It can be very, very frustrating.

This is a scenario I hear frequently.
- Someone travels overseas or to a neighboring country.
- They attempt to sign in to their Outlook.com account to check email.
- After specifying the correct username and password, they’re asked for additional information in the form of a code texted to their phone.
- They have no way to retrieve the message, as their phone is back home or doesn’t work where they’re traveling.
- They can’t sign in.
I’ll review why, what options you have, and perhaps most importantly: how to prepare so this is not an issue.
Become a Patron of Ask Leo! and go ad-free!

Additional verification triggered
Account theft is so rampant that service providers like Microsoft look for clues of suspicious activity. If such a clue is detected — such as a sign-in from an unusual location — additional steps might be required to authenticate and sign in. If you’re unable or unprepared to provide them, you might not be able to access your account.
Something unusual
This technique applies to services other than just Microsoft, but I’ll use them as my example since they seem to cause many inadvertent lockouts.
When Microsoft notices what they term “something unusual” upon signing in to any Microsoft account (not just your outlook.com account), they present a dialog asking you to “Help us protect your account.”
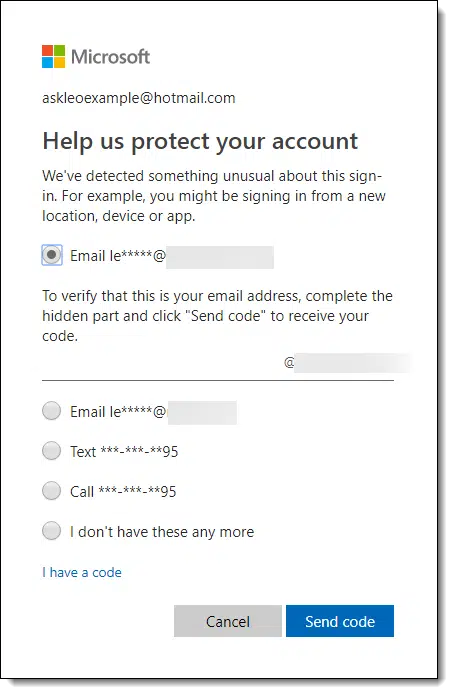
To generate this example dialog, I simulated traveling by turning on my VPN and having it route through The Netherlands (a country I’ve been known to actually travel to).
I proceeded to log in normally, entering my email address and password. Rather than taking me to my inbox, the dialog box above was displayed with several options to further confirm that I am the rightful account holder.
What is “something unusual”?
As listed in that dialog, there are several scenarios qualifying as “something unusual”:
- Signing in from a new location (as I made it appear).
- Signing in from a new device.
- Signing in from a new app on an existing device.
I’m pretty convinced other scenarios can trigger additional verification as well.
I’m also pretty convinced that #1 on the list is “signing in from a new location”.
Why? Because that’s where hackers usually are.
Why a new location matters
Microsoft is attempting to battle account hacks. Please believe me when I say that your account, my account — everyone’s account, regardless of provider — is under constant automated attack from hackers. Microsoft accounts, specifically, seem to be a popular target.
Unfortunately, hackers are both persistent and surprisingly often successful.
But one thing we know about most of these hacks is that they often originate “somewhere else”, in countries other than the one in which you reside (or even other areas within your country).
When Microsoft sees a new login from a new location, they err on the side of caution by asking for additional verification.
This is a good thing. This keeps the hackers attempting to break into your account from being successful even if they somehow know your password.
Unfortunately, if you’re traveling and haven’t prepared, it can also keep you from being successful.
Preparation means having options
In my example above, you’ll notice I have several options to prove that I’m the rightful account holder.
- An email message sent to an alternate email address.
- An email message sent to a different alternate email address.
- A text message sent to a phone number.
- A voice message delivered to a phone number.
I set up each of these three items (two email addresses and the phone number) in advance, as part of the recovery information associated with the account. Proving that I can access any of these — by providing the code delivered to the one I choose1 — proves that I’m the person who set up the account.
In other words, it proves that I am who I say I am, and I should be authorized to access the account.
You must set these up beforehand. As you can see, you can set up multiple methods of validation, but you need to have them in place before you need them.
And even then, there’s a catch.
The catch: traveling
Even if you’ve done due diligence in setting up these account validation and recovery options beforehand, there’s one catch that many people miss.
You need to be able to access them when you’re away from home.
That means:
- You need to be able to log in to one of your alternate email accounts to receive a code. If they’re all also protected by some kind of additional security that triggers when you travel, you may not be able to.
or
- You need to be able to receive a text message or phone call made to the phone number you have configured. If you don’t have access to this number while on the road, this approach may not work.
In other words, if you don’t have access to any of the alternatives listed, you may not be able to log in to your own account, at least not until you return home.
Additional preparation
In addition to setting up account recovery options (which you should do anyway) you now need to make sure that at least one, if not more, of the recovery items you’ve chosen will be accessible while you’re traveling.
If not, then you might want to:
- Set up an alternate email account with a provider that doesn’t perform this type of additional security check.2
- Add two-factor authentication using an authentication app such as the Google Authenticator or Authy. These apps do not require connectivity when used.
- Generate account recovery codes that act as one-time passwords or authorization codes that you then carry with you in some secure manner. (Not all services support this type of code.)
- Explore your service’s options for additional account validation options.
Arriving unprepared
If it’s too late — if you didn’t set any of this up beforehand and you’re now on the road and don’t have access to any of the alternate authorization items listed for your account . . .
You may be out of luck.
You may simply not be able to access your account until you return home. Though it’s small solace, take heart in knowing that hackers have also been prevented from breaking into your account.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: This is a subtle form of two-factor authentication. Something you know (your password) plus something you have: access to one of these second authorization mechanisms.
2: I do this using a domain I own, so that this email comes to me first in ways I can access from anywhere. You might choose your ISP’s email service, or a less popular email service. Unfortunately, I know of no way to test it beforehand, other than by using a VPN such as I used to create my example.




I had this same type of problem, but it was with gmail with 2 factor authentication. I changed my password as requested but then I got to thinking, how could this happen? Google told me when it happened and what kind of phone was used, which wasn’t mine. I never sign in anywhere but my desktop in my home. The only weak link I can come up with is the IP is an open WiFi connection provided to the whole complex by someone the landlord contracts with. Could be anybody on that open WiFi, or anyone able to monitor that WiFi.
I have 3 alternate emails for all of my accounts. This gives me alternate methods in case I lose access to one. My primary residence is in Germany and when I travel to the States, I still can receive text messages on my German phone and it’s even free. I believe that works because I use a GSM based SIM card. The CDMA system is used by most US wireless providers and those phones don’t work in most other countries. In the US, T-Mobile and AT&T use the GSM SIM card system and I’m wondering if anyone reading this has had any experience successfully receiving a text in any other country from a US phone. I might be able to experiment with that.
One of my recovery email accounts is with GMX.com. I’ve never been asked for a second factor when traveling.
For work I’m traveling on a weekly basis, so this actually is a really big problem as I’m unable to access my work email’s. First time it happened I had set up to text me, and for some reason it did not work. As I log in from the same device but from a different location, I just got a VPN (I use NordVPN because I often use public wifi so I have to encrypt my information and they are based in Panama) and when I’m travelling I set the location so it seems that I’m from the same place. Sometimes it asks for verification but not for my other emails.
I’m wondering if having a Google Voice phone number could help. I think that texts sent to that number can be forwarded to your choice of devices/accounts. Is there a way to use this when the worst happens and you can’t otherwise verify?
This article thinks Google Voice is great for travel: https://toomanyadapters.com/google-voice-travel/
Note, however, that some businesses will not send confirmation codes via text message to services such as Google Voice, which is VoIP and actually considered a land line. I can attest that Wells Fargo bank won’t, and have come across others. That said, when you set up 2FA for any site, add *both* your Google Voice number and your wireless carrier (cell phone) number and you should be covered.
You don’t need to be traveling for this to happen. I’ve had it happen periodically sitting in my own house. It’s happened with various financial institutions as well as other online accounts. I presume it has something to do with cookies being cleared. The message often says something to the effect of not recognizing the computer I’m using, even though the same computer worked last week. And once I re-authorize the computer, all is well for a few weeks. I’m not manually clearing the cookies, so it may be Windows Defender or some other software doing it.
Cookie clearing will absolutely cause this, though Windows Defender does not clear cookies. Using a different browser might cause it since each uses its own collection of cookies. And some cookies have expiration dates, which is perhaps the most common cause.
One question I’ve had for a while is, what purpose do expiring cookies serve. It seems as unnecessary as periodically changing your passwords when nothing has been compromised.
It’s a safety net. Login to a computer, walk away for days, weeks, months — you don’t want random person to walk up and be able to access your account. (It’s a site decision, FWIW — cookies can be told to expire in YEARS, allowing for effectively infinite expiration.)
I’m thinking more of the cookies that expire after a few days, week or months. It seems like cookies should either expire immediately on logoff to the website, for example, banks or any websites dealing with money. Facebook, on the other hand, keeps their cookies alive almost forever, and that really is a target for prank posts by friends or relatives.
this verification every few days is really a pain. My computer has been on the same table in the same house for 3 years and connects to the same ISP. The nuisance with the redmondians is as always happening when you want to do something quickly. The newest is a window opening, covering half the screen and no way to close it except switching off the computer. Task mgr, ctl alt del inactive. What a pain NoWIN10 can be when MS is tickled by fleas.
I’ve never had any problem with periodic requests from Microsoft asking for additional information. One way to increase the frequency of those requests is to delete cookies. When you delete cookies, it can cause the browser to lose the information which tells the website you’ve logged on before with that device.
Yeah. what you’re seeing isn’t normal. Like I said we’d have to know a LOT more about what your system is up to, what program is asking, how things are configured, and what EXACTLY you are doing at the time the pop-up appears. LOTS of specifics required here, I’m afraid.
I set up my account more then 10 years ago. So I don’t remember all the security information they are asking for. I know my user name and password but it won’t let me in! Keeps asking me to verify and when I do says I haven’t provided enough information. This is crazy. My account is now useless and it is associated to things I use! Is there any resolution to this?
No there is not. You must remember the alternate and security information you provided — or keep it current as you use the account. If you can’t prove you are who you say you are (by providing that information), there’s no way to get back in. Follow the recovery instructions carefully is all I can suggest.
GMail just forced 2-factor authorization on me. Fortunately, instead of sending a text it uses a notification from the Google Play store. (I say “fortunately” because the phone I use does not get unlimited texts.)
I’ve had problems using a VPN with a GMX.com email account. Whenever I’ve tried to login to that account when going through the VPN, even when it’s within the same country or city, GMX decided to lock me out of my account, no questions asked. Their “Support” simply told me there was suspicious activity on my account and it wasn’t until I asked if the login attempts were made from cities used by the VPN that they decided to let me back in. Sadly, I cannot use GMX.com when using a VPN.
It is my impression that updating a browser also results in “we don’t recognize the device you are logging in from”… possibly the browser update clears cookies or there is some “device signature” that’s being used…
I try to make a point of recording account related security information (answers to security question, back-up device & TFA / account details in LastPass.
I can see a need for an app or extension to LastPass to keep track of all the places you have used an e-mail account or phone no for account recovery/ TFA purposes. Really awkward when your recovery e-mail account was closed 2 years ago….
I’ve not experienced a browser update causing this. (And I definitely update my browser . . . often. )
)
It’s posible that a bug in the update may have cleared the cookies.