bestof
Ask Leo! Articles that are part of The Best of Ask Leo! email subscription available at http://bestofaskleo.com.
What is DHCP?
DHCP stands for Dynamic Host Configuration Protocol, and is how computers request and receive “dynamic” IP addresses as well as additional configuration information.
Should I Use Windows File Compression?
Windows File Compression automatically compresses files so they take up less space. In the best of circumstances, it can free up a lot of space, but all too frequently it’s not as much as you might expect, and there is a cost.
How Can I Find a Good Web Host?
Where to host your website depends on what kind of a website it is. Options range from free to expensive based on your needs.
What’s a .DAT File?
DAT files are used by many different applications. To know what to do with a DAT file, you need to know which application created it.
Do Desktop or Laptop Platforms Really Matter any More?
As platforms like Windows, Mac, and Linux have all matured, the differences in fundamental capabilities are getting smaller – in many cases, small enough that which one you choose can often boil down to simple personal preference.
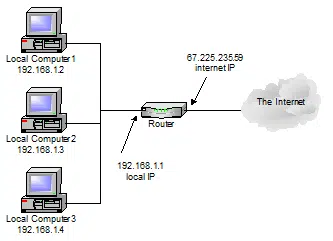
How Does NAT Work?
NAT is a fundamental technology used by routers allowing you to share internet connections and stay safe. I’ll give a conceptual overview.
Why is my email being immediately deleted?
Every so often, anti-malware software can go a little nuts, thinking that every email that you get is spam or a virus. Turn that scanning feature off.
How Do I Protect My Email Address Book?
With email account hacking on the rise, it’s important to understand what it takes to keep your account (and its address book) safe from compromise.
Why Are Electronic Greeting Cards a Bad Idea?
Electronic greeting cards, or ecards, seem like a nice idea, but often end up giving the recipient more than you intended, in the form of spam or worse.
Someone’s Sending Email that Looks Like it’s from Me to My Contacts, What Can I Do?
If your contacts are getting email from you that you didn’t send, then it’s very likely that your email account has been compromised.
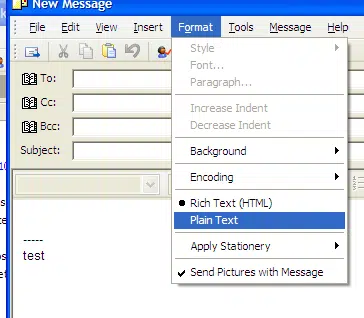
What’s the Difference Between “Plain Text” and “HTML” Email?
Email can be sent in several formats, the most common being plain text and HTML. We’ll look at the difference, and which might be preferable.
How do I resolve my problem with appcompat.txt?
Here’s what to do when you see appcompat.txt.