While pulling together a video describing how to use BitLocker to encrypt a hard drive, I ran into a problem.
I couldn’t.
More specifically, the machine I was using didn’t have a required hardware component used by BitLocker: the TPM, or Trusted Platform Module.
Fortunately, there’s a workaround.
The Trusted Platform Module
The TPM is, essentially, a hardware encryption component.
It’s fairly complex, but for our purposes, think of it as a tool to generate and store encryption keys used for things like BitLocker’s whole-drive encryption.
Generating the key is important, because the hardware implementation allows somewhat more secure1 keys to be generated more quickly. Storage matters because it prevents a drive encrypted on one machine to be physically moved to another and decrypted there.
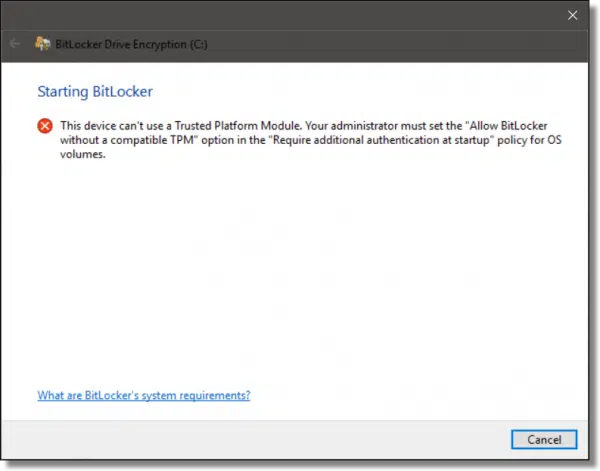
By default, BitLocker requires TPM. If you attempt to enable whole-drive encryption without it, you’ll get an error message.
The good news is, most newer, modern machines include a TPM, and have for several years. The bad news is, older machines do not. In my case, the virtual machine software I use apparently doesn’t support exposing the TPM to my Windows 10 virtual machine.
The workaround is a setting in the Group Policy Editor.
Group Policy Editor
Open the Windows “Run” dialog box (the easiest shortcut is Windows Key + “R”), enter “gpedit.msc”, and click on OK to run the Group Policy Editor.2
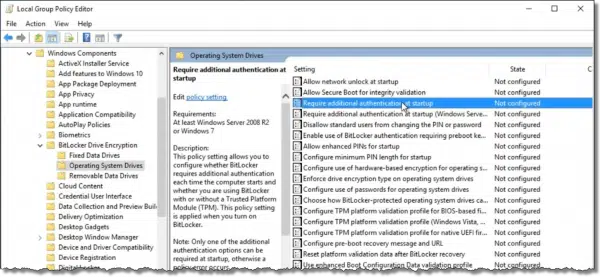
In the left-hand navigation bar, expand (by clicking on the arrow to each item’s left, if necessary), in turn:
- Computer Configuration
- Administrative Templates
- Windows Components
- BitLocker Drive Encryption
- Operating System Drives
and in the right-hand pane, locate the setting “Require additional authentication at startup”.
Double-click on that setting to open a dialog in which to edit it.
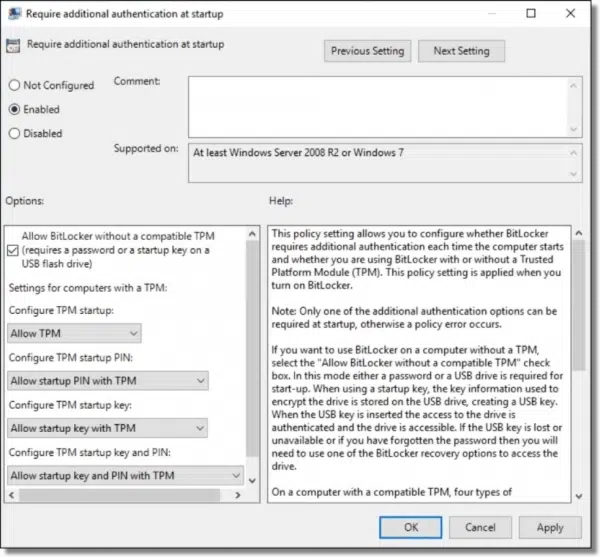
It will likely default to “Not configured”. Click on Enabled, and then OK to exit and save the setting. You can now close the Group Policy Editor as well.
That’s all there is to it. You can now enable BitLocker, even without a TPM.
Do this
Subscribe to Confident Computing! Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
I'll see you there!
Podcast audio
More for Patrons of Ask Leo!
Silver-level patrons have access to this related video from The Ask Leo! Video Library.


Hi Leo,
Good article, but you state: “Storage matters because it prevents a drive encrypted on one machine to be physically moved to another and decrypted there.” The problem I see here is that I encrypted my drive and a short time later the mother board permanently crashes. Now I have no way to decrypt after rebuilding the computer.
That is absolutely correct and completely as designed. That’s why you also need to back up your data.
Yup. We’ve run into that at work when laptops die unexpectedly. I’m not sure how our IT department does it, but there’s some way that they can pull the drive and hook it up with a USB cable, input a code and recover data to a network drive.
i tried this and at the end the only option was a start up key using a flash drive.
password and pin options were both grayed out. i followed the instructions.
this was with an optiplex 360, 2005 model. win 7 ult.
am i stuck with the flash drive?
this is Glen, left something out of my comment. how much space do i need on the flash drive
if it will be used exclusively for the start up key?
Very little. I suspect the smallest flash drive you can find will be much more than enough.
I am not an expert.
I am in the following situation: I have a PC with SSD W10 and a HDD (5 partitions). I have made a ”Recovery” of OS and after that a I have found on the HDD the patitions, even with their name, and only that. Some specialist said me that all the files are encrypted and did not find any solution.
Please give me some advice ? A solution. I am intersted alout two partions.
I have no (known) encryption program on PC.
Thanks !
I followed the article which said on the group policy editor to look for
Computer Configuration
Administrative Templates
Windows Components
BitLocker Drive Encryption
Operating System Drives
When I do this, I do not find the “BitLocker Drive Encryption” option. Why aand how do I get around this?
Which version of Windows are you using? BitLocker isn’t included in the Home editions. If you can’t use BitLocker, VeraCrypt is a good alternative.
https://askleo.com/how-do-i-encrypt-a-hard-drive-using-veracrypt/
I am using windows 10 Pro
i succeeded in making a cruise glide encryption key with the method above. Thank You. this morning when i started up i forgot to put the flash drive into the port. of course, a screen came up asking for the key. i noticed there was an option to enter the key myself by tapping the esc button. i think it consisted of about 8 groups of characters. i could only use the F keys to enter it and no letters were allowed.
where do i find this key? i could just keep that in a safe place instead of a another copy of the cruise glide itself.
Ahem. I use Windows 7 Home Premium, which has NO access to Group Policy Editor. Now what?
Footnote #2 applies.