(Particularly if it’s been turned on without your knowledge.)
I’m going to assume you’re talking about BitLocker’s full-drive encryption.
I also assume you understand that with Bitlocker turned off, anyone who steals your machine can access all the files on it, even without knowing your Windows log-in password.
Turning off BitLocker and decrypting your drive is a snap.

Decrypting Bitlocker
- Sign in.
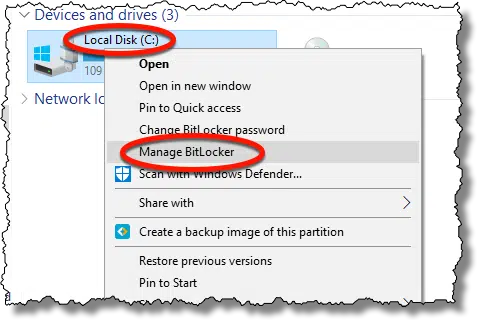
- Right-click the drive in Windows File Explorer.
- Click on Manage BitLocker.
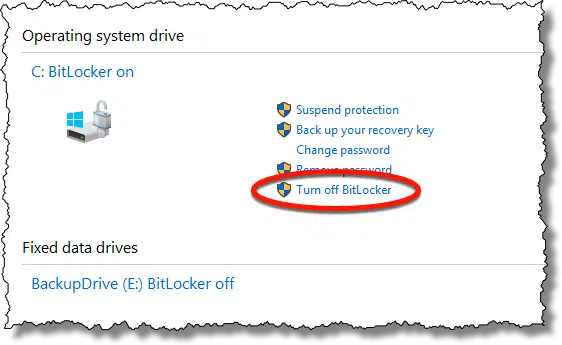
- Click on Turn off BitLocker.
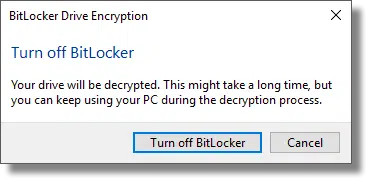
- Click on the Turn off BitLocker confirmation button.
- Wait for the operation to complete.
Decrypting a BitLocker drive
Boot your machine and sign in to Windows. Yes, this step is required. If you cannot sign into Windows, you will not be able to decrypt the drive; that’s kinda the point of the security BitLocker provides.
Run Windows File Explorer and right-click on the drive you want to decrypt. In the resulting context menu, click on Manage BitLocker.
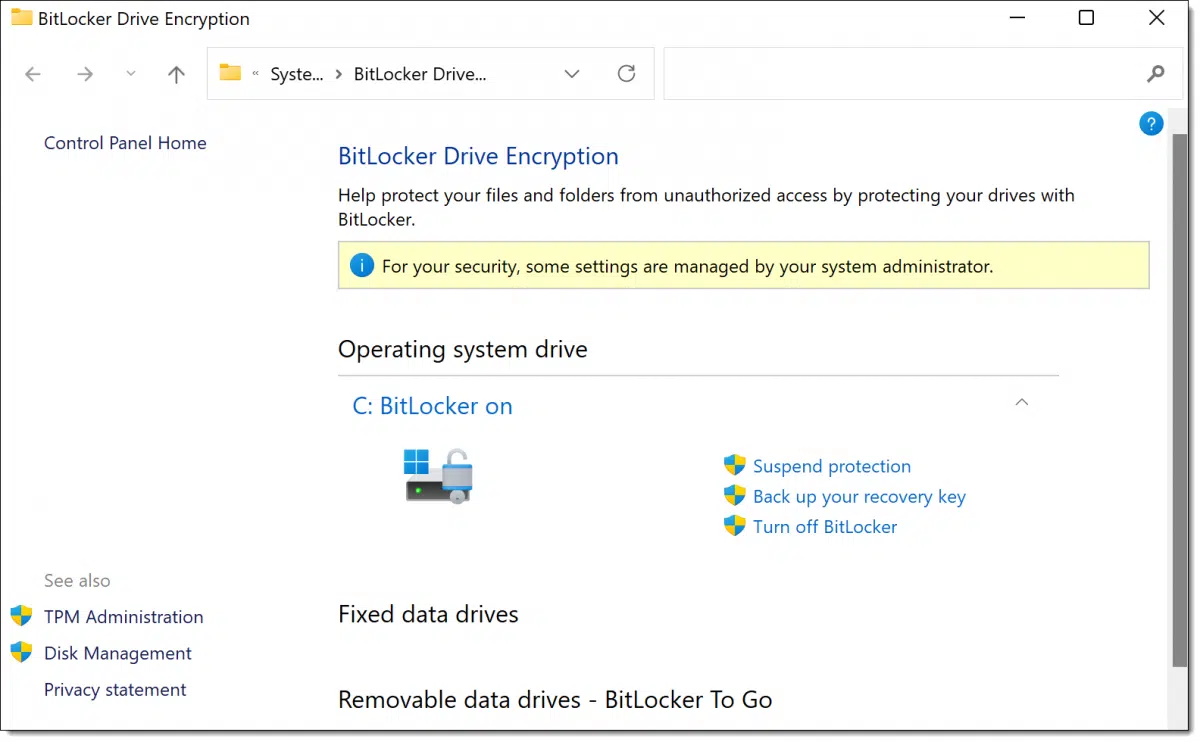
In the resulting dialog, click on Turn off BitLocker.
Click on the Turn off BitLocker button in the subsequent confirmation message box.
The system goes to work decrypting your drive.
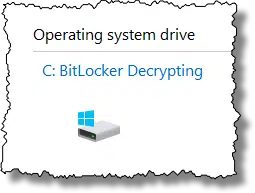
As the message said, decrypting can take a while. How long depends on the speed of your hard disk, the speed of your computer, and the amount of data you have stored on that drive.
After a while, the process completes.
You’re done! BitLocker has been turned off on that drive and the data decrypted.
If you can’t sign in
As I said, the point of Bitlocker is to prevent unauthorized access to your data, and “authorized” means you can sign in to your machine. If you can’t sign in, you can’t decrypt the data on the hard drive.
Unless maybe…
Check out Find Your Lost Bitlocker Recovery Key in Your Microsoft Account for a straw to grasp at.
Do this
- Check to see if Bitlocker is enabled on your drive.
- If it is and you want it off, follow the instructions above.
- If it’s not and you want it on, click on “Turn BitLocker On” and follow the prompts.
- If you use BitLocker, be certain to save the recovery key.
- Regardless, back up your drive .
- Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.




I was thinking to buy a TPM before trying to encrypt with BitLocker, but why I do not sell it in Japan.
Since it can not be helped, it was not amazon.co.jp but was about to create an account on amazon.com.
I felt BitLocker did not have to do it at all.
My main concern with BitLocker is that it would appear to me that Microsoft has a key to my machine stored under my Microsoft account which can be stolen by hackers or “shared” with others. I am not comfortable with anyone having any access to my machine. Am I wrong about this?
Stolen by hackers only if they hack into your account, at which point you’ll have much larger problems. In my opinion the safety of keeping it in your Microsoft account should you ever need it outweighs the risks that concern you.
I just set up a new Dell Inspiron laptop for a long time client.
It came with Windows 11 and BitLocker was already on.
I only discovered that when I set up the older Windows 7 backup and created in IMAGE.
I got a warning that the IMAGE would not be encrypted in spite of BitLocker being in use on the built-in SSD. That was my first clue that it was on.
I have VERY mixed feelings about this because generally my experience with clients and encryption is that they will EVENTUALLY lose all access to the encrypted information.
One client’s “solution” to this was to put the recovery key on a slip of paper and tape it to the laptop!
That sort of defeated the whole purpose but, who was I to (try to) tell this (very aggressive) person that! They were not much into critical thinking. I could say more. I won’t!
You couldn’t convince them to, at least, hide that password somewhere less obvious?
It appears that Microsoft is now making Bitlocker available on all Windows versions, including the Home versions of Windows 10 and 11. It used to be that to use Bitlocker one needed the Pro version of Windows or make changes in the registry of the Home version.
https://docs.microsoft.com/en-us/windows/security/information-protection/bitlocker/bitlocker-device-encryption-overview-windows-10
Or am I misreading the article? all my computers have the Pro version of Windows installed and I’ve been using Bitlocker for years.
Interesting:
What’s interesting to me is that this doesn’t match my experience — at least not with the available UI in Windows. I’ll double check.
What’s more interesting is that this also outlines the conditions under which Bitlocker might be enabled automatically. Thanks for the link!
I have a 500 gb SD card that I encrypted long ago. Bitlocker still accepts my password & unlocks, but when I attempt to turn it off on the drive I get an “Incorrect Function” message. Looks like I’ll have to copy it all to another drive, then format the SDCard. Sigh….
When I built this desktop PC, I decided that it should have more storage that I expect to ever need. I have a 1TB Sony M.2 drive and a 2 TB SSHD drive installed. I dual-boot Windows 10 with Neon GNU/Linux so the 1 TB drive has two partitions, 1 for Windows and the other for GNU/Linux.
The second drive also has two partitions, but both are currently for Windows. The first (labeled data) is used to store various image files for all the OS and utility installers (such as System Rescue, etc.) I usually use, installers for many of the Apps I use (Core-Temp, rufus, MD5 and SHA Checksum Utility, etc.), and many files I don’t want to store on OneDrive but that I still want to keep.
The other partition (labeled MacriumBackup) is for my backups. I use Macrium Reflect to create a full system backup monthly, and an incremental backup daily. I keep two complete backup sets so I can go back up to two months to recover an older version of a file if need be. I also sync my C: drive to OneDrive so most of my files are stored there too. I can access them from my desktop or either of my two laptops and if I have to re-install Windows on any of my PCs, my files will be accessible afterwards.
All my Windows partitions on my desktop and my newer laptop are encrypted with BitLocker. I have the recovery keys stored in my Microsoft account and I have hard copies stored in a safe in my office/computer-room.
My logic works something like this. I use Windows 10. I use Windows 11. I use Microsoft’s BitLocker to encrypt my Windows partitions. I use Microsoft’s Windows Defender as my antimalware suite. I use Microsoft’s Authenticator for 2FA to enhance the security of my Internet accounts. If I trust Microsoft enough to use all of these (especially Windows), why would I not trust them enough to store my BitLocker recovery keys in my Microsoft account which resides on one of their servers?
To understand how good Windows Defender really is, read this item:
https://www.neowin.net/news/microsoft-defender-beats-out-several-heavyweight-rivals-in-the-latest-av-test-ranking/
The odds are that my desktop PC will never get stolen, but if it is, the thief will not be able to rob me a second time by being able to access all my Internet accounts (especially my bank account) and other personal information.
At some point (after I settle on a GNU/Linux distribution – I keep changing my mind about which of several distributions I like the best) I will also encrypt my Linux partitions too (for similar reasons).
I know this post is not entirely on topic, but BitLocker is an important part of the larger discussion about computers and computer security. I’m sorry if I went to far off topic. I didn’t mean to,
Ernie
There’s a serious flaw in your backup regimen. You are not protected against a system drive failure. If that drive fails, your backup dies with it. Backups must be saved to an external drive, and the farther away the backup drive is from your computer, the safer it is.
Can I Back Up to an Internal Drive?
How Do I Back Up My Computer?
The only comment I have is that I’d still keep the BitLocker key locally somewhere, in addition to in the Microsoft account. If the account ever gets hacked, or you lose it for any reason, then you lose the key with it.
Its true, I have noticed BitLocker already turned on for boot partitions on many new PCs. I’m sure it could have slipped past me turned on for many others as well.
The first thing I do is turn the dang thing off. BitLocker creates many complications. For example, you can’t resize the encrypted partitions (or move them). Most disk imaging software will not work on BL drives. If the PC fails and you need to migrate the data from the old drive (which very often is good), it is not possible. You can’t access the drive on another PC to fix problems, remove malware, or save data. I’m not sure you can clone those drives with some tools (I haven’t tried that).
“Most disk imaging software will not work on BL drives.” -> Macrium Reflect and EaseUS ToDo will both work. They back up the UNencrypted contents of a Bitlocker encrypted drive.
” If the PC fails and you need to migrate the data from the old drive (which very often is good), it is not possible.” -> Not quite true. If you have the Bitlocker recovery key you should be able to access the drive’s contents on another Windows PC.
But yes, it’d definitely an added complication.
Life has been easy with True Crypt and am now finally using Vera Crypt on my newer machines. I also refuse to create a Microsoft Account. Now I am concerned that Bit Locker will encrypt without my permission.
Unless your computer comes with Bitlocker turned on, Microsoft will not turn it on automatically, but as long as you are using Veracrypt, you are equally protected.
And if you do find BitLocker turned on, turn it off. Simple as that.
I bought this Dell 8930 a year ago, and it came with Win 10 Home. I’ve searched (in the Win system) for Bitlocker and it just sends me to the Web so I assume it’s not on my machine. If Microsoft now permits using Bitlocker on a Home version, would it work on a year-old Win 10, and if so how do I get that and install it?
I don’t believe you can. Sorry.
I couldn’t find Bitlocker on my Win 10 machine, so I installed the free Veracrypt and set it up to encrypt the whole system drive. I have to type my password before starting Windows, but other than that, it’s completely transparent.
We recently got this question:
” . . . I could not find Bitlocker when I searched for it.”
I followed the instructions in this article, and I couldn’t find it either, so I tried the following which worked:
Right-click the Window Start icon and click ‘Settings’
Click ‘System’
Click ‘Storage’
Scroll down to and click ‘Advanced storage settings’ under Storage management.
Click ‘Disk & volumes’.
Click on the drive that you want to decrypt and click ‘Properties’.
Click ‘Turn on BitLocker’ and follow the instructions to configure Bitlocker
The question was about turning off Bitlocker, but the steps are the same until the last one.