It happened to me. The steps I took, the mistake I made, and what I had at risk.
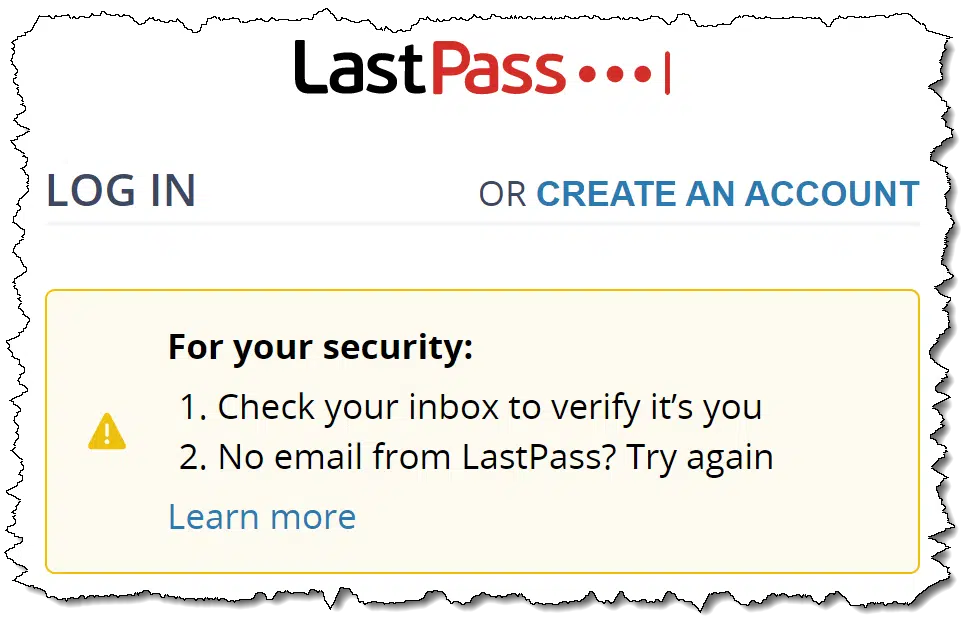
On a recent trip, I arrived at my hotel, set up my laptop, and was working along when I needed to sign in to my LastPass vault. After entering my ID and master password, I was greeted by a message saying I needed to check my email for a message confirming that it was really me.
Fine. No problem. Extra security is good.
Except the message never came.
Here’s what happened next.

LastPass security
I couldn’t sign in to my password vault due to an email that appeared not to arrive — but realized I had several other ways to access the information and accounts in my vault. After reaching out to LastPass support, they quickly reminded me of a security setting I’d overlooked that would have allowed me back in instantly. The experience reinforces the security of using a good password vault like LastPass.
Before we proceed
I want to be clear that LastPass did almost everything right. I have one suggestion for a minor improvement on their part, which I’ll mention below, but the reasoning behind the additional security is sound (I was signing in from a new location).
When you think about it, extra security on the part of providers like LastPass only makes sense. A minor annoyance, like an extra step to confirm you are who you are, is small compared to the disaster that might result should the wrong person be granted access.
You just have to do your part by having up-to-date security information.
That’s where I stumbled slightly.
It was never going to be a disaster
Not being able to sign in to my LastPass account on my laptop seems like it might be a huge problem.
It wasn’t. It was, at worst, an annoyance. I didn’t “lose” anything, and I certainly didn’t lose access to any of my accounts.
There were three ways I was covered, no matter what happened.
- LastPass on my phone. This is how I solved my immediate need. I opened LastPass, viewed the password for the site I was attempting to access, and carefully entered it on my laptop. Naturally, since my passwords are long and complex (example: “beKqRCS9UM6Wac5ffkBD”), this was a slow process, but it worked.1
- I have backups. I didn’t need this, but it was an option. I back up my LastPass vault more or less monthly, and had done so just a week or so prior to my trip. With remote access to my systems at home, I could, if needed, transfer the backup to my laptop and extract whatever passwords or account credentials I needed. The backup itself is manually encrypted2 and secure.
- Password recovery. Even if I lost access to the vault entirely and had been unable to access my backups, I still would not be locked out of anything. I can do a password/account recovery on those accounts to which I need immediate access. They all have current recovery information using alternate email accounts, phone numbers, or backup codes I had access to should I need them.
So, as you can see, losing access to my vault would be — at worst — an inconvenience.
With that knowledge, I relaxed and got my work done.
Then I reached out to LastPass.
LastPass support
I decided to reach out via Twitter. They responded with a request I direct-message them my account email address so they could look into it. The next day, I had received a more detailed response.
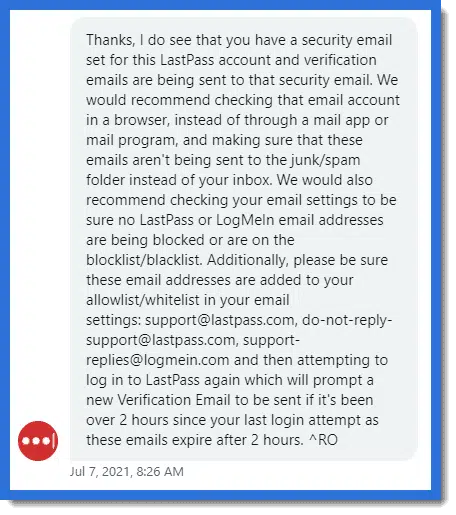
I’ve had LastPass for a long time, and honestly, I don’t recall ever having set up a security email. “No email from LastPass?” in the initial email might have clued me in to look elsewhere, but it didn’t occur to me.
And yet . . . I started checking some of my lesser-used accounts, and sure enough, there it was: the email I’d been missing.
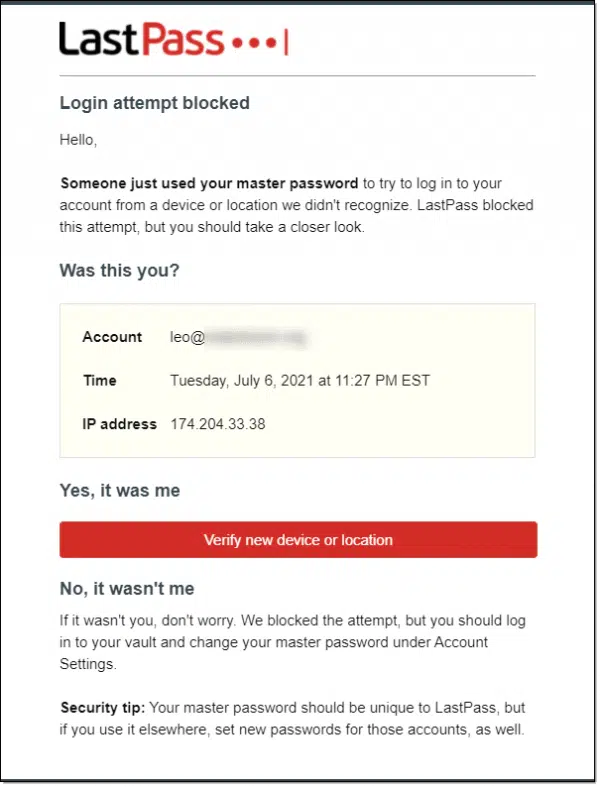
A pretty standard “verify a new location” request. Good security, as long as you remember that the message might be sent to the security email and not the primary account email. (And, of course, you remember that you have a security email configured.)
Again, this makes total sense. Had this been a malicious login attempt, it would imply that someone knew my master password. It might also imply that the email address used for my login could also have been compromised, or was at least at somewhat higher risk, so sending a verification email to the security email address makes sense.
The only change I’d suggest on LastPass’s part? Include some indication in the initial notification that the security email address might be used. That would have saved me from this entire scenario.
A change I’ve made since
Everything worked as it was supposed to. The only issue was that I didn’t remember that there was an “alternate” or security email address associated with the account, and remember to check that account.
Since the time I apparently set that up, I’ve started using a different email address at a different provider for my recovery emails for other accounts. This recovery email doesn’t rely on any of my other email infrastructure.3 More pragmatically, it has a mobile app and I have notifications turned on, so I would have immediately noticed that email had arrived at that account.
I’ve since updated my LastPass security email to use that same recovery address.
An indictment of password vaults — not
This isn’t an indictment of LastPass or password vaults in general. In fact, just the opposite: it shows just how protected you really are when strong security measures are in place. Using a password vault remains more secure than any other alternative I’m aware of — any other alternative.
You do, however, need to take responsibility for the security and recovery options associated with the account.
And (*cough*) not forget that you’ve set them up.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
Footnotes & References
1: After a couple of tries, I ended up doing what amounts to a secure copy/paste instead, using a text file, DropBox, and BoxCryptor on both the phone and laptop to avoid the re-typing. BoxCryptor is what kept the text file secure from prying eyes.
2: Using GPG, but I’m considering dropping back to the conceptually simpler Zip encryption.
3: Yes, I have “email infrastructure”. The best example is that all email is routed through my own servers. The recovery email address I’m now using doesn’t, just in case there’s a problem with my servers or other infrastructure. Clearly, that’s not a problem “normal” people will have.





This must be something new that LastPass is doing. A short time back, I went through the same thing with my spouse’s LastPass account (She doesn’t login to LastPass very often). Like Leo, I too had forgotten which email address was used for recovery until I went to my computer and found the email in my inbox. Not a disaster, but it does create a sinking feeling that something has gone wrong.
I use LastPass Family, so a few of the logins are shared between my wife and I. I also download logins to a spreadsheet for backup purposes.
I’m a little confused. Do I need to have a Security Email set up? Does it have to be different than my Account Email? If I don’t have a Security Email set up, does is just default to my Account Email?
I don’t believe it’s required, but recommended.
This is the way I understand it too. The help isn’t completely clear. I appreciate your comments confirming what I suspected.
Is there a way to search the security settings in each of the sites in your Lastpass vault without having to visit each site separately? If not, you would have to visit each site or keep a separate record of your own containing this information which could compromise the security of the vault.
I’m confused by your question — the security setting I was dealing with here is for LastPass itself, not the sites you track with LastPass.
If I understand you correctly, no, there is no way to easily search the security settings of every site in your vault. I’m in the process of dropping my ISPs email address and I’ve been logging in to every website, one by one and updating security information.
Given the way every website organizes their website and access security information, I can’t see how there could be any app that could simplify reviewing/updating security information.
I’ve found the easiest way to change to a new email provider is to set up the new provider to fetch all mail from the old address on an ongoing basis. You start by going to all the websites you can think of and changing their security to point to the new address. Then just sit back and wait until the ones you forgot send you an email. The email will show up in your new email account with the old “To” address. Just go to that site and change to the new address. The process can take months but you won’t lose a single email and eventually the mis-addressed emails will dry up.
That’s a great approach for accounts you can keep, or that you haven’t lost. Unfortunately, James indicated he’s leaving his ISP, which typically has a hard “it’s just not going to work any more” date.
After the last price increase and other problems with LastPass I tried Bitwarden. Liked it better on Android phone and PC’s. I quit paying for LastPass still have the free version but don’t really use. I give a $10 annual donation to Bitwarden, less headache much happier and saved some coin. After LogMeIn, Inc. acquired LastPass in October 2015 it pretty much gone down hill.
Thanks for posting this.
I need to check my settings because it is annoying to me that I have the E-mail sign-in AND I have 2-factor authentication that I do with the Authy App. I added the extra security because a few months ago, someone used my Amazon account to activate PRIME, and one credit card had 3 fraudulent purchases. I could not figure out how it happened, so I looked at if my LastPass got compromised, but not sure how that could have happened.
I’ve had a few fraudulent charges against my credit card and my checking account, but none of them were from online purchases. They happened because I handed my card to a person who either copied or memorized the numbers. LastPass uses strong encryption that has never been compromised.
I use 2 password apps simultaneously in case I have problems with one.
I periodically back up my LastPass vault to CSV and zip encrypt it.
I do the same. I mention in the article that realizing that made me feel a whole lot better about any possible issue even if LastPass never let me in on my trip. Fortunately it wasn’t needed, but I slept better because I had it.
By “zip encrypt” you mean you compress it (which app?) and put a password on it?
In windows, if I right-click a folder and select ‘Send To’ > ‘Compressed (zipped) folder’, I can then put a password on it but I’ve always felt someone who knew what they were doing could easily hack that password, yes?
Yes, “zip encrypt” is to use a zipping utility with a password. Current zip encryption technology is sound, and not easily hacked at all.
Thank you! Now I have confidence in something I shouldn’t have been worried about to begin with!
In the first solution you write: “I opened LastPass”. But how did you open it as it required additional security confirmation which you didn’t have?
My phone was already signed in and wasn’t requesting additional security. It was my Laptop on which I was having the problem.
Last Pass still works on my iPhone because I have it remembering my password. I can’t log in on my PC because the email address on the account has closed down and I can’t get the verification email. I have been trying to get in touch with their customer service for weeks but haven’t had any success. Can you help me change the email address on my Last Pass account?