It’s a feature. Really.
One of the nice aspects of VeraCrypt volumes is that they are great ways to back up information — to the cloud or elsewhere — safely and securely. Create a volume with a strong passphrase, load up your secure data, dismount it, and that data is private.
Or… maybe not.
Depending on your backup technique, there’s a default setting in VeraCrypt that might be getting in your way. Fortunately, it’s an easy fix.

Ensuring VeraCrypt volumes back up
In VeraCrypt preferences, make sure that the “Preserve modification timestamp of file containers” option is turned off, and you can back up your VeraCrypt container files as you would any other.
Traditional backups use timestamps
One of the most common ways backup software determines whether a file needs to be backed up is by looking at its timestamp — more specifically, the “last modified” timestamp, which indicates when the file was last changed.
The program compares the file’s timestamp with its backed-up copy.
- If the timestamps are the same, then the file hasn’t changed and doesn’t need to be backed up.
- If the timestamps are different, then the file has changed and does need to be backed up.
It’s a quick way to decide if something should be backed up.
And it works well almost all the time.
Help keep it going by becoming a Patron.
VeraCrypt and timestamps
VeraCrypt volumes are containers that hold an encrypted form of all the files and folders you choose to place there.
For example, you create a VeraCrypt container named “mystuff.hc” with all the files you want to keep secure. When mounted (which requires you to enter the decryption passphrase), its contents appear as a separate drive — say drive “P:”. Within P:, you can access all the files as you normally would. When you dismount the container, “P:” disappears, and only the container file — mystuff.hc, in this example — remains visible. If anyone opens it, they can’t read the files; it all looks like random data because it’s encrypted.
Here’s the dilemma: what timestamp should the container file have?
You might think that the container should reflect the most recently modified timestamp of any file it contains. If the volume is mounted and you change a file within it — say you edit P:\passwords.txt — you might expect the container file — mystuff.hc — to have the same timestamp, since that’s the time at which it was last modified.
By default, a VeraCrypt container’s ‘last modified’ timestamp is not updated as files within it change.
Why VeraCrypt works this way
It’s not obvious why this is, at least not until you think about the problem VeraCrypt is trying to solve.
VeraCrypt is trying to keep your encrypted information private.
And information about when you modified your encrypted information is part of that encrypted information.
Exposing it by updating the externally visible timestamp of the container — something that can be seen without needing the passphrase — boils down to a form of information leakage. Depending on how you’re using VeraCrypt, it’s a potential security/privacy risk. It’s a tiny leak, but a leak nonetheless.
VeraCrypt’s default behavior breaks backup
So, you’re going along and using VeraCrypt to keep your sensitive data. Fantastic.
You update the sensitive files in your VeraCrypt container. Great!
You dismount the VeraCrypt volume and run your backup.
And the volume doesn’t get backed up, even though you’ve changed information within it.
The volume doesn’t get backed up because as we’ve now seen, VeraCrypt doesn’t update the container’s timestamp by default. The backup software thinks the container hasn’t changed and doesn’t need backing up.
Even though it does.
Changing VeraCrypt’s behavior
For most of us, exposing the date that the container contents have last been updated isn’t a big deal, doesn’t represent a real risk, and is something we’d rather have so our backups will work.
We can do that. Right-click on the VeraCrypt icon in the notification area of the taskbar and click on Preferences.
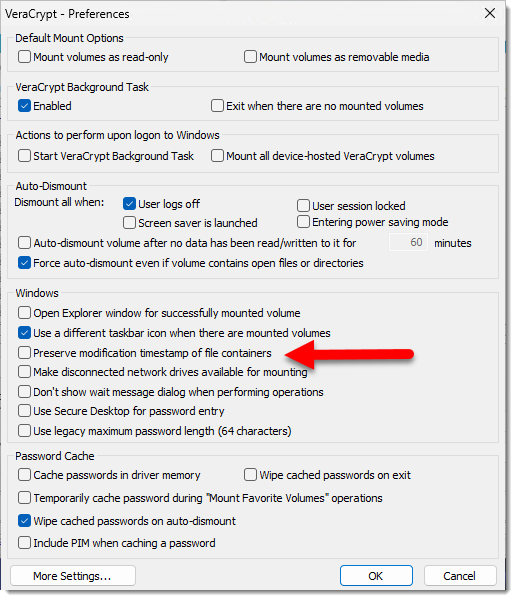
Make sure that “Preserve modification timestamp of file containers” is not checked, and click OK.
By unchecking this option, if something changes within the container, VeraCrypt sets the container’s timestamp to be the time at which it was dismounted.
Now, when your backup program runs, it’ll see that the timestamp has changed since the last backup, and the container will be backed up like any other file.
Note: your container may still need to be dismounted in order to be backed up. When the container is mounted, VeraCrypt locks it so that most other applications cannot access it. Dismounting resolves this issue.
Do this
I recommend you turn the “Preserve modification timestamp of file containers” option off. To me, backing up the container is significantly more important than the tiny bit of information leakage that an accurate timestamp represents.
I used to keep my VeraCrypt1 container in my Dropbox account. This meant that any time anything in the vault changed, the entire vault was uploaded when I dismounted. If your vault is large, that can make for a lot of unnecessary data transfer. Today, I use Cryptomator, which encrypts file-by-file specifically for these kinds of cloud-storage scenarios.
VeraCrypt and Cryptomator are both good solutions. VeraCrypt is generally a good choice if it’s commonly used for moving the entire vault around at once — say stored on a USB thumbdrive.
Another good choice? Subscribing to my weekly newsletter. Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: Well, actually, TrueCrypt, back in the day.




This article reminded me that I used TrueCrypt in the past. I have some archived TrueCrypt containers, and the install files for the last ‘full’ version if I need to move use on newer machines.
Is it safe to use TrueCrypt again? Supposedly its source code was audited by third parties with no issues found.
Is VersaCrypt safer?
TrueCrypt also seems to have a preserve timestamp setting.
I wouldn’t recommend using TrueCrypt over the long haul. It’s no longer supported and may have vulnerabilities. You can use TrueCrypt or older versions of VeraCrypt to open your TrueCrypt files and then re-encrypt them using VeraCrypt.
Well then, I don’t understand what was backed up every time I did a BU. I do daily BUs of my unmounted VeraCrypt volume to an USB drive & it takes several minutes to finish. I did not have the setting as you described – I do now by the way – yet I have several daily archived versions of the volume. Here are a couple of recent names of BU files: MyNewVolume 2023-12-13 07;52;50 (Full) & MyNewVolume 2023-12-12 09;48;03 (Full). If I understand your explanation that “the volume doesn’t get backed up, even though you’ve changed information within it” what was happening when I did a BU? I must be missing something.
Great article and thanks for writing it. This solved my problem with Onedrive and now it will backup my encrypted file correctly. I use AOMEI backupper to do a backup of my USB drive every time I insert it into my computer. The beautiful thing is my veracrypt encrypted file is kept on that usb drive and now it backs up automatically to onedrive thanks to this article. Once I unchecked the preference in veracrypt, everything worked flawlessly.
Thanks again!