If you rely on them, it pays to prepare.
What you describe happens more often than one might think.
There are people who use an application for some time and suddenly find that the company is no longer in business, and there’s no way to get an update. Sometimes that means they can’t migrate to current versions of their operating system if they want to keep running that now-unsupported software.
It’s something I consider when selecting important software. Depending on what programs we’re talking about, there are approaches you can use to back up your data and protect yourself from potential software obsolescence or disappearance.

Preparing for the death of an app
When an app you depend on dies, you don’t have to lose your stuff. Save your data in simple formats like text or CSV, keep copies of important software, and store unencrypted backups safely. With a little prep, you can switch apps later without panic.
Export as backup
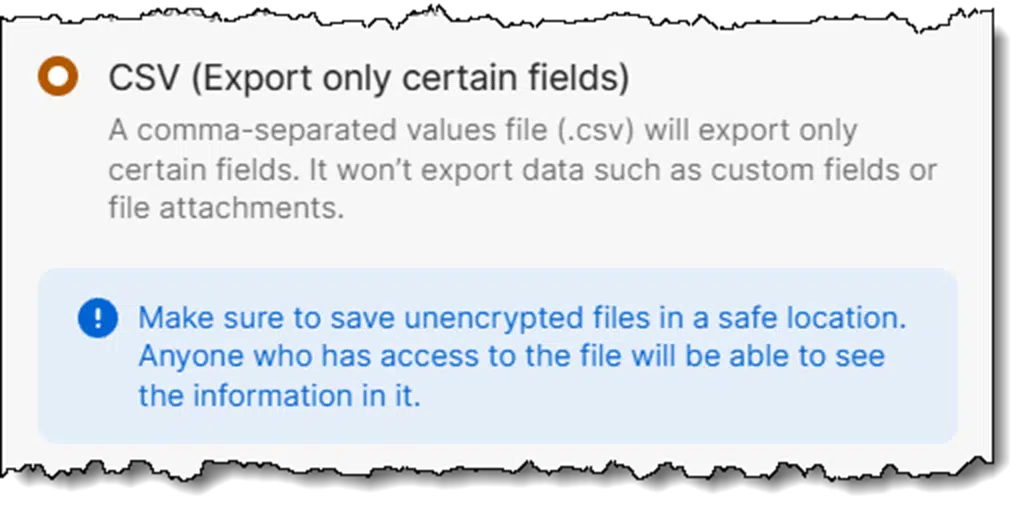
It is critical for utilities that keep important data in proprietary formats (like password managers such as 1Password and others) to support the ability to export your data into a common, simple, open file format. For example, they should support exporting everything to a text file, a CSV file that can be read by Excel, or a PDF file that can be read just about anywhere.
That way, if something ever happens to the utility or its ability to provide its functionality, you have a backup.
Not only that, but you have a backup that’s in a standard file format you can use or can import into a replacement utility.
This is one reason I stopped using RoboForm many years ago. At the time, it had no export capability. (I’m told it does now.)
Help keep it going by becoming a Patron.
Unencrypted files as backup
With encryption utilities like TrueCrypt, its successor, VeraCrypt, or Cryptomator, the approach is a little different. These utilities are tasked with encrypting or providing encrypted storage for important data files.
The approach to protecting yourself from the program “going away” is fairly simple:
- Keep a copy of the program that works. Presumably, you can always use your older version to access your data. This proved true when TrueCrypt “went away” some years ago.
- Back up your data in unencrypted form separately. Secure it using a different tool or mechanism. In the case of tools like VeraCrypt, that means backing up the contents of the VeraCrypt drive or volume, not the encrypted volume itself.
As long as you have a copy of the files you need outside of the utility — albeit perhaps in a significantly less convenient yet secure format or location — then it’s no disaster if the utility stops working some day.
As long as you keep a working version of the utility around, you’re protected nonetheless.
Backups as security risks
“But Leo!” I hear you saying, “We use tools like VeraCrypt and 1Password to keep things secure. Doesn’t keeping those unencrypted exports around leave us just as vulnerable as not using the utilities at all?”
Well, sure, if you leave those unencrypted files where anyone can get at them.
Don’t do that.
You must secure those unencrypted backups. That could mean storing them offline in a secure location. It could also mean encrypting them with a different tool. For example, if you encrypt your 1Password export using a tool like 7-Zip with encryption, then:
- Everything remains secure.
- You only lose access to your information if both tools become completely unusable (unlikely, as we’ve seen) at the same time (even more unlikely).
What I do
I follow my own advice and do what I’ve described.
The unencrypted files I store in Cryptomator are backed up nightly into an encrypted .zip archive, which is then stored in a secure location.
I periodically export my 1Password database1, which is bundled into a password-protected .zip file and then stored in a secure location.
The practical risk
When it comes to popular and pervasive software like VeraCrypt or 1Password, my belief is that the risks are quite minimal. You may not have to take all the steps I’ve listed. The only exception might be if you plan for your backups to be accessible decades from now. I expect that plain text and CSV will outlast almost any proprietary format and will be readable on whatever passes for a computer 20 years from now.
If a utility is destined to die, there is usually lots of notice, and you’ll be able to make other plans. Even though TrueCrypt’s demise was sudden, existing copies of the tool keep working, giving those so inclined plenty of opportunity to research and move to alternatives.
The risks are with the smaller operators or software destined for smaller markets. There may not be an equivalent “common format” to export to, or the export functionality might not be a priority2. In cases like this, there’s little to be done other than to stay on top of upgrades, if practical, or possibly keep a copy of the utility and an operating environment in which it works for as long as possible. It might also be a time to investigate more exportable alternatives.
And even then … sometimes the worse case scenario actually happens. For example, Microsoft’s Publisher is going away next year, and there seem to be no alternatives.
Do this
Back up. Above all, back up.
But if you can, back up your encrypted and proprietary data in unencrypted forms and open formats. That’s the safest way to protect you from possible problems down the road.
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.




The problem — in my case, with VeraCrypt — is that I use it exactly and precisely because it is by far THE most secure solution available for Windows. It can be (and in my case, IS) set to encrypt its containers, not just with one encryption algorithm, but with three. — a technique called “superencryption.” This is the very pinnacle of encryption security.
Almost by very definition, therefore, any other tool I use to “back up” my files is going to provide inferior security by comparison! Yes, sure, 7Zip and the like can encrypt files — but if I were to be content with that, I wouldn’t be using VeraCrypt in the first place!
Now, fortunately for me, there is an Android program I use — “Secret Space Encryptor”, or “S.S.E.,” that also uses superencryption (its “Paranoia” algorithm, is likewise a cascade of three different algorithms). So, yes, I could transfer my unencrypted VeraCrypt files to my Android device, and encrypt the with S.S.E.. But what a lot of trouble! And for what benefit?!
I do save up the encrypted container — and the VeraCrypt program — to other disks; I consider that adequate.
And the “S.S.E.” solution, which would work for me, won’t work for a lot of other folks.
So… what to do?!?!
You do not have to stop using a program just because the company dies or changes direction. I still use a program I purchased in 1998 as a shareware program.
“It could also mean encrypting them with a different tool.”
I’m glad you mentioned that. Most people don’t have a secure location to keep their unencrypted files. I use .zip encryption. It’s a ubiquitous format, and as you said about plaintext and .csv, it should outlast almost any proprietary format and will be readable on whatever passes for a computer 20 years from now.
I have only one thing I need to securely back up, and that’s the contents of my 1password vault, so I’ve exported all that information to a CSV file, then used 7-zip to save it to an encrypted 7Z archive, secured with a sixteen character password. I’ve set up a specific folder under Documents to store the archive. If I understand correctly, I can add other items to this archive later if I need to. Finally, my Documents directory is synced with my MEGA storage space, so it’s off-premises too, not to mention that it gets backed up along with everything else on my computer by Macrium Reflect Free, daily.
If I’m making any wrong assumptions here, or I’m missing anything, please tell me.
Ernie
As an alternative to keep unencrypted data with a zip file, do you consider storing this data on a Bitlocker USB drive as equally safe?
Bitlocker, Veracrypt, and Cryptomator, etc. are very effective encryption programs. We recommend .zip encryption as an additional backup because the .zip format is ubiquitous and will, likely, be around long after those other programs are no longer supported. Even though programs are no longer supported, they will still work, but future OS upgrades might render those programs useless.