The risk that’s often overlooked
I wouldn’t say incredibly stupid. But it’s definitely an additional risk, and one you need to understand.
You’re correct in considering physical security first. People often assume they have more physical security than they do.
And master passwords? Well, they’re important, but they have limitations.
Become a Patron of Ask Leo! and go ad-free!

- Letting your browser remember passwords can be risky.
- When you do, it’s easy to view actual passwords.
- If you let your browser remember passwords, specify a master password to prevent unauthorized access.
- For better security and greater convenience, use a dedicated password vault instead.
Remembered passwords in a browser
If you have your browser remember passwords for you and you’re wondering why this is even an issue, do the following in Firefox:
- Type the ALT key to expose the menu bar
- Click on the Tools menu
- Click on the Options menu item
- Click on Privacy & Security in the left-hand pane
- Scroll down to “Logins and Passwords”
- Click on the Saved Logins… button
This page lists the sites for which you have login information saved. Click on one in the left-hand pane, and you’ll see information about that login.
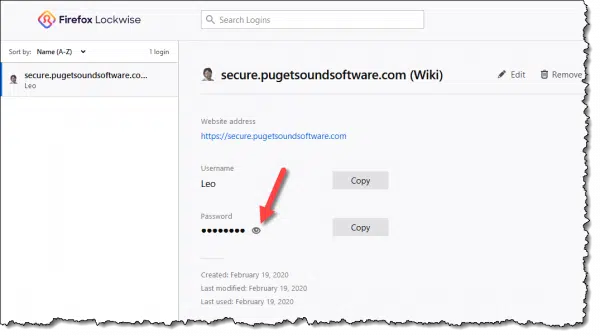
Click the eye icon next to the row of dots representing the password, and you’ll see the actual password.
A few clicks, and all your passwords are visible.
Most browsers let you do this; here are instructions for Google Chrome, for example. Internet Explorer and Edge use the Windows credential store, which you can also use to examine saved passwords.
This should have you thinking very carefully about your security.
Anyone who can walk up to your computer is able to examine your passwords quickly and easily.
Letting the browser save your passwords
If you allow it, most web browsers maintain their own database of usernames and login information collected on your behalf. It fetches the information as needed and fills it in for you. Convenient!
Unfortunately, there are a couple of security issues.
First, the database is sometimes not quite as secure as we want it to be. While this has definitely improved over the years, depending on the browser it may be possible for a hacker to extract the contents should they gain access to your machine. There are even utilities that display the database contents, including the passwords, for some browsers.
Second, most people fail to place a “master password” on the database. A master password further encrypts the database and prevents hacker access, but it does something much more important: it prevents casual access.
This is the real issue I see. If you have your passwords stored in the browser’s password vault, anyone can walk up to your machine and wreak all sorts of havoc. They may also be able to view passwords and make off with them.
If you’re going to use your browser’s password vault, I strongly recommend you place a master password on it. In addition, if the browser supports it, instruct it to require the master password more often than just once when you start using the browser — perhaps again after some amount of time has passed.
Let a utility save your passwords instead
I’m a strong believer in using dedicated “password managers” or “password vaults”, explicitly designed to keep website logins and much more secure.
Like the browser, these tools store your information in a database on your machine. Unlike your browser, however, a master password is required. You’ll get nothing out of a password vault’s database until you’ve specified your master password.
In addition, you can add more security:
- You can specify the master password be re-entered after a period of inactivity.
- You can configure certain logins (like, say, your bank’s) to require you to re-enter your master password before they can be used.
- Two-factor authentication can be enabled, requiring you to enter both your master password and a second authentication factor in order to be able to access your vault.
Password managers often store your encrypted information online. This is done so you can use your vault’s information from anywhere, on multiple machines and devices.
The reason I prefer these tools is that when the tool is implemented properly your master password never leaves your machine — it’s not stored elsewhere, period. It’s used only on your machines, and only to encrypt and decrypt your information on the machine. Even if the information stored on the tool’s servers were compromised, all the attacker would get is encrypted blobs of information they could do nothing with. They would not get your actual usernames or passwords.
It’s important to use password vaults properly. Configure them to require that master password periodically, and don’t walk away from your computer in a situation where someone else could walk up to it and begin using it.
What about cookies?
Cookies are not used to remember your password.
Cookies simply remember the fact that you’ve logged in. They remember that you did, indeed, specify the correct username and password when requested. Cookies prevent you from needing to specify a username and password for every page you visit after logging in.
The service puts a bit of data into a cookie — securely, and understandable only to that service — allowing it to remember who you are and that you are logged in.
Cookies typically expire after “a while” (as defined by the service). All that means is you need to log in again every couple of hours or every day or so, even though your browser never left the website.
This is also why explicitly clearing cookies forces you to log in to all sites when you return to them.
Mitigating the risk of browser-remembered passwords
What can you do? There are several approaches.
- Do nothing but rely on physical security. You must be certain about your physical security and know your machine cannot be easily stolen or accessed.
- Use a master password. A master password is used to encrypt stored passwords stored in your browser. In theory, you cannot access the stored passwords without it. Make it as strong as is practical.
- Clear the list and stop remembering passwords. Don’t use your browser to remember passwords.
- Use a dedicated password vault instead. If you want your computer to remember passwords, it’s far better to use a reputable application designed solely for the purpose of securely storing your information.
What I do
I’m a big fan of password managers1.
- I disable the “remember password” feature in all my browsers.
- I use a password manager to store all my password information. All of it.
- I use the password manager to generate long and strong passwords. These days, that means 20-character passwords like vx6RKPj4TDQ8Teq4TBsA. As a result, I couldn’t tell you the password for many of my accounts; I rely on my password manager to provide them as needed.
- On my mobile devices, the password manager is configured to require the master password after a period of inactivity.
- On my laptop, I require two-factor authentication in addition to the master password.
This is what I recommend you do as well. Don’t use the browser’s “remember password” feature, but instead rely on a tool written specifically to do so. Add additional layers of security — like reprompts, timeouts, and two-factor authentication — for the devices you use in potentially less-than-secure environments.
And as always, make sure that the master password — whether it’s for your browser or a password vault — is strong and secure.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!





Firefox uses the RC4 algorithm to encrypt the password file. Brute force attack using the known cracker will take years to crack if the master password is a long passphrase. After all, brute force can be used to attempt cracking even Roboform. So, in theory nothing is safe, but practically speaking the FF master password system is adequately secure.
There is a nice Firefox addon called LastPass that will save your passwords for you. Everything is stored in the “cloud” and not on your machine. You just log into your LastPass account with a password of your choice and they take care of filling in usernames and passwords. As an added feature, LastPass also handles form filling and supports multiple profiles.
Last pass has been hacked a few times, the last time was some months ago, even though they claim no information was taken but you never know do you.
They have never been “hacked” to my knowledge, and if so exactly and only once. They’ve noted “suspicious activity on their network” and warned everyone – which is not a hack as no data was stolen. No unencrypted user data has ever been stolen from LastPass, because they don’t have the means to decrypt it on their servers. They don’t have the decryption key – only you do.
Absolutely, great tool and being on my phone means I have password to sites I am permitted to view at work available, which incidentally includes a dozen just for my company alone so I can function as a manager where they base me, most of which resources are cloud based and insist on strong passwords.
Don’t forget the Quick Dial Syndrome. Not using your passwords all the time means you will forget them when you have to enter them manually again!
hello leo. thank you for the information. my next question is now do we burn things on the computer. i wish you a happy new year.
Well, I feel motivated to do something more about password security… but I’m not sure what? Maybe get a small flash drive and install Roboform on it?
I keep passwords in an Excel file and password protect that file. They are always with me and I understand that this is very hard to crack and gain entry to the file.
amherst college says to lock your computer…will that make it safe?
xp/vista…windows-key+l or options+l….seems to me if you can lock it, a few folks know how
to unlock it and help themselves? tu for your
hard work…
01-Jan-2010
By having the browser remember one’s password does not seem all that secure. I’m OK with typing in the password each and every time. However, when one uses a computer at work or in some public places, there is always the risk of key loggers being installed in the computers. So, which method would be better for privacy and security.
05-Jan-2010
Leo,
You could enable FIPs encryption in Firefox. It is little known that FIPs is standard on Firefox and can be enabled under advanced options and under encryption devices. Cracking a master password with FIPs enabled and a salt is virtually impossible.
TrueCrypt can’t be recommended as none of its encryption techniques has ever been verified since the creators are anonymous. Lately they have been deleting posts criticizing any faults in the program, which is disturbing.
As a small point, you still have to remember a Last Pass master password. So one is not completely without remembering something.
Absolutely. But by having only one thing to remember you can elect to make it strong and lengthy, and let Lastpass worry about remembering everything else (which can be long and strong and completely UNmemorable),
This is a valuable post, Leo. Thank you. I’ve been using RoboForm for the past few years to accomplish the same objective as LastPass.
Is there a material difference between the two programs that would make me want to consider switching to LastPass?
Not really – Roboform is also good. I switched to Lastpass because Roboform has more of a “lock in” mentality (it’s VERY difficult to export your information to a different tool), and Lastpass was examined in detail by Steve Gibson of grc.com and does their encryption in a way that I really, REALLY appreciate. (Always local – never on the Lastpass servers.)
And even if all things were equal, the PC version is free. It costs $36 a year to for the phone app which is well worth it.
Now I admit I didn’t thoroughly read each post but I did do a search in my browser on this page. That browser is Chrome. Currently Chrome asks for your Windows login password, which providing that’s strong is a pretty neat way of securing access to stored passwords. Like you, Leo, I am a fan of Gmail but it doesn’t stop there, I think most of what they have is pretty good in the application space. It also works for me across a number of different devices, one of them an Android mobile where the security is changed depending on when & where I am.
Hi Leo
Could you comment on Cyber Firefox using the RC4 algorithm to encrypt the password file.
Wikipedia states; “While remarkable for its simplicity and speed in software, RC4 has weaknesses that argue against its use in new systems. It is especially vulnerable when the beginning of the output keystream is not discarded, or when nonrandom or related keys are used; some ways of using RC4 can lead to very insecure cryptosystems such as WEP.
As of 2013, there is speculation that some state cryptologic agencies may possess the capability to break RC4 even when used in the TLS protocol. Microsoft recommends disabling RC4 where possible.”
While I’m not familiar with those specifics, it does sound like it bolsters my argument not to let browsers remember passwords.
I would never save passwords for banks, credit cards, other “high security” stuff like that on browser, but enter them every time (often along with other security measures specific to the particular institution). Also important to change them a lot. For things like local clubs, stores etc where to spend money (but not when they have retrievable credit card details), various other “trivial” websites I am happy to use browser facilities.
“important to change them a lot” —>>> Why? I’m still looking for a coherent reason as to why changing passwords periodically adds any value. Here’s my take on it: Is a periodic password change a good thing?
My bank uses 6 digit password. I’m not worried though. Anyone who knew my password would have to have their app installed on a phone with my phone number which is registered with the bank, and ever with that, they’d need my fingerprint to unlock the app, so I trust my password manager with it.
I do use a password manager (RoboForm) to help me generate secure/unique passwords for my various accounts but feel much safer knowing that the encryption key is known only to me, (even if that means not being able to recover it if I forget it). The other thing that is more convenient with a third part password manager than one built into my browser is that RoboForm is available in ALL of my various browser as well as on ALL of my various computers/devices
I just physically write my passwords into a note book, especially any pw’s related to banking. Would this be the most secure method of storing passwords? (lock the book in a safe for maximum security if concerned about it). Or am I being naive?
That depends on the physical security of the notebook. For example, if it’s not in a safe place, and your house is broken into, the thief would get your passwords
I know a lot of people who do this sort of thing. I see them have a hard time finding their passwords over the years in all the pages of the notebook. Sometimes they’ll update and write it in a new place and get all mixed up. But the biggest problem I see is that they don’t use very secure passwords. They use ones that are very easy to type, write and remember. The best solution I’ve found is Leo’s recommendation of LastPass.
The most secure? Don’t know. I don’t think I’d consider it so. It remains vulnerable to physical theft when it’s out of the safe, you have to remember to put it in the safe every time, and when out it’s vulnerable to loss by fire or similar catastrophe.
Leo, I took your advice years ago about making passwords different and *long* (most more than 15 characters, if permitted). Fortunately, many websites now allow more characters to be used…something worth checking if you hit their limit when you set up the account or tried to strengthen your password. And as a password manager I use Norton Internet Security’s built-in “Identity Safe” feature. I have no idea if its encryption is local, or on their servers. Do you have any opinion or comments about it?
BTW, rather than “renew” NIS each year I’ve found it much cheaper to buy a new “download” copy (digital key only) at discount from a reputable software retailer and just apply the new product key. Norton actually has an “I have a product key” button that appears when you click on Renew. (Wait until just before your current copy expires b/c unused days do not roll over.)
Related to not remembering logins on a website. I was using a library computer to check my email. Before I finished, my time ran out. I asked the attendant if that would have logged me out. He said no. I asked him to reconnect me to the Internet so I could log off. Anyone who used the computer after me could have accessed my email and even changed the recovery information to steal the account, although a security-conscious website would ask for a password before allowing changing passwords or recovery information.
Always be sure to log out of your accounts, email, Facebook, etc. on a public computer.
Leo and crew,
Having read several of Leo’s articles on the subject, I’m more than interested in upgrading password security on my devices. I’ve been on the internet since the way back and have a couple of books filled with user names and passwords for all the sites I use, have used, and may sometime want to use again.
Question: If one wants to convert to using LastPass or some such manager, will said programs somehow convert all those hundreds of existing log in settings saved in my browser (FF) or not, OR will one have to access each individual website and initiate a password change?
In theory, either of two things will work: LastPass will let you import directly from FireFox, OR you can export from FireFox and then import into LastPass. I’ve never done either. My preference has always been to BACK UP whatever my old mechanism was (presumably an export from FireFox would do the trick), and then let LastPass build it’s database normally (by logging in manually and letting LastPass save as you go). This means that LastPass will only contain the sites that I actually use.
I will say that the migration process tends to be fragile, in most password managers. Rebuilding from scratch seems to be the most reliable.
Using Google Chrome and Avast to collect and store passwords I find that it works well.
I also have a ‘cleaning’ system when shutting down the internet. When logged off from Gmail, I use the ‘hamburger’ to open and display history. Closing the Gmail tab, I select the first item in history and press Ctrl + A so that all are selected and then delete/remove them. Closing the browser, I open Ccleaner and have all spurious stuff removed (be sure to set up exactly what you want Ccleaner to delete).
I know have a lap-top with an empty cache and rubbish bin. I will run SUPERantispyware about once a week and Malwarebytes monthly.
My father loves his little password notebook, but when he needs to look in there, he never seems to know which password belongs to which site. Also if he’s forced to change passwords, he looks in the book and doesn’t remember which is the old or the new.
He also allows his browsers to remember some of the passwords, but the computer got reset and didn’t recognize his profile, so suddenly he was on a new installation with no history and an empty password vault. I tell him I use LastPass, but just don’t have the energy to teach him one more new thing at his age.
This is advice I would only give to an adamant notebook user. The only thing I would recommend is a password vault program. Buy him a notebook with alphabetic tabs and copy all the login information, alphabetized by website name. Have him cross out older passwords as new ones are used.
Yes, old age sucks. But unfortunately this anecdote demonstrates that if a person doesn’t understand what he/she is doing or doesn’t have basic organizational skills, a magic tool such as LastPass won’t help either. A suggestion for a person in your situation is to simplify password management for your father: except for financial site passwords, create no more than 3 passwords, composed of common phrases, and print them in big bold font along with the associated sites. In your father’s case, concerns about “security” are secondary for the type of typical social sites your father is likely to visit (because you may have other things to worry about).
Thanks aa1234aa,
I’m sure he would love to have a simple password for all sites, but some sites force him to change for various reasons.
When a site forces me to change, LastPass immediately offers to remember the new password. When he has to change, it’s pen and paper time again.
And now Last Pass has decided to make a change so that anyone with a free account can only use Last Pass on one type of device. So if my laptop keeps Last Pass, my tablet won’t be able to use Last Pass, so I’m not sure what I’m going to do besides saving password in the browser.
Bit Warden looks promising as a free solution, or consider 2 LastPass free accounts, one for your PCs and another for your phones and tablets. My solution was to shell out the $30 for a year. The convenience is worth it to me and LastPass deserves tom earn money for their work.
I’ve got an article coming up this week on the topic.
I had a feeling you were going to have an article when I read the news.
FYI, while the Brave browser (based on Chrome) saves passwords, it will not show the passwords until you enter your computer password.