Sharing files securely may be easier than you think.

Sending an encrypted document as an attachment is a reasonable approach to securely sending information in what is otherwise an insecure medium: email. Even though there are approaches to encrypting email messages themselves, they’re either obscure or complex (or both), and not widely known.
Encrypting individual files can also be an important step in secure data management.
I have a specific recommendation that should be easy and work just about everywhere.

Encrypting a file
Encrypting a file is easy with 7-Zip. Put the file in a .zip archive and set a passphrase. The result works across Windows, Mac, and Linux. Share the file securely, but give that long-and-strong passphrase separately.
Zip it
The .zip file format, formally referred to as an “archive”, lets you bundle multiple files together into a single file that is compressed to save space.
Password-protecting a zip file encrypts its contents.
There’s nothing that says you must include several files in the archive; you can also use .zip to encrypt single files.
I’ll use 7-Zip for my example, but the .zip file format is widespread, and zipping tools are available on every platform, including Windows, Mac, and Linux. You should be able to decrypt a zip file encrypted on one platform on any of the others.
Open 7-Zip and navigate to the folder containing the file you wish to encrypt. Right-click on the file, select 7-Zip, and then Add to archive.
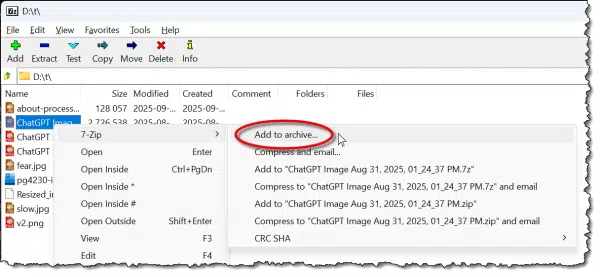
The other quick options, like “Compress to ‘<filename>.zip’ and email” look convenient, but they don’t encrypt; thus, our use of the “Add to archive…” option.
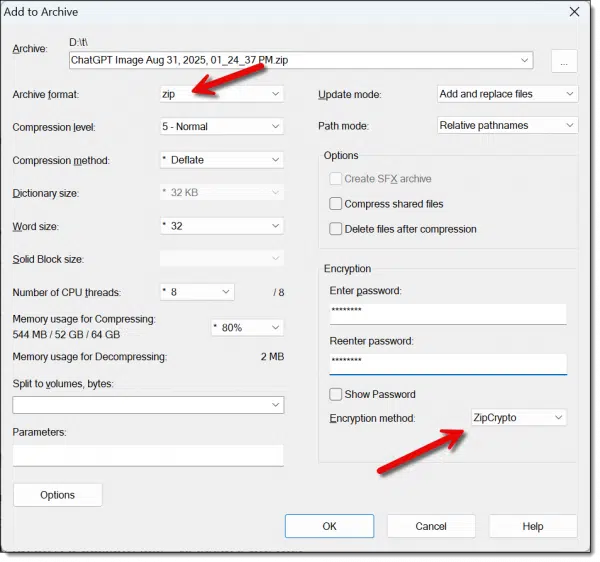
The first field lets you name the output file. By default, it’ll be the name of the file you selected, with the extension changed to .zip.
Settings to pay attention to:
- Set the archive format to “zip”. This ensures that 7-Zip is not required to extract the file. Anyone with a Zip program (and the password) can open it.
- Enter a password — more ideally, a passphrase — to secure the file.
- Select the encryption method: ZipCrypto, the default, is the most compatible across different unzipping programs. AES-256 is somewhat more secure. I’d recommend AES-256 unless your recipient tells you it doesn’t work in their zip program.
Click OK, and 7-Zip will create your .zip file.
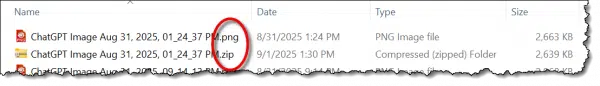
In this example, I encrypted a random ChatGPT .png image. Note that most zip utilities leave the original alone. You may want to delete that if you don’t want an unencrypted copy of your file to remain.
You can now send that file to others, and they can use their zipping program to extract the contents of the file. (Be sure to share the passphrase separately — ideally via a method other than email.)
7-Zip command-line
I’ll be honest and say that I’m not a big fan of the graphical interfaces of most zipping utilities. They’re too confusing and cumbersome for me.
Here’s what I really do to zip a file: in a Windows Command Prompt, where the file I want to encrypt is in the current directory, I type:
7z a -tzip -p example.zip example.doc
Where:
- 7z: Is the 7-Zip command-line program.
- a: Means that we are adding a file to an archive.
- -tzip: Indicates that the type of the archive to create is a zip file.
- -p: Causes 7-Zip to prompt for a password to be used to encrypt the file.
- example.zip: The zip file we are creating (or, if it exists, the zip file we are adding to).
- example.doc: The file we are adding to the zip file.
To decompress and decrypt the zip file back into its original file or files, the command would be:
7z x example.zip
Where the “x” command simply stands for extract.
One Zip drawback
One characteristic of the zip file format is that even when encrypted, the list of filenames it contains remains readable. The net effect is that in our example, someone without the password may not be able to see the contents of our file, but they can still see its name.
The traditional solution to this is to rename the file to something obscure before zipping, or to zip twice. Zipping twice has the added benefit of preserving the original filename for the intended recipient.
- Zip the file once, without a password, into a single .zip file with an appropriately obscure name, like “zippedfiles.zip”.
- Now, zip that file again into another .zip file, this time specifying an encryption password.
The net effect of this approach is that the contents of the files, as well as the names of the files contained within the original zip, are protected.
What about Windows?
Windows File Explorer includes .zip file support.
Except.
It’s not possible to create a password-protected zip file. You can use Windows File Explorer to open password-protected zips, like the ones we created above, and you can use it to create zip files that are not password-protected, but that by itself doesn’t solve the problem at hand: encrypting a file.
You are the weakest link
There’s a lot of discussion about which encryption technology is the “best” and thus least susceptible to cracking. This is an important discussion, and I believe the scenarios above are sufficiently secure for all but the most demanding applications.1
However, hackers rarely gain access to encrypted files by cracking the algorithm.
Instead, they simply hack the password.
Picking a weak password makes that kind of discovery easy.
Unlike hacking passwords online, in this case, an attacker can spend as much time with your encrypted file as he or she would like to. In fact, they can throw as much computational power at it as they want to perform a brute force attack, trying every possible password.
An eight-character password is nothing to an offline brute-force attack these days.
That’s why most of these programs don’t use the word password but default to passphrase.
Rather than using a short eight-character password, use a longer phrase comprising four or five words that total at least 20 characters or more. No matter how you do the math, this is virtually uncrackable using current brute-force techniques.
Do this
Encryption is an important tool for keeping your data secure. Particularly when exchanging files with others, encrypting using your favorite zipping tool is a fast, convenient approach.
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: Depending on your needs, you can delve deeper into different algorithms used in most zipping programs, or dive into public key encryption with PGP/GPG.


“Zippedfiles.zip” is not an “obscure” filename (in fact, it’s a perfectly logical one).
From a would-be snooper’s viewpoint, however, it is a completely unhelpful one. 🙂
One definition of “obscure” is:
“to prevent something from being seen or heard:”
Obscured might have been a better choice of words, but when something has been obscured, it is obscure. 🙂
“The first field lets you name the output file. By default, it’ll be the name of the file you selected, with the extension changed to .zip.” If you zip more than one file, the default will be the name of the folder the files are located in.
I know that this forum is primarily focused on Windows. Many users prefer to send messages, files, and pictures using Android or Apple devices for a lot of their daily communications in life. Is there a way to send a Zipped file with these devices?
There are apps for Android and iPhone that can compress and encrypt. A couple of popular ones are ZArchiver and RAR for Android. There are other similar apps for iOS devices.
Encrypted zipfiles have the advantage of compressing the file before encrypting it, which enormously increases the file’s security.
To answer a question about Android devices — a quick check of the Google Appstore confirms that 7zip itself is not available on Android. However, there are plenty of other zip programs for Android! Check ’em out.
One thing I don’t like about using zip to encrypt files is that their most secure algorithm is always AES.
I distrust AES — not because ut is insecure, but because it is “the” universal algorithm, and therefore the one most under attack. I prefer to use a lesser-known algorithm like Twofish. It’s just as secure (it was a runner-up in the same contest that gave us AES), but isn’t nearly as widely used. For this, one unfortunately requires a different encryption program; Twofish ISN’T included in any zip utility.