They assume perfection, and we all know how that goes.
A phrase we’ve heard more and more often in recent years is encryption backdoor. The concept is simple: government agencies want to be able to monitor otherwise encrypted communications.
The concept is flawed.
Become a Patron of Ask Leo! and go ad-free!

Encryption backdoors
Encryption backdoors allow governments or other entities to access private communications, undermining privacy. These backdoors create vulnerabilities; they rely on the trustworthiness of those entities to use backdoor keys responsibly and prevent leaks. Criminals can still bypass such measures using traditional, non-backdoored encryption. Encryption backdoors risk your privacy without effectively improving anyone’s security.
Securing communications with encryption
The fundamental concept of encrypted communications is that only the sender and the recipient can read a message exchanged between them. The sender encrypts it before sending, and only the recipient has the ability to decrypt it.1 One example I run into regularly is sending someone a password — you don’t want someone “in the middle” to be able to see it. An end-to-end encrypted messaging service is one solution.
Governments don’t like this at all. At its most basic, encryption prevents law enforcement from monitoring potentially illegal activities. At its most extreme, it prevents oppressive governments from monitoring what their citizens might be up to.
As a result, from time to time we hear of proposed legislation to force service providers to provide a back door that would allow authorized entities such as governments and perhaps others to access otherwise inaccessible communications.
How a backdoor might work
Traditional encryption works in one of two ways. One method uses a common secret, like a password, which is used to both encrypt and decrypt data. The other method uses a key-pair: one key can decrypt data encrypted by the other, and vice versa. Without the appropriate password or key, encrypted data cannot be decrypted.2
What both these approaches have in common is math — lots and lots of advanced, complex math.
A backdoor adds more math. In addition to the password or key, some kind of “master key” would also be needed to decrypt the data. That master key would be shared only with trusted entities (like governments) with (hopefully) legitimate reasons to decrypt the data.
A real-world physical example
Consider the TSA-approved padlock.

This padlock might have a key or combination. If you have the key or know the combination, you can unlock it.
In the United States, the TSA (Transportation Security Administration) has mandated that approved padlocks also have an additional key slot — a key slot for which their agents have a master key.
This master key is a back door allowing them to bypass your padlock’s mechanism completely and open it. This allows them to examine the contents of your luggage. You can use a non-compliant padlock, but the TSA has the right to break the lock.
There’s a reasonable argument that this contributes to public safety. However, even though it’s likely illegal to possess, the master key has long been available to anyone who cares to get it. Travelers have been forced to sacrifice personal privacy for public security.
Physical versus digital
The major difference between our physical example and encryption is the bolt cutter. Luggage locks are easily broken. Even the most secure locking mechanisms can typically be thwarted with enough skill or force.
That’s not quite the same as digital encryption. An appropriately strong encryption algorithm can be practically impossible to break.
Again, governments don’t like this. They would very much like a way to break the lock, so to speak, of digital encryption.
Why backdoors are a bad idea
Encryption backdoors are not just a bad idea; they’re a horrific idea.
To begin with, we would have to trust the government to hold the master key completely. That means:
- They would have sufficient security in place to prevent the key from being stolen.
- They would have sufficient security in place to prevent the key from being copied.
- They would only use the key appropriately in legitimate circumstances.
Every single employee of the entity holding a backdoor key would have to be trusted completely.
TSA master keys have already failed the first two tests; the master key is readily available.
Just like the TSA master key, the chances of an encryption master key being leaked are very, very close to 100%.
Besides which, the backdoor may not even increase public safety.
Good encryption already exists
Even in extreme cases where encryption backdoors are mandated and the use of non-backdoored encryption is outlawed, criminals still use uncrackable encryption to render any backdoors to new encryption algorithms pointless. Honestly, I don’t understand why more of the conversations on this topic don’t include this tidbit.
If good encryption is outlawed, then only outlaws will use good encryption.
That password I shared with someone? With a back door, anyone with the backdoor key could still see it if so inclined. The only way I have to ensure that’s not possible is to keep using non-backdoored encryption — legal or otherwise.
It just doesn’t make sense
Encryption with backdoors doesn’t make sense.
- Those who use it run the real risk of having their privacy violated.
- Those who understand it avoid it and take their communications elsewhere.
- Criminals naturally avoid it and continue to use more secure methods, legal or otherwise, to communicate.
It’s an ineffective approach to security that decreases the privacy of honest individuals.
Do this
Understand the discussion when you hear or read about it. However, if you’re able to communicate your thoughts to your elected officials here in the United States when the topic comes up (and it will), or the appropriate agency if you’re elsewhere, let them know how pointless this effort is.
No backdoors here! Subscribing to my weekly newsletter, Confident Computing? Less frustration and more confidence, solutions, answers, and tips in your inbox every week.
Podcast audio
Footnotes & References
1: The actual technology use isn’t relevant to this discussion.
2: This assumes an appropriately chosen encryption algorithm. And “cannot be decrypted” really means “cannot be decrypted in a reasonable amount of time”. If you have a few thousand or million years, even the strongest encryption could be cracked.
This article is based on a video I did several years ago: Encryption, Padlocks, and Backdoors. Yes, the topic’s been around that long.




To get around encryption backdoors, you can encrypt your files with a tool you can trust like 7Zip, Cryptomator, VeraCrypt etc. Even if your cloud storage or email service provider has a backdoor, your data remains inaccessible.
To protect email communications, there’s PGPTool Using PGP in the past was complex and too difficult for the average person. PGPTool has simplified it significantly. Get PGPTool before it’s banned or has a backdoor added.
Thunderbird has a tool to use OpenPGP to encrypt emails. I’ve never tried it as the recipent needs to be using Thunderbird, but it might work if you’ve prearranged with others to all use Thunderbird.
Which is kinda my point. Getting around backdoors, if they were ever mandated, is trivially easy.
Encryption backdoors would make file encryption useless. I’ve seen too many news stories of tools that are only supposed to be used for law enforcement purposes under strict use requirements being used by an individual within a department for personal reasons, usually for illegal purposes.
If a backdoor to encryption were to be made available, I’m sure that procedures would be put in place as to when, how, and by whom, the key would be used. But unless they were treated the same as the launch codes for nuclear weapons, it would be only a matter of time before the keys were leaked. Otherwise, someone would use the tool “just this once” for some other purpose.
(I served on ballistic missile submarines. Deadly force was authorized to protect anything to do with the systems associated with the missiles. Crew members who were authorized access were subject to stringent and intrusive security requirements. There was also a two-man rule for sensitive actions. I wasn’t one of them.)
Leo’s analogy for TSA Master Keys is great. You can even purchase TSA Master Keys very cheaply on Amazon.
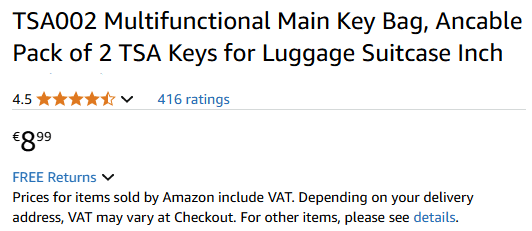
As soon as an encryption program adds a backdoor, the Master Key will be available on the Dark Web, or even Amazon, within hours.
If there is a backdoor on some encryption, then, criminals all over the world will work overtime to discover it AND use it. NO exception.
The question is not : «Will the back door be discovered ?»
The question is : «How long before criminals get their hands on in and how many criminals will use it ?»
The answer is probably within hours.