Last week I posted this on Facebook:
Just had to break the news to a friend that the photos on the hard drive that failed – the contents of which we WERE able to recover thanks to some hard disk utilities – turned out to be encrypted by ransomware (CryptoWall), and we had no way to decrypt them. And no, they didn’t have a recent backup. (And yes, there were some VERY important photos on there. I’m hoping that they’ll recover some at least from friends and family with whom they shared ’em.)
This is why, folks. This is why I harp and harp and harp on backing up. Seriously. Sh*t happens. Sometimes its benign, and sometimes its downright heartbreaking. PLEASE back up.
I want to go into that in just a little more detail, and expand on how this could have all been very close to a non-event.
Become a Patron of Ask Leo! and go ad-free!
Hard drive failure
The call I got was from a friend. He was at a local office supply store’s computer service desk, a tad befuddled at the terms, and dollar amounts, the technicians were throwing at him.
The situation turned out to be this:
|
My friend’s question was simple: did he need this, or was he being taken for a ride. He put the technician on the phone.
The bottom line was that, no, he probably wasn’t being taken for a ride, and that yes, the situation was serious. They’d just gone beyond what the in-store technician could do, hence the need to send it out.
He brought the machine to me instead.
Hard drive recovery
When I encounter bad sectors on a hard drive my go-to tool of choice for many years has been SpinRite, so that’s where I started. I hooked the faulty drive up to one of my spare systems and let it go.
Unfortunately SpinRite hasn’t been updated in years – which is really sad, actually, as it’s a great tool when it works. Naturally it didn’t work for me in this case. Be it the BIOS on the machine, the SATA interface or the sheer size of the 1 terabyte drive, SpinRite would only go so far before crashing.
I Googled SpinRite alternatives, and while there aren’t any really, I came up with something close: MHDD. (As always and for any website, be careful to understand what is and is not an advertisement – advertisements are not related to the site itself, and can often be misleading.)
MHDD’s most basic difference from SpinRite is that when it finds a bad sector it “remaps” it – basically taking it out of use and replacing it with one of the spare sectors that hard disks have for exactly this purpose. Note, however, that it doesn’t attempt to recover the data in that bad sector. SpinRite will actually first work long and hard, if need be, to recover the data in that sector – often both recovering it and repairing it so that no remap is needed.
I let MHDD do its thing, after which I was able to use Macrium Reflect to take a complete image backup of the faulty drive and restore that image to the replacement drive in my friend’s machine.
All seemed well, and I sent the machine home.
Later that day I got an email.
Cryptowall
After getting back into the machine and poking around, it appeared that several of my friend’s pictures were somehow damaged.
Since I’d kept a copy of the backup image “just in case”1 I restored it to a hastily-created partition on one of my active machines and started looking around.
What I found was not pretty.
The images weren’t images any more. Oh, they had the same names and the “.jpg” extension all right, it’s just that their contents didn’t look like jpg image data at all. In fact the contents looked more like random data. Almost as if the files had been … encrypted.
And then I found this:
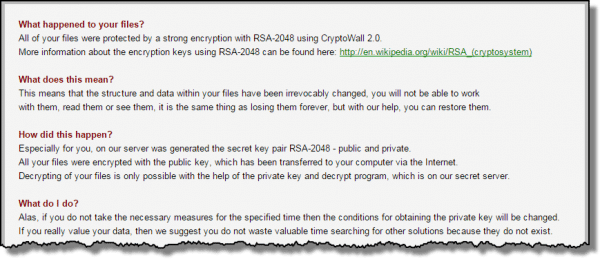
Somehow, somewhere, this machine had become infected with the CryptoWall ransomware: software that encrypts all your important files, and then displays a ransom note instructing you how to pay to get the decryption key to get all your files back.
My friend had never seen that ransom note. That means either the encryption process hadn’t completed when he’d last turned off the machine, or the virus had attached itself to the machine while at the service center. Timestamps on the files would indicate that it arrived prior to the service center touching the machine.
Either way:
- It appeared to be totally unrelated to the hard disk failure. (It’s possible that the encryption process caused the hard disk to stumble into a previously unused bad sector, but there was no real direct cause and effect at play here.)
- The hard disk recovery was a success, but the prognosis for this new situation was even worse.
Recovery efforts
BleepingComputer.com has a good page on CryptoWall, including common approaches to recovery. Unfortunately none of them could be used.
- Restore from a backup: There was no recent backup. Some files are available on a months-old backup, but that doesn’t help with recently created, updated (or encrypted) files. Naturally I’ll have more to say on this.
- File Recovery Software: The process of recovering the original drive to another drive invalidated anything that file recovery tools might use. (Though the original “failed” drive remains unaltered, and may be a last-resort at some point.)
- Shadow Volume Copies: The process of recovering the drive to another invalidated anything that file recovery tools might use. The original drive may have them, but the chances are slim since CryptoWall actually intentionally deletes them.
- Restore DropBox Folders: Dropbox wasn’t being used.
In short, and as of this writing, we are SOL: severely out of luck. The files that were encrypted remain encrypted with little-to-no chance of direct recovery.
Which leads to the moral of this story.
Avoid? No. Recover? What could have been…
Bad stuff happens. It just does. You simply cannot avoid it all the time.
Hard disks die – without notice and without warning. In fact they can die so quickly, so suddenly and so badly that all data stored on them can be instantly and irretrievably lost forever. Nothing malicious is required – they can just die. Stuff happens. Most failures aren’t instantaneous or irretrievable, but they can be.
And of course malware happens. It shouldn’t. In a perfect world, we’d never invite it in, and if we did, our perfect anti-malware tools would protect us 100% of the time. Neither the world, nor our computer, nor even ourselves are perfect. Stuff happens.
You can’t avoid it.
But you can prepare for it.
And this is what makes situations like my friend’s doubly frustrating. Here’s what could have been:
- Hard disk dies.
- Replace it and restore with the previous day’s image backup.
- Done. Get on with your life.
Or perhaps:
- Machine is infected and all files on it are encrypted and a ransom demanded.
- Restore the machine from the previous day’s backup.
- Done. Get on with your life.
(In the second case, there’s of course, another step: “don’t repeat whatever caused the infection”.)
THIS IS WHY I harp and harp and harp on backing up.
It hurts me to see data loss – particularly important data like irreplaceable family photos (as might well be the case here).
If there’s only one copy, it’s not backed up. If that’s true for anything you consider even the slightest bit important, start backing up, please.
I don’t really care how you do it or what tools you use (as long as they work, of course), just make sure that you’re doing it.2
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!


Thanks for the article. Wow, as if guarding against the possibility of HDD hardware failure wasn’t worrisome enough. Is CryptoPrevent enough defense against these CryptoWall extortion rackets (apart from making backups, I mean)?
Here’s an article on Cryptoprevent. You’ll find a lively discussion on the topic!
https://askleo.com/why-havent-you-mentioned-cryptoprevent/
CryptoPrevent protects against CryptoLocker. The problem is, you’d still have to worry about any similar ransomware or malware which CryptoPrevent doesn’t prevent. I have no idea if it even helps against CryptoWall.
Why haven’t you mentioned CryptoPrevent?
My understanding is that it does help against CryptoWall – BleepingComputer mentions it specifically.
One thing I don’t think you mentioned is that shouldn’t you disconnect the backup drive after taking the backup? Isn’t malware smart enough to encrypt the backup drive as well as the primary drive if it is connected?
Leo has a few article on that:
https://askleo.com/is-it-safe-to-leave-my-external-backup-drive-connected/
https://askleo.com/will-malware-infect-the-backups-on-my-connected-backup-drives-as-well/
Leo wrote an article on that. Bottom line: He leaves his plugged in.
Is it safe to leave my external backup drive connected?
Leo is the expert no doubt, but with these Crypto situations people report that it also targeted their external drives. From everything I’ve read you want to make a backup and disconnect that drive so it doesn’t become a casualty. Yes we should all be doing things so it never happens in the first place (safe surfing is #1) but in today’s world that’s not always possible as sometimes even experienced users get nailed… drive by infections, injection, a app that you may not have updated being exploited, etc.
Sorry to hear about your friend’s hard disk issue. Fortunately, you were able to spare him the data recovery expense for repairing the bad sectors. As for the Cryptolocker/Cryptowall, he basically has two options: 1) Pay the ransom or 2) Wait it out. The servers for the first variant of Cryptolocker were eventually seized and the corresponding private keys (needed to decrypt) were publicly released for free. If I were your friend, I would keep the image you created until I was able to recover the encrypted data. Good luck.
Actually I’ve kept that image (and the original drive, actually). I’m hoping that, as you say, eventually the crypto keys will be discovered.
And the only way this will happen is if someone can infiltrate the place where these keys are stored on the bad guys end no? Short of that or a miracle people will be waiting a very long time.
Is it possible that the MHDD tool you downloaded and run on the hard drive was the delivery path for cryptowall?
I don’t believe so.
Try: https://www.decryptcryptolocker.com :
“FireEye and Fox-IT have partnered to provide free keys designed to unlock systems infected by CryptoLocker”.
All you have to do is upload an affected file and “This portal will then email you a master decryption key along with a download link to our recovery program that can be used together with the master decryption key to repair all encrypted files on your system”.
Hope you get your photos back!
That’s for CryptoLocker, not CryptoWall … yet.
I Have since loaded and continue to use a cryptoware blocking program that was distributed as free ware by foolishit.
What about HDD Regenerator? I’ve seen mention of it’s use before. Do you have any experience with it?
I’m not familiar with it.