answercast 120
Are Silent Background Updates a Good Thing?
In my opinion, background updates are awesome. I love that Chrome is always up to date without my ever even having to think about it. Let’s look at why.
Can I Add More than One External Monitor to My Machine?
Depending on the hardware ports that you have on that laptop, you should be able to simply plug in a monitor. I’ll show you your options.
Why Doesn’t Malware Appear in the Add/Remove Programs List?
Malware not showing up in the Add/Remove Programs list doesn’t surprise me at all. After all, malware’s success is based on its ability to hide from you!
Can Backups of Email Be Hacked?
Not just email, but any information that is anywhere on “the cloud” is subject to backups. That means there is a copy somewhere. Is this a problem?
Is There a Way to Determine which Browser Tab is Playing Sound?
Websites that automatically play sound are evil, pure and simple. And there is only one way to quickly get rid of the intrusive sounds.
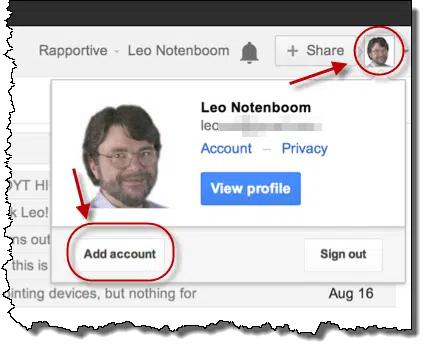
How Can I View Two Different Email Accounts at Once in a Browser?
From multiple browsers to native support, there are a few ways to have multiple browser-based email accounts open at once. I’ll review the most common.
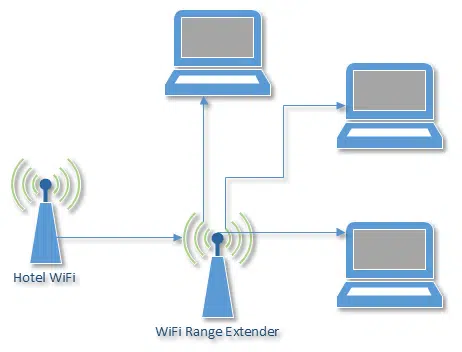
How can I share a single WiFi connection across multiple devices?
I have a rant about hotels that nickel and dime you on an internet connection. Fortunately, there might be something that you can do about it.