Sandboxes and virtual machines are two different technologies that share enough characteristics to make them easily confused.
One could confuse matters further by referring to a virtual machine as the ultimate sandbox. That would be an accurate statement, but it really only stirs up the mud in what is already muddy water.
Let’s look at the three scenarios: the default case without either, a sandbox, and a virtual machine.
Become a Patron of Ask Leo! and go ad-free!
First, a caveat for the knowledgeable: this is, of necessity, an over-simplification. I’m not trying to define exactly how these technologies work at a bits-and-bytes level. This is a high-level overview meant to convey the concepts for a basic understanding, nothing more.1
Windows on its own
Let’s start with a conceptual view on how Windows and Windows applications operate (at a very high level).
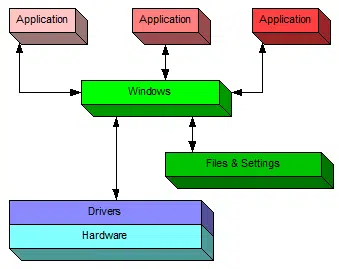
Applications running in Windows interact with the machine (and with you) through Windows.
Windows manages access to the files and on-disk resources; it also manages access to the hardware through the device drivers that are installed for your machine’s specific hardware configuration.
A sandbox under Windows
In a sense, a sandbox is a container placed around an application running within Windows.
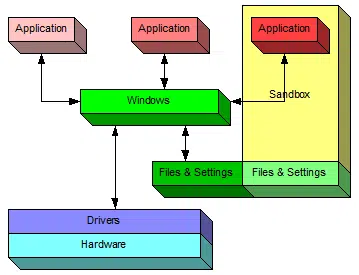
One of the three applications in this example is drawn as being within a sandbox, including a portion of the “Files & Settings” used by that application.
Therein lies the magic.
When you run an application inside a sandbox, it continues to have access to everything that it would were it not sandboxed. The primary difference is that anything created or changed by the sandboxed application is:
- Not visible outside of the sandbox; other Windows applications don’t see it.
- Not saved when the sandboxed application exits.2
The best example is simply that any malware that might have been downloaded and “installed” by the sandboxed application is discarded when the application exits.
A virtual machine under Windows
A virtual machine, or VM, is an application running under Windows that creates an environment simulating a completely separate computer.
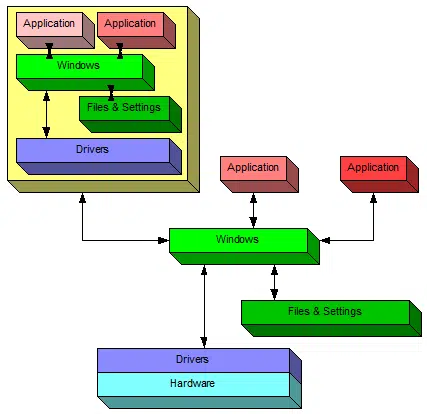
In this diagram, the application on the left is a VM running a completely separate copy of Windows. In a sense, it’s a “machine within a machine.” Windows running on the actual PC is often referred to as the “host” operating system, while any VMs running on it are referred to as “guest” operating systems.
Within a VM, applications continue to access the world around them through that VM’s copy of Windows. That “world” includes that VM’s own virtual hard disk, on which files and settings are stored.
The VM also includes its own set of virtual device drivers that behave as if they’re interfacing to actual hardware. In reality, they’re mimicking the presence of actual hardware and talking to the host copy of Windows to gain access to the real hardware.
Everything that happens in the VM stays within the VM. It behaves exactly as if it were a completely separate physical machine.
That implies that any downloads, changes, updates, installations created or saved within the virtual machine is only accessible from within the VM in some way.
And if you delete the VM, it’s like getting rid of a PC. Everything on the virtual hard disk is erased.
Multiple virtual machines
One of the best ways to demonstrate virtual machine technology is a scenario such as this one.
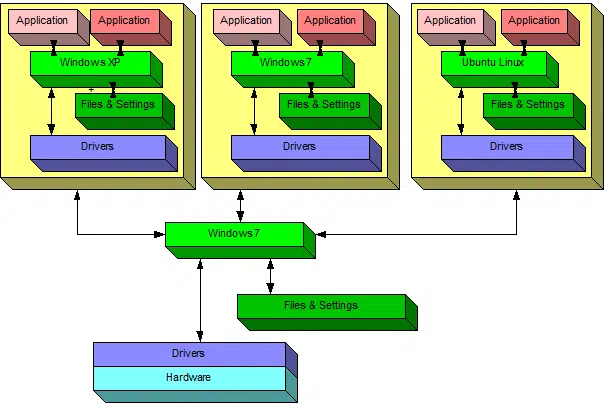
This illustrates a single PC running three virtual machines.
- The PC itself is running Windows 7
- One VM is running Windows XP, and would appear as a window within the host Windows 7 machine.
- One VM is running another copy of Windows 7, and would appear as a window within the host Windows 7 machine.
- One VM is running Ubuntu Linux, and would appear as a window within the host Windows 7 machine.
One physical machine runs three different virtual machines simultaneously.
Each virtual machine is completely separate — as if it was on completely separate hardware — except that it’s not.
This is actually more common than you might imagine. For example, so-called “cloud servers” are nothing more than virtual machines. As I write this, the Ask Leo! website is hosted on a modest virtual machine on a virtual hosting provider. I have no idea what the underlying hardware actually is; the virtual machine can’t look “out” to its host. My assumption is that it’s a fairly beefy piece of hardware on which several virtual machines are hosted.
Pros and Cons
Sandbox
Sandboxing doesn’t require much in the way of additional RAM or disk space, and is fairly easy to set up and use. I say “fairly” because there are complexities, most notably about how to preserve desired changes outside of the sandbox.
For example, if your browser is sandboxed (the most common scenario), getting a downloaded file that you want to use outside the sandbox may take a few extra steps. Other changes you might want to preserve while you’re in the sandbox can also be slightly complicated to retain.
Virtual Machine
Virtual machines can be resource hungry. Among other things, you’ll need to allocate disk space to the virtual hard drive and choose how much of your computer’s RAM to dedicate to the VM while it’s running.
When discussing the characteristics of a virtual machine, the phrase that keeps coming up is “just as if it were a separate physical machine”. And when looking at what a VM can and cannot do, and what it takes to set one up, that’s the best rule of thumb to remember.
Setting up a VM typically involves installing an OS from scratch. In the multiple-VM example above, each virtual machine would need to be set up — just as if they were separate physical machines.
A virtual machine and its host are effectively isolated from each other. A common way to copy files to and from the virtual machine is to set up network access on that machine — just as if it was separate physical machine.
As you can see, a VM is perfect if you want a completely isolated “virtual” second (or third, or fourth) machine. It’s also perfect if you want that machine to run a different operating system than its host. For example, I no longer have a physical machine that has Windows XP installed on it, but I have a virtual machine I can fire up at will on my primary desktop (currently running Windows 10) that provides me a copy of Windows XP to work with.
Specific Tools
One of the most popular sandboxing tools is called “Sandboxie“. Originally developed as a Sandbox for IE (hence the name), it’s grown into a powerful and flexible general purpose sandboxing solution. Unfortunately, it’s not free.
These days I use VirtualBox, a free and open-source VM solution for both Windows and Mac. I have clean installs of Windows 10 Home, Pro, Windows 7, and as mentioned above, Windows XP, that I can run as needed on my primary machine (which itself runs Windows 10 pro).
For many years, I used Parallels Desktop to run many of those same incarnations of Windows on my Mac Pro.
Finally, VMWare is another popular VM provider. There are many pre-configured VMWare “appliances” you can download and run. For example, you can download a ready-to-run VMWare appliance that is Ubuntu Linux without having to go through the steps of setting up the operating system.
Microsoft confuses terminology — again
Some editions of Windows 10 now include a feature called a “sandbox”. Naturally, it’s not a sandbox as I’ve described above. While not a full-fledged virtual machine, it’s close. When you run the Windows 10 sandbox, you’re running a lightweight but separate instance of Windows itself.
It’s convenient, since other than enabling the feature in Windows and running the tool, there’s little to set up.3 It can be a quick way to set up a safe environment to test items in isolation from your primary operating system.
Next steps
Full-blown virtual machines such as VirtualBox aren’t for everyone. However, if you know it’s what you need and you have the hardware to support it, it’s incredibly cool technology. I use it almost every day.
Sandboxing tools are easier to use, and many people swear by them. Particularly if your Windows 10 edition supports it and your computer meets the hardware requirements, the Windows 10 sandbox might be worth investigating as an additional tool in your security toolbox.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: In other words, no nit-picking, please.
2: Specific sandbox implementations may provide mechanisms to transfer or save data out of the sandbox, but the important concept here is that, unless such steps are taken, any changes made by the sandboxed application are lost.
3: Unfortunately, it does seem to conflict with VirtualBox.


Can the VM be made to simulate hardware as well? I am a gamer and would love to simulate older pc’s with 3dfx cards.
18-Jan-2012
glide works sometimes for that purpose.
google it if you feel opening that pandora box.
I use VMware player and have the Windows 8 previewer running in it, as well as three different Linux distros. One reason to run a virtual machine might be to do online banking in a safe environment. Another is to experiment with different OS’s without tying up a computer. This allows you to start from scratch again easily if you mess something up.
I was also going to say that about games not installing with VM as well. I run W7 Ultimate (64 bit) and first got into Virtual Machine when I couldn’t get Status Monitor software to work with my Epson printer under W7. The printer works fine, there’s just no way to check ink levels or run maintenance with Epson’s Status Monitor under W7. Running out of ink mid-task is not the best way to find I need it and ink is too expensive to guess when it’s time to replace the cartridges. I tried a couple programs that are supposed to work like Status Monitor but they had problems like changing the order of the colors so I didn’t know which was accurate- color name or cartridge location. None of them worked right with some things hanging up endlessly -not locked up or frozen, just appearing to be doing something while nothing was actually happening. So, I tried the Windows XP Virtual Machine set-up Microsoft offers. It allowed me to install the printer and Status Monitor although it only works less than half the time although the printer works fine. I did try to install some older games and while they appeared to install, none would work. The biggest problem was I was unable to get any gaming hardware to work. I tried several joysticks including an ancient Logitech Wingman Force and an older Logitech steering wheel. I could almost hear it laughing with newer hardware like my G27 wheel and Saitek joy stick. Although VM appeared that it was allow installation nothing ever installed. I’m still hoping someday to find a VM program a bit more functional. Until then I am hanging onto my faithful old XP based machine as well for older games. W7 compatibility mode is not as good as you’d expect.
An aside is the term ‘Sandbox’ also applies in gaming and means a game where you don’t have to follow the script constantly and can freely roam about doing (almost) whatever you want. What immediately comes to mind are the Grand Theft Auto games. To a lesser degree are Fallout 3 and Fallout New Vegas.
Isn’t Chrome already using sandbox technology for general browsing? I think I read recently that in Chrome each tab is its own sandbox. Do I have that right? I use SR Ware Iron, which uses Chrome as its core, without all the Google privacy concerns. I have used it for a few years, and I love it. Updates to Chrome are automatically applied to Iron as well.
18-Jan-2012
Dell has had the Secure Firefox for well over a year now. This provides safe surfing with a built-in sandbox. No configuring is needed.
It is called KACE secure browser and it is free to anyone. Many of my customer’s now use it.
Packrat1947
OK, I understand more than I did before about the differences, but does this include the JVM, or Java Virtual Machine?
21-Jan-2012
For over a decade, Sandboxie has been my #1 tool in my security arsenal. And it’s been effective keeping bloat out of my OS because I contain numerous programs in their own, individual sandboxes.
Sadly, Ronen Tzur, the creator and developer of Sandboxie sold this gem to Invincea a few years ago. And more recently, Invincea was purchased by Sophos. Since the Sophos acquisition, there have been disturbing signs that bring into question just how committed they are to supporting Sandboxie. The regular Sandboxie forum has been shutdown and attempts to access it are rerouted to a “temporary” forum at Sophos. A visit to that forum will reveal numerous inquiries by users to get clear answers regarding Sophos’ intentions, but answers are few and very evasive. Lastly, updates to the program have been few and far between.
I believe many users of Sandboxie feel as though they are in a state of limbo regarding how the future will unfold for this once (and still?) highly, highly regarded program. And Sophos has done a very poor job responding to requests for clarification. It’s truly been a very disappointing situation for a software program that deserves much better than what Sophos is providing.
the first image is broken 🙁
Windows Sandbox: A Conceptual Diagram
Windows sandbox: a conceptual diagram.
I have no trouble seeing it. It might be a problem with your browser’s cache. My first step would be to clear the cache. In the Related Posts section, you’ll find instructions for four major browsers. Here’s the link for Firefox. How Do I Clear the Browser Cache in Mozilla Firefox?
This worked for me.
Hyper V in Windows 10 / Server 2016 /19 is actually pretty good, has improved out of sight since 2008R2 , i prefer it now to VMWare which always seems to minor issues. I have 16 Virtual Servers over 4 Physical boxes two boxes are Hyper V 2019 and two boxes are VMWare 6.
You can still have issues running some old games on Virtual machines due to Video requirements not able to be replicated , i have had major problems trying to run D2 on a Virtual machine.
Are you able to run D2 at all? I know I had trouble getting it to work on a Win10 laptop but after jumping through a few hoops (I forget the details) it’s now running perfectly fine. It’s a laptop with a “dedicated” graphics card (I’ve always heard that dedicated laptop cards aren’t actually dedicated) so not sure if that gives you any hope?
Leo (or anyone), do you know of a sandbox app for Linux (Mint/Ubuntu/Debian)? I used Sandboxie in Win7 but alas it does not come in a Linux flavor. I know, a lot of propellerheads say they’re not needed, but cross-platform & even Linux-specific malware *does* exist & it worries me.
I’m not aware of a sandbox app for Linux, but it could exist. Of course VirtualBox exists for Linux, so you could set up a complete virtual machine if you like.
Almost 2 years late, but “Firejail” is what you are (or were) looking for.
Hi Mark,
I’m using Firefox on Windows 7. I cleared the browser’s cache and still can’t see the diagram for the sandbox. All of the other diagrams are fine. It’s just the sandbox diagram that I can’t see. Any other suggestions? Thanks for your continued help Mark!
Mike W.
Which browser are you using? Have you tried a different browser?
Hi Mark,
My primary browser is Firefox, which I did delete the cache and history, then closed the browser and clicked on the article in Leo’s email which reopened the article and still no joy. Yes, I did try the Chrome browser with the same result – no joy for seeing the sandbox diagram. Any additional suggestions?
Thanks for all your help!!!
Mike W.
It could be a hiccup in the content delivery network I use, I suppose. That should clear up in 24-48 hours. The URL for that image is https://askleo.askleomedia.com/wp-content/uploads/2012/01/windows_sandbox.png — you might see if that works on its own.
I wonder, a sandbox still seems accessible. Since hackers know that Win10 has a sandbox, are they going to find ways to slip out of the sandbox environment? Just seems too close to the OS to be safe.
With malware just about everything is possible. However, I find it unlikely that a hacker would go to the trouble since sandboxes are not that commonly used. Additionally, the hacker would have to find a vulnerability in that specific sandbox to exploit.
This may sound like a stupid question but do you need to purchase a separate Windows license for a VM running a version of Windows or does the host license cover that?
Windows Sandbox is included, and thus free.
If you run Windows in a full virtual machine, then technically yes, you do need another license. “It’s just like running on a separate physical machine” applies to this as well.
I use VirtualBox. When I create a new virtual machine, it asks me what specs I want for the computer (e.g. how much RAM should it use, how big of a hard drive, etc.). When I then run that virtual machine, it behaves exactly like a physical computer with a blank hard drive. All you see is a black screen telling you that no bootable media was found. I have to actually put in my Windows install disk (or a bootable USB) to actually get it to do something. If using the Windows install disk when starting up the virtual machine, it goes and installs Windows and will ask for your license key and go through the appropriate activation process, just as if you installed Windows on a physical computer. Once installed, subsequent starts behave just like turning on a physical computer. It boots into Windows and you get to work.
So yeah, you need a separate license because it is a separate computer. They both just happen to share the same hardware.
You can specify an ISO file instead of a physical DVD, for example, to boot from for that initial setup step. That’s what I do.
I bought a new Windows 10 (home) laptop to replace my aging Windows 7 laptop. The Win 7 laptop came with MS Office Starter edition built in (yes, I need MS Office because LibreOffice seems to break formulae when switching been MS Office and LibreOffice and I have a need to use the MS Office formats). I’m thinking that if I created a VM (I use VirtualBox), I could just install Win 7 in the VM so I could continue to use MS Office The problem is that the Recovery Disks that Win 7 had me make when I first booted up the Win 7 laptop don’t work when installing in the VM. It doesn’t think that disk 2 is disk 2. When I check the disk outside of the recovery install process, the disk is readable and is labeled the same as the other disks and indicates disk 2.
What I would like to know is can I take my Windows 7 backup file and boot up the VM and recover the backup as if I was doing a recovery to “bare metal” (as Leo calls it), if I configure the VM to have nearly identical specs to my Win 7 laptop? Or am I going to run into issues with the hardware being too dissimilar?
Interestingly, I was able to copy over the Windows XP VM from the Win 7 laptop to the Win 10 laptop, and with a few tweaks to the configuration am able to run XP on my Win 10 laptop without having to go through the whole Windows install. So I’m thinking recovering a backup might work.
(Currently I’m using Office through OneDrive on the Win 10 laptop, but that’s not as nice as actually having it installed. There’s a little bit of a lag between my typing and what shows up on the computer).
Which version of Office are you using? I deregistered office on my older machine and installed Office on my new machine with the original installation files and license,
It’s Office 2010 Starter. It was only ever distributed to hardware vendors to bundle with their new builds. So there is no installation files that I can use on my Windows 10 laptop. Otherwise, what you say would be the easiest to do.
I think MS’s idea was to tempt you with Office and that would make you want to buy the whole thing. But there is nothing in Starter Word that I’m missing out on and the only thing that I miss in Excel Starter is Freeze Panes (I think once I wanted to do a Pivot Table). I’ve never been tempted to buy Office when I’ve already got almost exactly what I need.
Libre Office does pivot tables and freeze frames and it’s absolutely free. It’s not as pretty as MS Office, but it does everything the vast majority of Office users need.
Hey everyone, go get WaveBox and try and figure it out. It’s got a little bit of each and I’m indecisive about which one it technically is. It’s almost just a self-installed mini-OS within a VM with built-in sandboxing! Also it’s awesome and removes your need for browsers almost entirely. YaWelks
So I have to ask, what is the difference between Containerization (docker concept) and Sandboxing?
I’ve used both vmware and VirtualBox. I prefer VirtualBox because of it’s open ‘source’ness. I run VirtualBox on a Windows 7 machine and since I have some old software with WindowsXP I use it for a virtual XP machine on my Windows7. I have no issues with what I use it for, and I’ve transferred files from the virtual box to win7. I have heard the virtual machines provide an extra level of internet protection but I have not yet done that. I recently purchased a new laptop Windows10 and the plan is to run the WinXP virtual machine there as well. I may even spark up a win7 virtual machine although I don’t as of yet have the need for it but I do like to dabble with linux once in a while so I might actually make a virtual PC with LInux, not sure yet, lots of potential.
The main reason for me using VirtualBox is running older software.