This is a sad case of some very amazing technology getting smeared with a bad reputation because of how some people choose to use it.
Absolutely: there are many legitimate uses for peer-to-peer file sharing (P2P) programs like BitTorrent.
In fact, I wish it were used more.
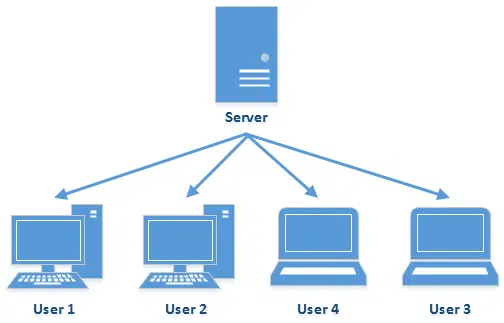
In order to understand why peer-to-peer file sharing is interesting, we first need to understand just a little about how traditional file sharing and downloads work.
Traditional file sharing and downloads
In a traditional download, there is one “master” server on which a file is placed. Each user wanting that file downloads it from that server.
|
|
Now, as you might expect, if a lot of people want that file, the server can quickly become overloaded.
Alternative #1: Get a bigger server
One solution is to place the download file on a server with much higher capacity. So, for example, a website might be hosted on one domain, such as askleo.com, but a download link from that site might reference a file elsewhere.
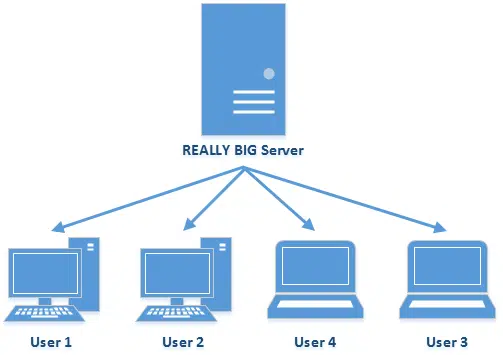
Amazon’s web service, S3 (which has massive capacity), is one common alternative. The image above, for example, can also be found at:
https://s3-us-west-2.amazonaws.com/askleo/images/bigserver1.png
There are techniques that can be used to obfuscate or hide the fact that the file is coming from a third-party file-hosting service, but the concept remains the same: rather than taxing my server with the download, the work is pushed off to a more powerful server with a faster internet connection.
But the bottom line is, you are still downloading from a single copy, and from a single server.
Alternative #2: Get more servers
Another solution is to “mirror” the file on several servers, and distribute the download requests across those servers.
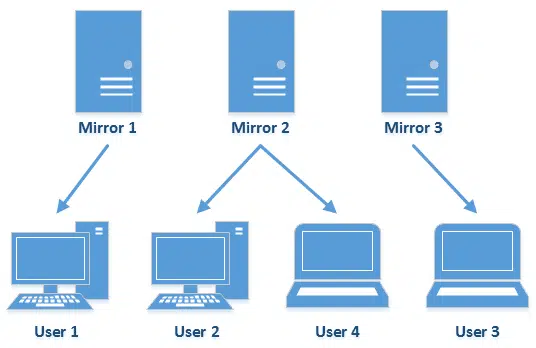
This is still a “master copy” model: only a handful of servers hold the master copy of a file, and you must go to one of those servers to get it.
There are two approaches here as well: explicit and hidden.
Explicit mirroring, as its name implies, presents you with a choice of potential download locations – perhaps listing which might be closer to you – and lets you select which server to use.
Hidden mirroring is more complex, but more powerful. The image above is referenced from this URL:
https://alssl.askleomedia.com/wp-content/uploads/2015/10/mirrored.png
That domain, “alssl.askleomedia.com”, actually points to a Content Distribution Network (CDN) that distributes the file across multiple servers world-wide. When you click on that link, you’ll get the file from the server closest to you, not only shortening the distance the file has to travel to get to you, but also transparently spreading the load across multiple servers.
After the server selection has been (transparently) made, though, you are still downloading from a single copy, and from a single server.
Alternative #3: Spread the load with peer-to-peer
Peer-to-peer file sharing does away with the concept of a “master” copy.
The fundamental concept is, instead: given that many machines eventually download the exact same file, they each then make the file available to others directly from their machine. There is no “master” distinction; all the computers are equal “peers”, and any that have a copy of the file can offer that file to any other computer looking for it.
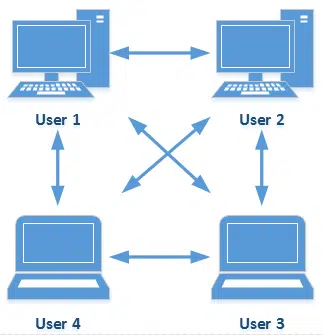
The advantages of peer-to-peer over normal file downloads are many.
If a traditional master file server goes down, you can’t get the file. If one of the peers in a peer-to-peer network drops off, you continue to download the file from another peer. The bandwidth usage, rather than being focused on a single master server, is distributed across all peers, often resulting in much faster downloads.
In addition, peer-to-peer protocols add some additional optimizations.
The biggest is that rather than downloading the file from start to finish on one connection, as you would in a traditional server-based download, a peer may open connections to several other peers, each downloading separate parts of the file all at once. This typically makes much better use of bandwidth than a single straight download. The moment any part of the file has been downloaded, that part can be immediately shared with other peers who don’t have it yet.
Yep, this means that a machine could be sharing and uploading parts of a file that it hasn’t even completed downloading yet.
Hopefully, by now you can see that peer-to-peer file sharing is just a technology designed to optimize how bits (files) get distributed on the internet. Nothing more, nothing less.
Help keep it going by becoming a Patron.
Peer-to-peer’s bad rap
The reason that peer-to-peer file sharing has a bad reputation is not because of the technology, but rather because of what is being shared: illegal copies of software, movies, music, and images. Many of the illegal file-sharing networks happen to use peer-to-peer technology.1
But that doesn’t alter the fact that the technology being used is valid and valuable for legal and legitimate uses as well.
For example, that same peer-to-peer software is often used to fetch the latest copies of many open source projects, such as Linux or OpenOffice. Since peer-to-peer works well for truly large downloads, like entire CD or DVD images, you’ll often find it as an option for these types of files.
It’s believed that peer-to-peer technology is also used in scenarios such as updates to large games installed on your PC, such as World of Warcraft, and even operating system updates, possibly including Windows itself.
Legitimate issues with peer-to-peer
Peer-to-peer is designed to maximize file transfer speed. It does this by maximizing its use of your internet connection.
If you’re trying to do something else on the internet at the same time, that could be a problem.
Thus, my expectation is that the program slowed down your internet connection, rather than your entire computer.
The good news is that almost all peer-to-peer file sharing programs have “bandwidth throttles” built in: you can instruct them to limit their upload and/or download speeds to something less than your full connection speed, leaving bandwidth for anything else you might like to do while files are being transferred.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!


Hi Leo — What security risks do P2P downloads have? How do you know that one of the peers has not corrupted the file?
19-Jan-2009
Every file has a hash. If the file doesn’t match that of the original file everyone else is sharing (which is the same copy as the first, original upload), it will not be shared. In fact, the torrent will warn you that a file does not match and wont share it to other peers.
As far as corruption while downloading.. It wont happen. The Transport Layer of the TCP/IP model insures that. If a packet is received corrupted, it will simply request the packet again and wait for it. TCP/IP insures that:
* data arrives in-order
* data has minimal error (i.e. correctness)
* duplicate data is discarded
* lost/discarded packets are resent
All of that still doesn’t mean that you can’t download a dangerous file. Many times a file is labeled with the name of a desired file only to contain a Trojan or worse.
After downloading your file AND BEFORE OPENING IT, let your antivirus program take a look at it. This one extra step has saved my own @ss many times.
Interesting quick tip with bittorrent that I noticed that other day:
If you are trying to download a torrent, and it suddenly becomes unavailable (and the download process turns “red” on the screen) then you can “repair your Internet” connection.
To do this you right-click the Internet connection icon on the bottom right of your screen, in the “system-tray” (with XP).
You then select the option “Repair Connection”.
By repairing the connection it seems to force your computer to find new peers, and some of those new peers may then hold the parts of the file that you need.
This technique works quite well for me.
Also… whenever I use bittorrent, I find that my Internet slows to a snail pace.
This is probably because my computer is using the limited band width of my Internet connection to send out parts of multiple files, and make connections with many other bittorrent users (peers).
If you want to see just how many peers you are connected to, you can use a couple of easy commands.
When you reboot your computer, press Windows-R key to bring up the run prompt. Type “cmd”.
Once you are in the command line, type:
netstat -b
That will show you all the connections you have to the “outside world”.
Next, run your bittorrent program, and wait a few minutes. Then type that command again:
netstat -b
You will see yourself suddenly connected to people all around the planet — sometimes hundreds of them. The list can grow to be really long.
If you want to disconnect all those people to speed up your internet again, once you are finished with Bittorrent, you can type these 2 commands:
ipconfig /release
ipconfig /renew
Wait a few seconds before typing the second command.
Also, sometimes after using bittorrent my internet connection seems glitchy for some reason. In those cases I “repair the connection” by right clicking the icon for the internet connection at the bottom right of the screen and selecting “repair connection”.
That usually does the trick, and re-stabilizes my Internet connection and makes it quick again.
Connecting to multiple computers is exactly how bittorrent and peer-to-peer file sharing is supposed to work.
If bittorrent is slowing your machine down, then as I said in the article, look for a setting to cap the bandwidth you’ll use.
And if you’re done downloading your file, then exit bittorrent completely. That’ll solve it too.
But there’s no need at all to go mucking about with your network connection.
20-Jan-2009
A couple of comments – firstly, one of the reasons that many people get download speeds that are less than advertised by their ISP is because of contention with other users ‘hogging’ bandwidth by file-sharing. A typical home broadband connection will have a contention ratio of 50:1, so you are already sharing your connection with up to 49 other people; it only takes a few of these to use Bit Torrent, Limewire, Azureus etc excessively and down goes your speed. Many ISPs are wise to this now, and will throttle your connection if you use P2P filesharing and may even impose penalties (including disconnection) if the abuse is too great. For this reason, it’s best to limit any P2P transfers to the hours between midnight and 6am.
Secondly, most P2P software lets you limit the number of shared connections – best not to leave this as unlimited! 10 download, 5 upload is reasonable.
Hi Leo, thanks for your reply, and that interesting metaphor about me hammering my network connection with a sledge hammer! I like that visualization!
Well, the reason I have been “hammering” my network connection in such an extreme way is because it remains slow even after I close my bit-torrent client (U-Torrent). I always make sure that I select “exit completely”.
And yet, even though U-Torrent supposedly closes completely, the internet speed remains noticeably slower, and more sluggish.
Interestingly, after I close the bittorrent client, and type “netstat -b” in the command line, I still see lots of open TCP connections to my computer.
So far the only thing I know that fixes the issue, is to take the drastic step and “hammer” my internet connection with the trusty sledge-hammer of “repairing Internet connection”!
Maybe my situation is unique and there’s something glitchy with the way my bittorrent client is operating, or the way I set up my network? (Admittedly I’m a complete amateur at home-networking, and I only just now bought some books on networking which I started reading.)
Anyways… not sure if anyone else is experiencing this type of problem after they have opened and then closed their bittorrent client?
21-Jan-2009
I’ve stopped using BitTorrent for the reason that it slows my computer considerably when I do. It was so bad as to make a decent, tough a little old, computer pretty much unusable. I’ve not stopped using P2P though. I simply switched to UTorrent.
I haven’t noticed nearly the problems with slowing the computer or my internet connection that I had with BitTorrent.
AG
I find that BitTorrent and Utorrent suck. Vuze is far superior in speed and you can search inside of the program from several different bittorrent sites.
Except Vuze is written in Java.
Actually, there are 2 ways that your internet may slow to a snails pace when using bittorrent..
1. You are maxing out your upload speed. (easily fixed by capping your upload in your bittorrent client).
2. You are surpassing window’s maximum allowed # of connections controlled by the tcpip.sys in your system32/drivers folder. (this is a precaution implemented by Microsoft to pretend the spreading worms from machine to machine post sp2)
If indeed your upload isnt being maxed out, you might want to think of getting a cracked tcpip.sys file if you’re thinking about continuing with bittorrent. You will know if you are surpassing the max number of connections if you see Event ID 4226 in your Event Viewer.
One has to be careful when using bittorrents. Every search includes infected files, usually with different names, but similar sizes. After some experience a careful user can tell which ones are suspicious. My antivirus and firewall software have very good P2P shields and so far haven’t let one infected file pass through.
P2P programs have to be configured to access only a dedicated folder otherwise private information can also be accessed by others. Copyrighted contents should also be avoided to be included. Legal action has been taken in some P2P sharing instances. Bandwidth U/D load limits, number of simultaneous uploaders permitted, chat options, search permits for other sharers should all be configured. Some of the P2P software programs can be still active even after exiting. Ctrl+Alt+Del window will usually indicate such a process in the process window, if not, in the network window. I have tried almost all of the bittorrent software and observed malicious behavior in one or two. If a user selects a good P2P software and configures it wisely, with P2P shields included, P2P file sharing is safe and sometimes invaluable.
you can also limit your torrent uploading and downloading to avoid slower internet connection.
I am an avid torrent user. One of the best things I did to speed up, or I should say, to manage, my bandwidth and stop the torrent client slowing down everything else was to install a program called CfosSpeed. this program gives you prioritising control over any Internet using software. You can allow certain protocols to have a higher priority on your bandwidth than others. for example, torrent programs are put on the lowest priority. this does not slow them down, it just means that, if another program like a web browser suddenly needs to use the bandwidth, then, as web browsers are set to the highest priority then the browser will always be able to just cut in and display pages as fast as it ever could, instead of what can happen if you have torrents going: The page cannot be displayed.
You can set up the priorities yourself and so have complete control over what protocols and or programs have the most or least bandwidth.
I don’t want to sound like I am trying to sell the program so let me just say there are now loads of similar programs out there and, I am sure I read there are also freeware ones too. I use CfosSpeed as it was one of the first of its kind and I have just stuck with it.
If you googled for speed up torrents or packet control you may well find something else like it. Download.com or a big site like that is bound to have a freeware option.
Still a bit confused. So where do these downloaded, available files sit on your computer that all the others have access to. In a separate folder?
And does that mean all the others in this network have access to your computer? Doesn’t sound very safe to me.
These files reside in whichever folder the peer to peer program places them. You can usually find out where, by going into the file sharing program’s settings or options or some similarly named menu option. The sharing program only allows access to those shared files. I suppose that if there is a bug in the peer-to-peer program, it might be an opening for hackers.
They’re in a separate folder set up by the file sharing program. NO, others do NOT have access to your computer.
In Peer to Peer “download” or sharing of files, is there a danger that someone knowingly or unknowingly may infect you? Can a virus from one computer get downloaded to another in the process? Can a person purposely infect you in the name of “sharing” data?
If the file you are downloading is infected, it can definitely infect your computer. This is very common with illegal program downloads. Posting torrents to infected files is very common. I’d guess that the majority of those are infected.