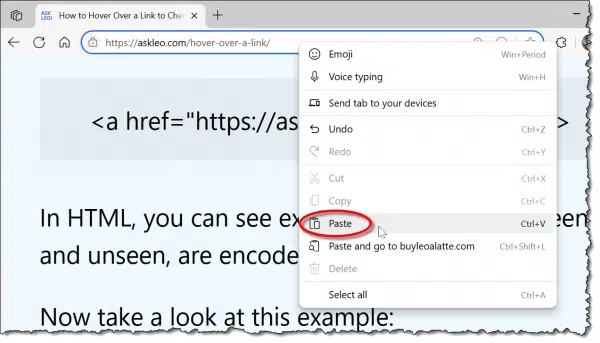
Click Paste (not “Paste and go”, if that’s available) to paste whatever was copied. Don’t hit the Enter key, which will take you to the webpage; just read the target link.
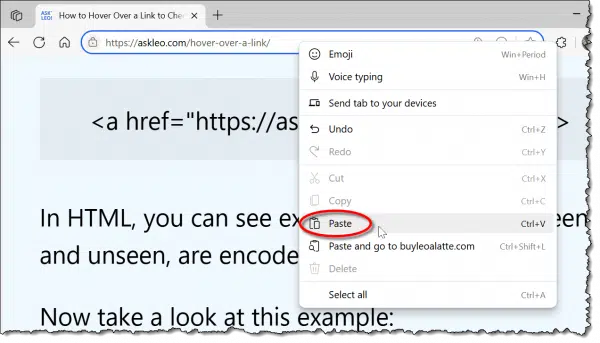
You can now see what was pasted. This is the true target or destination: the part you normally don’t see and the site you would have been taken to had you blindly clicked the original link. In this example, it’s fairly obvious this link wasn’t going to take you to eBay at all, but to some other site.
- If it’s a link you want to go to, press Enter and you’ll go there.
- If not, press ESC and it’ll be erased from the address bar.
You can, if you prefer, paste that URL wherever you like. Pasting it into Notepad is one option. That way, you can see exactly what the destination is without risking accidentally going there in the browser.
Dealing with mismatches
All this is to get you information from which you can make a decision. It doesn’t mean that every time things don’t match it’s a scam or something nefarious.
Here’s one example of my own:
That looks like a link to the Amazon Kindle, and if you click on it, that’s exactly where you’ll land: the Kindle product page on Amazon.com.
However, if you hover over that link using the techniques we’ve discussed here, you’ll see it actually goes to “https://go.askleo.com/kindle“.
So what’s the deal?
If you’ve ever used a service like tinyurl.com or bit.ly to make an excessively long URL into something shorter, this is the same idea. I have a private equivalent of a bit.ly. In these cases, there’s a database that maps a short URL or token (like “kindle”, in my case) to the original, longer URL.
When you click on the shorter URL, the service automatically and transparently redirects you to the longer destination URL.
So in this case, these two are identical:
Hover over each and you’ll see that they’re quite different, but click through and you’ll end up at the same place.
I point all this out because it’s extremely common, particularly in newsletters and other legitimate marketing emails. Links are often routed through third-party services, not just for shortening. Additional uses include:
- Counting clicks. For example, I can tell that “kindle” link has been clicked on 12 times in the last seven days. This lets me know how popular it is.
- Adding information such as affiliate codes. The links above include my Amazon affiliate code, which tells Amazon where the link came from. If you purchase a Kindle, I’ll get a small reward. (More about this in my affiliate disclosure.)
- Tracking clicks. This information can track who clicked on which links. This is most common in the email newsletter business, where redirection links can determine which recipients clicked on which link or who opened a newsletter.
So how do I know what’s legitimate?
It’s not always easy to tell what is or is not a legitimate link or an attempt to fool you. I’d claim, though, that most of the time, it’s not hard.
Suspicious signs include:
- Obvious misdirection. If the “part you see” looks like a URL or domain name like “www.ebay.com”, then the destination, the “part you don’t see”, should probably match.
- Links to IP addresses. If the destination is an IP address (something that has only numbers like this: http://67.227.211.203), don’t trust it. Legitimate sites always have names in text.
- Links to foreign domains. With all due respect to the legitimate businesses in those countries, destination links to domains that end in “.ru”, “.cn” (Russia and China, respectively), and others should be suspect. Certainly, if you don’t expect to be taken to a website in a foreign country, this should raise a red flag.
There are others, but those are the most common.
And again, any one of those doesn’t mean the link is a scam; it just means that it fits the characteristics of links that are. It means you should pay a little more attention before clicking through.
Do this
Look before you click. Hover over the link, or copy/paste it somewhere so you can confirm it will take you where you expect. Only when you’re certain it’s safe should you click.
Hover over this link: subscribe to Confident Computing, and then click through! My weekly newsletter is all about less frustration and more confidence, solutions, answers, and tips in your inbox every week.



Hi Leo
How does this work on a touchscreen tablet, please? Sorry if this is a dumb question.
No, that’s a great question! It … varies. Sometimes long-pressing a link will, instead, show you where it goes. Or offer you a copy option so you can paste it elsewhere before going to it. If there’s still a mouse pointer (as there might be on a touchscreen laptop or tablet) you can often move the pointer over the link without clicking on it as well.
O.K., two things:
(1) On a Kindle (how serendipitous! — I’m using a Year-2016, 6th-Generation Amazon Kindle Fire HD8), the equivalent action to a “hover,” is to “hold” on a link (i.e., place your finger or stylus on the link, don’t move, and wait a few seconds). A “pop-up” menu, similar to this article’s second illustration, should appear, except that above all the available options, in a slightly smaller font, will be the link’s actual target.
(2) Leo, you used a link of:
https://www.amazon.com/dp/B07FKR6KXF?tag=askleo-20
Please be informed that Amazon also has their own link abbreviator! The “short form” for the above link, is:
amzn.com/B07FKR6KXF
The only two disadvantages I’m aware of are (a) the target is not “https,” and (b) the target is not “AmazonSmile.”
But it most surely does take you directly to whatever product the ASIN represents!
My links also go through my own (go.askleo.com) so that I can count how many times they’re clicked. Not something I can do (easily) with anyone else’s shortener.
In Firefox and Thunderbird, it says Copy link location instead of Copy link address when you right-click on the link.
Is it possible (on a Windows 11 PC) to completely disable the “display URL when hovering over hyperlink” in websites? I am frustrated because the URL is always displayed over the horizontal scroll bar at the bottom of browser window making it difficult to navigate around websites, especially those that contain many ads and popups. For some reason, this has become a problem in both Microsoft Edge and Chrome only in the past couple months.
Not that I’m aware of. It’s an important security feature.
I remember being able to click on a link in Thunderbird (email), and a box would popup saying do you want to go to the (actual) destination or the links apparent destination (the cloaked link which forwards you on to the true destination) – for example it says its going to YouTube but it goes via their email marketing service provider first then redirects to YouTube, so they can scrape the marketing click information. In other words, an option popped up to click on going to the true destination direct rather than via their marketing link.
I no longer seem to be given that option, possibly because I updated Thunderbird to the latest generation and maybe it was a plugin that I was using but I can’t seem to find one.. When I click on a link it just goes to straight the redirect via the marketing provider.
Are there tools that perform this same function, easily, that is, as I believe there are websites where you can enter the link and it will tell you the true destination… but that’s a few extra steps.
Thanks for your help.
Yes, there are websites that will show the true destination of a link. There is a list of some of them here
https://www.defensivecomputingchecklist.com/LinkExpanders.php
Some show the intermediate steps as the link is re-directed over and over. Some offer an opinion as to whether the ultimate destination is trustworthy
And in case anyone’s wondering, Michael’s website(s) are trustworthy.
Thanks for the resource.
Just to clarify, if the link in the email says ‘YouTube XYZ Video’ (which is the ultimate true destination, but the actual link is something like Mailchimp/../../tracker etc. , which is being used to see if I click the link, and I put it in one of those link expanders that show the ultimate link. Does it register as I’ve clicked the link with Mailchimp?
I’m just trying to avoid the tracking/snooping.
I believe it does yes. (There may be techniques to avoid that, but this is where it gets really technical and highly dependent on the actual tracking technology being used.)
why do you have that large window window on the left of the screen that blocks your article?
“I” don’t. It’s likely an advertisement. That’ll get resolved this summer.
I often get suspicious emails while on my iPhone but I have to wait until I am on my computer to be able to hover over the link. So how do you check on an iPhone or any cellphone?
Long press often either displays or copies to clipboard.
Great information, thank you!!
Great advice and something I’ve been using for years. Here’s another telltale:
I use Thunderbird to access my Gmail account. One thing I’ve noticed is that spam messages often have a large amount of unrelated text at the bottom of the spam message. Just scroll all the way down to see it. It’s almost always the same text, indicating that it’s coming from either a single spammer or it’s a spammer using a spam generator he’s purchased. This text is not displayed in the Gmail web client, nor is it displayed when I forward the spam message to my Tuta secure email client. Here’s what I see in Thunderbird following the spam message:
===================
You don’t have to climb a mountain to experience the woes of elevation. Plenty of favorite travel spots perch on high, such as Cusco, Peru, at 11,152 feet, and Leh, India, at 11,550 feet. At altitude, there’s less oxygen in the air, which can leave you gasping for breath just trying to walk up a street. (Discover nine mountains to summit in a lifetime.) What exactly is happening to the body? “First it increases breathing, which can feel like a shortness of breath,†says Peter Hackett, director of the Institute for Altitude Medicine in Colorado. “Second the blood vessels in the brain expand, so that there’s more blood and therefore more oxygen. That gives the sensation of a headache.†Symptoms of acute mountain sickness, or AMS as it’s known, include trouble sleeping, nausea, loss of appetite, and fatigue. If you keep going higher and ignore signals from your body, you could develop HAPE, high altitude pulmonary edema, or HACE, high altitude cerebral edema, both of which are very serious. All that said, some of the best views on Earth are seen from up high. The key to your success? Go up slowly. Ascending over two or three days, if possible, and using these tips will help you feel good at the top.
Thank you for this, Leo! It’s about time that a clear, detailed explanation exists to help others do what I’ve been doing since I became aware of email and hyperlink scams. I’ve tried to explain what I do as a matter of course with hyperlinks on webpages or in email messages, but my explanations are always too ‘geeky’ for my non-technical friends/associates.
Ernie
The same effect applies to the small down arrow near the email address. One can usually see the email of who sent it.
That depends on which email program or email website.