I’ll start out by saying that options to protect yourself from supercookies and evercookies are relatively limited, if effective at all.
Supercookies and evercookies are the result of a website owner’s desire (or more often, the desire of the advertising networks used by websites) to accumulate data about computer users and the sites they visit — even those users who disable or clear cookies in their browser regularly.
Bottom line: clearing cookies isn’t enough — not nearly enough.
And there may be nothing that is.
Cookies 101
Cookies are part of the http (and https) protocol your browser uses to request webpages and web servers use to deliver them.
When you visit a site — say https://askleo.com — the web server may deliver, along with the webpage you see, a small text file containing some data you don’t see. In a sense, your browser says, “Please give me https://askleo.com“, and the server replies, “Here’s the page you requested, and here’s some other data I’d like you to hold on to for me.”
The data is called a “cookie”. It can be anything — what a cookie looks like is not defined in any way. It’s just data provided by the website that your browser stores on your computer.
The next time your browser requests a page from that same site, it automatically sends that saved data along with the request. To continue the analogy above, your browser might say, “I’d like to see https://askleo.com, and here’s that data you asked me to keep last time.”
That’s all a cookie is.
As I said, a cookie can be anything. The most obvious example might be a unique number. The web server might make up a completely new, unique number the first time it sends a cookie back to your computer. When your computer sends that number back on subsequent requests, the server knows the new request is coming from the same machine.
Cookies are most commonly used to remember you’re logged into a site as you move from page to page. They’re also used, as they are here on Ask Leo!, to remember you’ve been shown things like newsletter subscription offers, so you don’t see them again and again1.
Cookies also allow ad services to see what pages that machine has been visiting.
 Supercookies
Supercookies
It’s somewhat ironic, but what are called “supercookies” aren’t really cookies in the traditional sense, because they don’t work in that browser-supported, behind-the-scenes way.
A supercookie is just any other way of storing something unique from a website on your computer so it can be given back to or somehow detected by the website the next time you visit.
The problem is, a supercookie is often difficult or impossible to clear.
Let’s say the goal is, as in the example above, to assign your computer a unique number that can be “read” during subsequent website visits to track that it’s the same machine visiting each time.
There are perhaps a dozen or more different ways to do this that don’t involve traditional cookies at all.
Here are just two examples:
- Plugin cookies: Even though Adobe Flash is falling into dis-use, it’s an example of plugin-provided cookies. “Flash cookies” are managed by the Flash player in a way very similar to regular cookies. Unfortunately, your web browser has no way to clear Flash cookies, though some tools, like CCleaner, can. Other plugins have the capability to maintain their own cookies or cookie-like data.
- Image hack: I call this a hack because it uses techniques never intended to achieve this goal. There are many possible variations, but as one example, let’s say the webpage you’re visiting includes a small image hidden behind something. The colors values assigned to some pixels in the image, when combined, serve as the unique ID the web server uses. A small amount of Javascript or HTML5 coding elsewhere on the page reads the pixel “colors” and reports the number found back to the server. On subsequent pages, the image — containing your unique number — comes from your browser’s cache, rather than being downloaded anew.
These are just two examples. One is an intentional feature and the other is an unintentional side effect of some clever programming. There are other approaches, and probably more that haven’t yet been discovered or devised.
Evercookies
Let’s assume a website uses all three of the techniques I’ve discussed so far: http cookies, Flash cookies, and the image hack.
It only takes one of them to work for your computer to be uniquely identified.
In fact, if any one of them works, the website can immediately re-create the other two.
That’s the concept behind what some have termed the “evercookie” — a technique that uses more like ten different approaches to identify your computer. If any one of those techniques work, the other nine can be reset, no matter how aggressively you clear them.
Clear your browser’s http cookies? Evercookie techniques cause it to be immediately reset on your next visit, because perhaps a Flash cookie wasn’t cleared. Cleared the Flash cookie? The cookie can be immediately reset on your next visit, because the image cache wasn’t cleared. And so on for any number of techniques that could be used.
Evercookies turn all this into a game of whack-a-mole to uniquely identify your computer, despite any attempts at the contrary.
No cookies at all
Visit the site amiunique.org (Am I Unique?), and click “View my browser fingerprint“. You may find that you are, indeed, unique, and thus trackable.
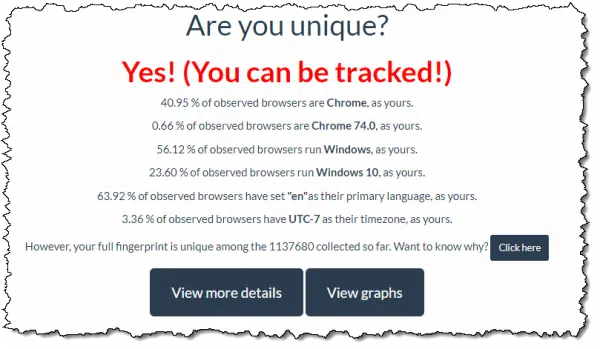
Whenever you visit a website, your browser provides that site a variety of information, including the version of the browser, your screen resolution, your operating system, and so on. Other information — like the plugins you have installed, whether there’s an adblocker present, or if Flash player is available — can also be determined by script included on any webpage you view. All of this information is made available so websites can use it in various ways to provide you features and functionality — in other words, for “good”.
But the combination of all these bits of information (amiunique.org examines 17 different items) can indeed be completely unique to you. As improbable as it might seem, yours might be the only computer connected to the internet with that specific combination of characteristics. That means when websites see that specific combination of characteristics, they know it’s your machine.2
What I do
What do I do about all this?
Absolutely nothing.
I just don’t believe that browser-based tracking represents as huge of a threat as some seem to feel. Even supercookies, evercookies, and browser fingerprints don’t really worry me that much.
Most tracking isn’t done at the individual level. No one cares that Leo Notenboom visited this site, and then that site, and then that site, or bought this or that. What they do care about is that 1,000 people did, and that those 1,000 people should now see ads related to that site. Anyone that bought X might be interested in Y, so we’ll show ads for that.
As I said, I don’t care. At worst, it’s an annoyance when I see the same ad everywhere I go on the internet.
If you want to do something…
Help keep it going by becoming a Patron.
I’ll admit, though, as unlikely as I think it is, the technology certainly could be used to track me as an individual.
Some people simply don’t appreciate their movements being tracked, even in a relatively benign, anonymous, aggregate way. And some are legitimate targets for some form of state-sponsored tracking at the individual level.
So how can you avoid it?
It’s not easy. In fact, it’s darned near impossible, if the websites you visit are determined to track you.
The only way is to be certain that nothing has been saved from a prior visit, and thus, nothing trackable is sent on subsequent visits.
The only guaranteed way to do that is to start with a completely fresh computer each time you browse.
Harsh, I know.
The problem with the various techniques that create supercookies and evercookies is that we have no real confidence that we can clear them all. Yes, browser extensions will come along and clear more of them, but as the evercookie example illustrates, a determined site need only have one technique that slips through to continue to track.
As I said, it’s whack-a-mole, and the moles are winning.
There are two approaches to making the “start with a clean machine every time” approach slightly more palatable:
- Do your browsing within a virtual machine you reset each time.
- Use a Live CD (or DVD or USB), containing a completely stand-alone operating system, including a web browser, that saves nothing to your disk when it exits.
“Private” or “incognito” browsing does not cover all possible tracking techniques; you need to take much more aggressive steps.
The future
Even if so-called supercookies were completely outlawed, that law would only be valid in those countries that passed it, and even there, those that choose to flout the law would carry on. Legislation won’t make the technology go away. If supercookies are outlawed, only outlaws will have supercookies.
I expect that the arms race will continue: browser features and add-ons will be developed to increase your privacy, and new tracking techniques will be developed to bypass them.
The good news is, I do believe various privacy watchdog groups monitor most major sites and advertising networks — and perhaps law enforcement too, should legislation become a reality — and as a result, blatant violations will be taken to task.
I hope.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: Or at least for “a while”. The newsletter offer popup on Ask Leo! should appear only every month or six. Unless, of course, you clear cookies.
2: Even when it’s not truly unique, but say, limited to “only a few” that share the characteristics, that level of tracking can still be valuable.


You should have mentioned that the vast majority of cookies are benign and actually add to the browsing experience. For example on my website, there’s an introduction video on the splash page. And I drop a cookie that simply tracks that this browser has been here before. The next time they visit my site, they won’t have to watch the intro video again – they go straight to the home page.
Even your site has a benign “Remember me” cookie.
Cookie paranoia has really been blown way out of proportion.
Hi Leo, there is a ‘good’?? Wall Street Journal article at
http://online.wsj.com/article/SB10001424052748703940904575395073512989404.html
titled “The Web’s New Gold Mine: Your Secrets”
I long for the day when Adobe Flash player will become obsolete. I believe Adobe engineered their flash player to install ‘super cookies’ (LSOs: Local Shared Objects) so as to make their software popular to on-line companies. Software should not have to write to my hard drive to play a flash video. But Adobe Flash Player DOES. That is one reason why we have to update the flash player every few weeks to patch the holes hackers find in A.F.P.
I use Firefox browser with the ‘Better Privacy’ add-on installed. Since May of this year Better Privacy has removed 1613 flash cookies. However, one feature Firefox either lacks ( or at least I haven’t found it) is that of automatically emptying the browser cache and automatically deleting cookies upon Exit.
Leo, you were spot-on when you wrote, “browser features and add-ons will be developed that increase your privacy, and new tracking techniques will be developed that bypass them.”
Yet another trick web sites can use to track you goes beyond any sort of cookie or pixel hack. The Electronic Frontier Foundation’s Panopticlick project asks, “Is your browser configuration rare or unique? If so, web sites may be able to track you, even if you limit or disable cookies. Panopticlick tests your browser to see how unique it is based on the information it will share with sites it visits. Click below and you will be given a uniqueness score, letting you see how easily identifiable you might be as you surf the web.”
Just your combination of browser, fonts, plug-ins, time zone, etc. probably makes you unique.
http://panopticlick.eff.org/
The Air Force has created a publicly available product called LPS (Lightweight Protable Security) which is basically a Windows like GUI running on a verison of Linux that you burn to a bootable CD or DVD. So basically, every time you boot it up, you are on a new clean computer. You can get more info at http://www.spi.dod.mil/lipose.htm
I use Ubuntu Linux on my laptop and use the “Guest Session” when I need to browse privately. Actually, I also use this method to let my kids or any 3rd person access Internet on this machine, without compromising the safety or privacy of data in my user account.
Note for uninitiated people:
A guest session on Ubuntu Linux creates a temporary (sandbox type) user account that is wiped clean when you logout from that session.
The escalation of the ‘cookie’ war sounds a lot like the escalation of the ‘injunction’ war.
At this rate, we’ll all end up using hardware-OS web-books to do our surfing, because any other method is just too ‘dangerous’.
As Rod pointed out, if you use Firefox there is the Better Privacy add-on. Moreover Firefox has long had an option, under Privacy, to keep cookies only until “I close Firefox”.
And it’s not difficult to clear the cache (Clear recent history, under the Tools menu).
And if your worried about what can be done with Javascript, get the add-on NoScript, though I have to admit it can be a confounded nuisance.
Then there’s “Tell web sites I do not want to be tracked”, “Always use private browsing mode”, and “Clear history when Firefox closes”.
This might not be enough for some, but it’s more than enough for me. (I’m happy with Opera)
06-Oct-2011
What is the function of the files “iesnare.exe”, “mpsnare.exe”, “NMindexstoresvr.exe and 44334 Adminand 44334 Admin? Some or all of these files are required for applications like Norton AV, SuperAntiSpyware, and others to run.
In fact, these applications will not update themselves without the presence of the files, which suggests they are used as an anti-piracy measure– a means to identify the computer used to run the applications.
1. While anti-piracy efforts are understandable, most users not only expect, but have a right to control what is placed on their computers, especially since they must live with the result of software and hardware malfunctions.
2. More than half of households (individuals and families) own multiple computers. If a computer owner decides to uninstall an application on one computer and install it on another machine, that usually is his right (OEM-installed operating systems aside).
Which means authorizing individual computers via a “clandestine cluster” (of files) poses a potential roadblock to user REinstallations on different or slightly different hardware. A REinstallation is not necessarily or even usually a case of piracy, but normal user behavior and entirely benign.
For example, a routine upgrade of hardware (a new computer) means the licensed user may be prevented from normal use of the REinstalled application when the application does not get permission from “home” to update itself and perform other functions on different (or even slightly different) hardware.
@Bob
Unfortunately many programs are licensed to be run on only one computer. A couple of notable examples are MS Office which sometimes come with 3 licenses and some antivirus software. It might not seem fair to limit program buyers to installing a program on only one computer, but fairness and legality are two different issues.
And I should also have mentioned that, if you really want to be anonymous, you can always try Tor (https://www.torproject.org/). Though I have to confess I haven’t bothered to myself.
06-Oct-2011
@MarkJ
You will recall I stated, “If a computer owner decides to uninstall an application on one computer and install it on another machine, that usually is his right (OEM-installed operating systems aside).”
Now, if MS DRM means something else is afoot– a “clandestine cluster” approach by which MS has more control over how you use your license than a simple “one machine installation– like a book”– that is exactly my point.
@Bob A computer owner is just that – the owner of the computer, not the software that runs on it. Twenty years ago, it was common to include clauses that allowed software to be transferred to another computer if the software was completely removed from the original computer. But the software manufacturer owns the software and the user’s right to install software only extends as far as the license agreement (EULA or similar) specifies – “if you do not agree to the terms of this agreement, do not open the package and return the software to the place it was purchased.” Unfortunately, and increasingly, many software license agreements contain tighter limits on where and how the software can be installed.
Fast-forward to now (admittedly a few years since you posted), and the only thing I can say is, if the expectation is that we should approve which files should be written to our computers, someone forgot to tell Microsoft, Adobe, Google, and a whole bunch of other companies. Windows 10 updates automatically, Adobe is very aggressive with their updates (although they insistently require you to agree to their terms each time), and Google … let’s just say it’s virtually impossible to get online without Google putting something on your computer. And DRM and music/video/content licensing and its related issues is just a whole ‘nother can of worms that’s even murkier than software licensing.
That being said, we do have a right to control what goes on our computers. However, exercising that right in a strict sense usually means we have vastly fewer options regarding the software we can use on them – for better or for worse. If enough people did that, I’ll bet conditions would change fast. But I wouldn’t count on that happening.
I don”t care if someone wants to track me. They can track me all day long. They’ll be bored to tears. What really steams me is that they are storing stuff on MY computer and using up MY valuable space, they are defragmenting MY hard drive, and they’re shortening the life of MY computer. I try to run a lean machine and they have so much crap stored on MY computer, I can’t store anything on it myself. The expiration dates on some of their crap means it will live longer than I do. I think it takes a lot of arrogance for anyone to think I won’t mind if they store their crap on MY computer without even asking me.
@Carol
Cookies take up an insignificant amount of space on your computer.
I wish you had provided more info about removing super cookies. And btw even if a cookie is only one bit it still takes a minimum amount of space that depends on the hard drive format whether it be fat16, fat32, NTFS, or some other type. A single bit file will take 4K+ space on a hard drive with NTFS. It adds up. Check your java directory. When you install a new version all of the older versions are left on your system. It adds up to a lot of lost capacity. Is it any wonder computers come with TB drives now while my first computer include an absolutely huge 540 MB HDD.
13-Oct-2011
There are some programmes that remove cookies. I have used Maxa Cookie Manager for some time and it removes all the usual cookies and flash, silverlight, IE UserData DOM and FirefoxDOM cookies. It also marks all persistent cookies so you can remove them.
13-Oct-2011
Re: Stephen at October 4, 2011 9:34 AM
“You should have mentioned that the vast majority of cookies are benign and actually add to the browsing experience. “
I agree completely with the comments made by Carol Putman at October 11, 2011 12:45 PM-
“I don’t care if someone wants to track me… …What really steams me is that they are storing stuff on MY computer…”
But I would like to add my own comments. If these cookies are so benign, why then are online companies and websites finding frankly devious ways to do the same thing with pseudo-cookies (LSO’s); why are they so determined to track us, supposedly anonymously?
Why don’t more websites give us the choice of enabling or disabling cookies? Surely if it is for our convenience as opposed to theirs, cookies should be disabled by default with an option to enable them?
As for the ‘anonymity’ of cookies-
https://secure.wikimedia.org/wikipedia/en/wiki/Data_mining
“Data mining requires data preparation which can uncover information or patterns which may compromise confidentiality and privacy obligations. A common way for this to occur is through data aggregation. Data aggregation is when the data are accrued, possibly from various sources, and put together so that they can be analyzed. This is not data mining per se, but a result of the preparation of data before and for the purposes of the analysis. The threat to an individual’s privacy comes into play when the data, once compiled, cause the data miner, or anyone who has access to the newly compiled data set, to be able to identify specific individuals, especially when originally the data were anonymous.”
“One may additionally modify the data so that they are anonymous, so that individuals may not be readily identified. However, even de-identified data sets can contain enough information to identify individuals, as occurred when journalists were able to find several individuals based on a set of search histories that were inadvertently released by AOL.”
So much for anonymity; though I suspect the response will be ‘they just aren’t that interested in you’…. for now; call it paranoia, but being paranoid doesn’t mean they aren’t after you!
Will these “Super Cookies” be able to collect signing in passwords to the likes of eBay or PayPal? And more important can they retrieve your credit card details, and anyone doing online banking “which I never do” how safe are their details?
03-Nov-2011
“They simply allow advertising networks to track what sites you.” And the websites can only retrieve the cookies, they themselves place. What many don’t understand is how a cookie they got from one website gets them a related ad on another one. That’s because if a website uses an ad server, you are also accessing that ad server’s website so they can place cookies and retrieve them when you visit any websites that use their services. That’s how ads follow you using classic .html cookies.
As a computer geeky person I have found a malware program which protects against not only the ‘normal’ intrusions, but allows you to double protect your computer against the major of all ;cookies’ A combination of Firefiox and Panda Security limit or eliminate most unwanted intrusions.. once you have set permissions for allowing cookies, there two programs work quite seamlessly in tandem .. this DOES include a good portion of javascript and flash cookies.. it allows you to determine which cookies you want and which ones you DON’T. ANYTHING with analytics, ad… track… etal.. will follow every move on the internet you make..
One way to protect yourself is to be aware of what cookies are being stored on your computer!!
1. Skip fancy programs like windows, etc, etc …
2. Have a fresh copy of your OS w/ browser program.
3. Go online, surf, message, troll, email or whatever else you do.
4. Get offline, format drives and reinstall #2 clean from disk.
5. Wake up, have coffee, and begin at #1 again.
I know this article mentions that anonymous browsing might not work, but it can’t hurt either. One solution is use TOR (a.k.a. The Onion Router) to avoid your browsing habits being tracked. Head to your favorite search engine and search something like “TOR browser download.” Leo’s suggestion about using Ubuntu is also a good one, though less convenient.
My website for those interested: http://computerrepaircompanyinabox.com
what about the clutter? if cookies that can`t be removed keep being added a computer would slow to a crawl.
will a clean reinstall clear these cookies?
A clean install would get rid of cookies, but cookies are so small they don’t affect browsing speed. In fact, clearing cookies will slow your machine down a bit. For example, it forces you to log in again to every site and/or re-enter other information.
A clean install would get rid of a lot of things, but is completely unnecessary to remove cookies. Don’t go that far just because you want to clear a browser’s history!
In most browsers – and in all the major ones – there are built in mechanisms to clear things such as cookies. When properly configured, Microsoft’s Internet Explorer will delete even the Flash data. Just examine the Internet options > General tab > Delete… button. Click it and you can configure what IE deletes.
This does not mean you will be anonymous online, but it can go a long way to disrupt commercial entities building a profile on you.
Seriously consider installing a hosts file. You can get one from
http://winhelp2002.mvps.org/hosts.htm
It will prevent many of the tracker companies from tracking you. You can also manually add Google’s analytics to that hosts file.
The problem with online hosts files, such as the one you reference, is that many are overly aggressive. That one, for example, will block you from clicking links in The Ask Leo! Newsletter. Yes, of course, you could modify the file, assuming you know what modifications are needed, but that’s actual beyond the scope of many average users.
I don’t know how well this works, but there’s a freebie called Flash Cookie Cleaner 2.0. Details and download here:
http://www.majorgeeks.com/files/details/flash_cookie_cleaner.html
I’m no PC expert, just an average user since WIN 98 and I have adapted to each WIN version and its security vulnerabilities accordingly. That said, currently I use Pale Moon browser with “do not track” selected, run MSE and AVG anti-virus, Ad-block Plus and Priv-Dog, on my Vista, XP and WIN 7 PC’s and route them thru COMODO’s free public access servers. I clean up with Crap Cleaner and eyeball and verify all the separate entries it finds to avoid problems before deleting them.
What can you folks tell me about my precautions? I hope I’m doing OK!
As satisfying as it might be to deny aggressive vendors access to tracking data outright, it might be even more fun if someone came up with a program to leave the data in place, but randomly ‘pervert’ it.
For any current readers, this tactic of intentionally corrupting typically-reliable non-consensually-collected data now has a widely-accepted term – “Data Poisoning”, though it is typically used in reference to AI (read: LLM) models.
The tactic may also be called “Disinformation” (not to be confused with “Misinformation”, which can be benignly incorrect rather than always maliciously incorrect). “Disinformation” is often used in political discussions, where one group of people/interests is corrupting another group’s social media (trusted news outlets) with believable lies rather than deletion or blatantly false lies.
Visual Graphics artists occasionally call this tactic “Nightshade”.
I have two computers.: One is a business computer. This I use strictly to do my direct business – no surfing. To all intents and purposes, no profile can be built on me beyond what my business interests already know from my use of this computer
I keep beside it another computer I surf with. A hosts file is installed, of course, which blocks many or most of the tracker sites. I clear the cookies, browser history cache, and flash cache regularly. Silverlight is disabled, so nothing goes into the Silverlight cache. It means I log in a fair bit, but the commercial profiles built on me would be truncated.
I suppose much of this is about what one wants to do verses how comfortable one is knowing that there are all manner of tracking mechanisms out there.
I use ‘FlashCookieView’ & ‘Cookienator’.
Deletes them…….I think !!
I’m curious if you’ve looked at Chrome’s “Incognito Mode”. That appears to block the normal cookie, image cookie and flash cookie you mention in your article.
Certainly. The point of the article, though, is that there are MANY techniques that persist – even in incognito mode.
A great topic for the times. Many readers want to be not tracked but are unwilling to do what it takes to really be ‘not tracked’ on the Internet. I’m on Bob’s side here, it’s not worth it to do everything you need to do to avoid tracking:
Among those things is change your IP address – TOR by itself is not good enough, you need also to use a VPN. Of course don’t accept any cookies, either first or third party which will break many sites. (Just blocking third party cookies is not enough, HTTP redirection can make 3rd party cookies look like 1st party cookies.) Block flash, browser tracking add-ons, e.g. “Maps Galaxy” and the like. It’s good to change computers as any single computer can be fingerprinted, see EFF’s Panopticlick for your computer’s fingerprint. Certainly never login to any site or give any site your email address, use an independent DNS server, DNS-sec if you can, and use incognito mode to limit what’s stored on your computer, or wipe & reload (maybe a static VM) with every browsing session. An ad-blocker may help, but even simply using a ad-blocker will help a site to track you – “Here’s that guy from IP xxx.xxx.xxx.xxx that is using Opera with uBlock Origin, Privacy Badger and Ad-Block plus” – is all a site needs to identify you.
The web will be much less friendly if you do these things, many sites will not work, and of course you would not be able to do any e-commerce. You must assume that anything that can be done is being done to track you. There is a huge tracking industry, lots of money is involved, and huge incentives to do so. Smart people want to track you; *anything* you can think of they have already done so and implemented. “They” in most cases are commercial interests, if “they” are governmental interests the problem just gets harder.
So just like trying to think of a rememberable password, trying to avoid tracking on the Internet is now is effectively a lost cause. It is not worth the effort and disadvantages to do block everything. I block 3rd party cookies and use an ad-blocker, (but not on Askleo.com :-)) any more than that is not cost effective.
An easy solution is to install uBlock and master how it works. Definitely out of reach for the average user, but power users and geeks will love it. I’ve been using it for a couple years now and it is awesome. It basically looks at any external requests from the website you are visting and then blocks the common ad ones (like doubleclick). You can also manually select/deselect any requests. It saves your preferences for that site so the next time you visit you don’t have to worry about tweaking it.
Again, not easy to use for the average user, but super powerful.
https://www.ublock.org/
It’s also great for just seeing what a site is loading. For example, I can see that the only tracking that AskLeo implements is Google (Analytics) which is very common and shouldn’t cause anyone concern.
It also connects to Facebook, which enables those like/share buttons at the top of the articles. Aweber, which is an email list/mailing company, is also requested (for email signups). Other than a benign request to a CDN (to speed up file delivery), there is nothing else loaded from AskLeo.
Install ublock and try a site like Mashable. It’s insane how much tracking they use.
I’d be shocked if any blocker were 100% effective at all the different ways that these “evercookies” can be created.
Even if supercookies and evercookies can’t easily be blocked, would it be possible to identify sites that have set them on my computer? If so, I might choose not to revisit a site I deem too intrusive.
Your only real choices are listed under the heading “If you want to do something…” in this article. But I agree with Leo that this isn’t really something to be worried about – unless you are doing something that you are afraid of being tracked. Then I would choose the full nuke option of starting with a fresh computer each time.
Not with 100% accuracy, since we don’t know all the different techniques they might use. Using a blocker that shows you the attempts of normal tracking techniques is a start, I suppose, but like I said – there’s no way to be 100% certain.
If someone is feeling paranoid use sandboxie for web browsing, after browsing delete the sandbox. Everything will be gone which was stored during the internet session. It’s only surefire and less painful way of preventing such cookies.
Control panel>flash player>Local storage settings by site then delete them OR user>app data>Roaming>macromedia>flash player>Roaming>shared objects, then DELETE
That’ll get some, but not all.
Not something most people are going to do on a regular basis. And something that CCleaner can handle for you.
And only ONE of the dozens of ways that tracking can happen, and can quickly be reestablished. If you read the article you’ll note that doing this is pretty pointless.
The nice thing about seeing the same ad on so many pages is that you easily know whom not to patronize.
One side will always have a temporary win until the other side works out a counter measure.
A boot disc or possibly a sandbox will will save you from ads …but is it worth the effort?
Without ads, much free content disappears.
Additionally, even if we could permanently block tracking cookies of all stripes, we’d still get just as many ads, only less relevant to us. Not that all targeted ads are relevant. Targeting is simply the process of increasing the probability of relevance via cookies and other devices.
I’ve read your article but i wonder if my supercookies could be seen by my freinds or family or is it just the website i visit that has this information? Most important question is if it can be seen by someone you know?
Super cookies which are on your computer can only be seen by the websites which placed them. With the right tools and knowing where to look, I suppose someone who has physical access to your computer might be able get them, but that’s highly unlikely.
Thank you for your reply.
Websites you visit and their advertising partners. Depending on the techniques used they could leave data on the PC that could be discoverable, but there’s no way to know for sure in general.
I use Blur – Do Not Track which is a free extension that I use on my Chrome browser (see abine.com). It seems to do what is says, and shows how many cookies are blocked each time you visit a website.
Please read the article – it very likely cannot block all the different types of cookies that are out there.
Thanks for the article. It provides some helpful information but the general theme of “give up on trying to do anything about either super- or ever-cookies” negates the value of writing any such article (although this isn’t as bad as one of the comments here suggesting that the bad press about cookies is over-inflated).
It doesn’t matter that most sites and most cookies are not only not harmful but even helpful, and we might choose to have them anyway. I have a right to that choice. The focus here and in most articles about cookies is on those sites and cookies that ARE invasive, and do send home information that I may not wish the site to have. The issue is therefore one of my right to privacy–a right that the supercookie and evercookie clearly wish to deprive me of.
And suggesting that we simply sigh and resign ourselves to this degree of subterfuge and assault on personal privacy is…well, I won’t go there. Yes, it may be a difficult task but that doesn’t mean that we should give up.
I’d love to hear concrete suggestions on what you propose we do.
Qubes OS + WireGuard.
With an Apple Computer and MacOS there is a guest account, and everything can be deleted from the guest account. Would that be like starting with a new computer each time? Windows had a guest account also, but it can’t be used very easily anymore.
What do you mean by Windows guest account can’t be used very easily anymore? I have one on my computer which I let other people use when they want to use my computer. It’s as simple as clicking on an picture to use.
It is my understanding that Microsoft did not do away with the guest account, but made it harder to use. In the most recent versions at least. I was able to get the guest account working again, but it could not be called the guest account. It had to be called something different. I am not talking about just a standard account.
But I don’t really know very much about computers.
Best I can say is maybe? But I don’t trust that some of these techniques aren’t persistent even across guest account. Especially the whole browser fingerprinting approach.
Also, in Windows 10 Pro Version 1909, I think, it will be possible to have a virtual operating system. Could that achieve the same purpose?
Same answer — it’s better, but not perfect. But it is close to starting with a new computer each time.
I have a friend who is a privacy freak. He doesn’t even use a cell phone. He runs Linux and accesses the web via TOR. Does TOR protect against supercookie tracking?
I used the Tor Network twice-not for any evil purposes but just to have privacy on the internet.
I will never use Tor again. I don’t think it is as secure as people claim. If somebody was going to use it, it would probably be a good idea to install it on a USB drive using the Tails Linux and running it on a Linux computer with some other Linux operating system. I would rather use a VPN for privacy.
I don’t want to be attacked but I personally feel Linux is overrated. The Russians had malware running on Linux computers for a long time and nobody even knew. And look at Shell Shock and whatever the other one was called. I have a Chromebook and from personal experience I know the ChromeOs is not bulletproof, especially now that Android apps will run on Chromebooks. I got malware from the Play Store.
There are techniques I’m sure that can’t be detected or somehow avoided by even TOR. Remember, TOR isn’t about absolute privacy — they go through great lengths to point this out on the web site. Installing and running TOR is not enough — you need to do more and behave appropriately.
You have other things to worry about too when using Tor to protect your privacy. Things that only nations or very strong collective action groups can fix, not individual users.
For example, BGP Hijacking severity reduction by having ALL Internet Service Providers (ISPs) implement RPKI. To this day, most ISPs have not implemented it, and it seems like they won’t in the future. The sole fact that BGP Hijacking exists and is possible on a massive scale makes Tor unsafe to use if you desire full confidence in your privacy.
Video: https://www.youtube.com/watch?v=XDsLDhKG8Cs
Author: Sam Bent
Title: “For 9 Years Tor Ignored Princeton’s Proof: BGP Attacks Can Unmask Millions of Users”
————————————————————————————————————————–
Tor runs on the Firefox web browser, operated by Mozilla. The browser itself can have vulnerabilities too, fingerprinting capabilities never intended by the developers, such as a single Firefox browser process creating repeatable reliable orderings of elements inside an IndexedDB database (which is technically a cookie), necessitating a full shutdown and reboot of the entire browser after visiting a single site rather than simply closing a tab and opening a new tab.
Site title: “We found a stable Firefox identifier linking all your private Tor identities (fingerprint.com)”
Discussion Site URL: https://news.ycombinator.com/item?id=47866697
Original article (research authors): https://fingerprint.com/blog/firefox-tor-indexeddb-privacy-vulnerability/
I only used TOR a couple of times to try it out. I use a VPN, but rarely for privacy. I use it to watch content in other regions.
My “friend” who uses TOR and other tinfoil had apps is a full conspiracy nutcase. He refused the COVID vax and masks. I’d say that in western countries, it’s mainly (but not all) tinfoil hat conspiracy theories who use TOR.
Hi Leo, always current yaks…thanks. I use a VPN, and also use a portable browser that resides on a flash drive and I always run it sandboxed…so nothing really gets to the computer itself.
So my question: If i use a configuration like this, dont “cookies” get deleted with the sandbox after each session? thanks
Sure, but as outlined in the articles there are many, many, MANY more techniques at play here than just cookies.
Leo —
You went out of your way to say that cookie files can be “anything.”
So… does that mean that they can they be executable malware???
Are cookie files really that dangerous???
Interesting thought. I suppose a cookie could contain an executable, but there’d be no way to actually get the system to run it … unless of course you already had other malware on your machine, at which point all bets are off anyway.
So, no, cookies are not dangerous.
I visited a website using firefox and put some items in a cart just to get the total of how much they would cost if I bought them. I did not create or log in to an account on the website. I then cleared cookies, cache, and offline data. I went back on the website later on in the day to price things all over again and the items were still in the cart! I cleared cookies, etc. again on firefox and went back to the website and the items were still in the cart! I cleared cookies, etc. on firefox again and then went to Chrome. I never use Chrome and had never been on the website before in Chrome. Went straight to the cart and there was everything! Cleared everything in Chrome and went to Edge, which I also never use. Sure enough, everything was still in the cart when I went to the website’s cart using Edge. Again, I had not logged in to this website or in to an account on this website at all in any of these instances. I thought this was malware and used Malwarebytes, Bitdefender, CC Cleaner, and Hitman Pro to scan my computer. Absolutely nothing came up. I’ve messaged the webmaster of the problem website and also posted on the business’ facebook page, and of course I’m being ignored. I finally came across this article and I just want to confirm with you after reading this article: Is this an instance of this business using an evercookie, and is this something I really don’t have to worry about? I am eternally grateful to you regardless of your answer to my questions, as this article has informed me immensely, but you are really going to make my day if you tell me that there’s nothing I have to worry about. I’ve been so worried that I’ve been thinking about factory resetting my computer.
I don’t believe there’s anything to worry about. It’s just a shopping cart.